Information Security Theory vs Reality 0368 4474 01
![The AES Cipher (3) void Rijndael. Encrypt( u 8 input[16], u 8 output[16] ) The AES Cipher (3) void Rijndael. Encrypt( u 8 input[16], u 8 output[16] )](https://slidetodoc.com/presentation_image/42a7bf99f97c76017b4218364c42a2a5/image-7.jpg)
- Slides: 29
Information Security – Theory vs. Reality 0368 -4474 -01, Winter 2012 -2013 Guest Lecturer: Yossi Oren Lecture 6: Power Analysis 1
Required Reading http: //www. dpabook. org http: //www. springerlink. com/content/g 01 q 1 k 2
Fundamentals 3
Fundamentals �AES �Circuit Design �Statistics �Introduction to Power Analysis 4
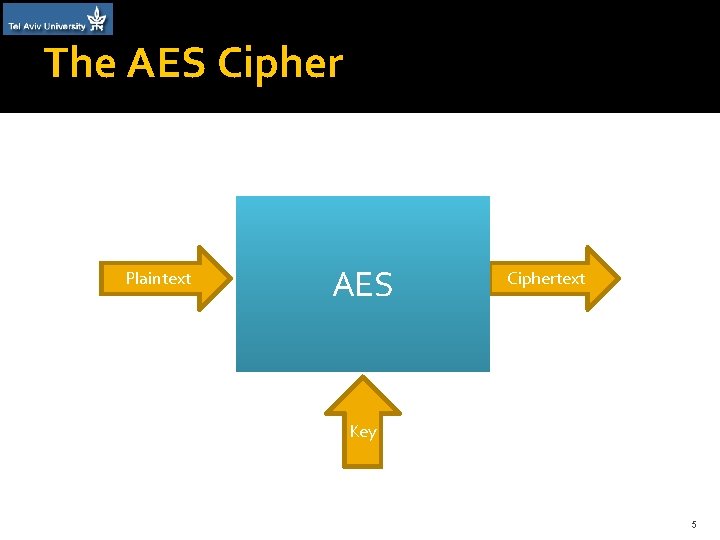
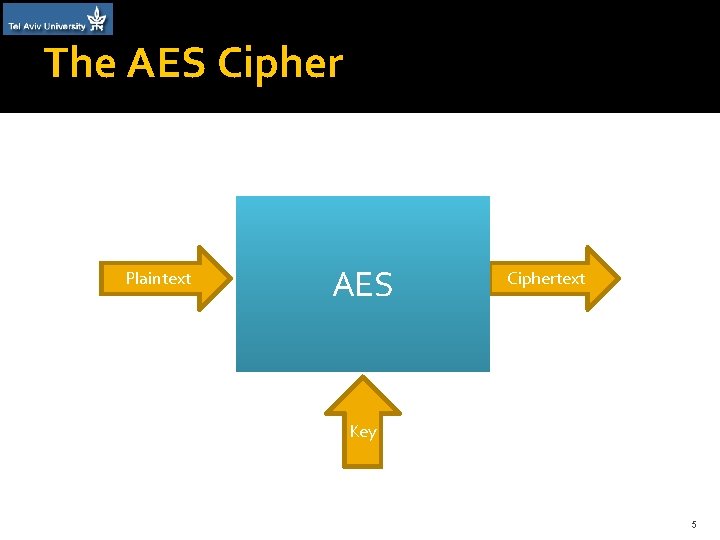
The AES Cipher Plaintext AES Ciphertext Key 5
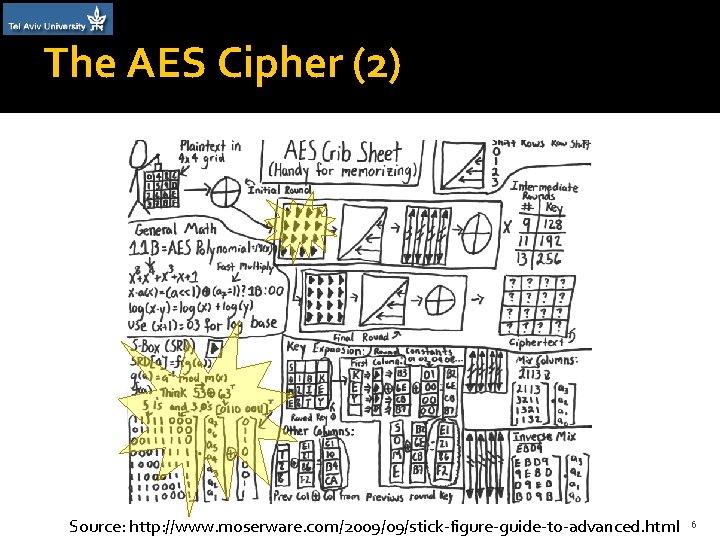
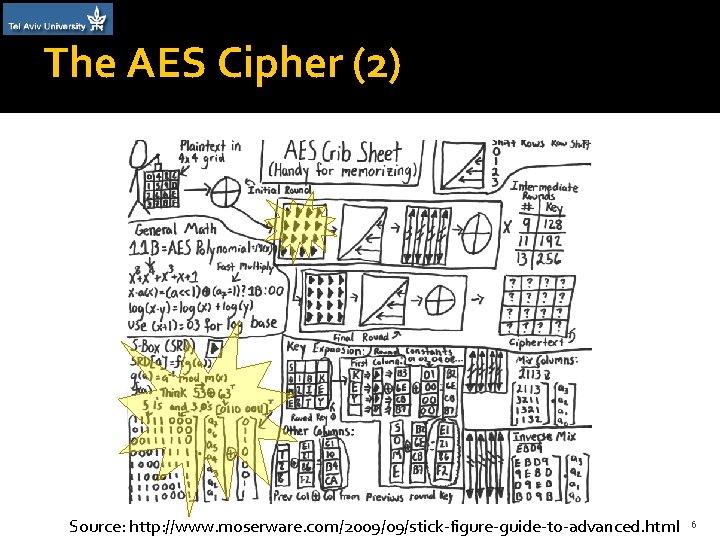
The AES Cipher (2) Source: http: //www. moserware. com/2009/09/stick-figure-guide-to-advanced. html 6
![The AES Cipher 3 void Rijndael Encrypt u 8 input16 u 8 output16 The AES Cipher (3) void Rijndael. Encrypt( u 8 input[16], u 8 output[16] )](https://slidetodoc.com/presentation_image/42a7bf99f97c76017b4218364c42a2a5/image-7.jpg)
The AES Cipher (3) void Rijndael. Encrypt( u 8 input[16], u 8 output[16] ) { […] for (r=1; r<=9; r++) { Byte. Sub(state); Shift. Row(state); Mix. Column(state); Key. Add(state, round. Keys, r); } […] Source: http: //users. ece. utexas. edu/~gerstl/ee 382 vics_f 09/soc/tutorials/System_C_Code_Examples_2/date 04_ examples/cosimulate/sw_only/ 7
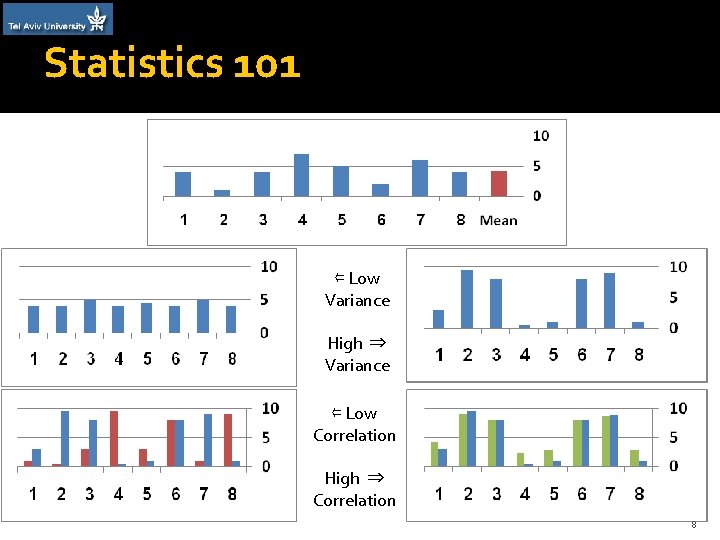
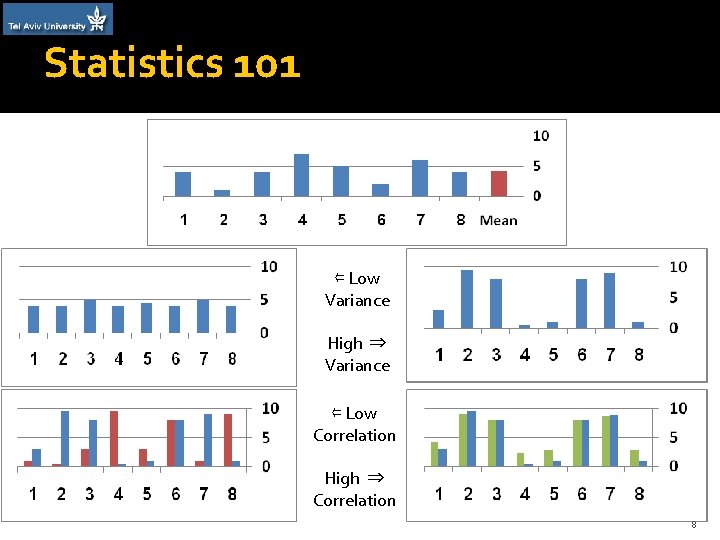
Statistics 101 ⇐ Low Variance High ⇒ Variance ⇐ Low Correlation High ⇒ Correlation 8
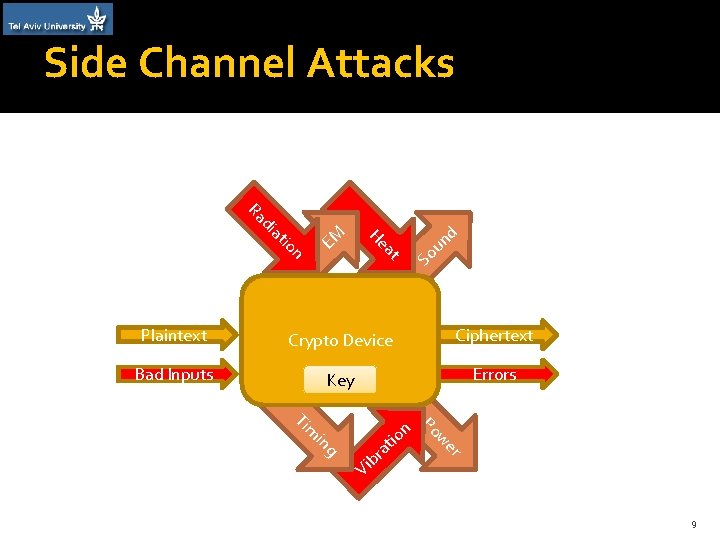
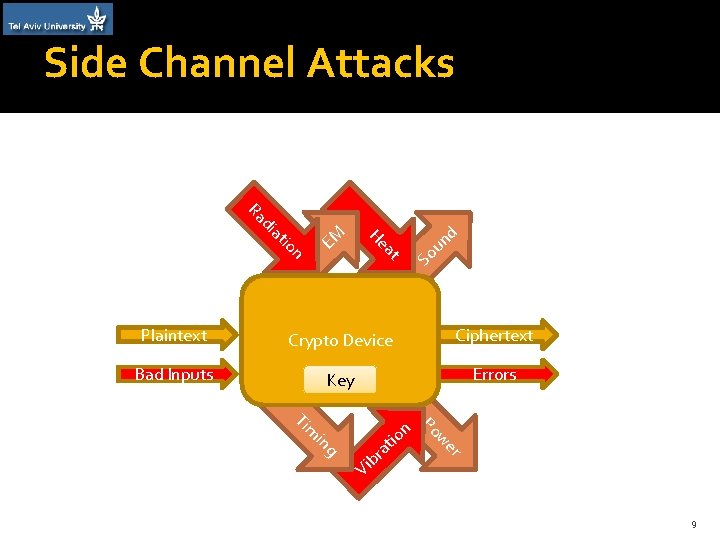
Side Channel Attacks Ra di at EM io n He at d n u So Plaintext Crypto Device Ciphertext Bad Inputs Key Errors Ti m in Po n w io er t ra g b Vi 9
Theory of power analysis �Power consumption is variable �Power consumption depends on instruction �Power consumption depends on data 10
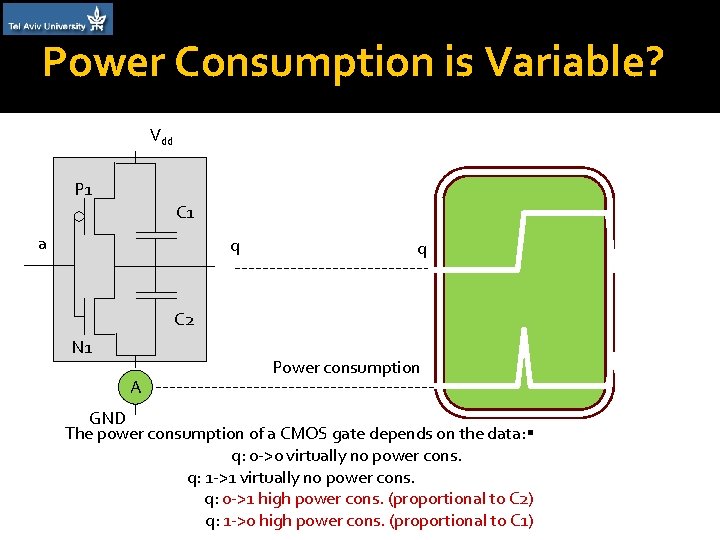
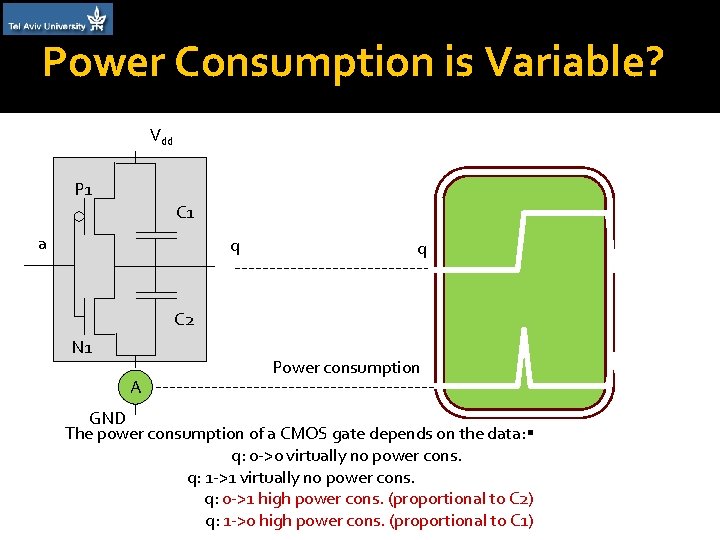
Power Consumption is Variable? Vdd P 1 C 1 a q q C 2 N 1 A Power consumption GND The power consumption of a CMOS gate depends on the data: q: 0 ->0 virtually no power cons. q: 1 ->1 virtually no power cons. q: 0 ->1 high power cons. (proportional to C 2) q: 1 ->0 high power cons. (proportional to C 1)
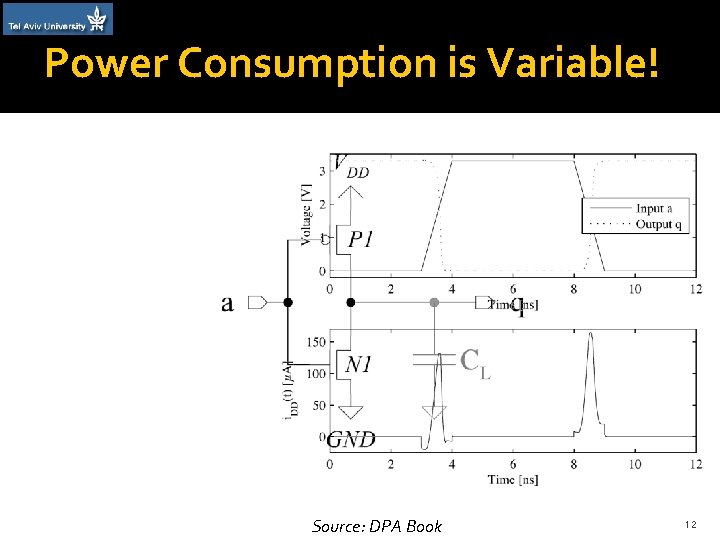
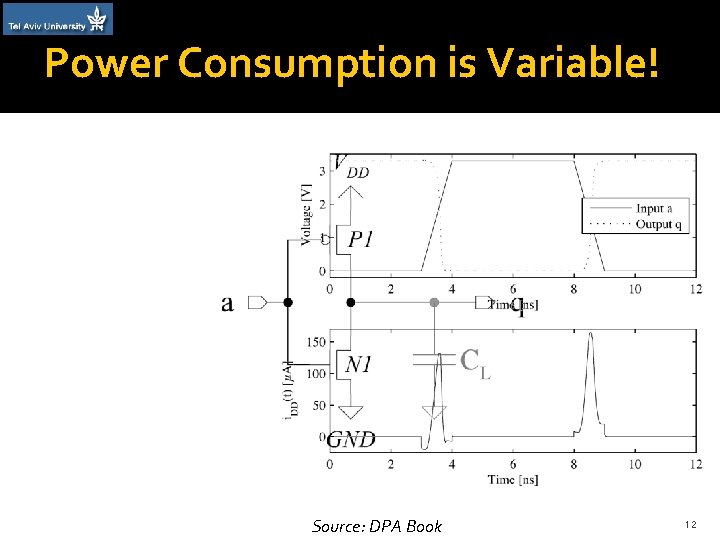
Power Consumption is Variable! Source: DPA Book 12
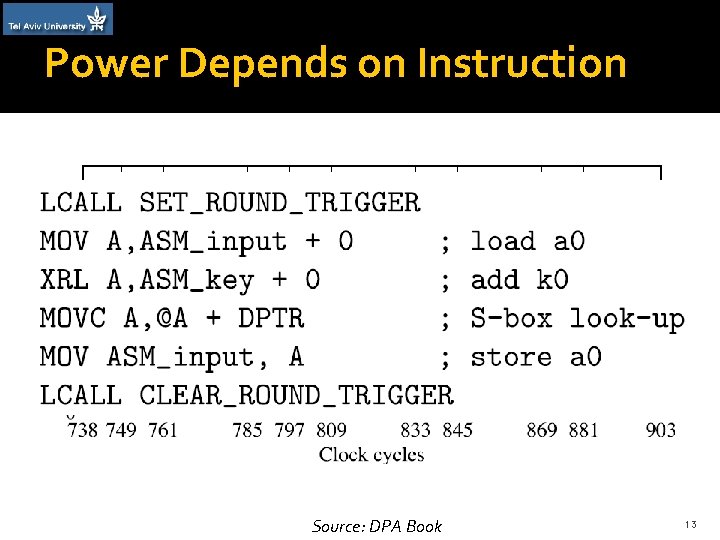
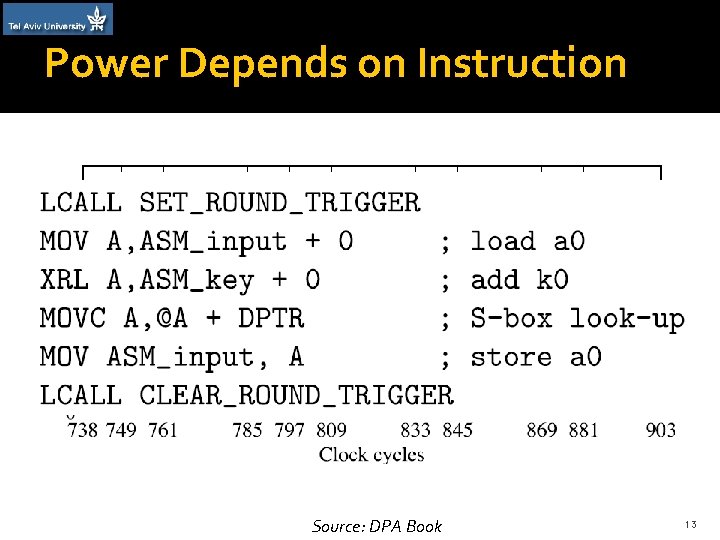
Power Depends on Instruction Source: DPA Book 13
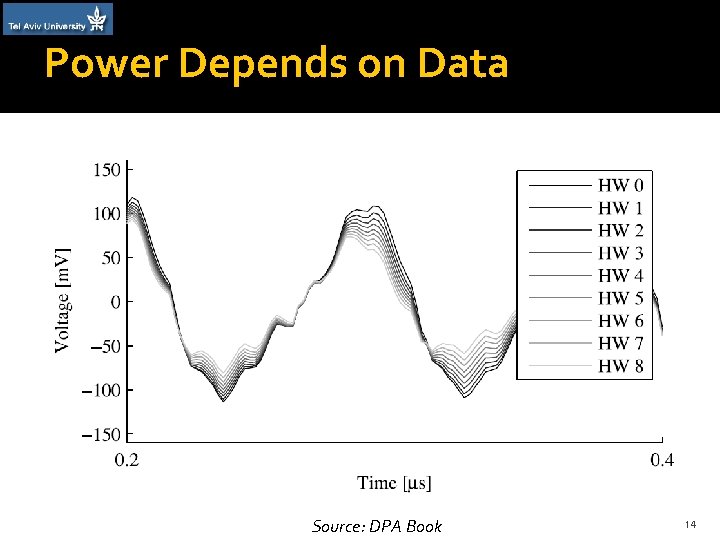
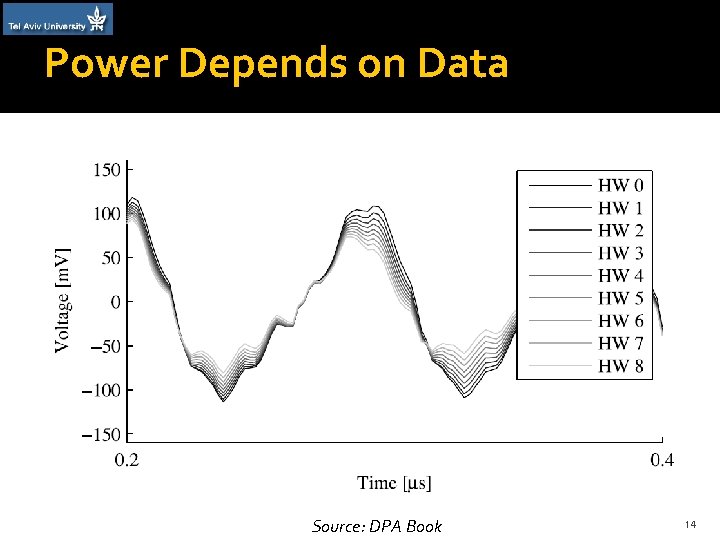
Power Depends on Data Source: DPA Book 14
Q&A (Fundamentals) • AES • Circuit Design • Statistics 15
Correlation Power Analysis (CPA) 16
Correlation Power Analysis �Simple Power Analysis �Warm-up Correlation Power Analysis �Full Correlation Power Analysis 17
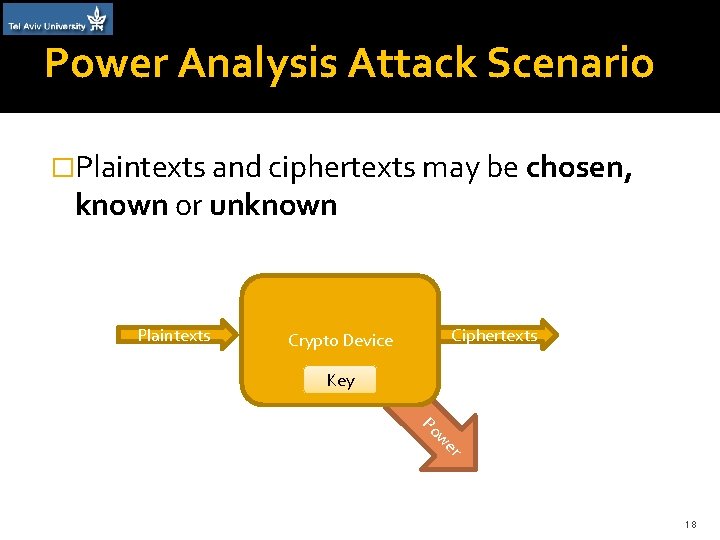
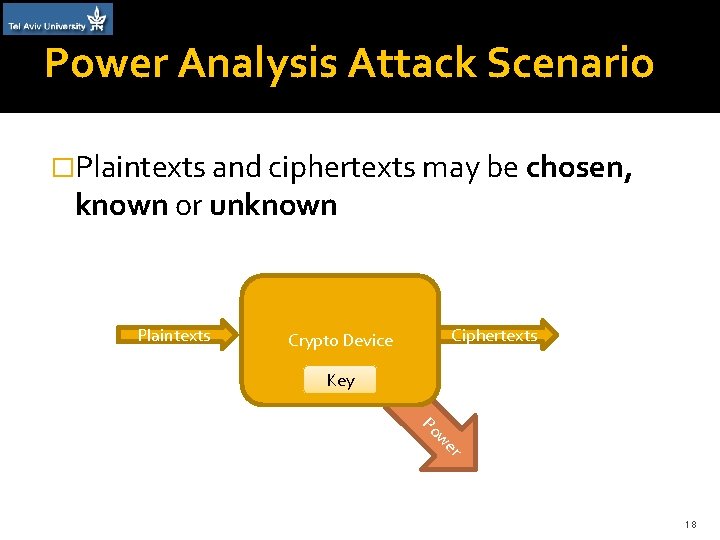
Power Analysis Attack Scenario �Plaintexts and ciphertexts may be chosen, known or unknown Plaintexts Ciphertexts Crypto Device Key Po w er 18
Theory of power analysis �Power consumption is variable �Power consumption depends on instruction �Power consumption depends on data 19
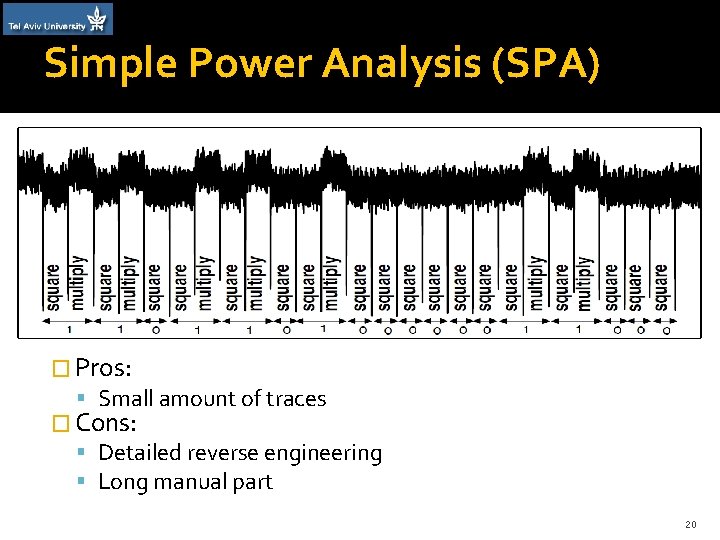
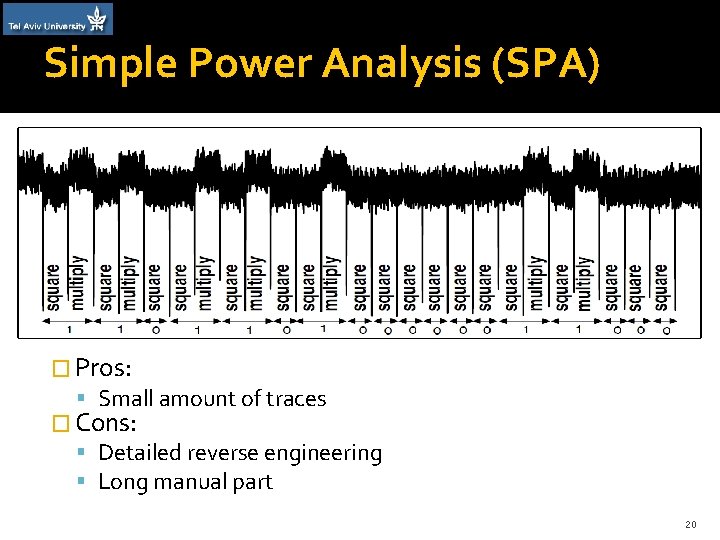
Simple Power Analysis (SPA) � Pros: Small amount of traces � Cons: Detailed reverse engineering Long manual part 20
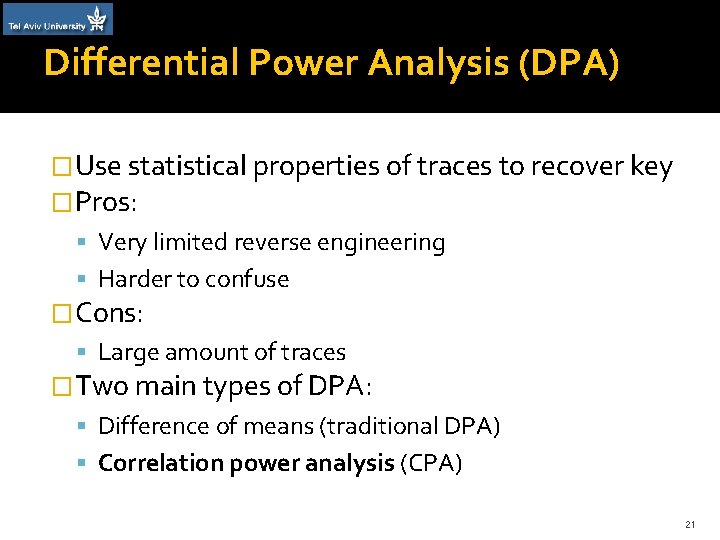
Differential Power Analysis (DPA) �Use statistical properties of traces to recover key �Pros: Very limited reverse engineering Harder to confuse �Cons: Large amount of traces �Two main types of DPA: Difference of means (traditional DPA) Correlation power analysis (CPA) 21
CPA Basics �We want to discover the correct key value (ck) and when it is used (ct) �Idea: On the correct time, the power consumption of all traces is correlated with the correct key On other times and other keys the traces should show low correlation 22
Warm-up CPA �Assume plaintext and correct key are known but correct time is unknown �Form hypothesis and test it �Good hypothesis: Depends on known plaintext Depends on small amount of key bits Non-linear – sensitive to small changes Maps to power consumption using a model 23
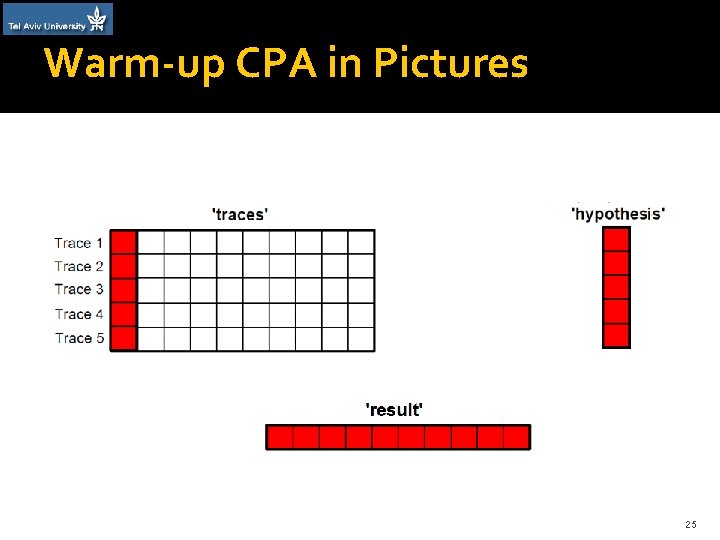
Warm-up CPA in Numbers � 1000 traces, each consisting of 1 million points �Each trace uses a different known plaintext – 1000 plaintexts � 1 known key �Hypothesis is vector of 1000 hypothetical power values �Output of warm-up CPA: vector of 1 million correlation values with peak at ct 24
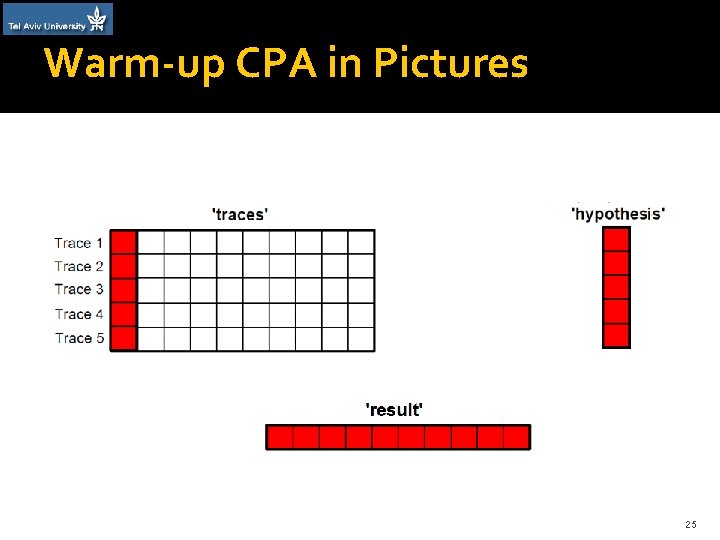
Warm-up CPA in Pictures 25
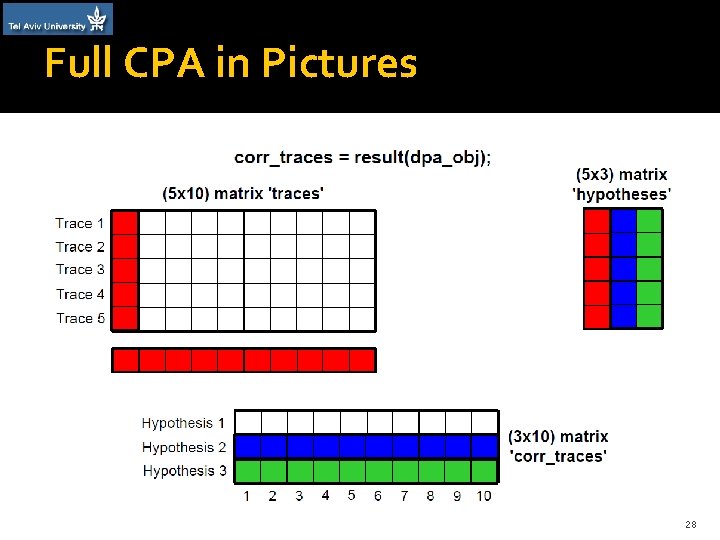
Full CPA �Plaintext is known, but correct key and correct time unknown �Idea: run warm-up CPA many times in parallel �Create many competing hypotheses 26
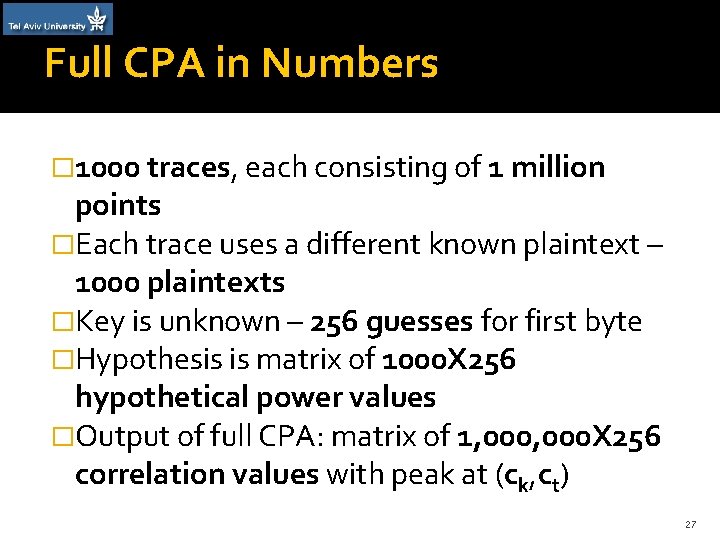
Full CPA in Numbers � 1000 traces, each consisting of 1 million points �Each trace uses a different known plaintext – 1000 plaintexts �Key is unknown – 256 guesses for first byte �Hypothesis is matrix of 1000 X 256 hypothetical power values �Output of full CPA: matrix of 1, 000 X 256 correlation values with peak at (ck, ct) 27
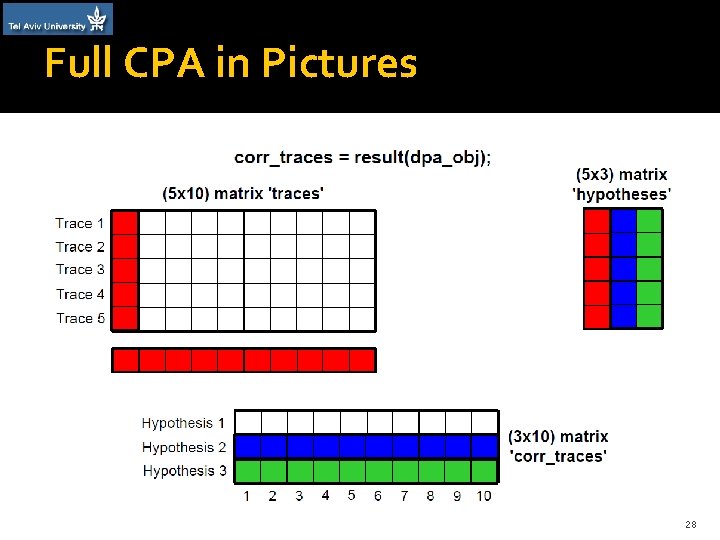
Full CPA in Pictures 28
Q&A (CPA) • Simple Power Analysis • Warm-up Correlation Power Analysis • Full Correlation Power Analysis 29