Information Security Learning objectives Why information security What
Information Security
Learning objectives § Why information security? § What information is covered? § Classifying information § Information security in practice § Our company’s information security policy
Why is information security important? • Information = Valuable • Information = Personal
What information is covered? § Personal § Legal § Corporate § Operational If it’s not in the public domain, protect it!
Risks and consequences Ø The data’s value Ø The added risk of a direct attack – on our people or our systems Ø The cost of regulatory fines Ø The cost of restoring or recreating what’s lost Ø Reputational damage
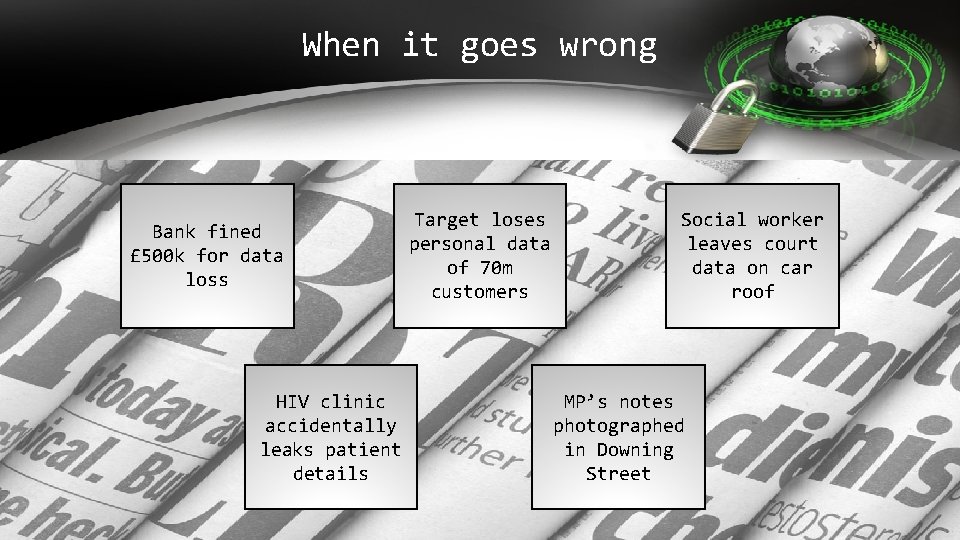
When it goes wrong Bank fined £ 500 k for data loss HIV clinic accidentally leaks patient details Target loses personal data of 70 m customers Social worker leaves court data on car roof MP’s notes photographed in Downing Street
Information Security breaches Why do information security breaches occur? a) Ignorance of the rules – eg policy violations caused by a lack of training b) Failing to realise data was confidential c) Insufficient methods to protect data d) Deliberate leaks e) User error – eg sending an email with data to the wrong people
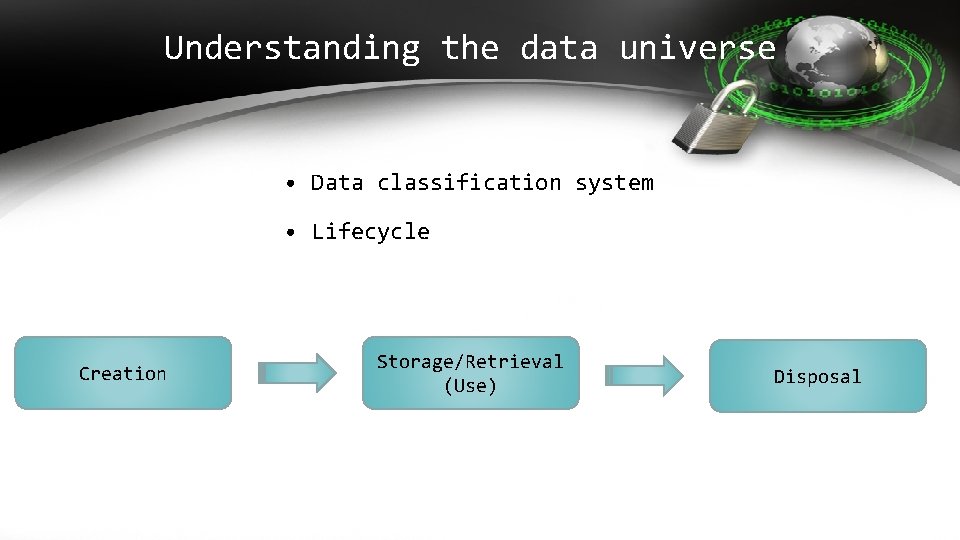
Understanding the data universe • Data classification system • Lifecycle Creation Storage/Retrieval (Use) Disposal
Classifying information 1. Confidential 2. Inside 3. Internal 4. Public

You make the call: What type is it? Last year’s annual company report A client’s payment details Our company’s telephone directory and handbook Confidential Inside Internal Public Inside
Communication and information security IL A EM I forwarded the email without thinking. I forgot to check what else was further down the thread. IN ME STA SS NT AG ES I clicked on Reply to All by accident. The message went to all our 3, 000 employees. The system was swamped when people replied back.

Information security and the internet Happy Birthday to my favourite client Lydia Clarke In Leeds today with Magee Investments – exciting times ahead Bye desk – see you in 2 weeks
Information security on the move § Eavesdropping § Shoulder surfing § Unsecure Wi. Fi connections § Loss of physical information § Loss of equipment or devices
Opinion: Security and portable media I lost a memory stick after travelling to a client meeting. The data wasn’t encrypted. My laptop was stolen on the train. There wasn’t much information on it but that’s not the point.
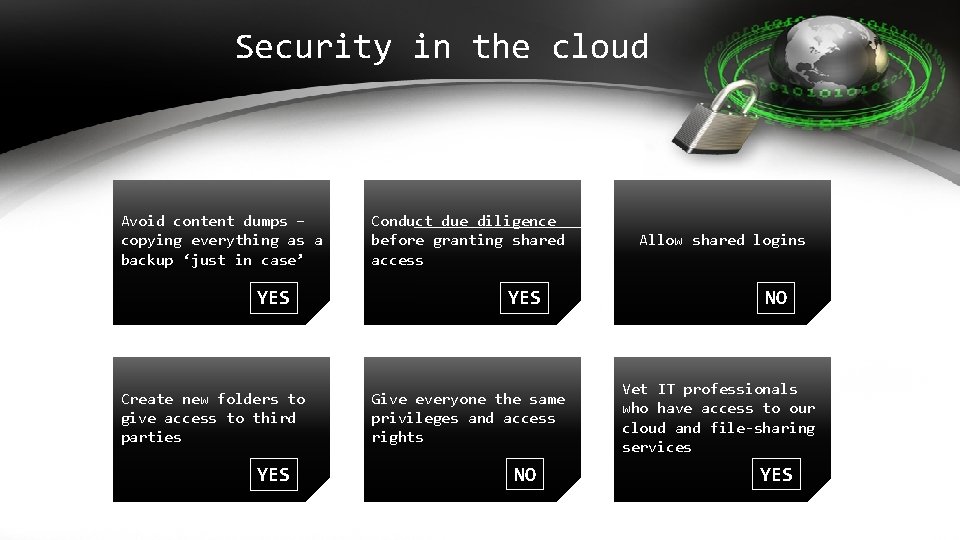
Security in the cloud Avoid content dumps – copying everything as a backup ‘just in case’ YES Create new folders to give access to third parties YES Conduct due diligence before granting shared access YES Give everyone the same privileges and access rights NO Allow shared logins NO Vet IT professionals who have access to our cloud and file-sharing services YES
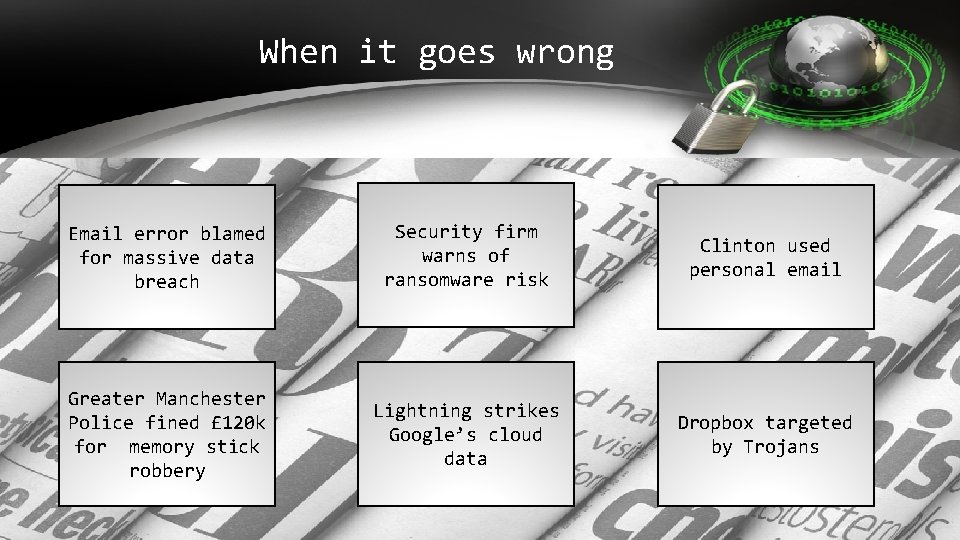
When it goes wrong Email error blamed for massive data breach Security firm warns of ransomware risk Clinton used personal email Greater Manchester Police fined £ 120 k for memory stick robbery Lightning strikes Google’s cloud data Dropbox targeted by Trojans

Watch out: GDPR is coming… 4% of global turnover € 20 million
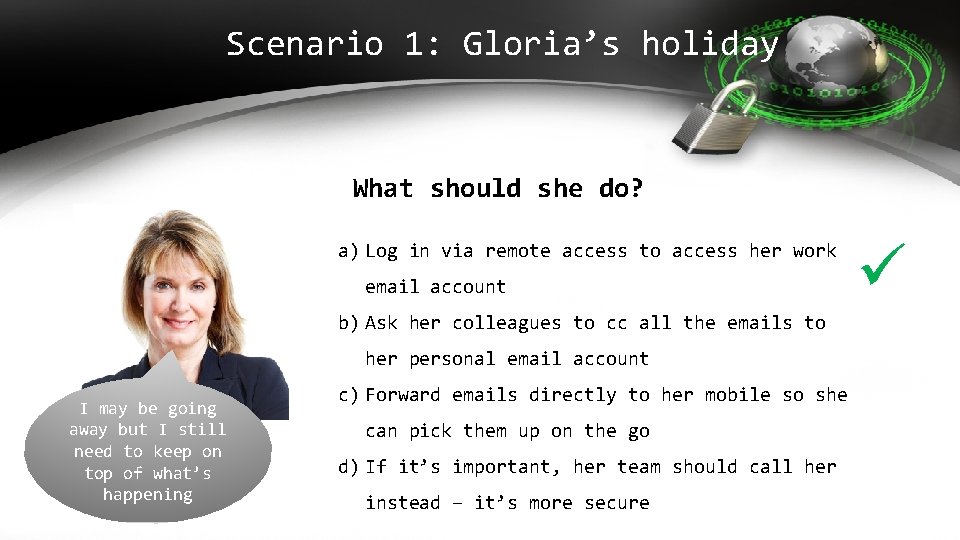
Scenario 1: Gloria’s holiday What should she do? a) Log in via remote access to access her work email account b) Ask her colleagues to cc all the emails to her personal email account I may be going away but I still need to keep on top of what’s happening c) Forward emails directly to her mobile so she can pick them up on the go d) If it’s important, her team should call her instead – it’s more secure
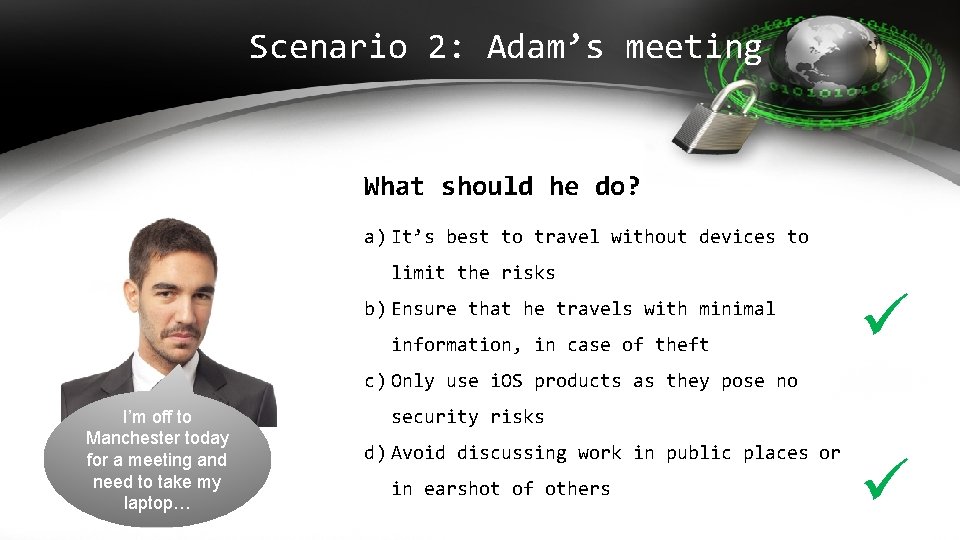
Scenario 2: Adam’s meeting What should he do? a) It’s best to travel without devices to limit the risks b) Ensure that he travels with minimal information, in case of theft c) Only use i. OS products as they pose no I’m off to Manchester today for a meeting and need to take my laptop… security risks d) Avoid discussing work in public places or in earshot of others
Our Information Security Policy § Providing information and training – raising awareness § Carrying out regular risk assessments § Testing our systems are secure § Providing appropriate technology to keep information safe § Appointing people with specific responsibility for information security § Requiring everyone to read and implement our Information Security Policy
DO Read our Company's Information Security Policy – make sure you understand our rules and know what to do Be aware of how data you use is classified Take appropriate precautions whenever you use our information, right throughout the lifecycle – from creation to disposal Report any issues or breaches immediately to your manager – so we can limit our losses
DON’T • Assume that everyone is entitled to see the same information as you • Leave your computer logged on or leave information unattended on your desk • Send or store sensitive information electronically without encryption • Forward our information to your personal devices • Share your login with anyone else • Let visitors walk around our offices unattended
Any Questions?
Next steps • Call _____ on _____ if you need information or guidance • Call _____ on _____ if you need to raise concerns • Access self-study courses on our e-learning portal for further training [or optionally – Complete your mandatory training on our corporate e-learning portal]
- Slides: 24