Information Security and the CIA Triad Lesson 1

![References “ 2017 Internet Crime Report [PDF]” Internet Crime Complaint Center. FBI. Damiani, J. References “ 2017 Internet Crime Report [PDF]” Internet Crime Complaint Center. FBI. Damiani, J.](https://slidetodoc.com/presentation_image_h/06428332ecb8cef375a9773e70d63d03/image-42.jpg)
- Slides: 43
Information Security and the CIA Triad Lesson 1 Gone Phishing This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Learning Outcomes Upon completion of this lesson, students will: • understand how phishing leads to unauthorized access to computing resources or information. • identify examples of personally identifiable information (PII). This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Guiding Questions • What is “trust” based upon in the online world? • How does the CIA Triad affect information security? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm-Up Activity: Word Cloud What are 3 words that come to mind when you think about online security risks? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Is online security a big problem? • During the first quarter of 2019, Facebook removed 2. 2 billion fake accounts from its platform. That is nearly as many active monthly users as it claims to have in total. • In October 2018, Twitter announced that it had removed 9 million users through a crackdown on bots. • The total number of phishing sites detected by the Anti-Phishing Working Group (APWG) in Quarter 1 of 2019 was 180, 768. • In Q 1 2019, 58 percent of phishing sites were using SSL certificates. • The FBI’s Internet Crime Complaint Center (IC 3) receives over 800 complaints per day. • In 2017, the FBI’s IC 3 received 1, 783 complaints identified as ransomware with adjusted losses of over $2. 3 million. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
What is the danger of deepfakes? • A phishing website named klkviral. org, listed 55, 851 Snapchat accounts, along with their usernames and passwords. The attack relied on a link sent to users through a compromised account that, when clicked, opened a website designed to mimic the Snapchat login screen (Newton 2018). • In March 2019, an artificial intelligence-generated voice deepfake was used in a scam. The CEO of a UK-based energy firm thought he was on the phone with his boss when he followed the orders to immediately transfer € 220, 000 (approx. $243, 000) to the bank account of a Hungarian supplier. It is the first known use of AI deepfake for a financial crime (Damiani 2019). This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Phishing Defined Phishing is an attempt by an individual or group to solicit personal information from unsuspecting users by employing social engineering techniques. Phishing emails are crafted to appear as if they have been sent from a legitimate organization or known individual. These emails often attempt to entice users to click on a link that will take the user to a fraudulent website that appears legitimate. The user then may be asked to provide personal information, such as account usernames and passwords, that can further expose them to future compromises. Additionally, these fraudulent websites may contain malicious code. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Why is Phishing a popular attack? • The World Wide Web is a system of linked pages, programs, and files. • The very nature of the Internet makes it relatively easy to redirect a user using an embedded link in an email. • Many users simply don’t take the time to carefully examine each email due to the volume of emails in the inbox. This makes it relatively easy to insert a malicious link. The link may redirect to a website asking for username or password, or start downloading a file, or perhaps deploy ransomware on a computer system. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Keeping Secrets Read: “Top-Secret NAS Report Details Russian Hacking Efforts Days Before 2019 Election” (Cole, Matthew, et al. The Intercept, 5 June 2017. ) Discussion Questions: 1. What happened? How did it happen? Why did it happen? 2. Who are the stakeholders? 3. Where is accountability assigned? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Does abstraction impact security? • Abstraction is the process of reducing complexity by focusing on the main idea. By hiding details irrelevant to the question at hand bringing together related and useful details, abstraction reduces complexity and allows one to focus on the idea. • The design of the Internet is an example of abstraction. It has enabled an untold number of users worldwide to communicate and interact online with little to no understanding of how it works. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Activity: Gone Phishing • “Can you spot when you’re being phished? ” (Google Jigsaw) • “How is your Phishing IQ? ” (Sonic. Wall) • Phishing Quiz (Cisco) What did you notice about the phishing emails? What are some of the characteristics of a scam email? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
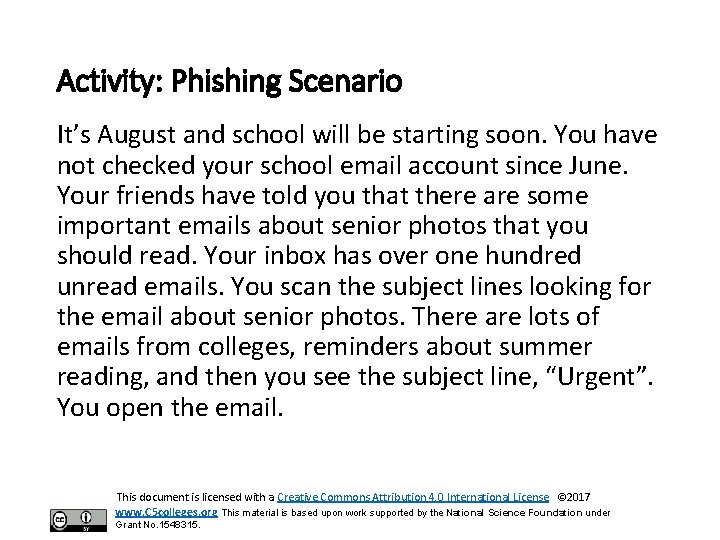
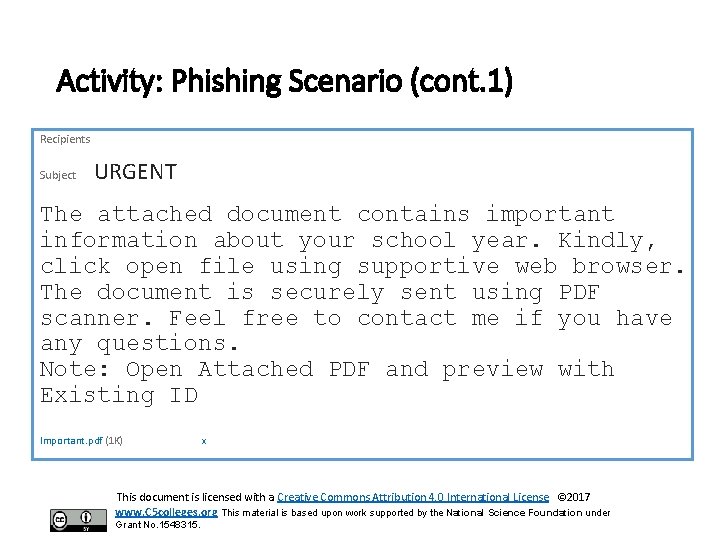
Activity: Phishing Scenario It’s August and school will be starting soon. You have not checked your school email account since June. Your friends have told you that there are some important emails about senior photos that you should read. Your inbox has over one hundred unread emails. You scan the subject lines looking for the email about senior photos. There are lots of emails from colleges, reminders about summer reading, and then you see the subject line, “Urgent”. You open the email. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
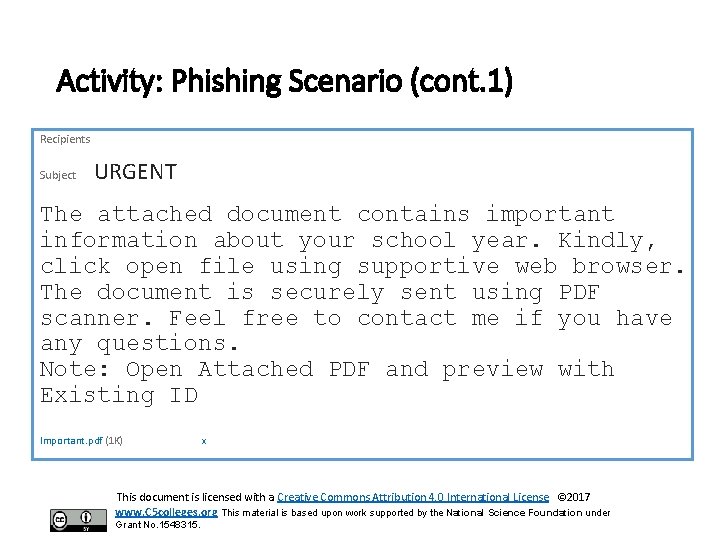
Activity: Phishing Scenario (cont. 1) Recipients Subject URGENT The attached document contains important information about your school year. Kindly, click open file using supportive web browser. The document is securely sent using PDF scanner. Feel free to contact me if you have any questions. Note: Open Attached PDF and preview with Existing ID Important. pdf (1 K) x This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Activity: Phishing Scenario continued You click on the attachment, it opens in the browser, and you click on a link that says, “Sign in to view the document. ” You are redirected to a login page requesting your email address and password. You enter your credentials and some files start downloading to your computer. You now wonder whether you should have provided your email address and password. You feel a sense of panic as your computer is restarting. Panic! This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Activity: Fake social media accounts While checking your social media account on your phone, you see several new follower requests. You tap to confirm the requests as some of them look familiar, but others do not. You want to raise your follower count to boost your online presence, so more is better. Or is it? What harm can come from accepting fake follower requests? Real or Fake? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
What are fake accounts? • Fake accounts may be created by individuals with an intent to deceive. • A sockpuppet is an online identity used for purposes of deception. • Socialbots control social media accounts and perform automated tasks with the intent of convincing other users that the socialbot is a real person. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.

Activity: Think-Pair-Share Prompt What do phishing emails and fake social media accounts tell us about trust in the online world? Trust but Verify. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Record Student Responses This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm-Up Activity • What information is valuable to a hacker? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm-Up Activity (cont. 1) • In 2015 the Office of Personnel Management (OPM) discovered a data breach. OPM serves as the storehouse of personnel records for federal employees. The stolen data included names, addresses, places of birth, social security numbers, financial information, fingerprints, and background checks on millions of people. • Over the course of at least two months in 2017, 143 million Americans were impacted by the Equifax data breach. Equifax failed to apply a security patch. The hackers acquired names, Social Security numbers, birth dates, addresses and even some driver's license information. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Activity: Personally Identifiable Information What is Personally Identifiable Information? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Examples of Personally Identifiable Information • Social security number • Age • Race • Phone number(s) • Medical information • Financial information • Biometric data This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Writing prompt What defines personally identifiable information (PII)? What are some possible effects of a data breach involving this information? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
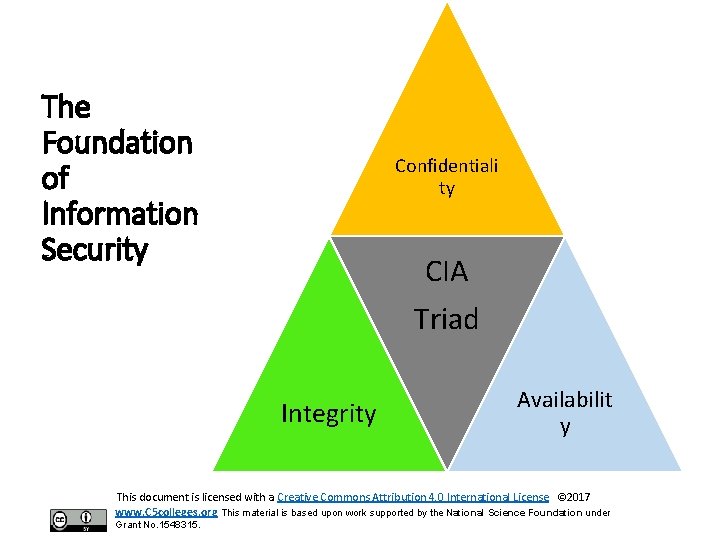
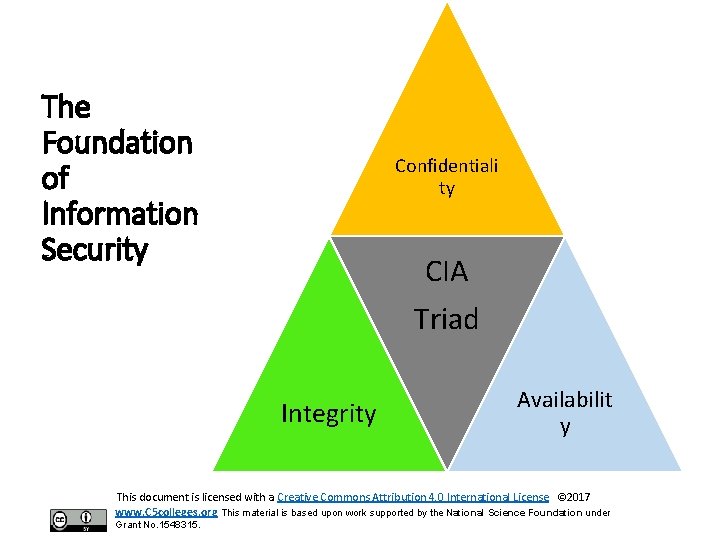
The Foundation of Information Security Confidentiali ty CIA Triad Integrity Availabilit y This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
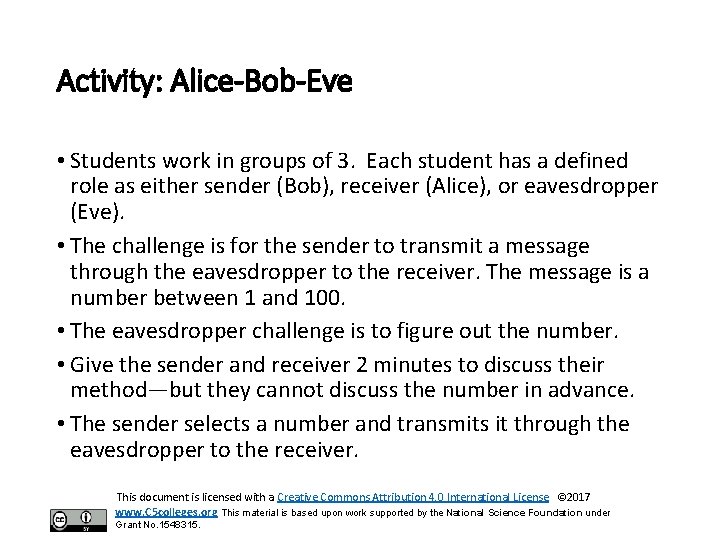
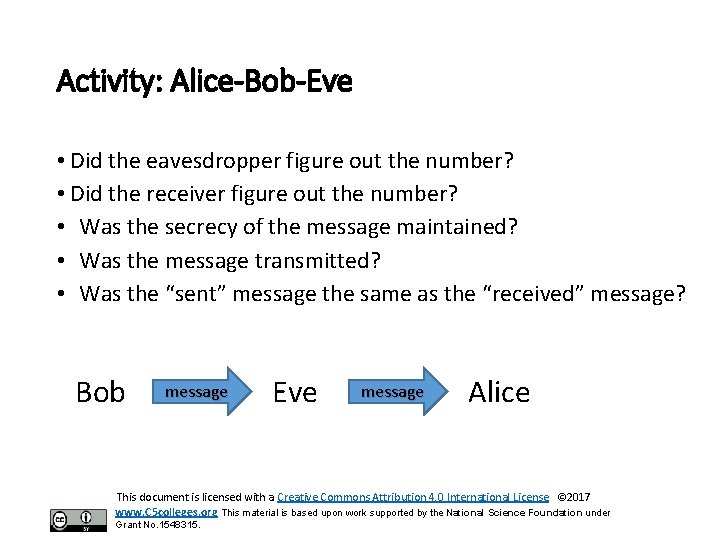
Activity: Alice-Bob-Eve • Students work in groups of 3. Each student has a defined role as either sender (Bob), receiver (Alice), or eavesdropper (Eve). • The challenge is for the sender to transmit a message through the eavesdropper to the receiver. The message is a number between 1 and 100. • The eavesdropper challenge is to figure out the number. • Give the sender and receiver 2 minutes to discuss their method—but they cannot discuss the number in advance. • The sender selects a number and transmits it through the eavesdropper to the receiver. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
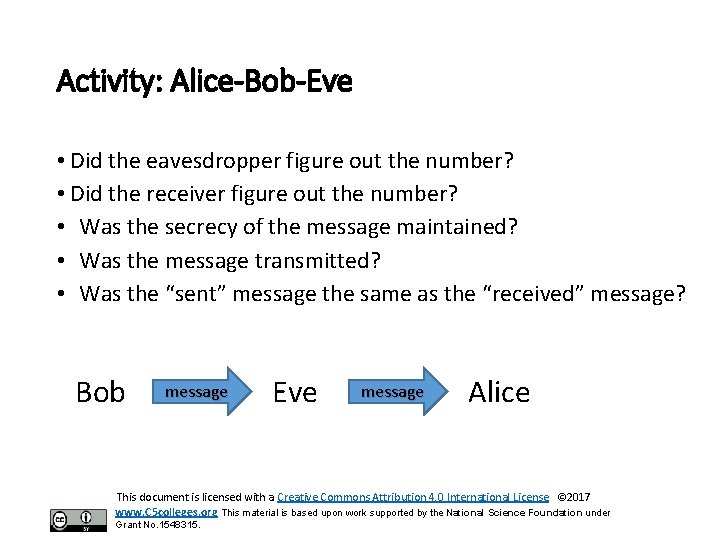
Activity: Alice-Bob-Eve • Did the eavesdropper figure out the number? • Did the receiver figure out the number? • Was the secrecy of the message maintained? • Was the message transmitted? • Was the “sent” message the same as the “received” message? Bob message Eve message Alice This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
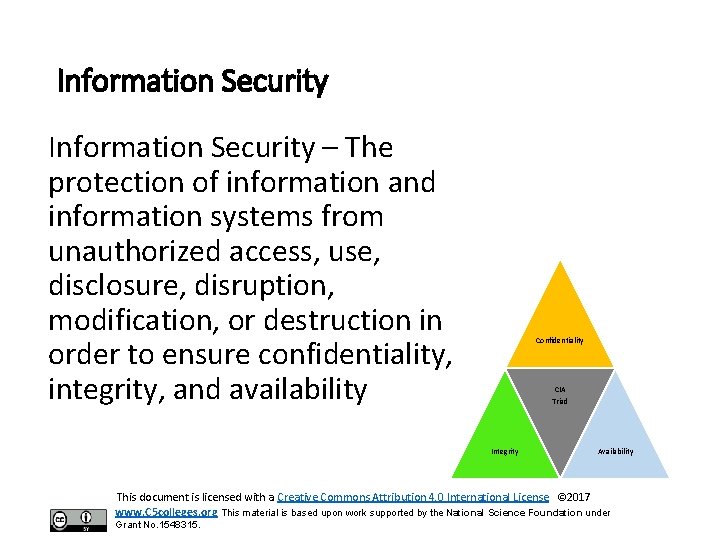
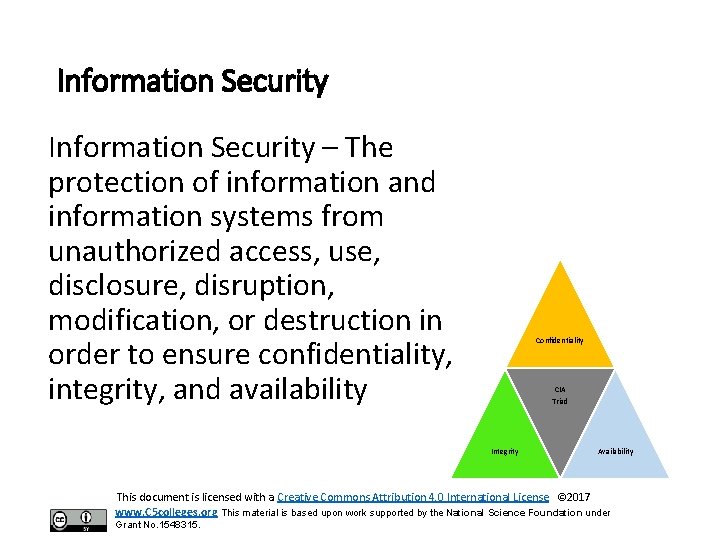
Information Security – The protection of information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction in order to ensure confidentiality, integrity, and availability Confidentiality CIA Triad Integrity Availability This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
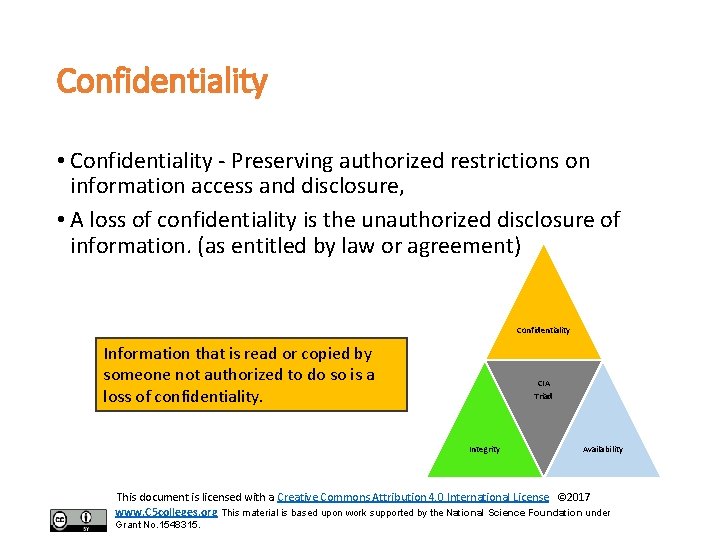
Confidentiality • Confidentiality - Preserving authorized restrictions on information access and disclosure, • A loss of confidentiality is the unauthorized disclosure of information. (as entitled by law or agreement) Confidentiality Information that is read or copied by someone not authorized to do so is a loss of confidentiality. CIA Triad Integrity Availability This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
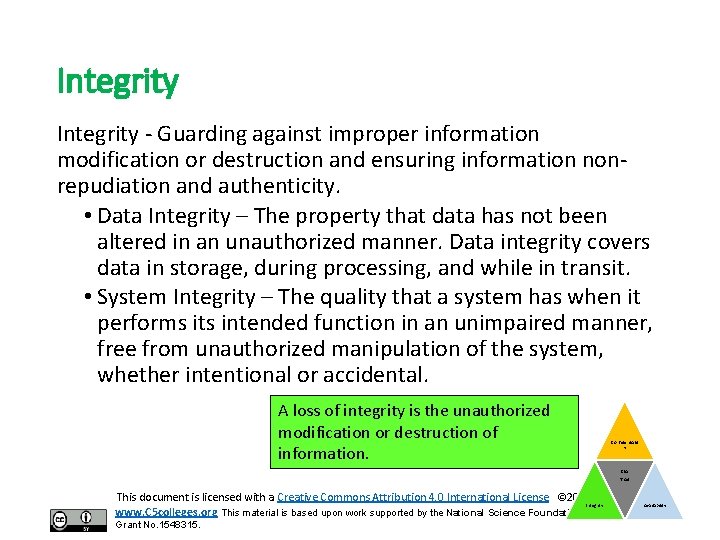
Integrity - Guarding against improper information modification or destruction and ensuring information nonrepudiation and authenticity. • Data Integrity – The property that data has not been altered in an unauthorized manner. Data integrity covers data in storage, during processing, and while in transit. • System Integrity – The quality that a system has when it performs its intended function in an unimpaired manner, free from unauthorized manipulation of the system, whether intentional or accidental. A loss of integrity is the unauthorized modification or destruction of information. Confidentialit y CIA Triad This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 Integrity www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315. Availability
Integrity (cont. 1) • Non-repudiation Assurance that the sender is provided with proof of delivery and that the recipient is provided with proof of the sender's identity so that neither can later deny having processed the data. • Authenticity The property of being genuine and being able to be verified and trusted; confidence in the validity of a transmission, a message, or message originator. A loss of integrity is the unauthorized modification or destruction of information. Confidentiality CIA Triad Integrity Availability This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Availability • Availability - Ensuring timely and reliable access to and use of information • A loss of availability is the disruption of access to or use of information or an information system. Examples: Ransomware, natural disasters, power disruption, DDo. S, hardware failure Confidentiality Information can be erased or become inaccessible, resulting in a loss of availability CIA Triad Integrity Availability This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Security Controls – The management, operational, and technical controls (i. e. , safeguards or countermeasures) prescribed for a system to protect the confidentiality, availability, and integrity of the system and its information. Confidentiality CIA Triad Integrity This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315. Availability
Discussion Can you think of some security controls to ensure confidentiality, integrity, and availability? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
What are some security controls? • Encryption of files • Controlling physical access to confidential data • Passwords • Prevent unauthorized modification • Backups, cloud storage • Fault tolerance • Redundancy This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Activity: Is it a breach of confidentiality, integrity or availability? 1. How did the 2017 Equifax exposure of 143 million records breach the CIA Triad? 2. Downloading what appears to be a legitimate app, a user installs malware which contains keylogging software. What type of breach is the downloading of malware? 3. An email phishing attack results in ransomware, in which the files and folders on a computer are encrypted. What type of breach is ransomware? 4. How do fake social media accounts breach the CIA Triad? Confidentialit y CIA Triad This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 Integrity www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315. Availability
Activity: Identity Theft What is identity theft and how to avoid it? Read: “Avoiding Identity Theft. ” (Consumer. Gov, Federal Trade Commission) Explore the information on the Federal Trade Commission’s website and answer the following questions: 1. What is identity theft? 2. Why does it matter? 3. What protective measures are available? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
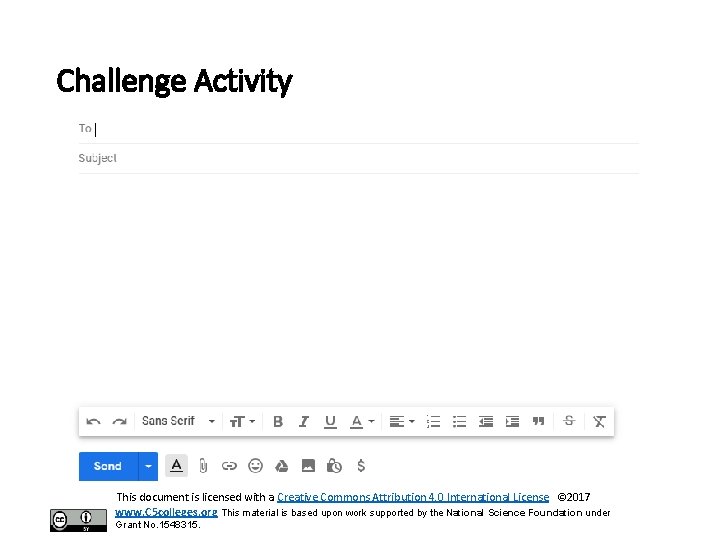
Challenge Activity: Create a Phishing Email • What type of information are you trying to obtain and what do you plan to do with this information? • How will you obtain the information you are seeking? What strategies will you need to implement? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Challenge Activity This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Challenge Activity (cont. 1) Investigate the legal requirements for confidentiality under FERPA, HIPPA, or FISMA. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Legal Requirements • The Family Educational Rights and Privacy Act (FERPA) (20 U. S. C. § 1232 g; 34 CFR Part 99) is a Federal law that protects the privacy of student education records. The law applies to all schools that receive funds under an applicable program of the U. S. Department of Education. FERPA gives parents certain rights with respect to their children's education records. These rights transfer to the student when he or she reaches the age of 18 or attends a school beyond the high school level. Students to whom the rights have transferred are "eligible students. " • The HIPAA Privacy Rule for the first time creates national standards to protect individuals’ medical records and other personal health information. It gives patients more control over their health information. It sets boundaries on the use and release of health records. It establishes appropriate safeguards that health care providers and others must achieve to protect the privacy of health information. It holds violators accountable, with civil and criminal penalties that can be imposed if they violate patients’ privacy rights. And it strikes a balance when public responsibility supports disclosure of some forms of data – for example, to protect public health. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Legal Requirements (cont. 1) • The Computer Security Act of 1987 required agencies to identify sensitive systems, conduct computer security training, and develop computer security plans. The Computer Security Act of 1987 was superseded by the Federal Information Security Management Act of 2002 (FISMA), described below. • The Federal Information Security Management Act (FISMA) was enacted as part of the E-Government Act of 2002 to address specific information security needs, which include, but are not limited to, providing: a comprehensive framework for ensuring the effectiveness of information security controls over information resources that support federal operations and assets; and the development and maintenance of minimum controls required to protect federal information and systems (as written in SEC. 301 of Public Law 107 -347). • The Federal Information Security Modernization Act of 2014 was an amendment to FISMA that made several modifications to modernize federal security practices as well as promote and strengthen the use of continuous monitoring. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
![References 2017 Internet Crime Report PDF Internet Crime Complaint Center FBI Damiani J References “ 2017 Internet Crime Report [PDF]” Internet Crime Complaint Center. FBI. Damiani, J.](https://slidetodoc.com/presentation_image_h/06428332ecb8cef375a9773e70d63d03/image-42.jpg)
References “ 2017 Internet Crime Report [PDF]” Internet Crime Complaint Center. FBI. Damiani, J. (2019, September 3). A voice deepfake was used to scam a ceo out of $243, 000. Forbes. “Global Risks Landscape 2018, 13 th Edition”. (No. 09012018). World Economic Forum. Kastrenakes, J. (2018, October 25). Twitter loses 9 million users amid bot crackdown. The Verge. Newton, C. (2018, February 16). A phishing attack scored credentials for more than 50, 000 Snapchat users. The Verge. “Phishing Activity Trends Report, 1 st Quarter 2019 [PDF]”. (2019, May 15). Anti. Phishing Working Group, Inc. “Report Phishing Sites”. CISA. Department of Homeland Security Stewart, E. “Facebook Has Taken down Billions of Fake Accounts, but the Problem Is Still Getting Worse. ” (2019, May 23) Vox. The terms and definitions were retrieved from CNSSI 4009, Committee on National Security Systems (CNSS) Glossary, dated April 6, 2015. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Catalyzing Computing and Cybersecurity in Community Colleges www. ncyte. net This material is based upon work supported by the National Science Foundation under Grant No. 1548315.