Information Security ESS Ari Benderly Chief Information Security
Information Security @ ESS Ari Benderly Chief Information Security Officer www. europeanspallationsource. se
Agenda • • • Introduction Risk Landscape Program Status Priorities Q&A 2
Introduction • Started at ESS in April 2018 • My background – 20 years of IT and information security experience – Most recently worked for NASA – Previously worked in the technology and software industries – HP, Alcatel. Lucent, Genesys Labs 3
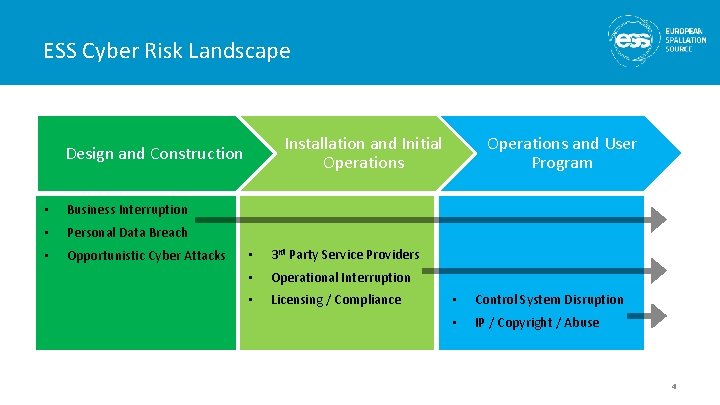
ESS Cyber Risk Landscape Installation and Initial Operations Design and Construction • Business Interruption • Personal Data Breach • Opportunistic Cyber Attacks • 3 rd Party Service Providers • Operational Interruption • Licensing / Compliance Operations and User Program • Control System Disruption • IP / Copyright / Abuse 4
Program Status • Developing the information security program – ISO 27000 – top level ISMS approach – IEC 62443 – approach and design patterns for control systems and technical networks – Adapted to meet the needs of ESS • Building information security governance structures – Steering committee for Security and Privacy – Federated Local Information Security Officers (LISOs) • Represent the main organizational units • Starting to promote a security culture and awareness – Training • New staff • Recurring training – Communication campaign 5
Program Status • Assessing our information security risks – – Information assets Data classification Threats and vulnerabilities Risk analysis • Accelerating our GDPR compliance efforts – We have addressed the highest risk components first: • General privacy policy • Privacy consents • Website and cookies policies • New third party services and external processor agreements • Personal data breach assessments 6
Program Status • Addressing SSM licensing requirements – Awaiting revised conditions for Information Security • Coordinating ongoing activities with an impact on information security – – Bringing the internal ESS information technology functions together Elevating efforts to develop an enterprise architecture Standardizing and consolidating Addressing security in the system development lifecycle 7
Priorities • Incident Response Planning – Connect with emergency response and crisis management – GDPR personal data breach notifications • Vulnerability Management – Risk based – Continuous monitoring • User training and awareness – Targeted communications – Newsletters – Role based security training • Identity and access management – We are planning for a flexible system that can support dynamic policy based physical and logical access authorizations • • Training status Dosimetry Environmental conditions (time of day, operational state, etc…) Privileged access management 8
Priorities • GDPR / Data Protection – Data Protection Impact Assessments – Comprehensive internal data processor compliance – Technical measures to support the exercise of data subject rights • 3 rd party risk (services, supply chain, In-Kind) – Contractual requirements – Incident response coordination • Personnel security – Position risk assessments – Risk based employee screening and security clearance – Connect with worker safety training requirements • Everything else… – – – Maturing information security policies Security architecture Monitoring Business continuity planning Penetration testing 9
Collaborations • • • MAX IV CERN Lund University SUNET Nordic e-Infrastructure Collaboration (Ne. IC) 10
Thank you Questions? 11
- Slides: 11