INFORMATION SECURITY MANAGEMENT LECTURE 10 PERSONNEL SECURITY You
- Slides: 25
INFORMATION SECURITY MANAGEMENT LECTURE 10: PERSONNEL & SECURITY You got to be careful if you don’t know where you’re going, because you might not get there. – Yogi Berra
Introduction • Maintaining a secure environment requires that the Info. Sec department be carefully structured and staffed with appropriately credentialed personnel • Proper procedures must be integrated into all human resources activities
Qualifications and Requirements – Recognizing that Info. Sec is a management task that cannot be handled with technology alone – Acknowledging the role of policy in guiding security efforts – Understanding of the essential role of information security education and training – Perceive threats facing an organization – Understanding how to apply technical controls
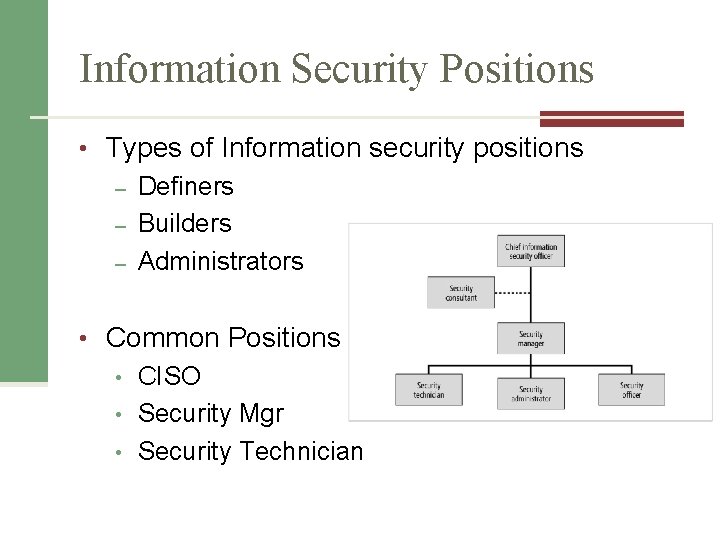
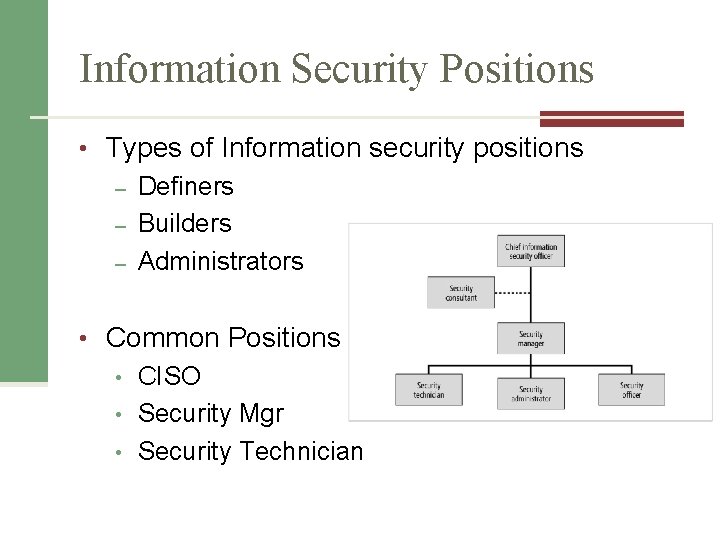
Information Security Positions • Types of Information security positions – Definers – Builders – Administrators • Common Positions • CISO • Security Mgr • Security Technician
Information Security Professional Credentials • Many organizations rely on professional certifications • Employers struggle to match certifications to position requirements • Certifying bodies work to educate their constituent communities on the value and qualifications of their certificate recipients
(ISC)2 Certifications - CISSP – Info. Sec common body of knowledge n n n n n Access Control Application Security Business Continuity and Disaster Recovery Planning Cryptography Information Security and Risk Management Legal, Regulations, Compliance and Investigations Operations Security Physical (Environmental) Security Architecture and Design Telecommunications and Network Security
(ISC)2 Certifications (cont’d. ) • Systems Security Certified Practitioner – Focuses on practices, roles, and responsibilities covering seven domains: n n n n Access controls Analysis and monitoring Cryptography Malicious code Networks and Telecommunications Risk, Response and Recovery Security Operations and Administration
(ISC)2 Certifications (cont’d. ) • ISSAP®: Information Systems Security Architecture Professional – – – Access control systems and methodology Telecommunications and network security Cryptography Requirements analysis and security standards, guidelines, criteria Technology-related business continuity planning and disaster recovery planning Physical security integration
(ISC)2 Certifications (cont’d. ) • ISSEP®: Information Systems Security Engineering Professional • ISSMP®: Information Systems Security Management Professional
Global Information Assurance Certification • GIAC Certifications – Information security fundamentals (GISF) – Security essentials certification (GSEC) – Certified firewall analyst (GCFW) – Certified intrusion analyst (GCIA) – Certified incident handler (GCIH) – Certified Windows security administrator (GCWN) – Certified UNIX security administrator (GCUX) – Certified forensics analyst (GCFA)
Global Information Assurance Certification (cont’d) • GIAC Certifications (cont’d. ) – Securing Oracle Certification (GSOC) – Intrusion Prevention (GIPS) – Cutting Edge Hacking Techniques (GHTQ) – Web Application Security (GWAS) – Reverse Engineering Malware (GREM) – Assessing Wireless Networks (GAWN)
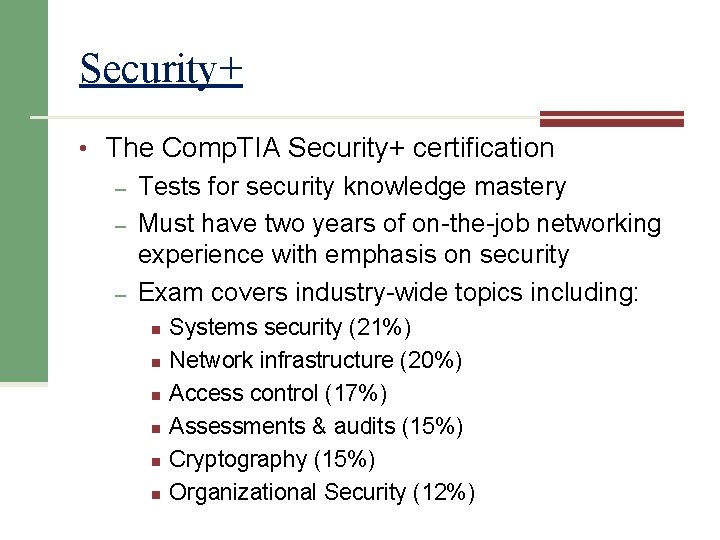
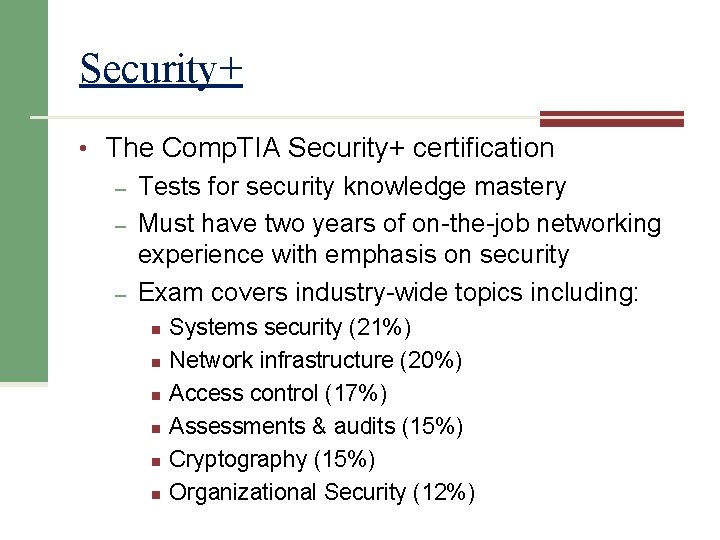
Security+ • The Comp. TIA Security+ certification – Tests for security knowledge mastery – Must have two years of on-the-job networking experience with emphasis on security – Exam covers industry-wide topics including: n n n Systems security (21%) Network infrastructure (20%) Access control (17%) Assessments & audits (15%) Cryptography (15%) Organizational Security (12%)
Certification Costs • Preferred certifications can be expensive • Certifications recognize experts in their respective fields • Most examinations: – – Require between two and three years experience Structured to reward candidates who have significant hands-on experience
Employment Policies and Practices • Management should integrate solid information security concepts – Across all of the organization’s employment policies and practices – Including information security responsibilities into every employee’s job description and subsequent performance reviews
Security as Part of Performance Evaluation • Organizations should incorporate information security components into employee performance evaluations
Termination Issues • When an employee leaves an organization, the following tasks must be performed: – – – – Disable access to the organization’s systems Return all removable media Hard drives must be secured File cabinet and door locks must be changed Keycard access must be revoked Personal effects must be removed Escort the former employee from the premises
Termination Issues: Hostile Departure – – – Security cuts off all logical and keycard access before the employee is terminated The employee reports for work, and is escorted into the supervisor’s office to receive the bad news The individual is then escorted from the workplace and informed that his or her personal property will be forwarded, or is escorted to his or her office, cubicle, or personal area to collect personal effects
Termination Issues: Friendly Departure – The employee may have tendered notice well in advance of the actual departure date – Employee accounts are usually allowed to continue, with a new expiration date – The employee can come and go at will n Usually collects any belongings and leaves without escort, dropping off all organizational property before departing
Termination Issues • In either circumstance: – Offices and information used by departing employees must be inventoried, their files stored or destroyed, and all property returned to organizational stores – Departing employees may have collected and taken home information or assets that could be valuable in their future jobs – Scrutinizing system logs may allow an organization to determine whether a breach of policy or a loss of information has occurred
Personnel Security Practices • Methods of monitoring and controlling employees – Separation of duties – Two-man control – Job rotation – Task rotation
Security of Personnel and Personal Data • Organizations are required by law to protect sensitive or personal employee information – Responsibility extends to customers, patients, and anyone with whom the organization has business relationships • Personnel data is no different than other data that information security is expected to protect – But more regulations cover its protection
Security Considerations for Nonemployees • Many individuals who are not employees often have access to sensitive organizational information
Security Considerations for Nonemployees • Temporary workers • • Not employed by the organization for which they’re working May not be subject to the contractual obligations or policies that govern employees Unless specified in its contract with the organization, the temporary agency may not be liable for losses caused by its workers Access to information should be limited to what is necessary to perform their duties
Security Considerations for Nonemployees • Contract employees • Know what they need access to • Not all contractors need universal access • Regulations for service agreements or contracts: – Require 24 to 48 hours’ notice – Require all on-site personnel to undergo background checks – Require advance notice for cancellation or rescheduling of a maintenance visit
Security Considerations for Nonemployees (cont’d. ) • Consultants – Have their own security requirements and contractual obligations – Protecting your information may not be their number one priority – Apply the principle of least privilege