Information Security Risk Management A SYSTEMATIC VIEW TO

- Slides: 12
Information Security Risk Management A SYSTEMATIC VIEW TO APPROACHES
Content Concept Management Principles Framework Process Approaches Samples

What is an IT Risk? Risk = ƒ (Threat x Vulnerability x Impact) Vulnerability: weakness in the system or situation Threat: probability of occurrence of an event exploiting the vulnerability Impact: consequence Example – Information leakage Vulnerability: Unprotected sensitive traffic, unnecessary services enabled Threat: Eavesdropping, illegal processing of data Impact: Loss of business
How to manage IT Risks? Information Security Risk Management Identify organizational needs on info security in a systematic approach Create an effective information security management system (ISMS) Align with overall enterprise risk management Address risks in an effective and timely manner as needed Be an integral part of all information security management activities Apply both to implementation and ongoing operation of ISMS It is a continual process Organization as a whole, any discrete part of organization, or any IT system Principles apply
What are the Principles? Creates value 2. Integral part of organizational processes 3. Part of decision making 4. Explicitly addresses uncertainty 5. Systematic, structured and timely 6. Based on the best available information 7. Tailored 8. Takes human and cultural factors into account 9. Transparent and inclusive 10. Dynamic, iterative and responsive to change 11. Facilitates continual improvement and enhancement of the organization 1.
How to apply the Principles? Risk Management Framework Provide foundations and arrangements to be embedded at all levels Assist in managing risks effectively through application of risk management process at varying levels within specific contexts of the organization Ensure risk information is adequately reported to the management Ensure risk based decision making and accountability The key to success Effectiveness of framework
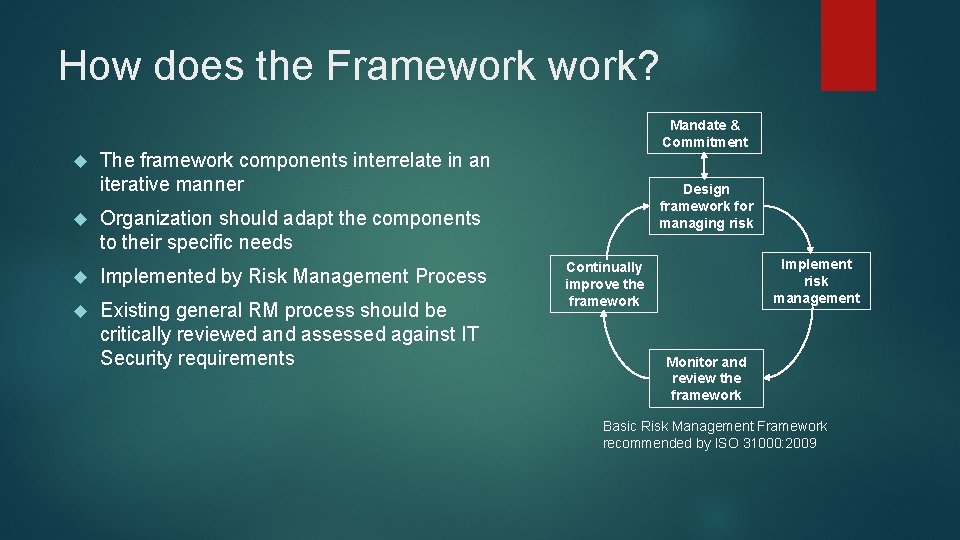
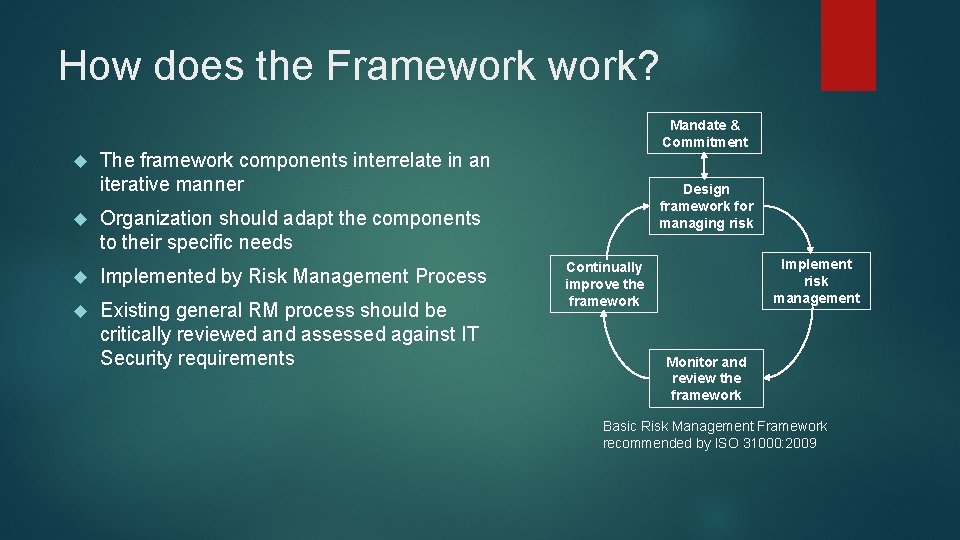
How does the Framework? Mandate & Commitment The framework components interrelate in an iterative manner Organization should adapt the components to their specific needs Implemented by Risk Management Process Existing general RM process should be critically reviewed and assessed against IT Security requirements Design framework for managing risk Implement risk management Continually improve the framework Monitor and review the framework Basic Risk Management Framework recommended by ISO 31000: 2009
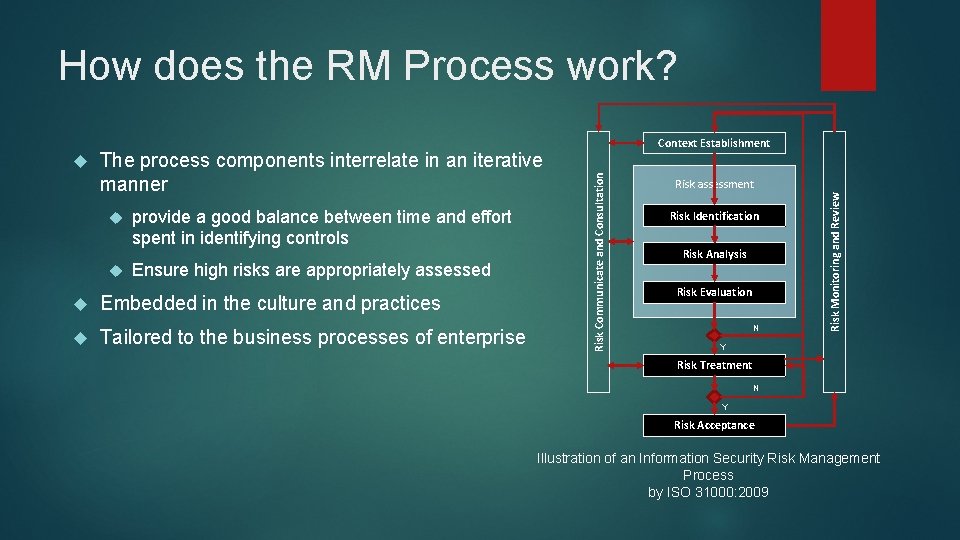
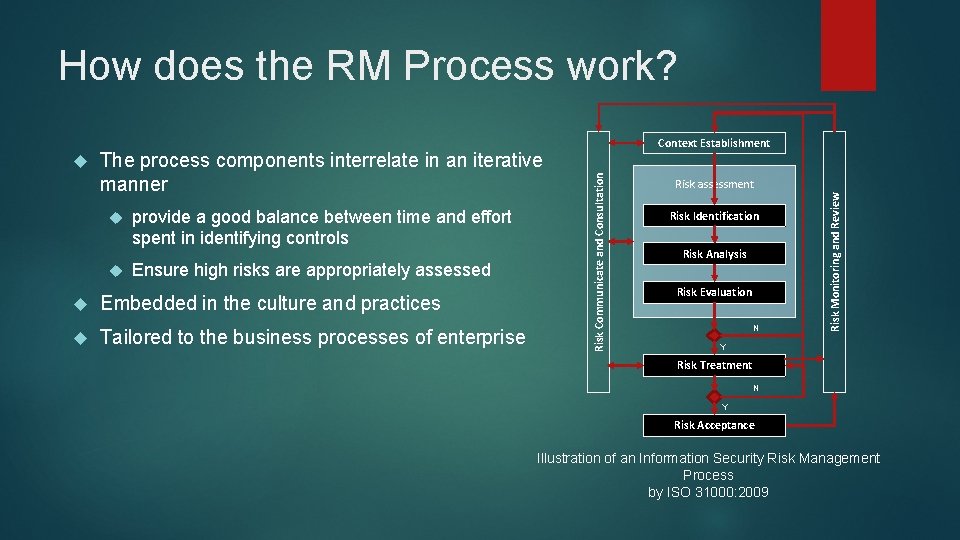
How does the RM Process work? provide a good balance between time and effort spent in identifying controls Ensure high risks are appropriately assessed Embedded in the culture and practices Tailored to the business processes of enterprise Risk assessment Risk Identification Risk Analysis Risk Evaluation N Risk Monitoring and Review The process components interrelate in an iterative manner Risk Communicate and Consultation Context Establishment Y Risk Treatment N Y Risk Acceptance Illustration of an Information Security Risk Management Process by ISO 31000: 2009
Why always iterative approach? A systematic approach is necessary for Infor Sec Risk Management is a continual process Iterative approach provides good balance between time and effort Information security protection efforts will vary over time Why again? Ultimately, CHANGES! from internal and external parties Including but not limited to technology changes and enemy changes
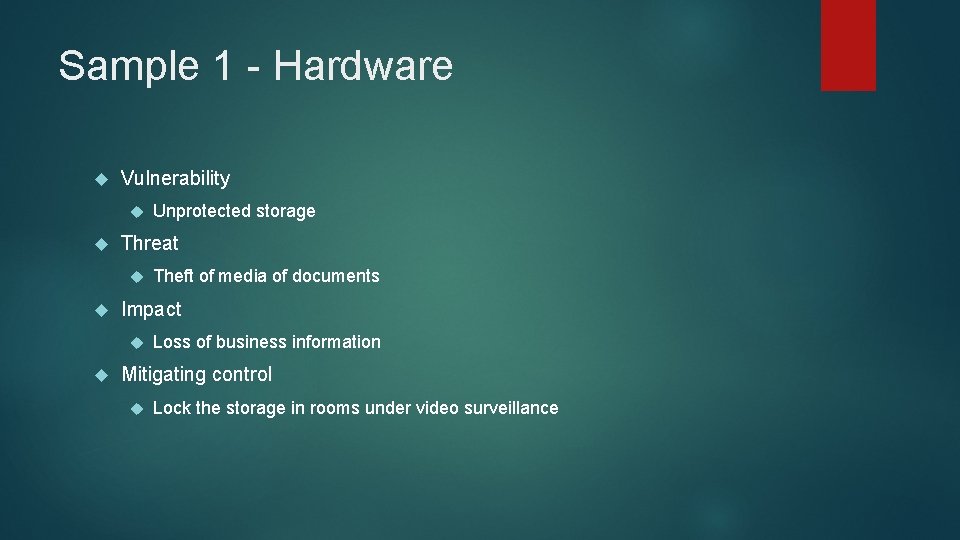
Sample 1 - Hardware Vulnerability Threat Theft of media of documents Impact Unprotected storage Loss of business information Mitigating control Lock the storage in rooms under video surveillance
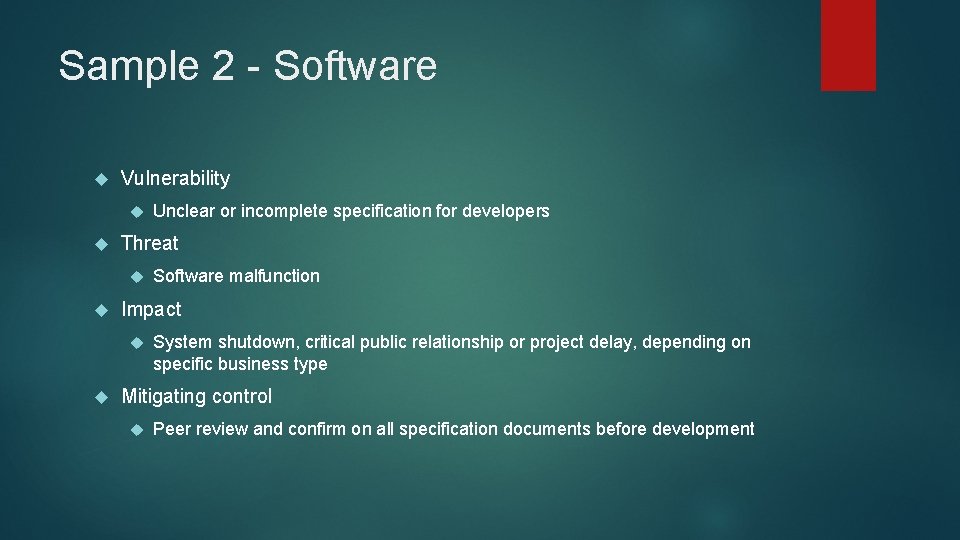
Sample 2 - Software Vulnerability Threat Software malfunction Impact Unclear or incomplete specification for developers System shutdown, critical public relationship or project delay, depending on specific business type Mitigating control Peer review and confirm on all specification documents before development
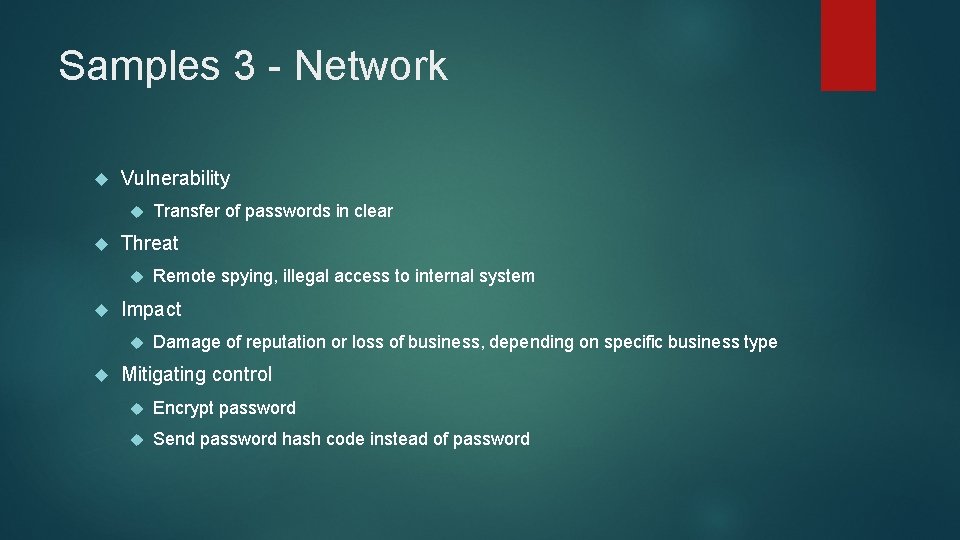
Samples 3 - Network Vulnerability Threat Remote spying, illegal access to internal system Impact Transfer of passwords in clear Damage of reputation or loss of business, depending on specific business type Mitigating control Encrypt password Send password hash code instead of password