Information Systems Creating Business Value John Wiley Sons
Information Systems: Creating Business Value John Wiley & Sons, Inc. Mark Huber, Craig Piercy, and Patrick Mc. Keown Copyright 2007 John Wiley & Sons, Inc.
Chapter 9: The Connected Enterprise: Business Partnering and Protecting Copyright 2007 John Wiley & Sons, Inc.
What We Will Cover: • • • Corporate and IT Governance A Global Perspective Global IS and Global IT Enterprise Risk Management Enterprise Information Security Copyright 2007 John Wiley & Sons, Inc.
Student ROI (Return on Investment) Your investment of time and effort in this course will result in your being able to answer these questions: 1. Why are corporate and IT governance important? 2. What does it mean to have a global perspective? 3. How do global IS and IT globalization help a business to create value? 4. What is enterprise risk management and what are some of the enterprise risk management procedures that every business should implement to avoid business losses? 5. What is enterprise information security? Copyright 2007 John Wiley & Sons, Inc.
Topics for Discussion • The important laws, regulation, and frameworks that impact IT governance and the creation of business value. • The need for knowledge workers and businesses to have a global perspective and to understand the globalization of IT • The opportunities and risks when organizations seek to create business value through partnerships and global sourcing • The requirement for all parts of the organization to manage risks to the enterprise, to establish and maintain enterprise information security, and to ensure the proper control of financial and other sensitive data and information. Copyright 2007 John Wiley & Sons, Inc.
Corporate and IT Governance • Corporate governance is … ? • Technology impacts corporate governance necessitating IT governance. • IT governance is. . . ? 1 • IT governance begins as a very high-level process that specifies … 2 1. 2. 3. ____ 1. Peterson, R. , 2004. “Crafting Information Technology Governance, ” Information Systems Management, www. ism-journal. com. Fall 2004. 2. Adapted from IT Governance Institute ® website, http: //www. itgi. org, 6/15/2005. Copyright 2007 John Wiley & Sons, Inc.
The CIO The Chief Information Officer (CIO): 1. 2. 3. 4. Copyright 2007 John Wiley & Sons, Inc.
Creating value via IT governance • Effective IT governance and leadership combines Porter’s competitive strategies with the value chain model to help create business value. • Examples of ways IT can create business value include (see next figure to interpret the numbers that follow each statement below): – By integrating technology to reduce or eliminate costs throughout its value chain, until it becomes the lowest cost producer or retailer (1). – By developing a specific IT strategy, which enables the business to implement its lowest-cost strategy (2 -5). – Enabling outsourcing opportunities with reduced labor costs that helps the business to offer a lower price for quality product or service (6). – If outsourcing a business process to another country, IT leadership will need to develop a strategy that includes how to support global operations (back to 1). – Regardless of whether implementing automation, outsourcing, or both, the business must measure the performance and costs of the automation or outsourcing effort against the unit cost savings for the product or service. This determines if the IT strategy aligns with and meets the needs of the “lowest-cost” business strategy (7 -8). – If not, the IS leadership must act to bring performance in line with expectations (5). Copyright 2007 John Wiley & Sons, Inc.
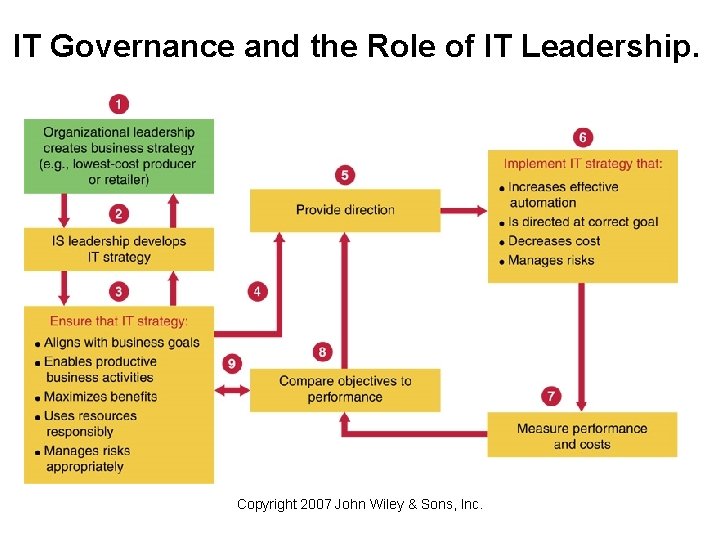
IT Governance and the Role of IT Leadership. Copyright 2007 John Wiley & Sons, Inc.
A global perspective • What is a global perspective? • Friedman writes that, “More people can collaborate and compete in real time with more other people on a more equal footing than at any previous time in the history of the world using computers, e-mail, networks, teleconferencing, and dynamic new software. ” – What does this mean for businesses? • Omahe writes that a global economy is borderless, invisible (money moves around the globe in electronic format), cyber-connected, and measured in multiples (premium value that investors are willing to pay for ownership of some companies. – How does this apply to companies like Google? Like Ikea? Copyright 2007 John Wiley & Sons, Inc.
A global perspective (cont. ) • C. K. Prahalad suggests that global success can only come from discarding old ways of viewing the global marketplace as simply a geographic expansion of current business processes and existing product sales. – Do you agree or disagree with Prahalad’s opinion and why? • One viewpoint is that the world is much more of a level playing field with more opportunities than ever before to compete and collaborate without being stifled by geographical boundaries--not only do you have to think globally, but you must act “locally” in multiple locations. – Do you think that globalization has leveled the playing field, made it more uneven, or had no effect at all? Copyright 2007 John Wiley & Sons, Inc.
One view of a “flat earth” Relative to a global economy and globalization, what does the term “flat earth” mean to you? Copyright 2007 John Wiley & Sons, Inc.
Global perspective continued… • Outsourcing is not the same as destroying US jobs • Not all American products are fully American and vice versa • Corporate success comes from thinking globally and acting locally like News Corp, HSBC et al. • Globalization need not be originated by American firms all the time, e. g. : Lenovo’s Acquisition of IBM’s PC business Copyright 2007 John Wiley & Sons, Inc.

Partnerships • Complementary talents, large capital requirements and opportunities to synergize necessitate partnerships. • Partnerships can be local as we all global. E. g. Nokia, a Finnish firm, partners with firms across the globe, like IBM, Avaya, Cisco, Vodafone and so on. • Credit cards are a result of partnerships among banks and retailers. • IT is a huge enabler of global partnerships. Copyright 2007 John Wiley & Sons, Inc.
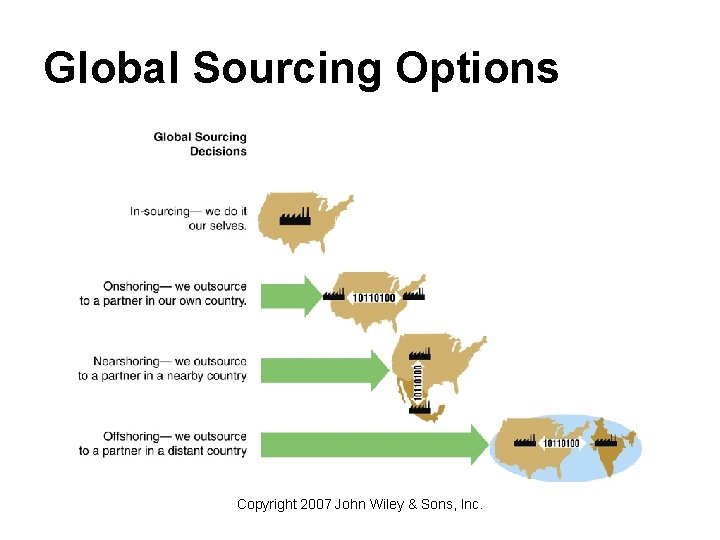
Global Sourcing Options Copyright 2007 John Wiley & Sons, Inc.
Global sourcing • In-sourcing: • On-shoring: • Near-shoring: • Off-shoring: Copyright 2007 John Wiley & Sons, Inc.
Trans-border data flow (TBD) • What is trans-border data flow? How is TBD be related to global sourcing? • What types of issues are raised by TBD and why should businesses be concerned with these issues? Copyright 2007 John Wiley & Sons, Inc.
Organization for Economic Co-operation and Development (OECD) guidelines on trans-border data flow • Collection limitation: • Use limitation: • Security safeguards: • Data Haven: Copyright 2007 John Wiley & Sons, Inc.
Multinational and Transnational companies • How are Multinational Companies (MNCs) defined? – – Can you name one or more MNCs? • How are Transnational Companies (TNCs) defined? – – Can you give an example of one or more TNCs? Copyright 2007 John Wiley & Sons, Inc.

Logitech Products Logitech – MNC or TNC? Copyright 2007 John Wiley & Sons, Inc.
Global Information System • What is a global information system? • What are some examples of global IS creating business value for companies? Copyright 2007 John Wiley & Sons, Inc.
IT Globalization According to Ives and Jarvenpaa, the key issues in the successful deployment and management of global IT include: 1. 2. 3. 4. Copyright 2007 John Wiley & Sons, Inc.
Enterprise Risk Management (ERM) • Enterprise Risk Management (ERM) is a process effected (made to happen) by an entity’s stakeholders applied strategically across the enterprise. ERM is designed to identify potential events that may affect the entity, and manage risk to be within its risk appetite, and to provide reasonable assurance regarding the achievement of entity goals. Copyright 2007 John Wiley & Sons, Inc.
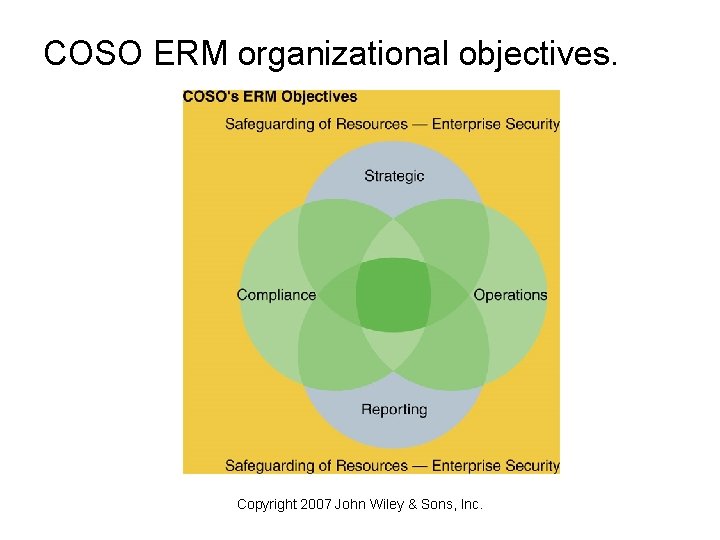
COSO ERM organizational objectives. Copyright 2007 John Wiley & Sons, Inc.
More about risk • Security provides the backdrop for all successful ERM efforts. • Protection is needed against theft of data, hacking, denial of service attacks, and so on. • Impact and likelihood of perceived dangers give an idea on how much money needs to be spent in averting risk. Copyright 2007 John Wiley & Sons, Inc.
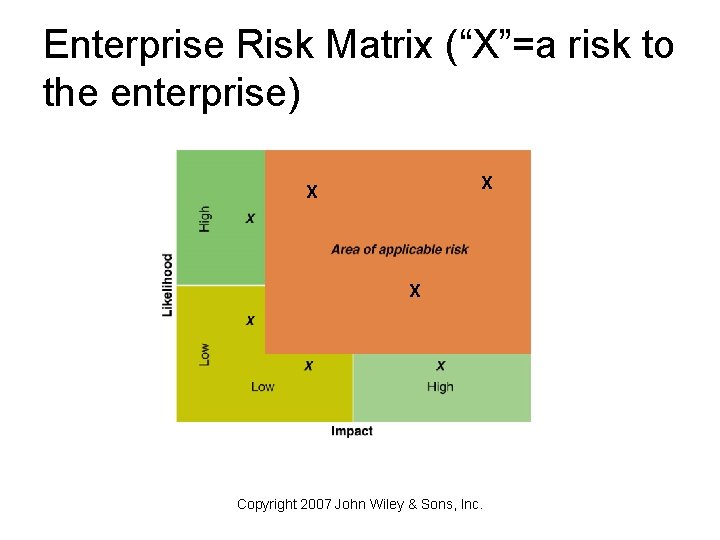
Enterprise Risk Matrix (“X”=a risk to the enterprise) X X X Copyright 2007 John Wiley & Sons, Inc.
Risk management methods • Risk Transfer – • Risk Deferral – • Risk Reduction – • Risk Acceptance – • Risk Avoidance – Copyright 2007 John Wiley & Sons, Inc.
The Role of Compliance • Compliance is about adhering to both the letter and the intent of relevant laws and regulations. • How can effective compliance reduce risk? – – – • How can effective compliance build trust and confidence regarding the organization and it’s practices? Copyright 2007 John Wiley & Sons, Inc.
Examples of compliance-related laws and regulations • Sarbanes Oxley Act: • California Senate Bill 1386: • Gramm-Leach-Bliley Act: Copyright 2007 John Wiley & Sons, Inc.
More examples of compliancerelated laws and regulations • EU Data Protection Directive: • Basel II Accord: • Health Insurance Portability And Accountability Act (HIPPA): Copyright 2007 John Wiley & Sons, Inc.
About HIPAA • What is HIPAA? • HIPAA is applicable to. . . ? – – – • HIPAA ensures the _____ and _____ of the health related data of patients. • HIPAA necessitates that the healthcare business has to invest heavily in information security technology. Copyright 2007 John Wiley & Sons, Inc.
Europe (mostly) and US (pretty much) privacy laws • EU privacy laws much more restrictive as to what firms can do with individual’s data – – Firms tracking data must register with government Firms cannot access emails No asking for phone number at checkouts Data sharing is a no-no without explicit permission • In EU government is allowed to track a great deal more information than in US and has more control over certain things – What my baby’s name? – Wiretapping • EU tends (more or less) to trust government • US tends (more or less) to dis-trust government
Compliance and Control Frameworks and Standards for IT • COSO (Committee of Sponsoring Organizations of the Treadway Commission) • Cobi. T (Control Objectives for Information and Related Technology) • ISO 17799 and BS 7799 • ITIL (Information Technology Infrastructure Library) • Capability Maturity Model Integration (CMMI) • UCCnet • Rosetta. Net Copyright 2007 John Wiley & Sons, Inc.
Control Advantage, Control and Controls • Control Advantage: The strengthening of internal controls and compliance through ITbased controls to business processes, policies, and procedures. • What is a “control? ” • What is are organizational controls? Copyright 2007 John Wiley & Sons, Inc.
Internal Control • Internal controls are concerned with – – – • Internal controls can be 1. Preventive – 2. Detective – 3. Corrective – Copyright 2007 John Wiley & Sons, Inc.
Three Types of Controls: Preventive, Detective, Corrective Preventive Detective Copyright 2007 John Wiley & Sons, Inc. Corrective
Specific Internal Control Processes • Segregation of duties: • Authorization: • Security: • ID codes: Copyright 2007 John Wiley & Sons, Inc.
Internal Process Control Methods (Cont. ) • Verification controls: • Control totals: • Supervisory review: Copyright 2007 John Wiley & Sons, Inc.
Segregation of Duties Why is segregation of duties and effective internal control practice? How would you apply segregation of duties to IS? Copyright 2007 John Wiley & Sons, Inc.
Enterprise Information Security • Enterprise information security is an on-going, strategic business process of risk assessment and management, which helps to ensure safe business operations and the availability, confidentiality, and integrity of an enterprise’s information resources wherever they may be located. • Enterprise information security encompasses ________, and ____. • From a technology standpoint, enterprise information security is concerned with security against viruses, spyware and hacking. Copyright 2007 John Wiley & Sons, Inc.
The People-Policy-Technology Framework • Includes security awareness, training and governance. • Mitigates security risk as well as litigation risk. • People and organizational dynamics are at the center of the framework. • Relative to the P-P-T framework, how is policy defined? • Relative to the P-P-T framework, how is technology defined? Copyright 2007 John Wiley & Sons, Inc.
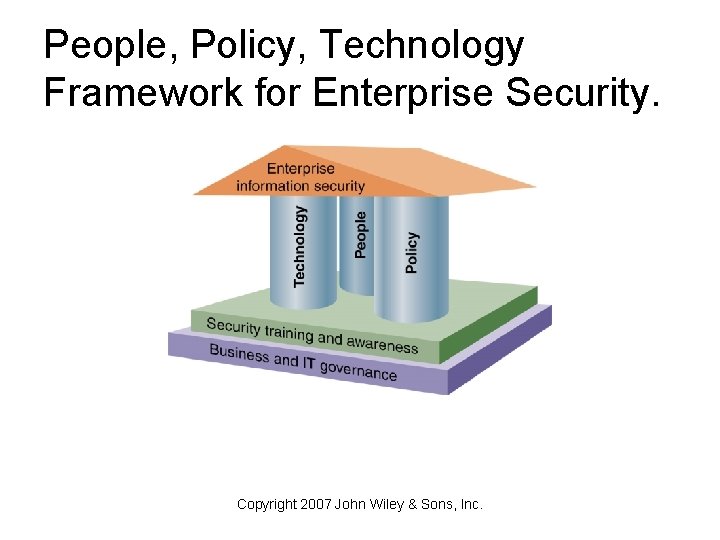
People, Policy, Technology Framework for Enterprise Security. Copyright 2007 John Wiley & Sons, Inc.
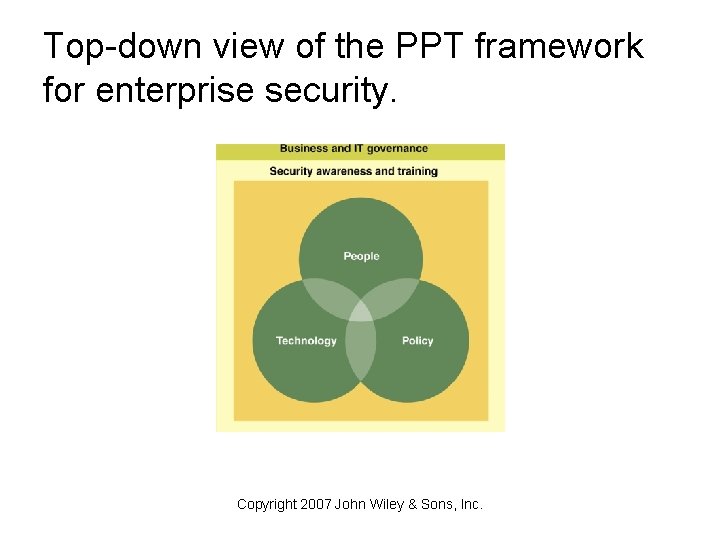
Top-down view of the PPT framework for enterprise security. Copyright 2007 John Wiley & Sons, Inc.
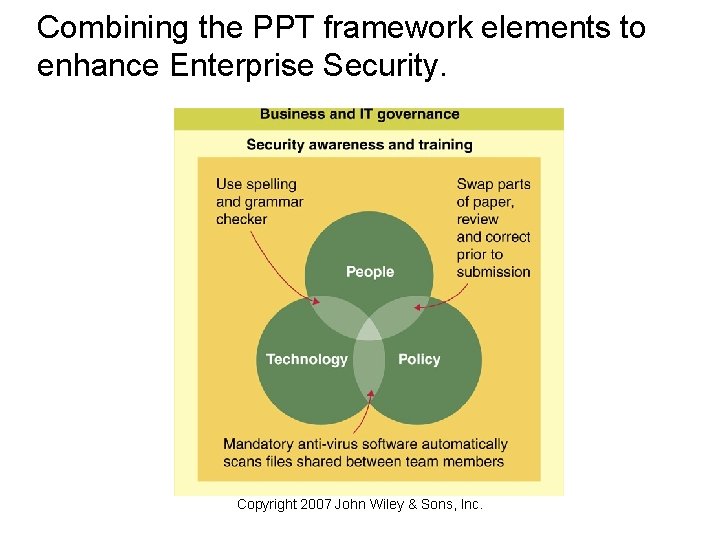
Combining the PPT framework elements to enhance Enterprise Security. Copyright 2007 John Wiley & Sons, Inc.
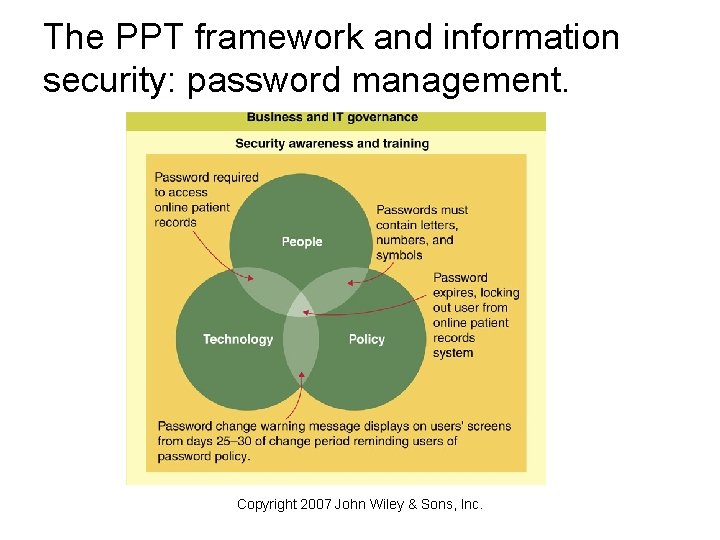
The PPT framework and information security: password management. Copyright 2007 John Wiley & Sons, Inc.
Takeaways • Globalization presents many challenges and risks to firms. • Globalization necessitates that the IT strategy of firms includes integrating, automating, informating, and transforming business processes to cut costs or to differentiate products and services. • IT strategy (including governance) has to be inline with corporate strategy (including governance). • Good governance is part of successful businesses strategies. • Enterprise risk management includes an on-going process that is the responsibility of all organizational members. • Compliance and internal control are elements of enterprise risk management and of good governance • Information security is a critical part of risk management as well as governance • Information security uses a PPT framework to ensure that people, policies, and technology support ERM, compliance, governance, IT and business strategies, and ultimately the creation of business value. Copyright 2007 John Wiley & Sons, Inc.
- Slides: 46