Information Systems Creating Business Value John Wiley Sons
Information Systems: Creating Business Value John Wiley & Sons, Inc. Mark Huber, Craig Piercy, and Patrick Mc. Keown
Chapter 8: E-Commerce Technologies

What We Will Cover: • The Stages of E-Commerce • First Generation E-Commerce Technologies: Establishing a Web Presence • Second Generation E-Commerce Technologies: Providing Interaction • Third Generation E-Commerce Technologies: Supporting Transactions • Fourth Generation E-Commerce Technologies: Transforming Process
Student ROI (Return on Investment) Your investment of time and effort in this course will result in your being able to answer these questions: 1. How has e-commerce evolved over the years to provide ever-increasing business value? 2. Why do many businesses still rely on first generation ecommerce technologies? 3. How do the second-generation e-commerce technologies provide businesses with more effective customer relationship management? 4. How do the third-generation e-commerce technologies support business transactions. 5. How the fourth-generation e-commerce technologies contribute to strategic alliances.
The Stages of E-commerce • Previously you were introduced to the applications of e-commerce. Now, you will be introduced to the underlying technologies support e-commerce. • In its short history, e-commerce has gone through several distinct generations of growth.
Four Generations of E-commerce • First generation: • Second generation: • Third generation: • Fourth generation:
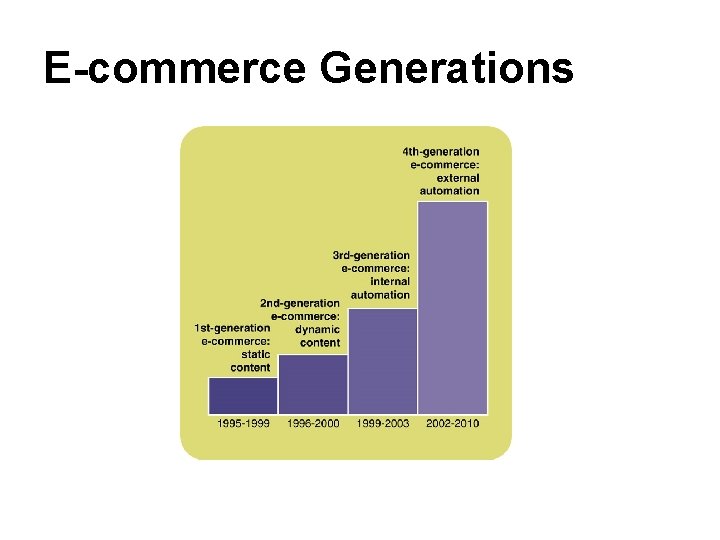
E-commerce Generations
First Generation: Establishing a Web Presence Basic technologies are still used: – Client/server networks: – Browser: – HTTP protocol: – HTML:
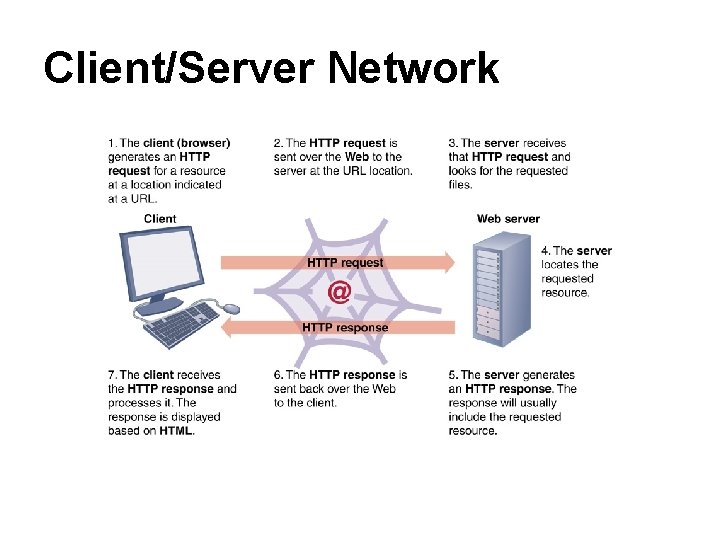
Client/Server Network
Web Browsers • What is a Web browser? • It responds to the URL you enter or the hyperlink you click by displaying a hypertext-based file. • Hypertext organizes content into units that are connected using associations called ____. • Browsers typically include a ________ (GUI) that make them easy to use. • Browsers have multimedia capabilities that enhance the information a business conveys. • Browsers all work similarly presenting a common interface to all users.
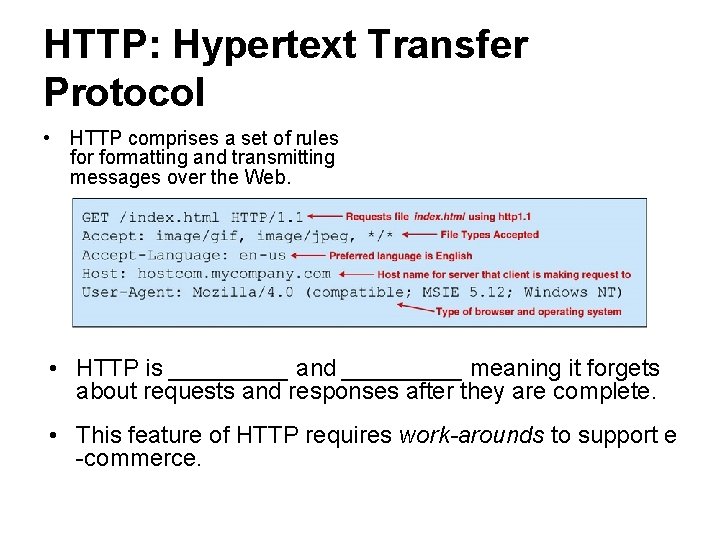
HTTP: Hypertext Transfer Protocol • HTTP comprises a set of rules formatting and transmitting messages over the Web. • HTTP is _____ and _____ meaning it forgets about requests and responses after they are complete. • This feature of HTTP requires work-arounds to support e -commerce.
HTML: Hypertext Markup Language • What is Hypertext Markup Language (HTML)? • The browser interprets the HTML through the use of tags which are used to format the content of the Web page. • The tags, enclosed in angle brackets (< and >) mark the placement and appearance of page components.
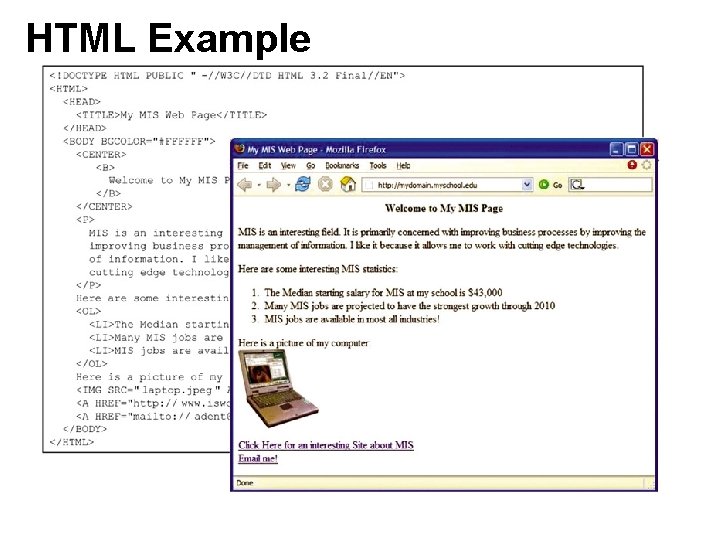
HTML Example
Second Generation: Providing Interaction • Providing interaction between the Web page and user requires dynamic content based on user input and programming instructions. • The process is: – – • Input data comes from several sources – –
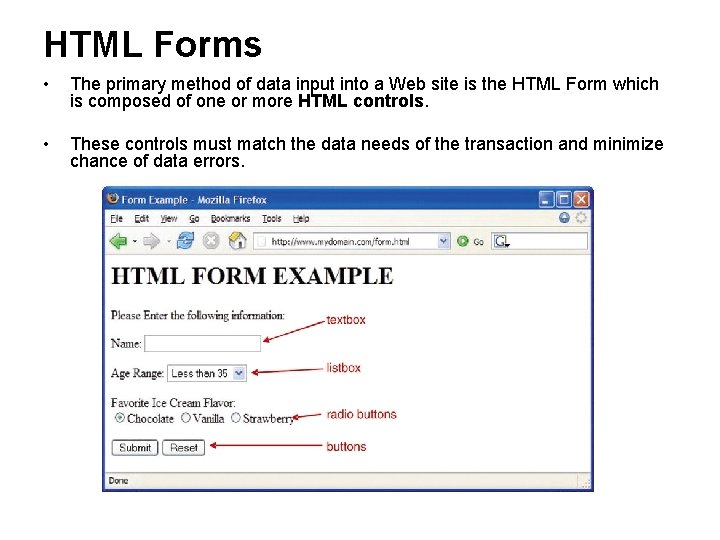
HTML Forms • The primary method of data input into a Web site is the HTML Form which is composed of one or more HTML controls. • These controls must match the data needs of the transaction and minimize chance of data errors.
Storing Data on the Client Side • To be able to carry out e-commerce transactions, it is necessary to store data about the customer on the client side. • One way to do this is to use a ______ which is small bit of data stored on the client machine and passed back and forth between it and the Web server. • Typical data on a cookie include information about the client machine, the domain name of the server that created it, and so on. • When data remain on the client machine for a period of time, this is a _____ cookie. • How and why can the use of cookies create privacy concerns?
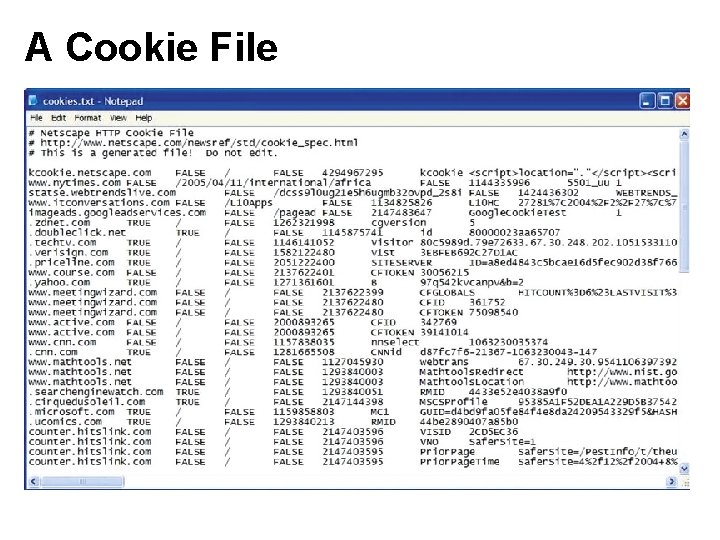
A Cookie File
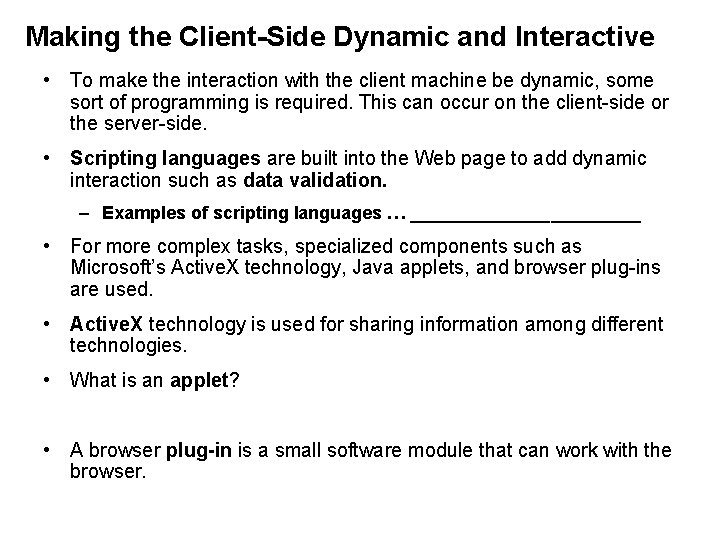
Making the Client-Side Dynamic and Interactive • To make the interaction with the client machine be dynamic, some sort of programming is required. This can occur on the client-side or the server-side. • Scripting languages are built into the Web page to add dynamic interaction such as data validation. – Examples of scripting languages … ____________ • For more complex tasks, specialized components such as Microsoft’s Active. X technology, Java applets, and browser plug-ins are used. • Active. X technology is used for sharing information among different technologies. • What is an applet? • A browser plug-in is a small software module that can work with the browser.
Server-side Programming • When programs run on the Web server to provide dynamic interaction, this is known as server-side programming. • It is more powerful than client-side scripting and allows the Web page owner to retain control over the programs. • With server-side programming, a business can: – – –
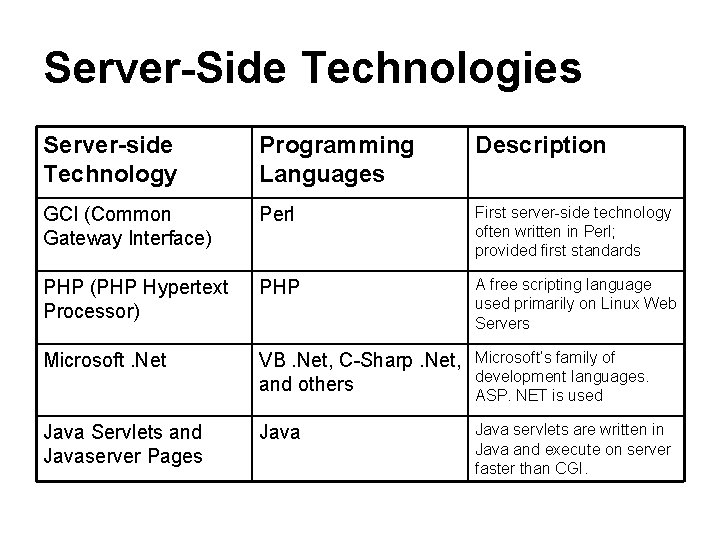
Server-Side Technologies Server-side Technology Programming Languages Description GCI (Common Gateway Interface) Perl First server-side technology often written in Perl; provided first standards PHP (PHP Hypertext Processor) PHP A free scripting language used primarily on Linux Web Servers Microsoft. Net VB. Net, C-Sharp. Net, and others Microsoft’s family of development languages. ASP. NET is used Java Servlets and Javaserver Pages Java servlets are written in Java and execute on server faster than CGI.
The n-Tier Infrastructure • An e-commerce system is composed of various layers or tiers with the number of tiers depending on what components are used. • What tiers make us a typical 4 -tier system? • For a really large system, there will be multiple computers set up to handle the processing at each server tier.
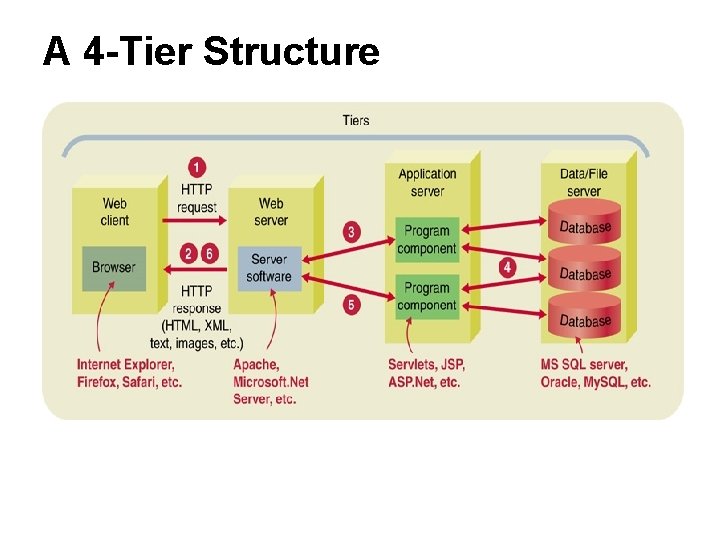
A 4 -Tier Structure
Carrying out a Transaction 1. An HTTP request for a Web page is sent from your browser. 2. Web server receives request and determines how to respond (almost always sending a Web page. ) 3. If request requires a dynamic response, Web server acts as controller routing messages between client and application server. 4. When needed, the database server is queried. 5. Results of an executed application are formulated into a Web page. 6. The Web server includes dynamically generated page in HTTP response which is sent to browser.
Third Generation: Supporting Transactions In the third generation of e-commerce, businesses recognized that they must deal with three issues to be successful: 1. 2. 3.
Search Engines • Internet search engines make it possible for customers to find information—probably too much information! • When you search the Web, you are really searching a database that was created from previous Web searches. • The main difference in search engines is how the database of Web locations is created and organized. • What is a Web crawler? Is this the only way that sites are “found” (added/incorporated) by search engines? • An important consider is how the database organizes or indexes the Web data. Which pages are shown first when you submit search criteria?
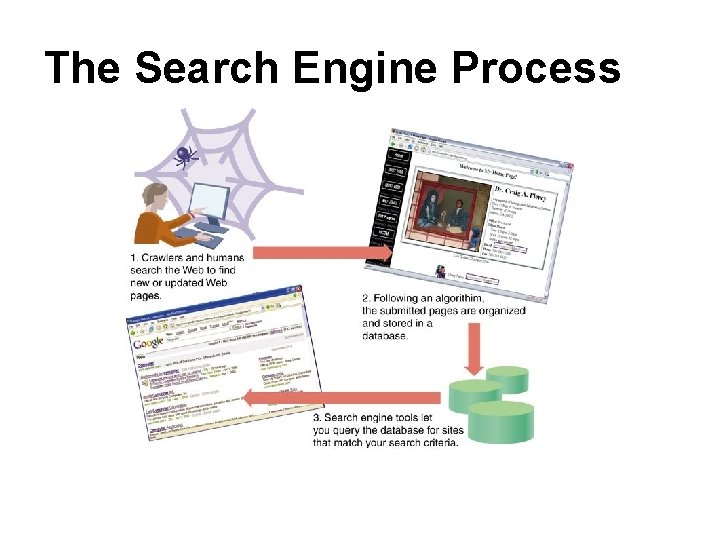
The Search Engine Process
Order and Payment Systems All e-commerce sites must have components for processing orders and accepting payments. The four primary components of a typical e-commerce site are: 1. 2. 3. 4. Most e-commerce systems use a secure HTML order form or an in-house shopping cart system. Smaller businesses often use third party merchant accounts like that available from Pay. Pal. The shopping cart system is the most popular e-commerce system for larger businesses where a customer wants to buy multiple products usually using a credit card.
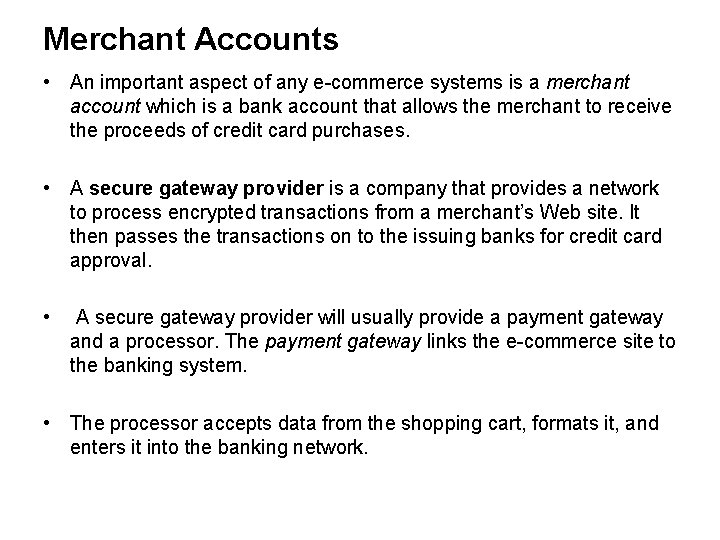
Merchant Accounts • An important aspect of any e-commerce systems is a merchant account which is a bank account that allows the merchant to receive the proceeds of credit card purchases. • A secure gateway provider is a company that provides a network to process encrypted transactions from a merchant’s Web site. It then passes the transactions on to the issuing banks for credit card approval. • A secure gateway provider will usually provide a payment gateway and a processor. The payment gateway links the e-commerce site to the banking system. • The processor accepts data from the shopping cart, formats it, and enters it into the banking network.
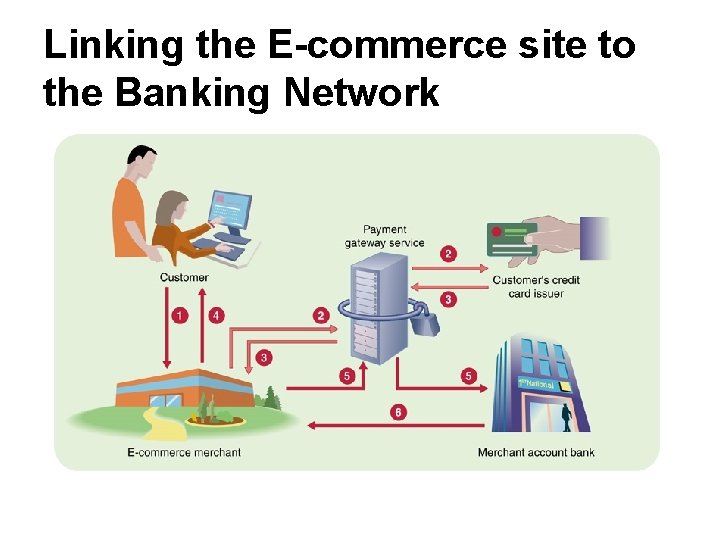
Linking the E-commerce site to the Banking Network
Steps in the E-commerce Process 1. Customer places order thought e-commerce Web site. 2. The payment gateway provider detects the placement of an order. The provider securely encrypts the transaction data and passes an authorization request to the bank to verify the customer’s credit card account and available funds. 3. The gateway provider returns a response, indicating whether or not the transaction is authorized, to the e-commerce merchant. This process typically takes less than 3 seconds. 4. Upon approval, the e-commerce merchant notifies the user and fulfills the customer's order. 5. The gateway provider sends a settlement request to the merchant account’s bank. 6. The merchant account’s bank deposits the transaction funds into the ecommerce merchant’s account.
E-commerce Security • The order and payment systems must be secure to protect both the customer and the merchant. Several technologies to do this have been developed. • Most e-commerce security technologies relate to the Secure Socket Layer (SSL) protocol, which allows a client and a server to communicate in a way that prevents eavesdropping, message forgery, or tampering. • A server that encrypts data using the SSL protocol is known as a secure server which uses shttp instead of http. • A web site can signal that it uses SSL to encrypt data by purchasing an SSL site certificate. • Another security system is the Secure Electronic Transaction (SET) protocol from Microsoft and Master. Card. • Cookies are an important part of these security systems as they are used to authenticate users or to hold data to match the user in the shopping cart.
Encryption • The most common method of providing security to e-commerce transactions, as well as most other Internet activity, is encryption, which is the process of scrambling a message so that it is meaningful only to the person holding the key to deciphering it. • The reverse process, decryption, converts a seemingly senseless character string into the original message. • There are two primary forms of encryption systems: private key and public key encryption. A key is an algorithm used to encode and decode messages. • What is Private Key encryption? • What is a Public-Key encryption system?
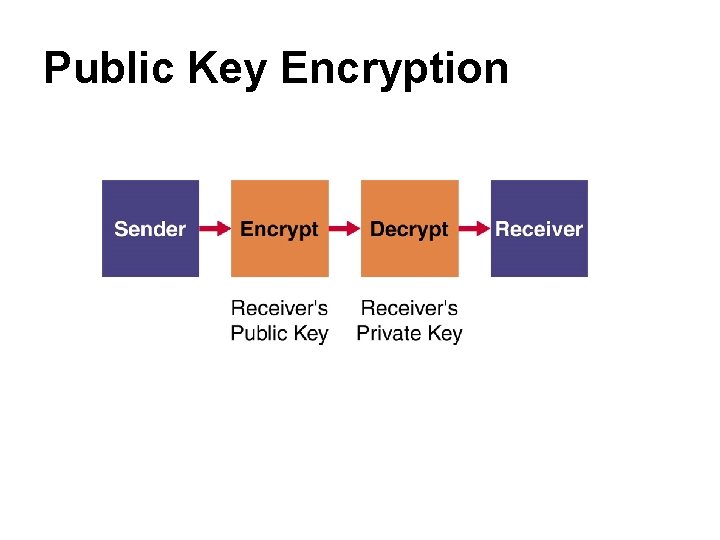
Public Key Encryption
Fourth-Generation: Transforming Processes • XML and web services were mentioned earlier as technologies for dealing with the software integration problem. • These technologies are moving us into the realm of automatic interaction between computers at one business automatically interacting with computers at another business. • For e-commerce, these technologies are improving the ability to exchange small amounts of data via the web and to standardize the support of transactions.
e. Xtensible Markup Language (XML) • How is XML (e. Xtensible Markup Language), like HTML? – • The goal of XML is to –? – while the goal of HTML is to describe how to display data. • Using XML, companies can define their own tags that their trading partners can understand.
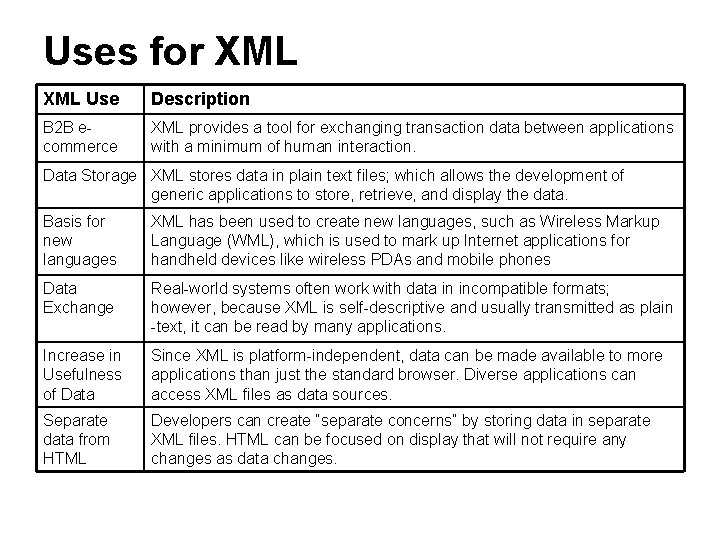
Uses for XML Use Description B 2 B ecommerce XML provides a tool for exchanging transaction data between applications with a minimum of human interaction. Data Storage XML stores data in plain text files; which allows the development of generic applications to store, retrieve, and display the data. Basis for new languages XML has been used to create new languages, such as Wireless Markup Language (WML), which is used to mark up Internet applications for handheld devices like wireless PDAs and mobile phones Data Exchange Real-world systems often work with data in incompatible formats; however, because XML is self-descriptive and usually transmitted as plain -text, it can be read by many applications. Increase in Usefulness of Data Since XML is platform-independent, data can be made available to more applications than just the standard browser. Diverse applications can access XML files as data sources. Separate data from HTML Developers can create “separate concerns” by storing data in separate XML files. HTML can be focused on display that will not require any changes as data changes.
Web Services • What are Web services? • A web service is a platform-independent software component that can be: – – – • Web services give companies the ability to do more e-commerce business, with more potential business partners, and in more different ways than before at a reasonable cost. • Web services are based on a number of accepted standards that allows everybody to work on the same basis.
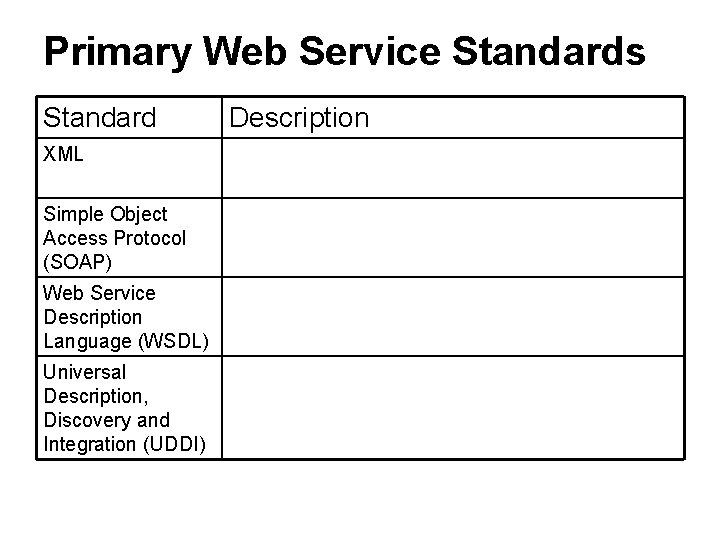
Primary Web Service Standards Standard XML Simple Object Access Protocol (SOAP) Web Service Description Language (WSDL) Universal Description, Discovery and Integration (UDDI) Description
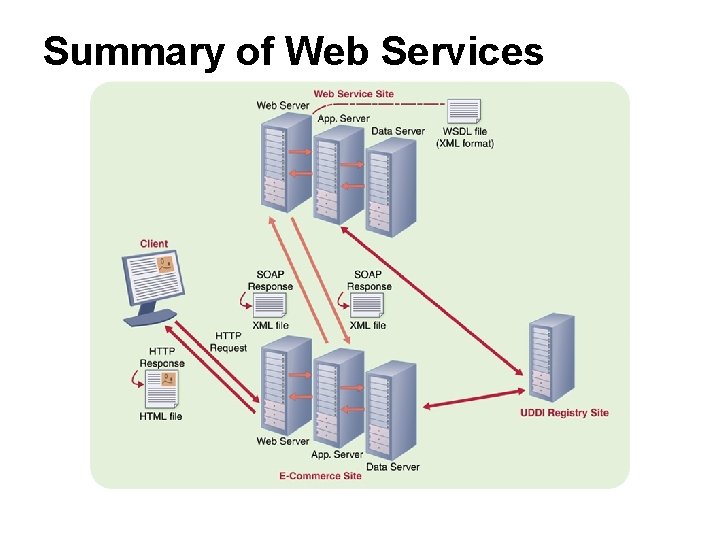
Summary of Web Services
- Slides: 39