Information Security Principles of Data Security Data Inventory
- Slides: 57
Information Security Principles of Data Security Data Inventory Authentication Audit Trail Additional Audit Functions
Acknowledgments Material is sourced from: CISA® Review Manual 2009, © 2008, ISACA. All rights reserved. Used by permission. CISM® Review Manual 2009, © 2008, ISACA. All rights reserved. Used by permission. CISA ® Certified Information Systems Auditor All-in-One Exam Guide, Peter H Gregory, Mc. Graw-Hill Author: Susan J Lincke, Ph. D Univ. of Wisconsin-Parkside Reviewers/Contributors: Megan Reid Funded by National Science Foundation (NSF) Course, Curriculum and Laboratory Improvement (CCLI) grant 0837574: Information Security: Audit, Case Study, and Service Learning. Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author(s) and/or source(s) and do not necessarily reflect the views of the National Science Foundation.
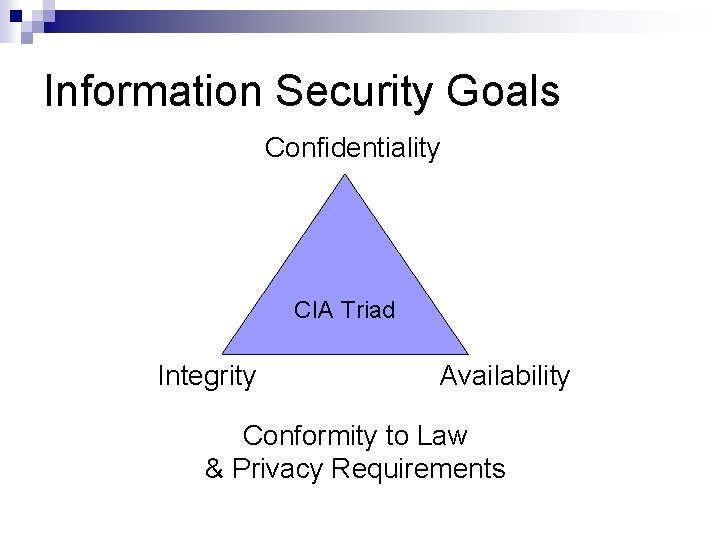
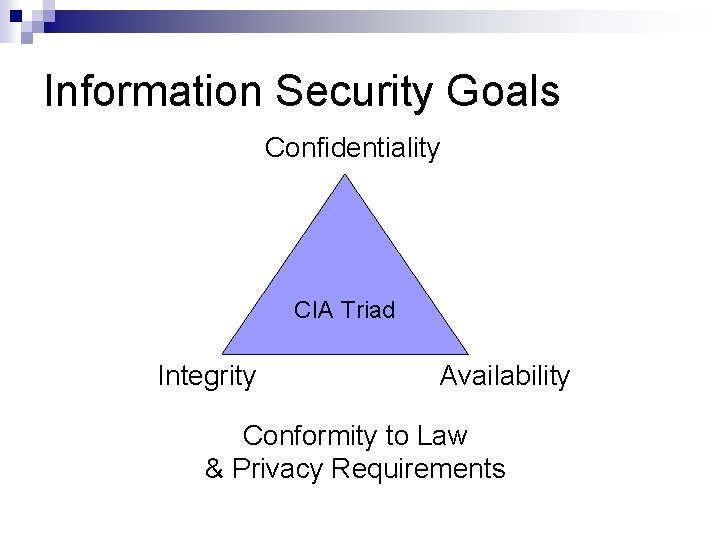
Information Security Goals Confidentiality CIA Triad Integrity Availability Conformity to Law & Privacy Requirements
Information Security Principles Need-to-know: Persons should have ability to access data sufficient to perform primary job and no more Least Privilege: Persons should have ability to do tasks sufficient to perform primary job and no more Segregation of Duties: Ensure that no person can assume two roles: Origination, Authorization, Distribution, Verification Privacy: Personal/private info is retained only when a true business need exists: Privacy is a liability ¨ Retain records for short time Personnel office should change permissions as jobs change
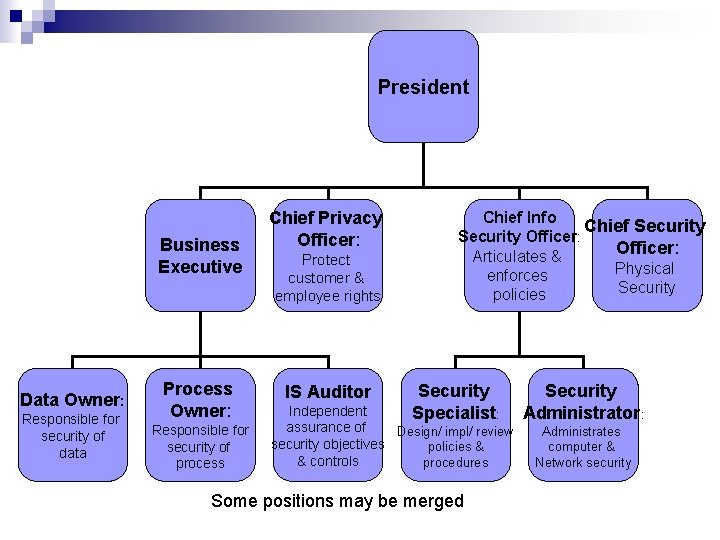
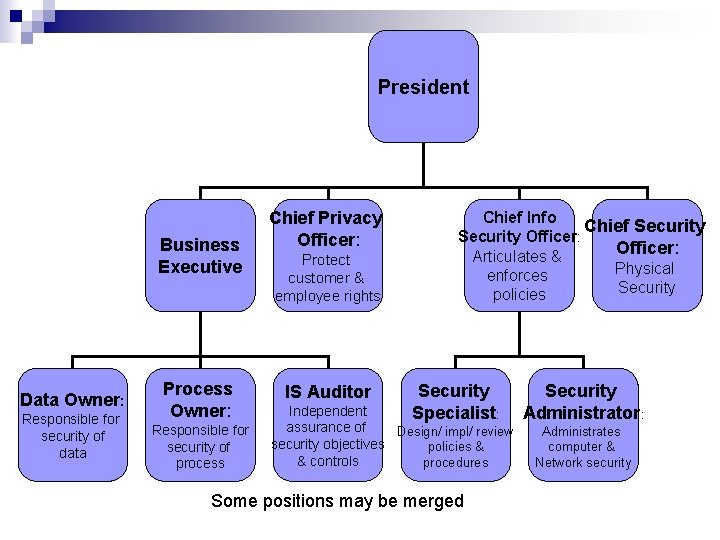
President Business Executive Data Owner: Responsible for security of data Process Owner: Responsible for security of process Chief Privacy Officer: Protect customer & employee rights IS Auditor Chief Info Chief Security Officer: Articulates & Physical enforces Security policies Security Specialist: Independent assurance of Design/ impl/ review security objectives policies & & controls procedures Some positions may be merged Security Administrator: Administrates computer & Network security
Information Owner or Data Owner Is responsible for the data within business (mgr/director - not IS staff) Determines who can have access to data and may grant permissions directly OR Gives written permission for access directly to security administrator, to prevent mishandling or alteration Periodically reviews authorization to restrict authorization creep
Other Positions Data Custodian IS employee who safeguards the data May be Systems Analyst or System Administrator Security Administrator Allocates access to employees based on written documentation Monitors access to terminals and applications ¨ Monitors invalid login attempts Prepares security reports
Criticality Classification Critical $$$$: Cannot be performed manually. Tolerance to interruption is very low Vital $$: Can be performed manually for very short time Sensitive $: Can be performed manually for a period of time, but may cost more in staff Nonsensitive ¢: Can be performed manually for an extended period of time with little additional cost and minimal recovery effort
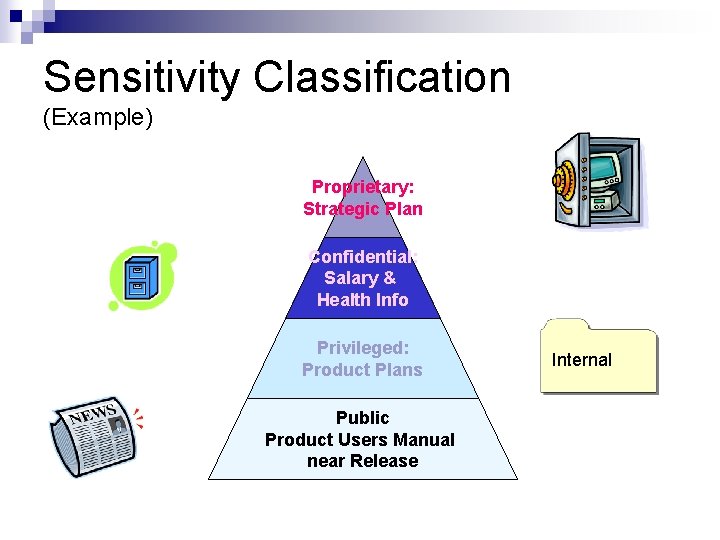
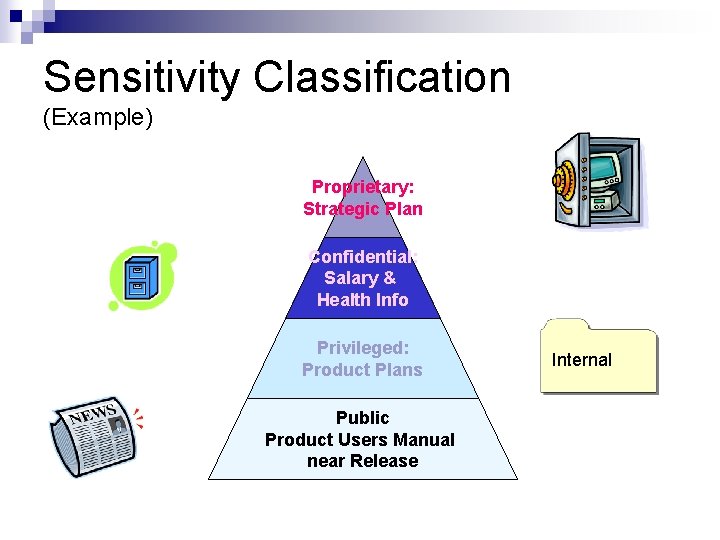
Sensitivity Classification (Example) Proprietary: Strategic Plan Confidential: Salary & Health Info Privileged: Product Plans Public Product Users Manual near Release Internal
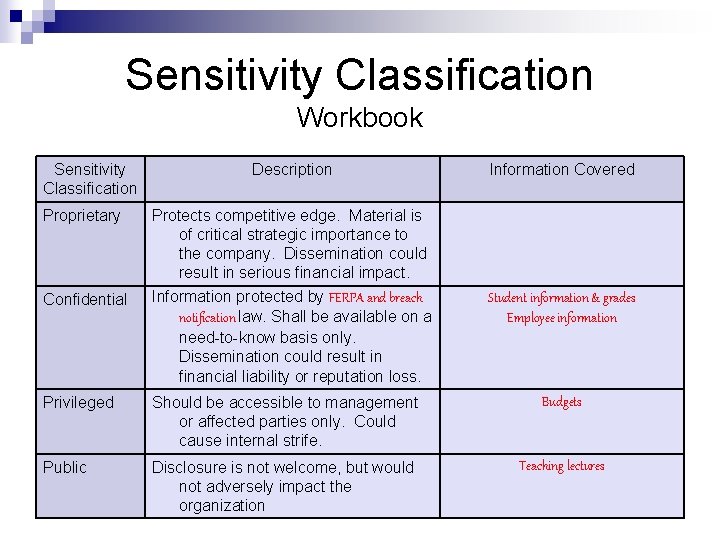
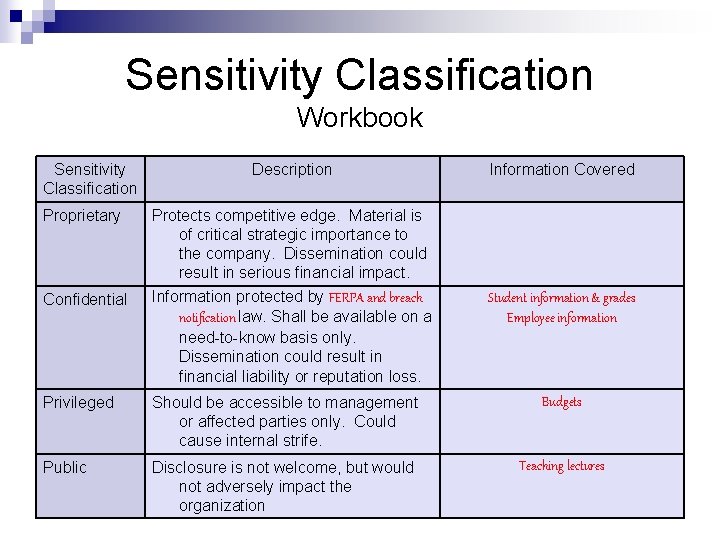
Sensitivity Classification Workbook Sensitivity Classification Proprietary Confidential Description Protects competitive edge. Material is of critical strategic importance to the company. Dissemination could result in serious financial impact. Information protected by FERPA and breach notification law. Shall be available on a need-to-know basis only. Dissemination could result in financial liability or reputation loss. Information Covered Student information & grades Employee information Privileged Should be accessible to management or affected parties only. Could cause internal strife. Budgets Public Disclosure is not welcome, but would not adversely impact the organization Teaching lectures
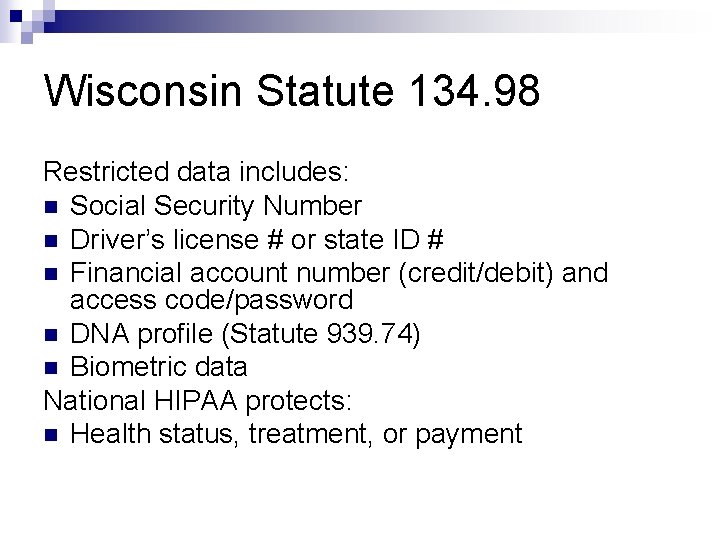
Wisconsin Statute 134. 98 Restricted data includes: Social Security Number Driver’s license # or state ID # Financial account number (credit/debit) and access code/password DNA profile (Statute 939. 74) Biometric data National HIPAA protects: Health status, treatment, or payment
Data Classification How do we mark classified information? How do we determine which data should be classified to which class? How do we store, transport, handle, archive classified information? How do we dispose of classified data? What does the law say about handling this information? Who has authority to determine who gets access, and what approvals are needed for access?
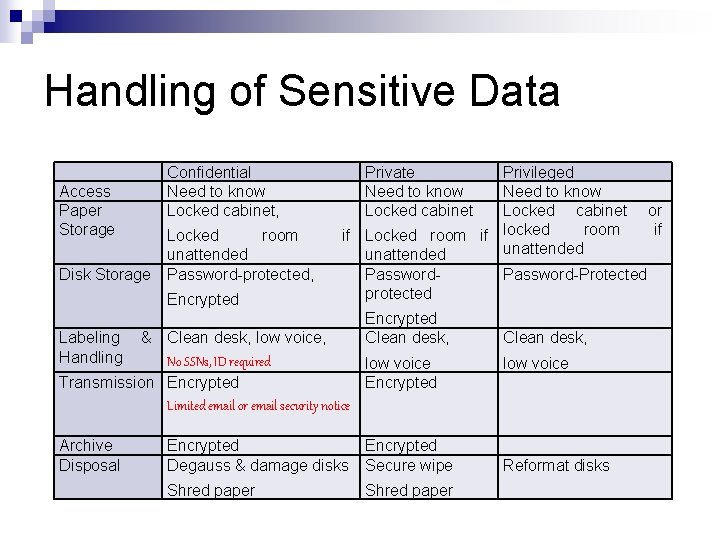
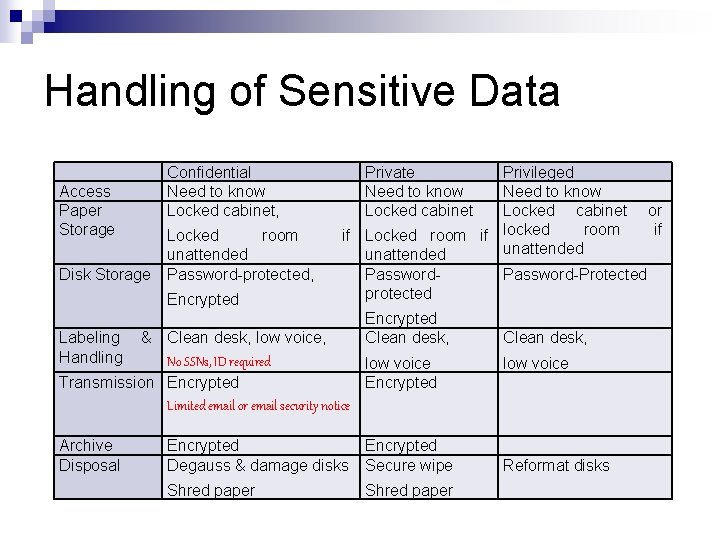
Handling of Sensitive Data Access Paper Storage Disk Storage Confidential Need to know Locked cabinet, Locked room unattended Password-protected, Encrypted Private Need to know Locked cabinet Privileged Need to know Locked cabinet or room if if Locked room if locked unattended Password-Protected protected Encrypted Clean desk, Labeling Handling & Clean desk, low voice, No SSNs, ID required low voice Transmission Encrypted Limited email or email security notice Archive Disposal Encrypted Degauss & damage disks Encrypted Secure wipe Shred paper Clean desk, low voice Reformat disks
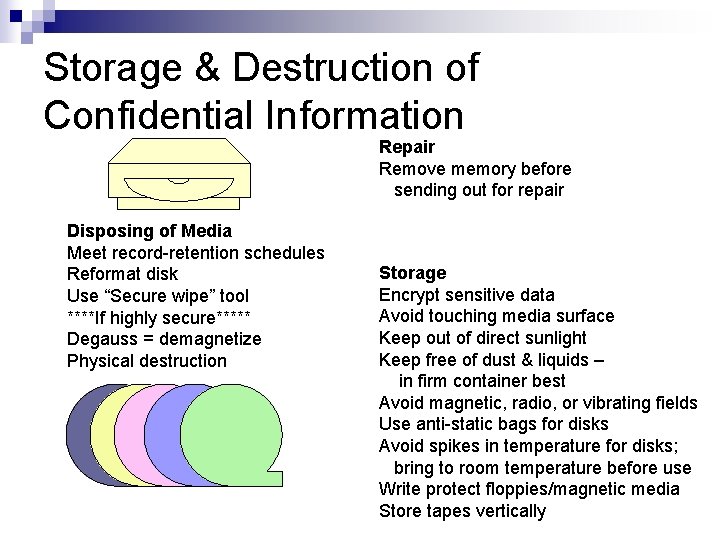
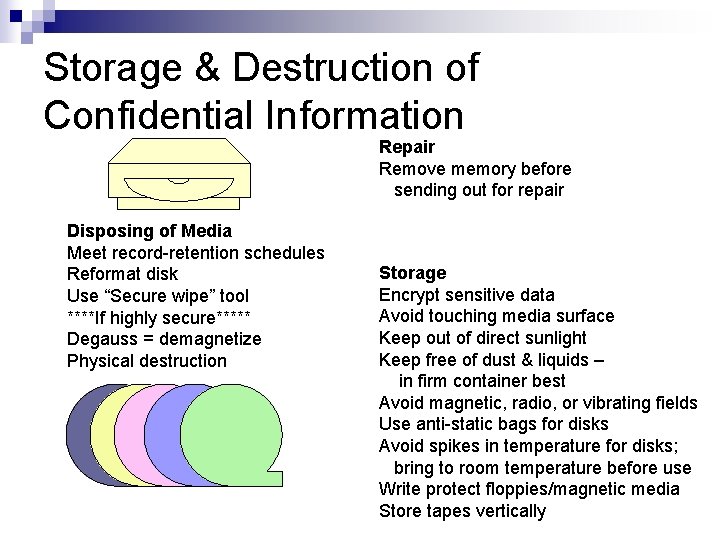
Storage & Destruction of Confidential Information Repair Remove memory before sending out for repair Disposing of Media Meet record-retention schedules Reformat disk Use “Secure wipe” tool ****If highly secure***** Degauss = demagnetize Physical destruction Storage Encrypt sensitive data Avoid touching media surface Keep out of direct sunlight Keep free of dust & liquids – in firm container best Avoid magnetic, radio, or vibrating fields Use anti-static bags for disks Avoid spikes in temperature for disks; bring to room temperature before use Write protect floppies/magnetic media Store tapes vertically
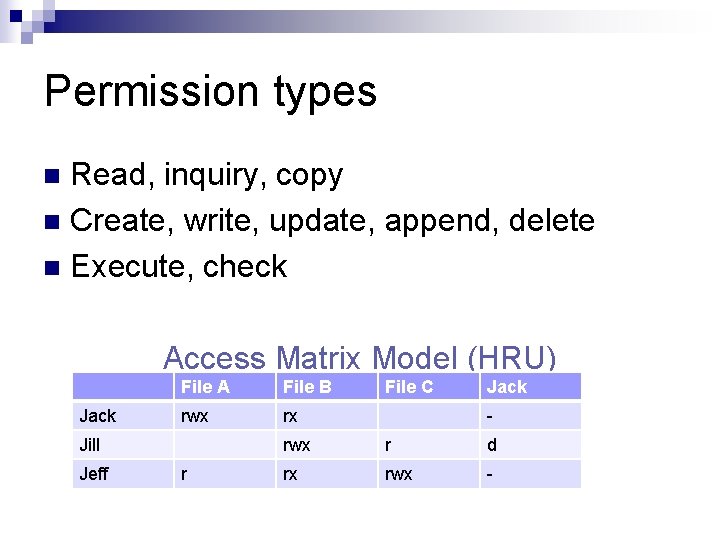
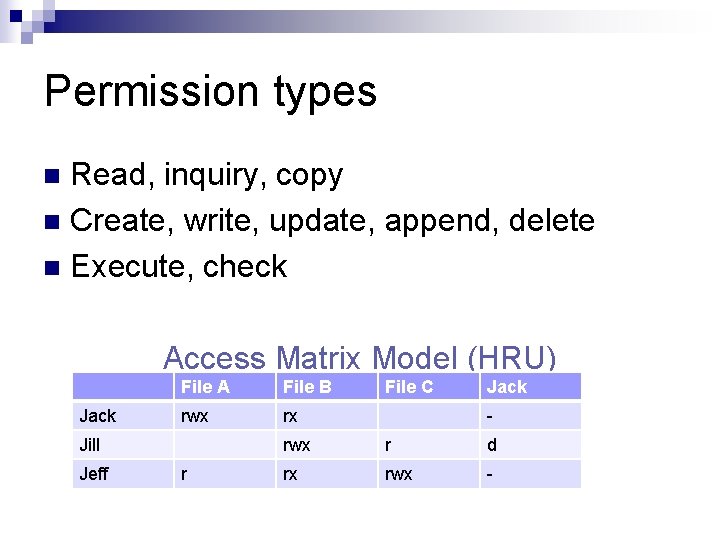
Permission types Read, inquiry, copy Create, write, update, append, delete Execute, check Access Matrix Model (HRU) Jack File A File B rwx rx Jill Jeff r File C Jack - rwx r d rx rwx -
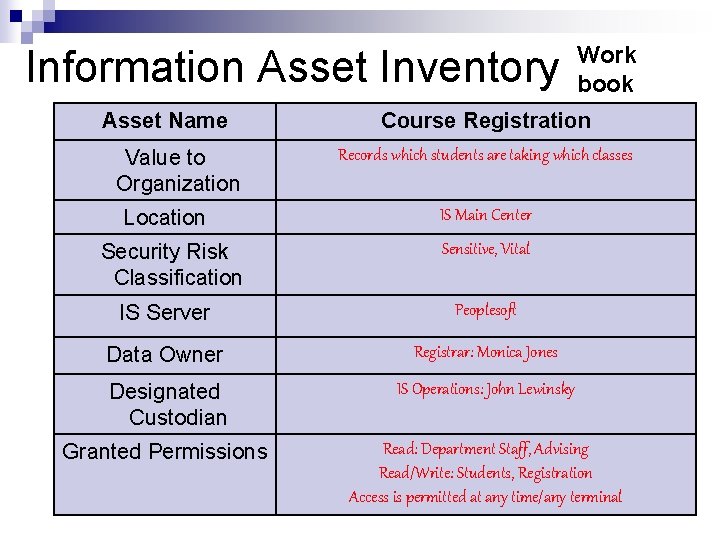
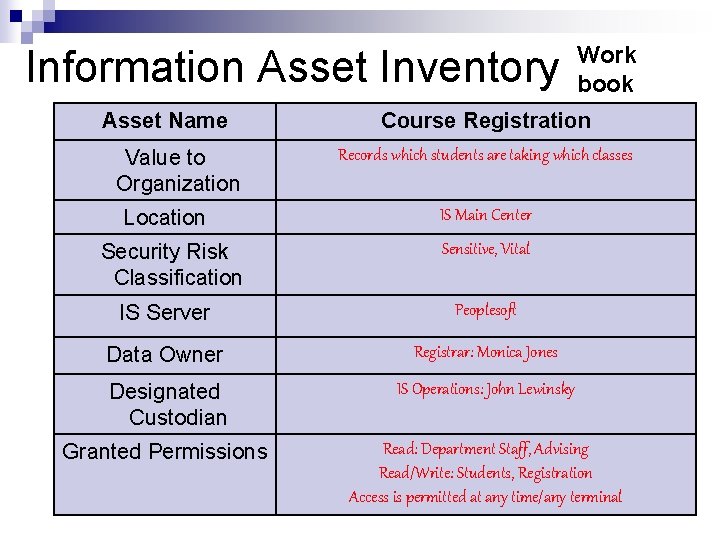
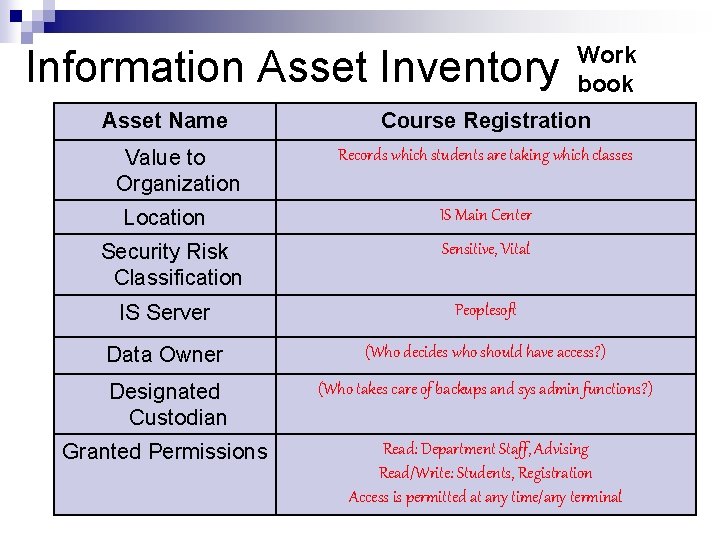
Work book Information Asset Inventory Asset Name Value to Organization Location Security Risk Classification Course Registration Records which students are taking which classes IS Main Center Sensitive, Vital IS Server Peoplesoft Data Owner Registrar: Monica Jones Designated Custodian IS Operations: John Lewinsky Granted Permissions Read: Department Staff, Advising Read/Write: Students, Registration Access is permitted at any time/any terminal
Question The person responsible for deciding who should have access to a data file is: 1. Data custodian 2. Data owner 3. Security administrator 4. Security manager
Question Least Privilege dictates that: 1. 2. 3. 4. Persons should have the ability to do tasks sufficient to perform their primary job and no more Access rights and permissions shall be commensurate with a person’s position in the corporation: i. e. , lower layers have fewer rights Computer users should never have administrator passwords Persons should have access permissions only for their security level: Confidential, Private or Sensitive
Question A concern with personal or private information is that: 1. Data is not kept longer than absolutely necessary 2. Data encryption makes the retention of personal information safe 3. Private information on disk should never be taken off-site 4. Personal data is always labeled and handled as critical or vital to the organization
Question The person responsible for restricting and monitoring permissions is the: 1. Data custodian 2. Data owner 3. Security administrator 4. Security manager
Authentication Path Access Login/Password Biometrics Remote Access
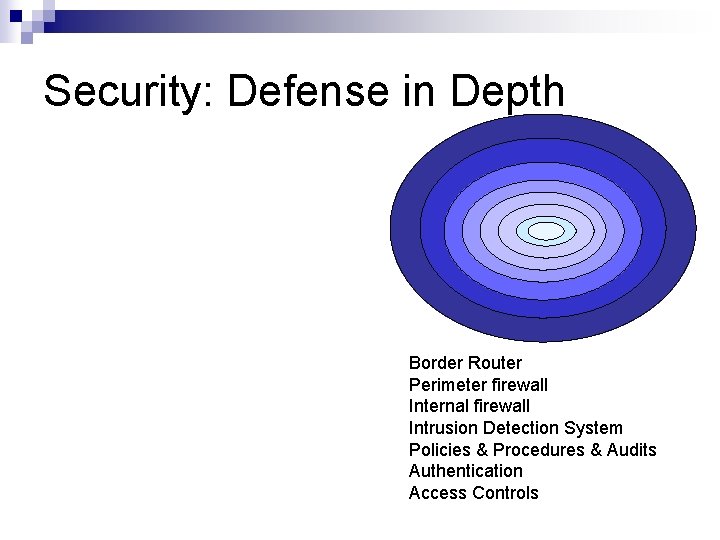
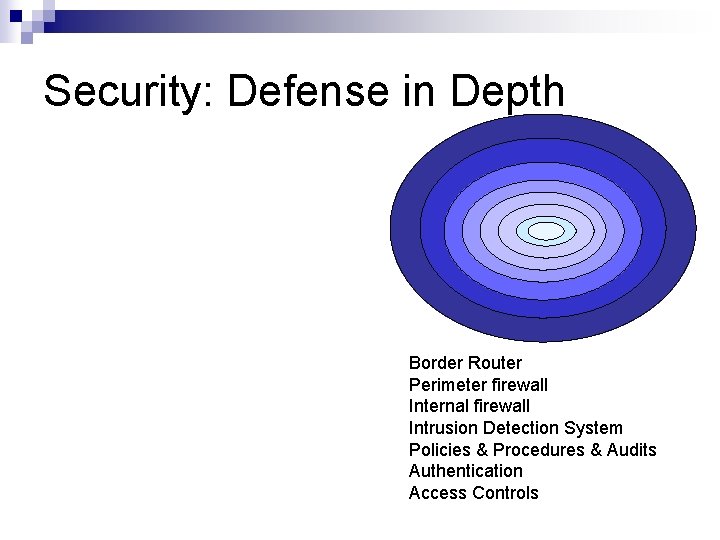
Security: Defense in Depth Border Router Perimeter firewall Internal firewall Intrusion Detection System Policies & Procedures & Audits Authentication Access Controls
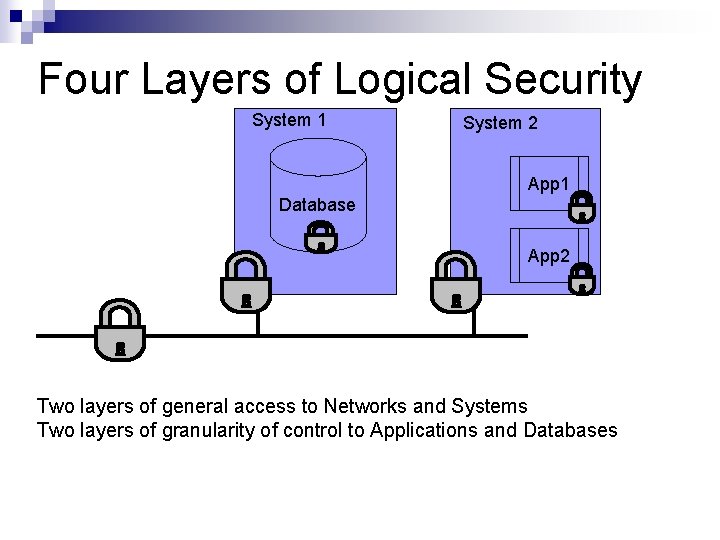
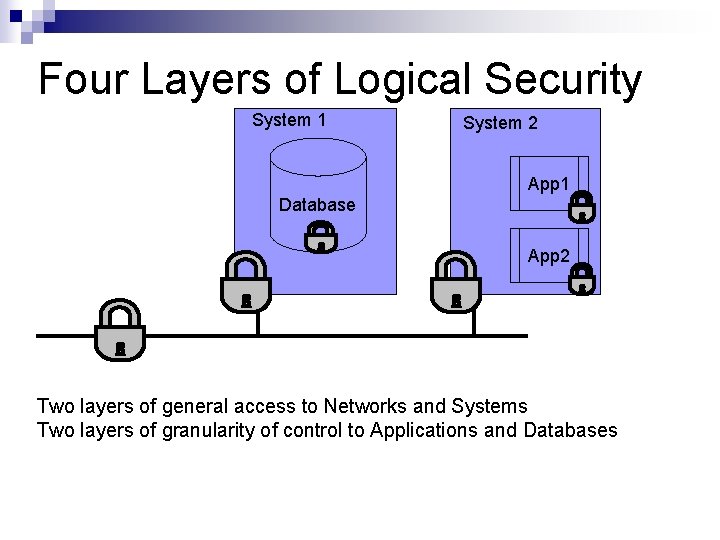
Four Layers of Logical Security System 1 System 2 App 1 Database App 2 Two layers of general access to Networks and Systems Two layers of granularity of control to Applications and Databases
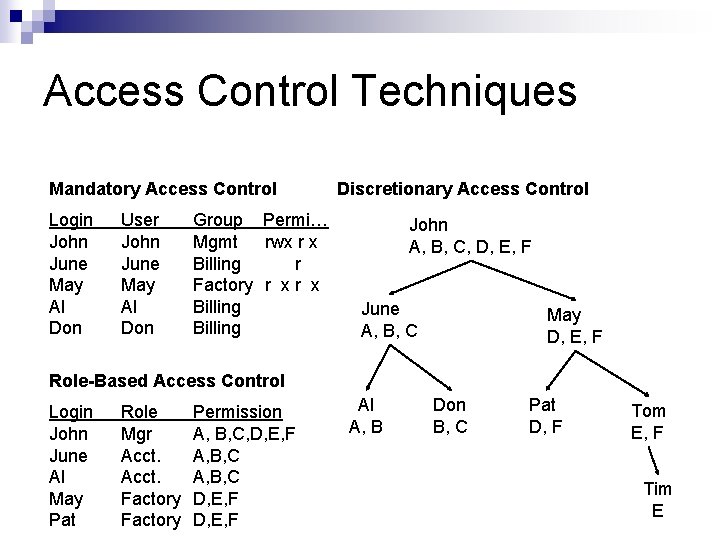
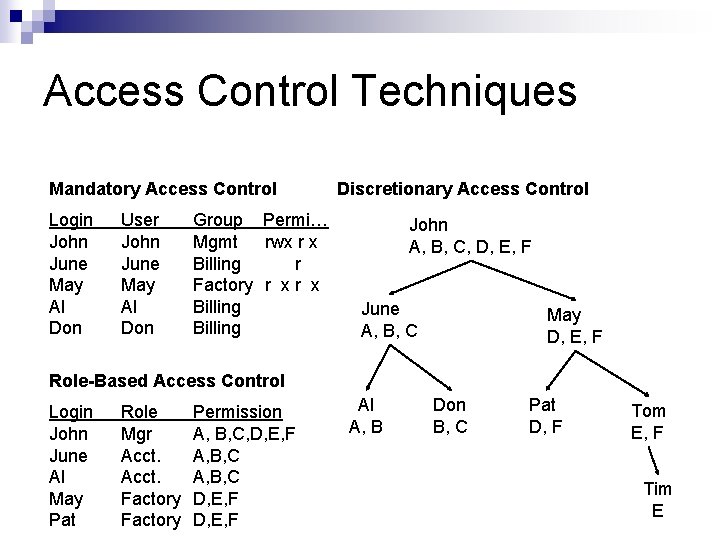
Access Control Techniques Mandatory Access Control Login John June May Al Don User John June May Al Don Group Permi… Mgmt rwx r x Billing r Factory r x Billing Discretionary Access Control John A, B, C, D, E, F June A, B, C May D, E, F Role-Based Access Control Login John June Al May Pat Role Mgr Acct. Factory Permission A, B, C, D, E, F A, B, C D, E, F Al A, B Don B, C Pat D, F Tom E, F Tim E
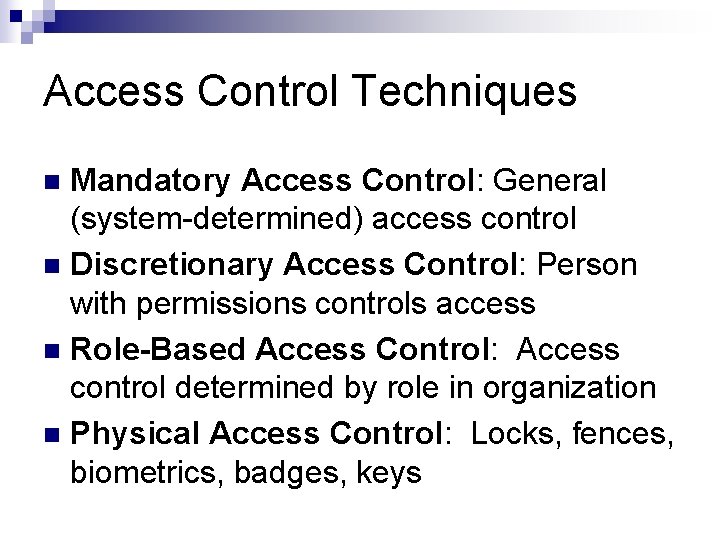
Access Control Techniques Mandatory Access Control: General (system-determined) access control Discretionary Access Control: Person with permissions controls access Role-Based Access Control: Access control determined by role in organization Physical Access Control: Locks, fences, biometrics, badges, keys
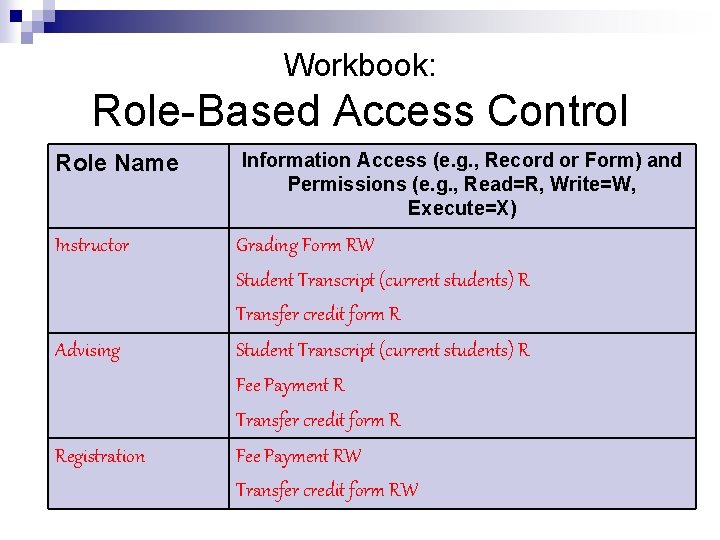
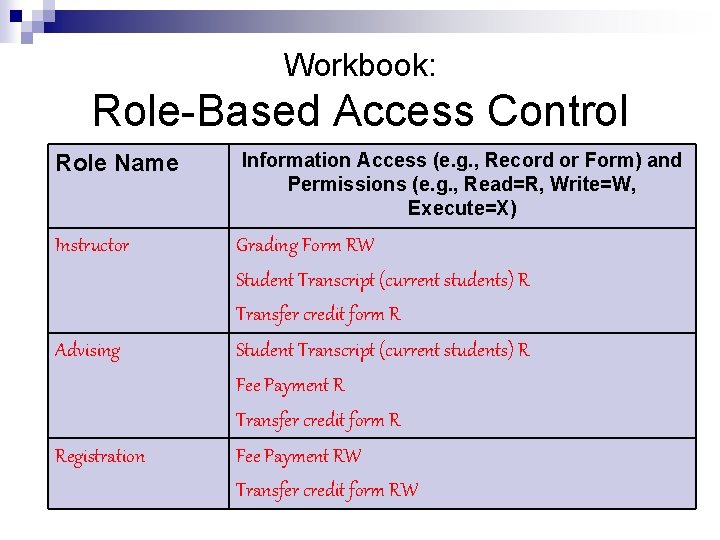
Workbook: Role-Based Access Control Role Name Information Access (e. g. , Record or Form) and Permissions (e. g. , Read=R, Write=W, Execute=X) Instructor Grading Form RW Student Transcript (current students) R Transfer credit form R Advising Student Transcript (current students) R Fee Payment R Transfer credit form R Registration Fee Payment RW Transfer credit form RW
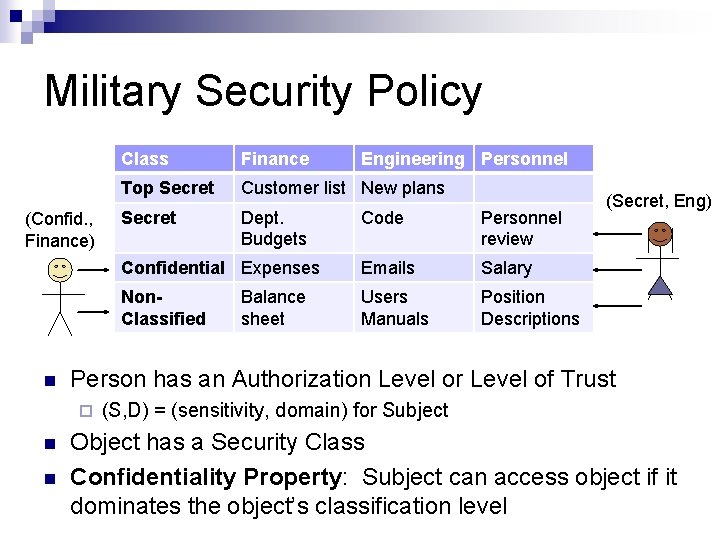
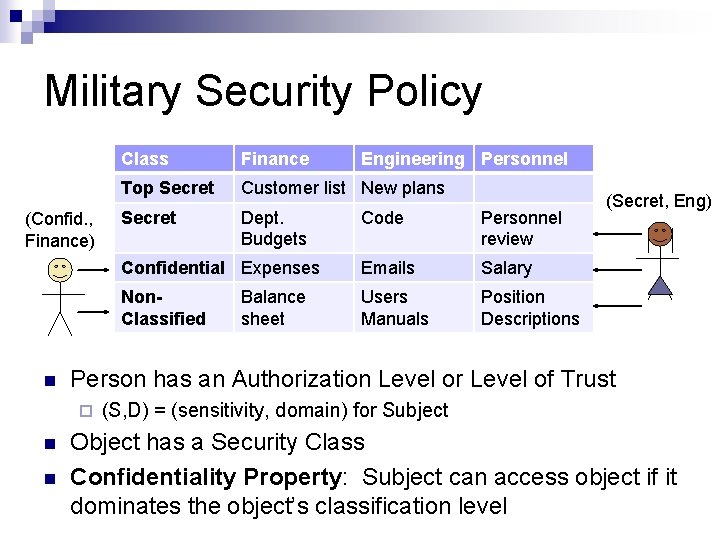
Military Security Policy (Confid. , Finance) Finance Engineering Personnel Top Secret Customer list New plans Secret Dept. Budgets Code Personnel review Confidential Expenses Emails Salary Non. Classified Users Manuals Position Descriptions Balance sheet (Secret, Eng) Person has an Authorization Level or Level of Trust ¨ Class (S, D) = (sensitivity, domain) for Subject Object has a Security Class Confidentiality Property: Subject can access object if it dominates the object’s classification level
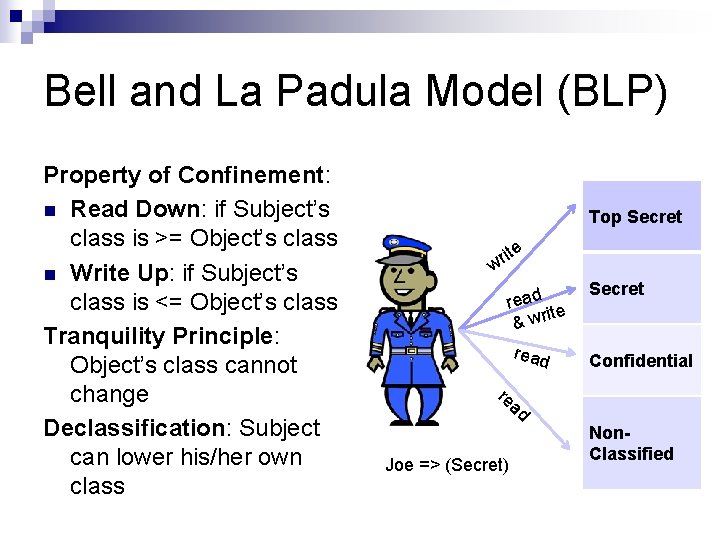
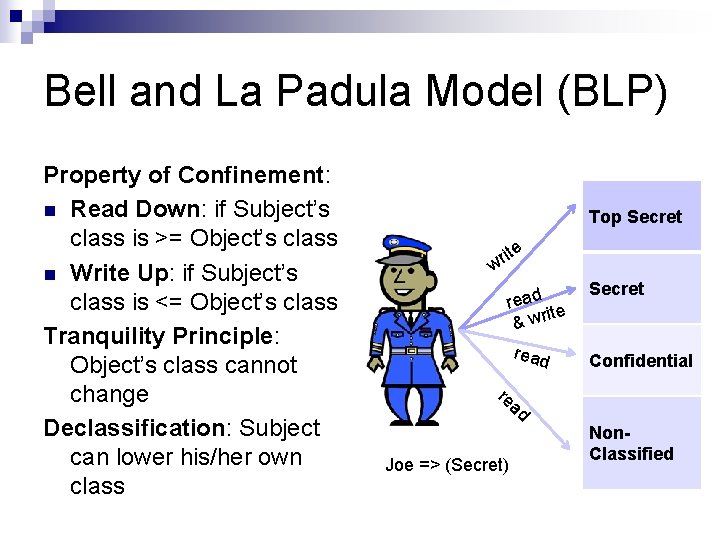
Bell and La Padula Model (BLP) Property of Confinement: Read Down: if Subject’s class is >= Object’s class Write Up: if Subject’s class is <= Object’s class Tranquility Principle: Object’s class cannot change Declassification: Subject can lower his/her own class Top Secret ite r w read ite & wr Secret read Confidential re ad Joe => (Secret) Non. Classified
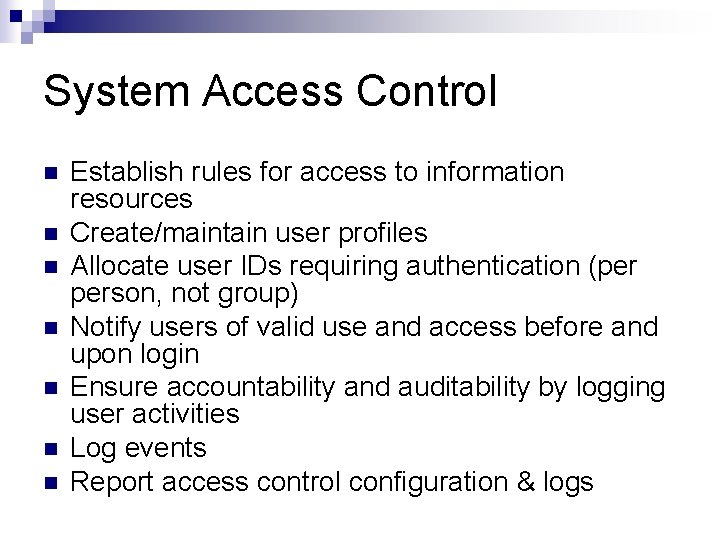
System Access Control Establish rules for access to information resources Create/maintain user profiles Allocate user IDs requiring authentication (per person, not group) Notify users of valid use and access before and upon login Ensure accountability and auditability by logging user activities Log events Report access control configuration & logs
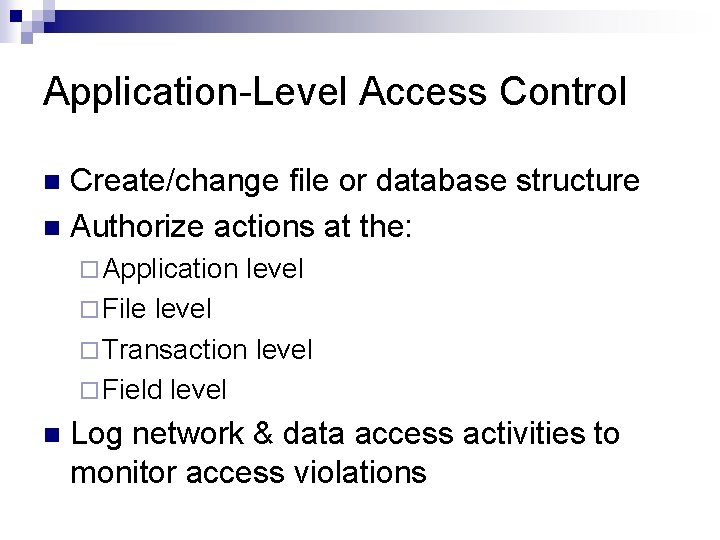
Application-Level Access Control Create/change file or database structure Authorize actions at the: ¨ Application level ¨ File level ¨ Transaction level ¨ Field level Log network & data access activities to monitor access violations
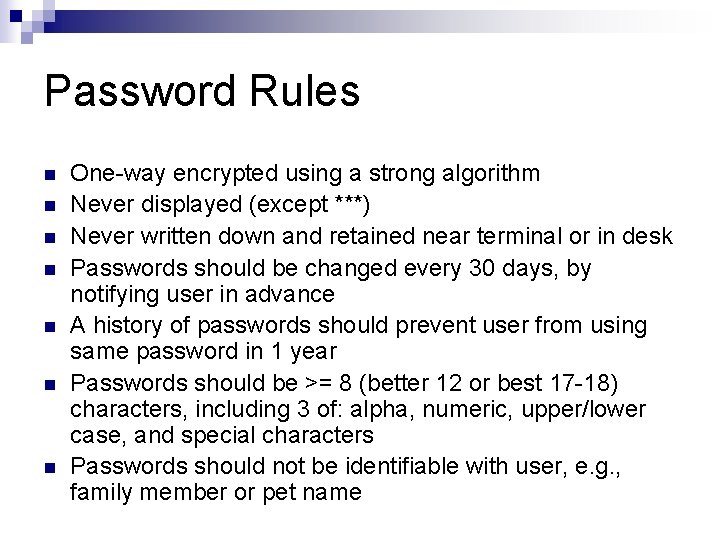
Password Rules One-way encrypted using a strong algorithm Never displayed (except ***) Never written down and retained near terminal or in desk Passwords should be changed every 30 days, by notifying user in advance A history of passwords should prevent user from using same password in 1 year Passwords should be >= 8 (better 12 or best 17 -18) characters, including 3 of: alpha, numeric, upper/lower case, and special characters Passwords should not be identifiable with user, e. g. , family member or pet name
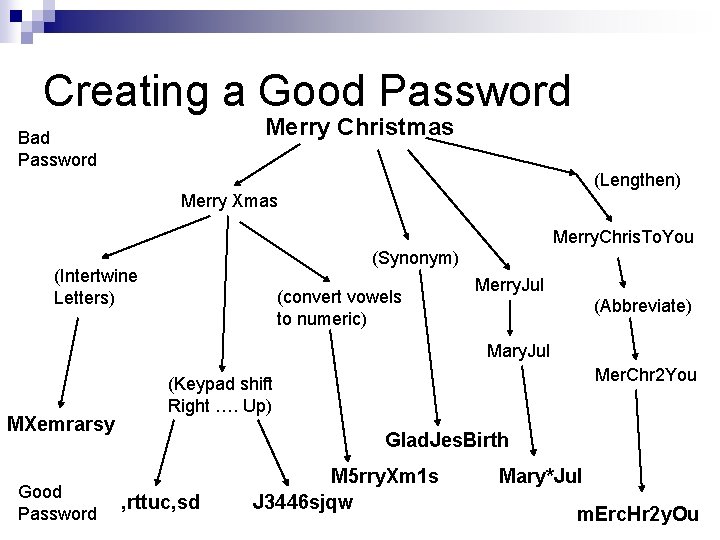
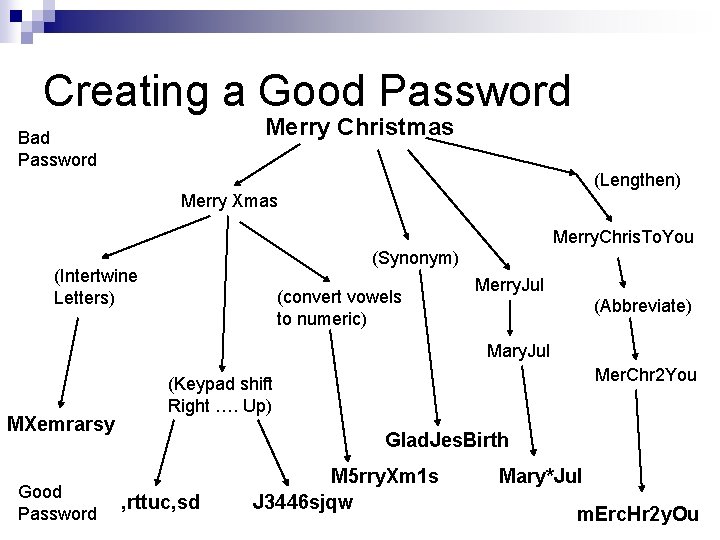
Creating a Good Password Merry Christmas Bad Password (Lengthen) Merry Xmas Merry. Chris. To. You (Synonym) (Intertwine Letters) (convert vowels to numeric) Merry. Jul (Abbreviate) Mary. Jul MXemrarsy Good Password Mer. Chr 2 You (Keypad shift Right …. Up) Glad. Jes. Birth , rttuc, sd M 5 rry. Xm 1 s J 3446 sjqw Mary*Jul m. Erc. Hr 2 y. Ou
Admin & Login ID Rules Restrict number of admin accounts Admin password should only be known by one user Local Admin accounts should never be locked out, whereas others are Admin password can be kept in locked cabinet in sealed envelope, where top manager has key Login IDs should follow a confidential internal naming rule Common accounts: Guest, Administrator, Admin should be renamed Session time out should require password re-entry
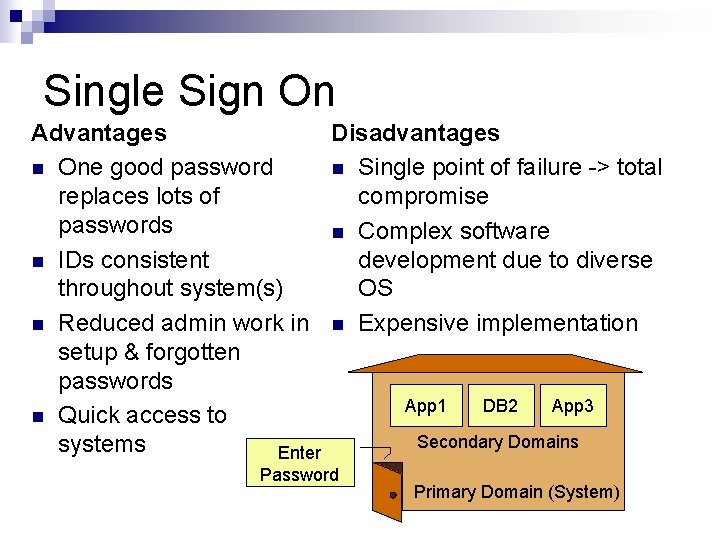
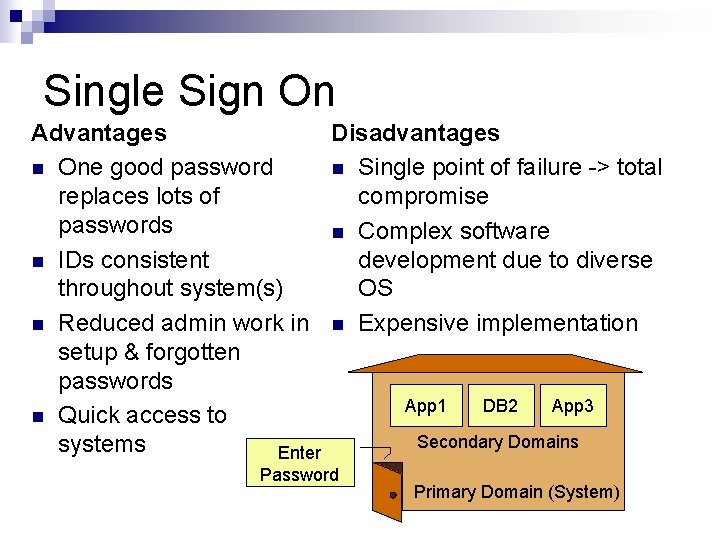
Single Sign On Advantages Disadvantages One good password Single point of failure -> total replaces lots of compromise passwords Complex software IDs consistent development due to diverse throughout system(s) OS Reduced admin work in Expensive implementation setup & forgotten passwords App 1 DB 2 App 3 Quick access to Secondary Domains systems Enter Password Primary Domain (System)
Authentication Combinations Single Factor: Something you know ¨ Login & Password Multifactor Authentication: Using two or more authentication methods. Add: ¨ Two Factor: Add one of: Something you have: Card or ID Something you are or do: Biometric ¨ Three Factor: Uses all three: e. g. , badge, thumb, pass code
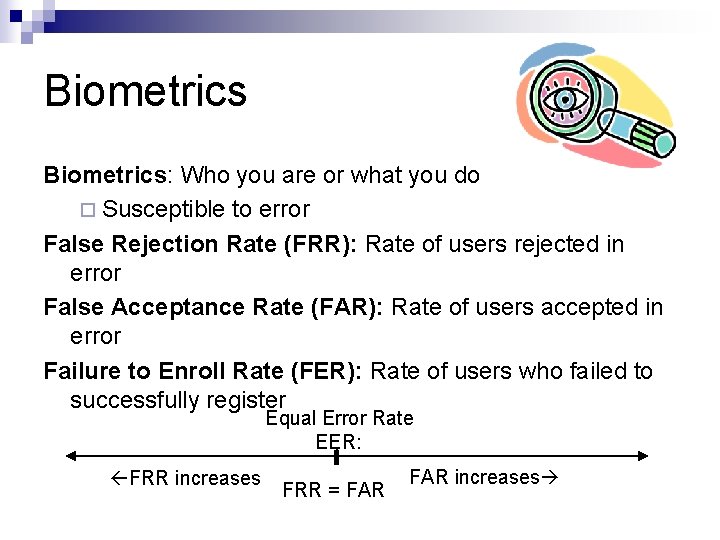
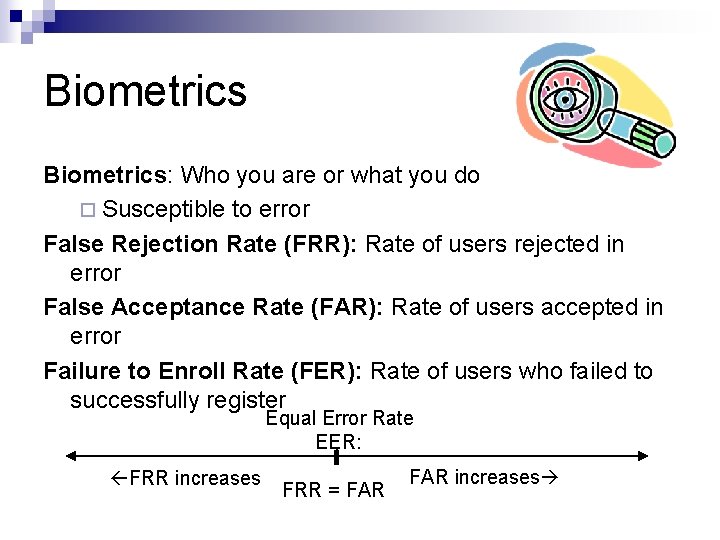
Biometrics: Who you are or what you do ¨ Susceptible to error False Rejection Rate (FRR): Rate of users rejected in error False Acceptance Rate (FAR): Rate of users accepted in error Failure to Enroll Rate (FER): Rate of users who failed to successfully register Equal Error Rate EER: FRR increases FRR = FAR increases
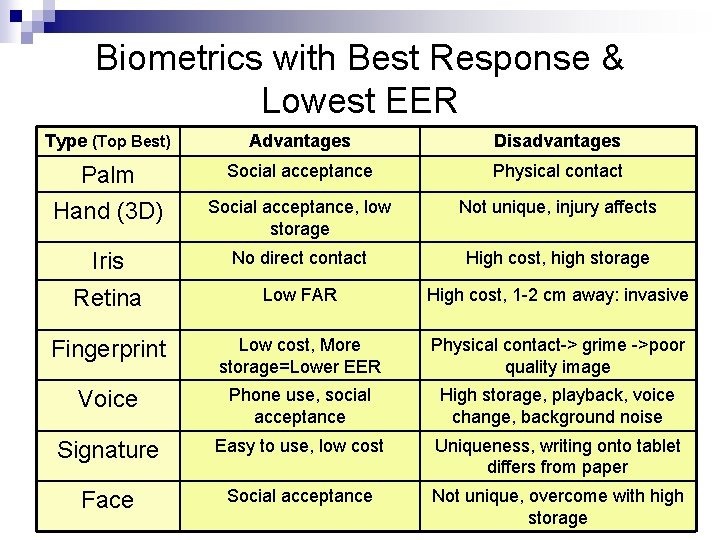
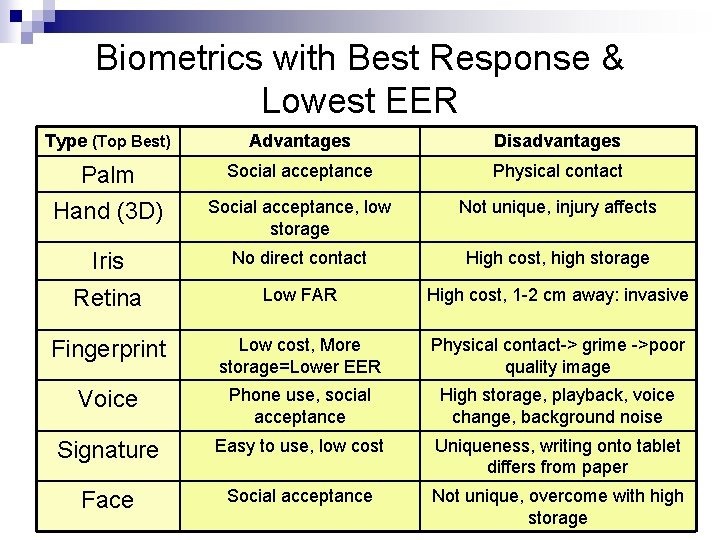
Biometrics with Best Response & Lowest EER Type (Top Best) Advantages Disadvantages Palm Hand (3 D) Social acceptance Physical contact Social acceptance, low storage Not unique, injury affects Iris No direct contact High cost, high storage Retina Low FAR High cost, 1 -2 cm away: invasive Fingerprint Low cost, More storage=Lower EER Physical contact-> grime ->poor quality image Voice Phone use, social acceptance High storage, playback, voice change, background noise Signature Easy to use, low cost Uniqueness, writing onto tablet differs from paper Face Social acceptance Not unique, overcome with high CISA Review Manual 2009 storage
Question A form of biometrics that is considered invasive by users is: 1. Retina 2. Iris 3. 3 D hand 4. Signature
Question A form of biometrics that is not prone to error is 1. Retina 2. Voice 3. Finger 4. Signature
Question Julie is a Data Owner. She configures 1. 2. 3. 4. permissions in the database to enable users to access the forms she thinks they should be able to access. This technique is known as Bell and La Padula Model Mandatory Access Control Role-Based Access Control Discretionary Access Control
Question John has a security clearance of (Engineering, Confidential). Using Bell and La Padula Model, John can write to: 1. Confidential 2. Top Secret, and Confidential 3. Confidential and Unclassified 4. Unclassified
Data Storage Protection Storage Audit Trail
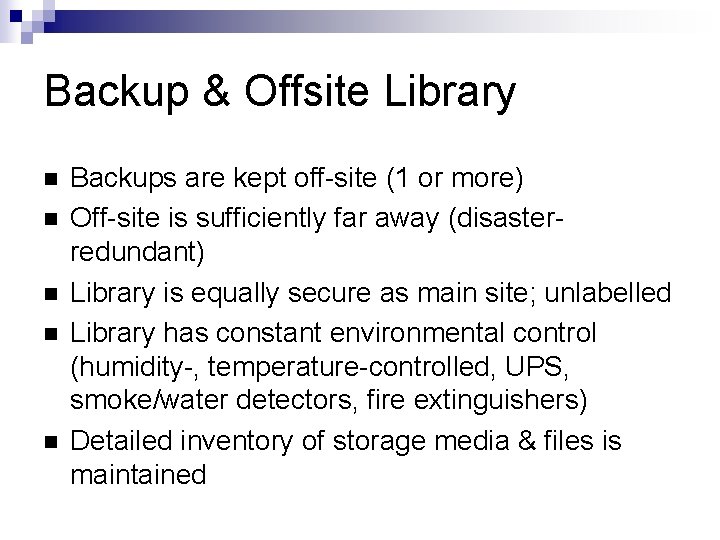
Backup & Offsite Library Backups are kept off-site (1 or more) Off-site is sufficiently far away (disasterredundant) Library is equally secure as main site; unlabelled Library has constant environmental control (humidity-, temperature-controlled, UPS, smoke/water detectors, fire extinguishers) Detailed inventory of storage media & files is maintained
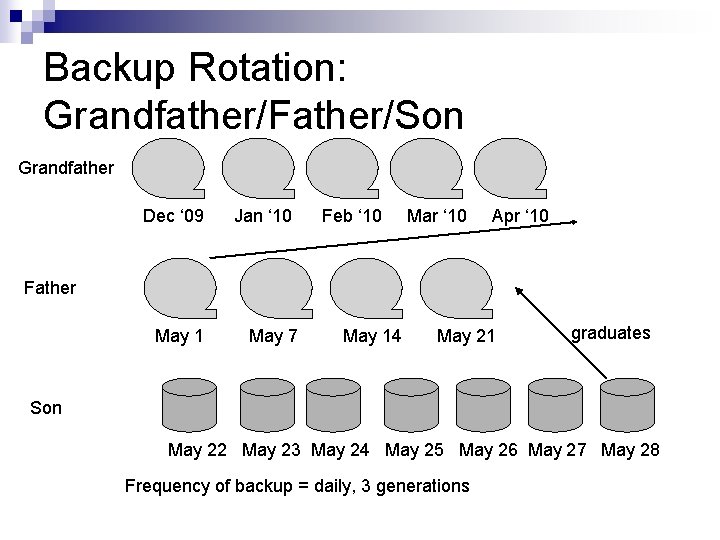
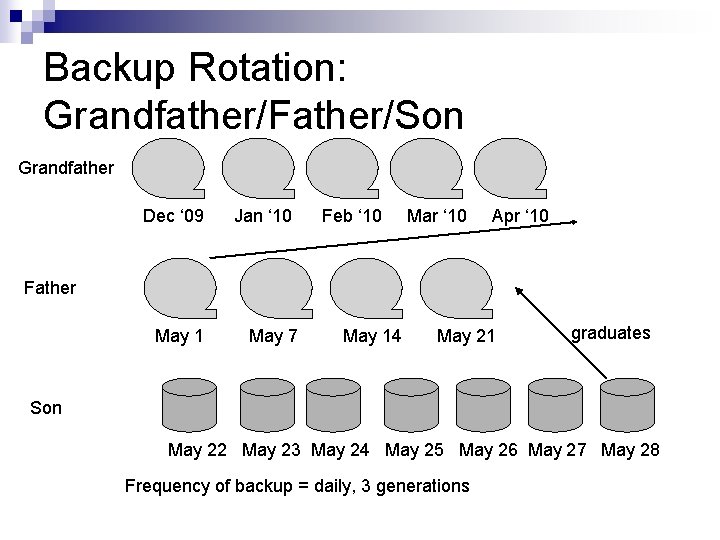
Backup Rotation: Grandfather/Father/Son Grandfather Dec ‘ 09 Jan ‘ 10 Feb ‘ 10 Mar ‘ 10 Apr ‘ 10 Father May 1 May 7 May 14 May 21 graduates Son May 22 May 23 May 24 May 25 May 26 May 27 May 28 Frequency of backup = daily, 3 generations
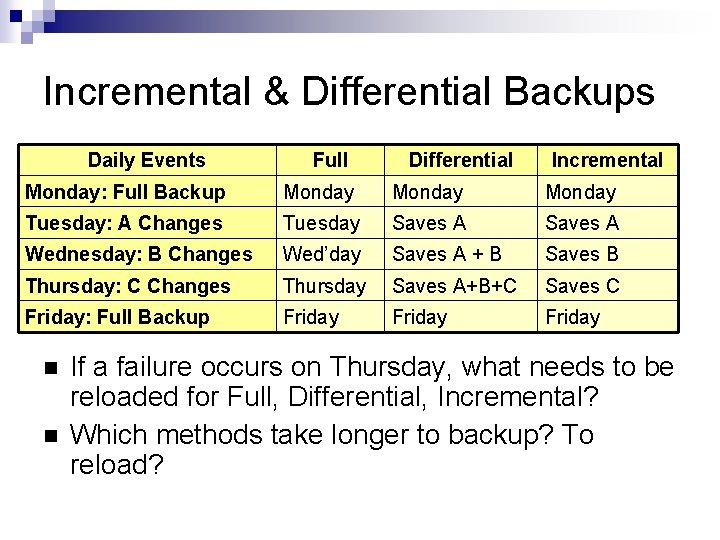
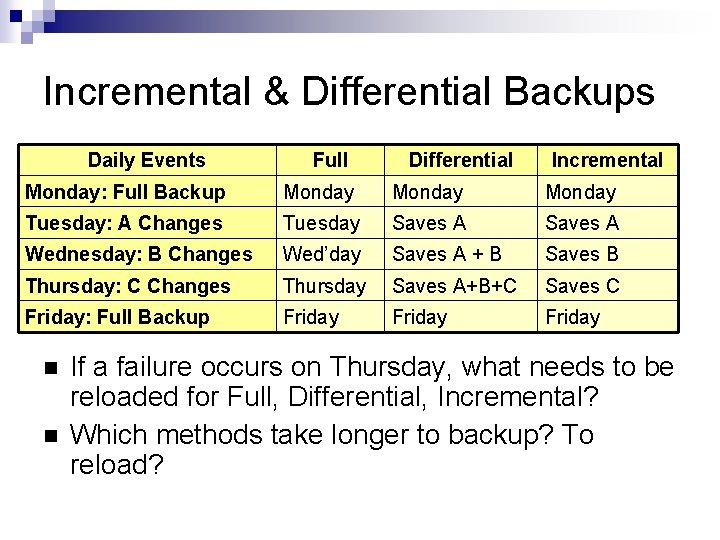
Incremental & Differential Backups Daily Events Full Differential Incremental Monday: Full Backup Monday Tuesday: A Changes Tuesday Saves A Wednesday: B Changes Wed’day Saves A + B Saves B Thursday: C Changes Thursday Saves A+B+C Saves C Friday: Full Backup Friday If a failure occurs on Thursday, what needs to be reloaded for Full, Differential, Incremental? Which methods take longer to backup? To reload?
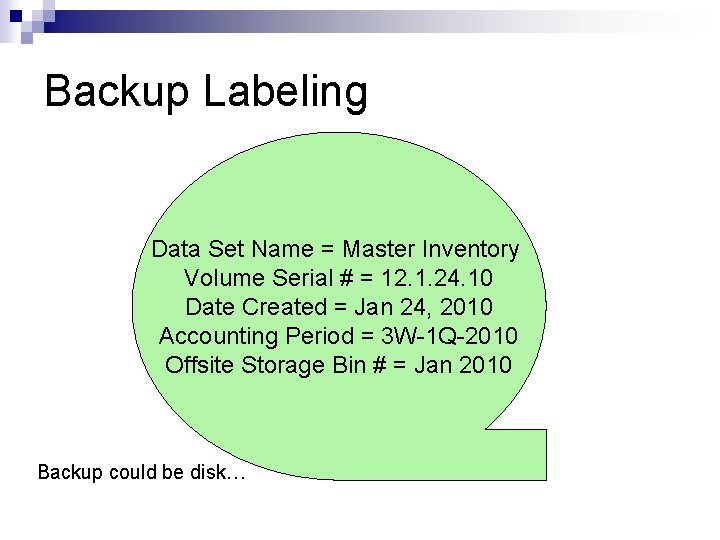
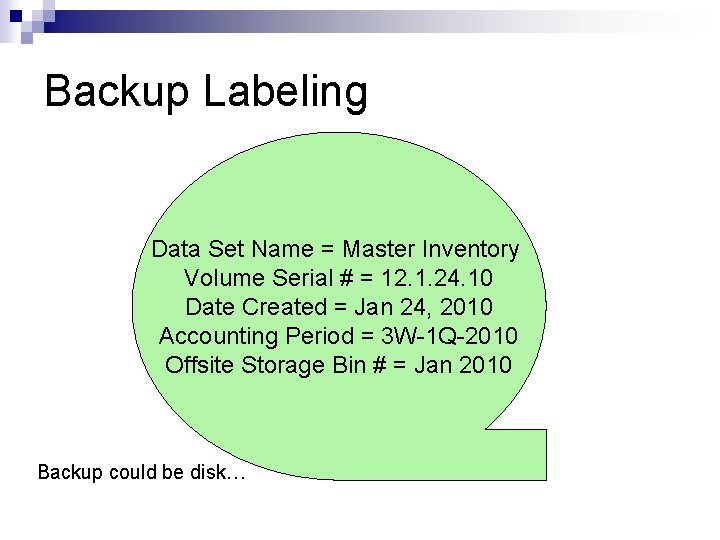
Backup Labeling Data Set Name = Master Inventory Volume Serial # = 12. 1. 24. 10 Date Created = Jan 24, 2010 Accounting Period = 3 W-1 Q-2010 Offsite Storage Bin # = Jan 2010 Backup could be disk…
Audit Trail Audit trail tracks responsibility Who did what when? ¨ Periodic review will help to find excess-authority access, login successes & failures, and track fraud ¨ Attackers often want to change the audit trail (to hide tracks) Audit trail must be hard to change: Write-once devices ¨ Security & systems admins and managers may have READ-only access to log ¨ Audit trail must be sensitive to privacy ¨ Personal information should be encrypted
Audit Trail Tools Audit Reduction: Emphasize important logs - eliminate unimportant logs Trend/ Variance-Detection: Notices changes from normal user or system behavior (e. g. , login during night) Attack/Signature Detection: A sequence of log events may signal an attack (e. g. , 1000 login attempts)
Question Audit trails: 1. Should be modifiable only by security administrators 2. Should be difficult to change (e. g. , write-once) 3. Should only save important logs, using log reduction 4. Should avoid encryption to ensure no loss and quick access
Vocabulary Need-to-know, least privilege, segregation of duties, privacy Data owner, data custodian, security administrator, criticality classification, sensitivity classification Mandatory access control, discretionary access control, physical access control, role-based access control, single sign-on Single factor, two factor, three factor, multifactor FRR, FAR, FER, EER Level of trust, Confidentiality Principle, Declassification, Write-up, Read-down Backup rotation, incremental backup, differential backup Degauss, audit trail, audit reduction
Interactive Crossword Puzzle To get more practice the vocabulary from this section click on the picture below. For a word bank look at the previous slide. Definitions extracted from: All-In-One CISA Exam Guide
Jamie Ramon MD Doctor Chris Ramon RD Dietician Terry Medical Admin Pat Software Consultant HEALTH FIRST CASE STUDY Designing Information Security Sonia Medical Transcriber
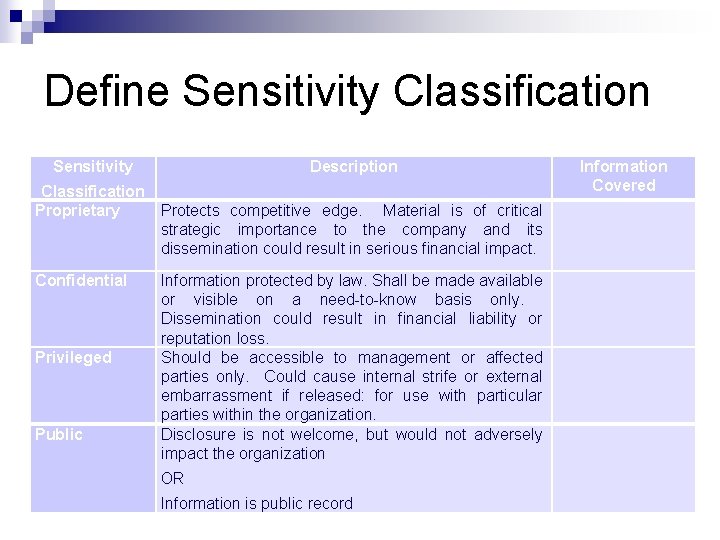
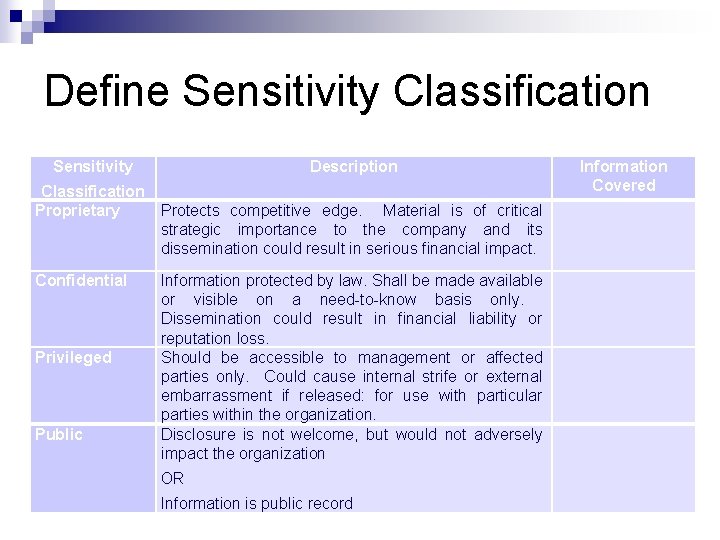
Define Sensitivity Classification Proprietary Confidential Privileged Public Description Protects competitive edge. Material is of critical strategic importance to the company and its dissemination could result in serious financial impact. Information protected by law. Shall be made available or visible on a need-to-know basis only. Dissemination could result in financial liability or reputation loss. Should be accessible to management or affected parties only. Could cause internal strife or external embarrassment if released: for use with particular parties within the organization. Disclosure is not welcome, but would not adversely impact the organization OR Information is public record Information Covered
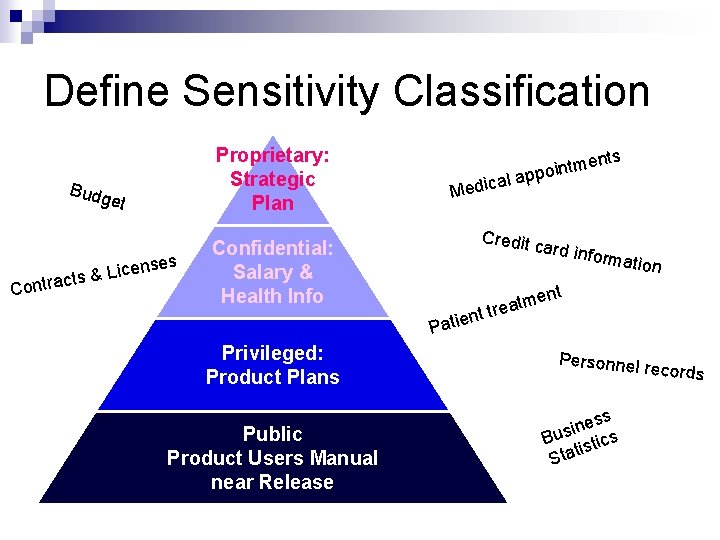
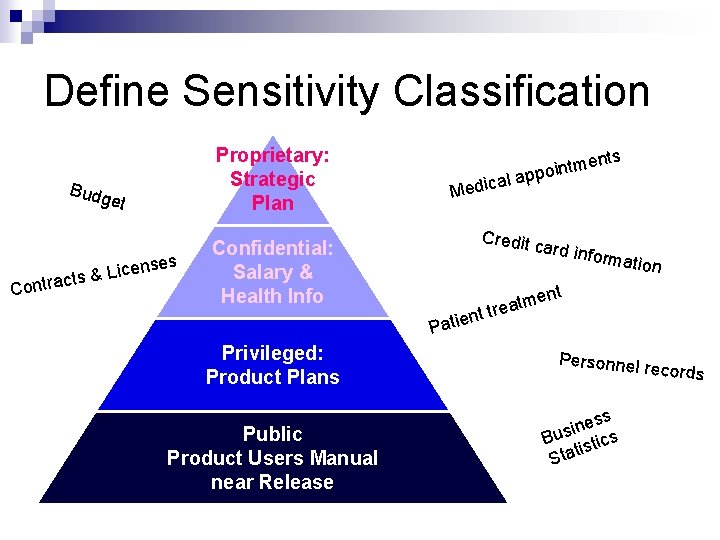
Define Sensitivity Classification Budg Con Proprietary: Strategic Plan et ses n e c i L tracts & al Medic Credit rmation nt Patie Public Product Users Manual near Release nts card in fo Confidential: Salary & Health Info Privileged: Product Plans ntme appoi e m t a e t tr n Personnel r e cords ss e n i Bus stics ti Sta
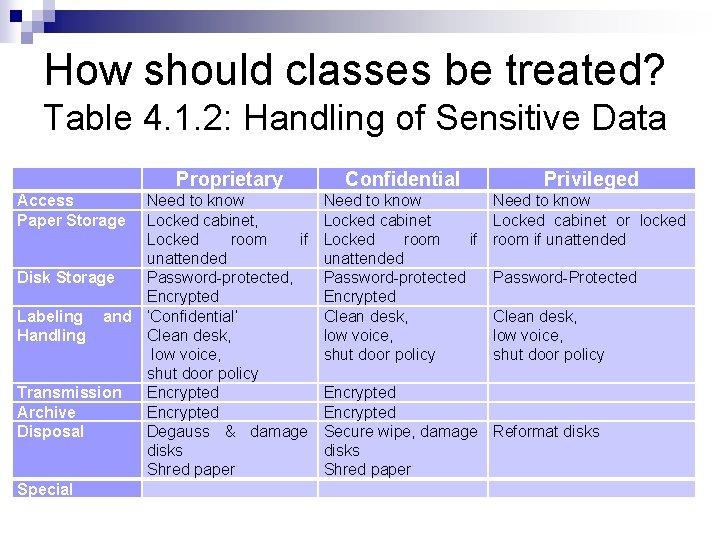
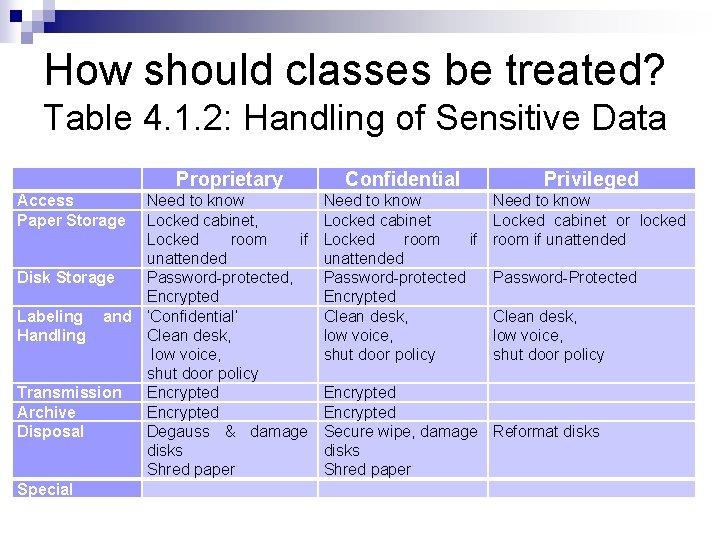
How should classes be treated? Table 4. 1. 2: Handling of Sensitive Data Access Paper Storage Proprietary Need to know Locked cabinet, Locked room if unattended Disk Storage Password-protected, Encrypted Labeling and ‘Confidential’ Handling Clean desk, low voice, shut door policy Transmission Encrypted Archive Encrypted Disposal Degauss & damage disks Shred paper Special Confidential Privileged Need to know Locked cabinet Locked room if unattended Password-protected Encrypted Clean desk, low voice, shut door policy Need to know Locked cabinet or locked room if unattended Password-Protected Clean desk, low voice, shut door policy Encrypted Secure wipe, damage Reformat disks Shred paper
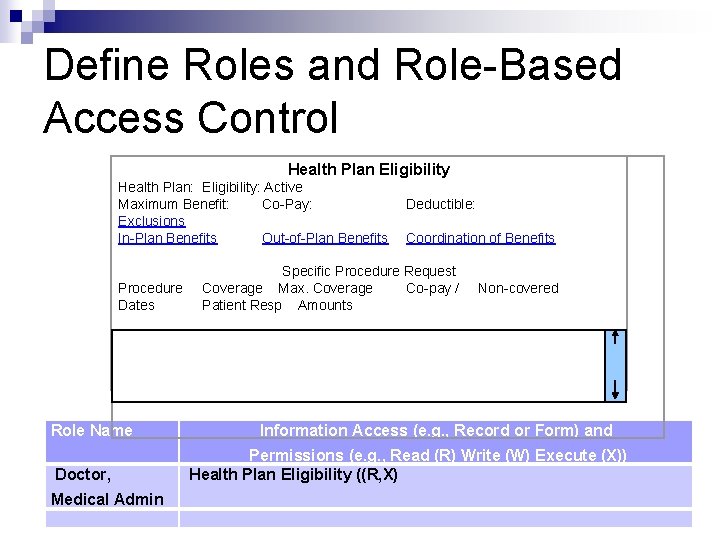
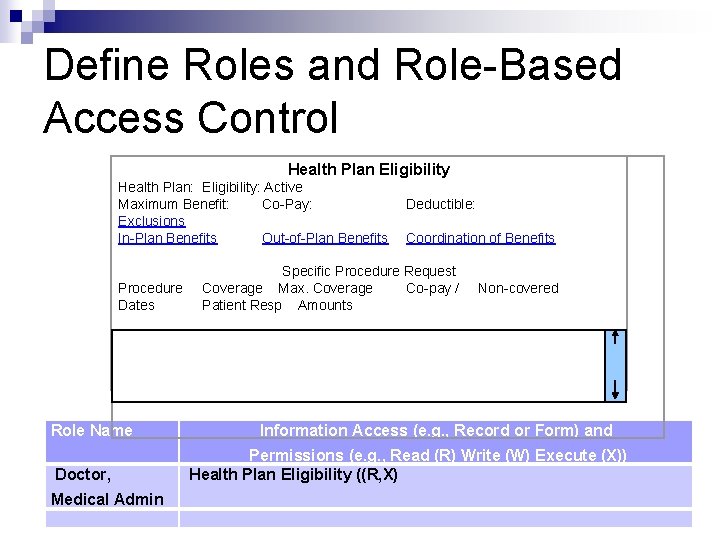
Define Roles and Role-Based Access Control Health Plan Eligibility Health Plan: Eligibility: Active Maximum Benefit: Co-Pay: Deductible: Exclusions In-Plan Benefits Out-of-Plan Benefits Coordination of Benefits Specific Procedure Request Coverage Max. Coverage Co-pay / Patient Resp Amounts Procedure Dates Role Name Non-covered Information Access (e. g. , Record or Form) and Doctor, Permissions (e. g. , Read (R) Write (W) Execute (X)) Health Plan Eligibility ((R, X) Medical Admin
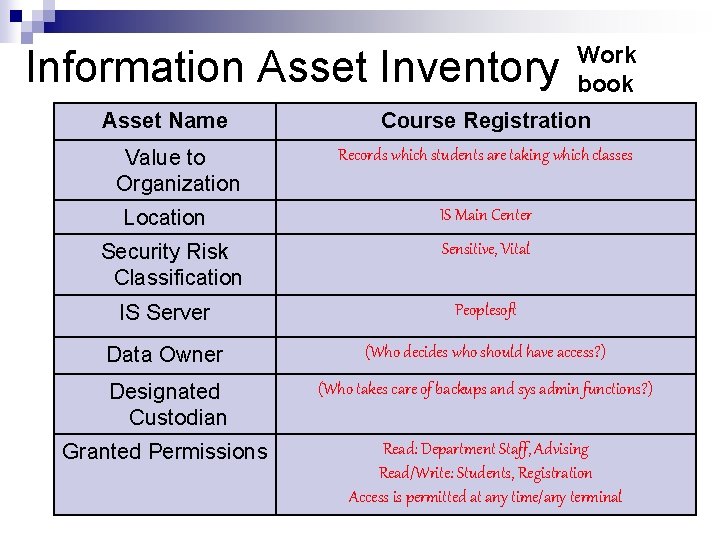
Work book Information Asset Inventory Asset Name Value to Organization Location Security Risk Classification Course Registration Records which students are taking which classes IS Main Center Sensitive, Vital IS Server Peoplesoft Data Owner (Who decides who should have access? ) Designated Custodian (Who takes care of backups and sys admin functions? ) Granted Permissions Read: Department Staff, Advising Read/Write: Students, Registration Access is permitted at any time/any terminal