Information Security and Records Management Are they a

- Slides: 27
Information Security and Records Management: Are they a good marriage? EDUCAUSE SPC May 2015
Theresa Semmens NDSU CISO Kathy Kimball University of Virginia CISO Caroline Walters University of Virginia University Records Officer
Records Management Information Security Historically, in order to succeed in the role of CISO, strong technical skills have been required. A current trend is to meld managerial/business-oriented roles, such as records management, under the CISO. Trends that blend more than one function such as records management and information security are provoking debate among security professionals who are concerned that information security is no longer a primary focus. The University of Virginia and NDSU have combined these roles under the Information Security Office. This interactive presentation will provide two different institutional perspectives on how it works and how it can be woven into security.

Poll questions coming soon! • For Smart phones • Audience can respond by texting SPC 2015 RM to 37607 to join the session • For laptops and tablets • To join the session, the Audience can respond at Poll. Ev. com/spc 2015 rm.
Poll Question • Records Management can cohabitate peacefully with Information Security A. B. C. D. Yes No Maybe No Clue Poll. Ev. com/spc 2015 rm or text SPC 2015 RM to 37607
What is records management? • ISO 15489 -1 defines records management as the field of management responsible for the efficient and systematic control of the creation, receipt, maintenance, use and disposition of records, including the processes for capturing and maintaining evidence of and information about business activities and transactions in the form of records
What is a record? • ISO 15489 – defines record definition as information created, received, and maintained as evidence and information by an organization or person, in pursuance of legal obligations or in the transaction of business. • Simple definition: records are "all books, papers, maps, photographs, machine readable materials, or other documentary materials, regardless of physical form or characteristics, made or received by a university.
What is information security? • The processes and methodologies which are designed and implemented to protect print, electronic, or any other form of confidential, private and sensitive information or data from unauthorized access, use, misuse, disclosure, destruction, modification, or disruption. • ~ http: //www. sans. org/information-security/
University of Virginia • History • Position description and responsibilities • Reporting Structure • Skills, education, certification and talents for • CISO • University Records Officer
University of Virginia • Information Security became concern in 1999 (1 FTE) • By 2008 had grown to 6 FTE and included IT policy • 2008 Records Management Process Simplification Project • Moved Records Management from Library to Information Security • Records Officer position created • Funded the program • 2009 Additional FTE hired in Records Management • 2015 Additional FTE hired in Records Management
Why Is Records Management Under Security? • Process Simplification Project felt the following criteria were critical in determining in which unit Records Management should reside: • • • Breadth of Unit Function (Both Administrative and Academic) Compatibility of Records Management with the unit mission Customer service orientation Regulatory and Compliance role Resources for both technical and administrative support for Records Management
Why Security (Continued) • Records Management could potentially flourish in a number of areas: • Library – Based on the criteria, Project Team felt there was insufficient regulatory and compliance responsibility inherent in the mission; mission somewhat at odds with data destruction emphasis. Recommended library remain responsible for Archival functions • Financial Administration/Business Operations – Strong compliance function, customer focus. Felt revenue generation emphasis might be at odds where Records Management was concerned. A good candidate if less need for electronic record technical expertise and guidance is deemed appropriate • CIO/Security – Regulatory and Compliance/Policy role. Educational emphasis/customer interaction. Particularly recommended if significant expansion of electronic records occurred (as seemed likely)
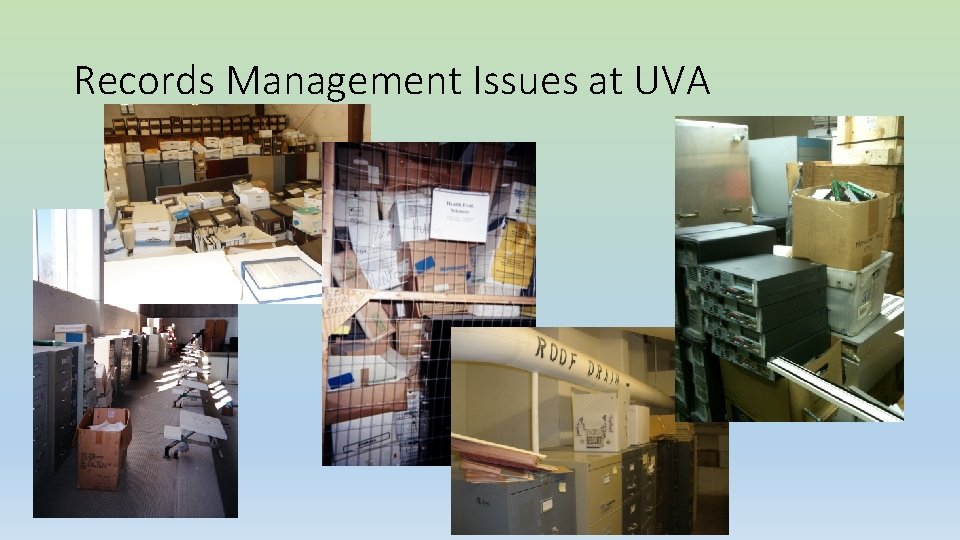
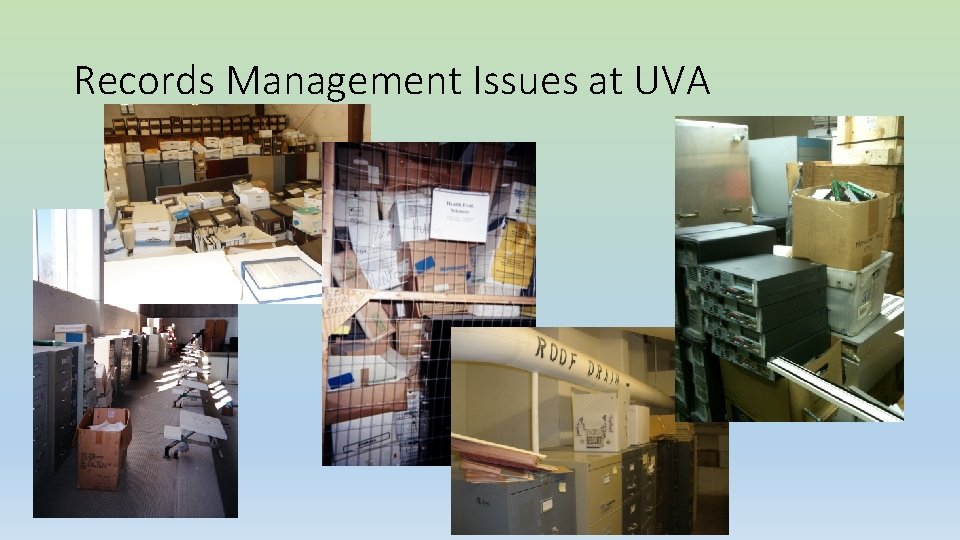
Records Management Issues at UVA
UVA CISO • Develops, implements, enhances and oversees information security and privacy policies and security of the University’s diverse and decentralized computing environment • Includes overall responsibility for assessing, monitoring, and improving the security of the University of Virginia’s computing systems, networks, and data • Works in partnership with units and individuals across the university to formulate policies and to assess security risk • Investigates and coordinates response to security incidents • Provides operational management of the Information Security, Policy, and Records Office
UVA Records Officer • Formally appointed as Records Officer to Library of Virginia per Virginia Public Records Act, responsibilities include: • Compliance with the Virginia Public Records Act – following retention schedules, completing Certificates of Records Destruction • Provide training and guidance to staff/faculty on policies and procedures for proper Records Management • Identification of archival records and ensure transfer of archival/historical records to proper archival repository • Coordinate with Library of Virginia on the revision or creation of records series for the Commonwealth or individual agencies.
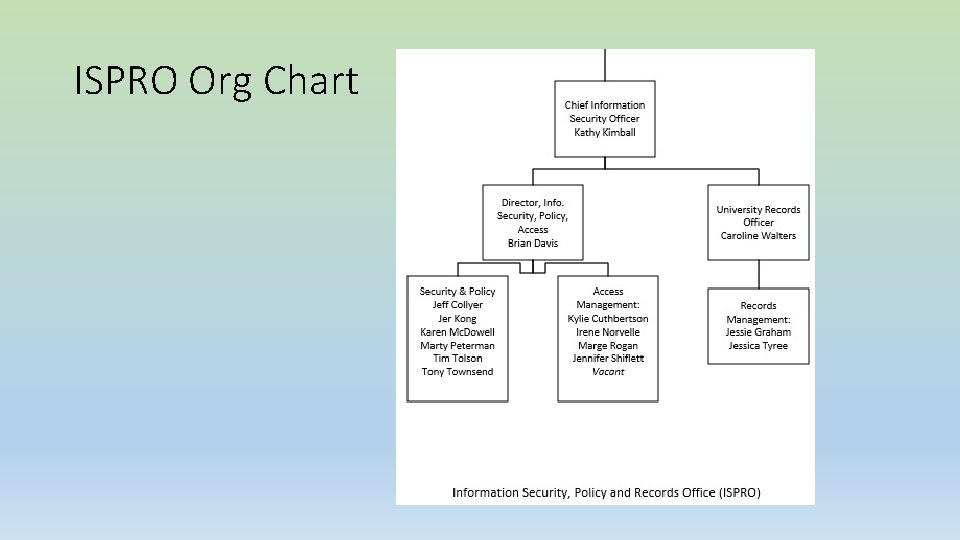
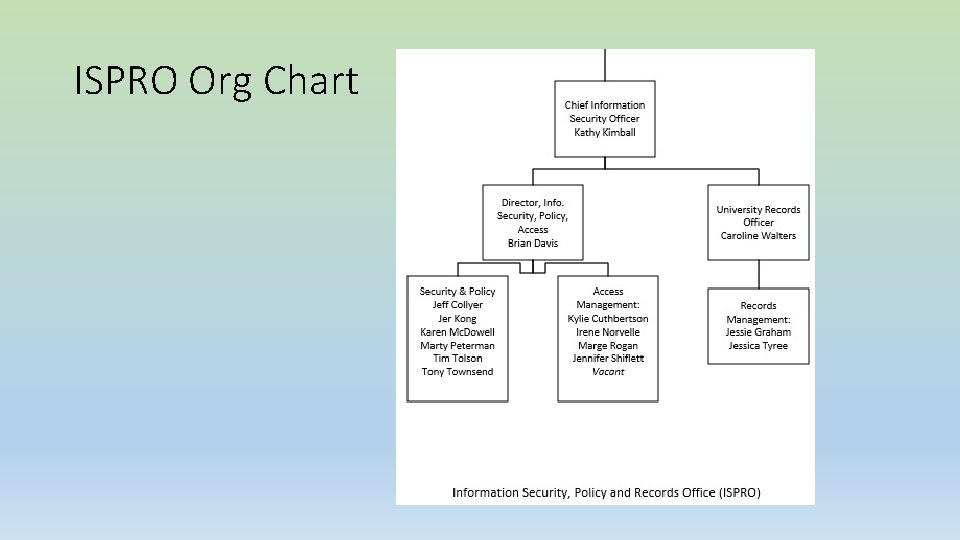
ISPRO Org Chart
North Dakota State University • History • Position description and responsibilities • Reporting Structure • Skills, education, certification and talents for • CISO/Director, Records Management • Reports to the Vice President for Information Technology
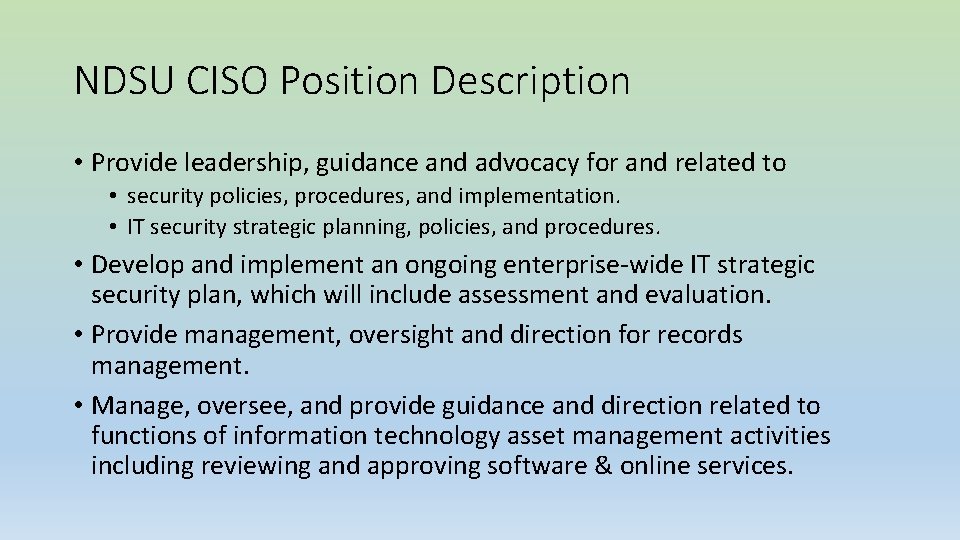
NDSU CISO Position Description • Provide leadership, guidance and advocacy for and related to • security policies, procedures, and implementation. • IT security strategic planning, policies, and procedures. • Develop and implement an ongoing enterprise-wide IT strategic security plan, which will include assessment and evaluation. • Provide management, oversight and direction for records management. • Manage, oversee, and provide guidance and direction related to functions of information technology asset management activities including reviewing and approving software & online services.
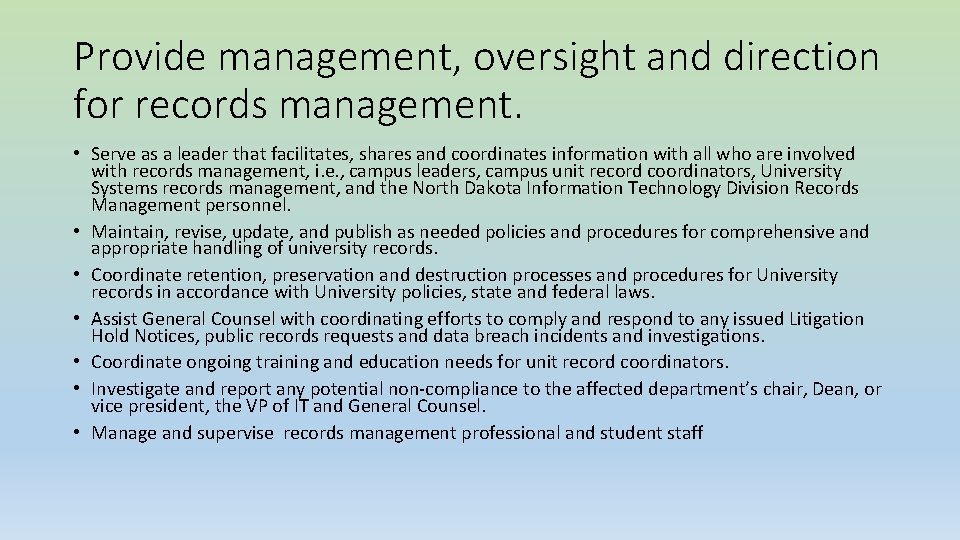
Provide management, oversight and direction for records management. • Serve as a leader that facilitates, shares and coordinates information with all who are involved with records management, i. e. , campus leaders, campus unit record coordinators, University Systems records management, and the North Dakota Information Technology Division Records Management personnel. • Maintain, revise, update, and publish as needed policies and procedures for comprehensive and appropriate handling of university records. • Coordinate retention, preservation and destruction processes and procedures for University records in accordance with University policies, state and federal laws. • Assist General Counsel with coordinating efforts to comply and respond to any issued Litigation Hold Notices, public records requests and data breach incidents and investigations. • Coordinate ongoing training and education needs for unit record coordinators. • Investigate and report any potential non-compliance to the affected department’s chair, Dean, or vice president, the VP of IT and General Counsel. • Manage and supervise records management professional and student staff
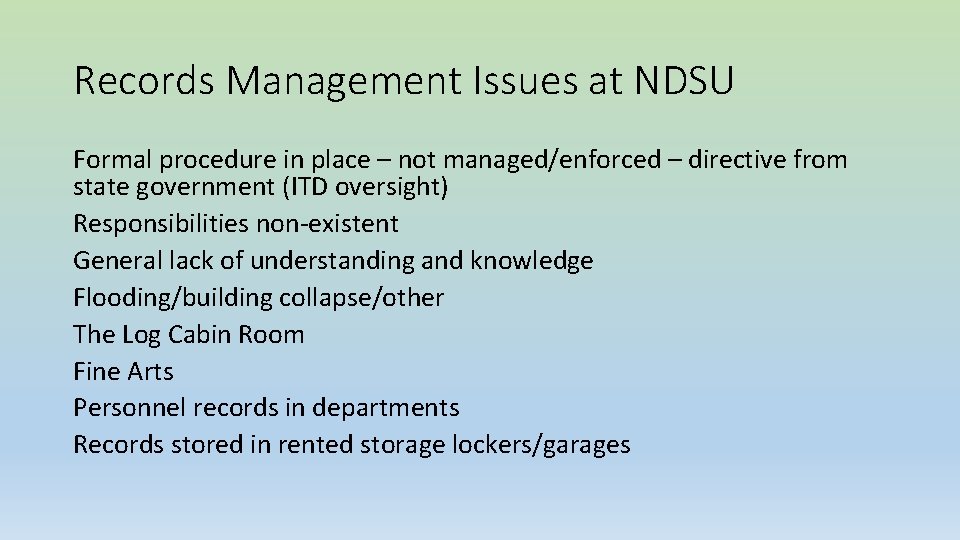
Records Management Issues at NDSU Formal procedure in place – not managed/enforced – directive from state government (ITD oversight) Responsibilities non-existent General lack of understanding and knowledge Flooding/building collapse/other The Log Cabin Room Fine Arts Personnel records in departments Records stored in rented storage lockers/garages
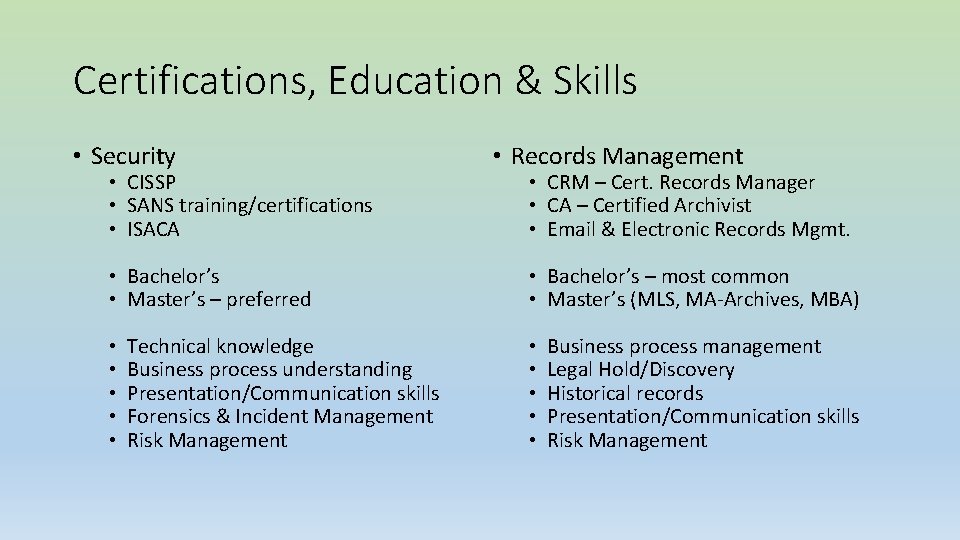
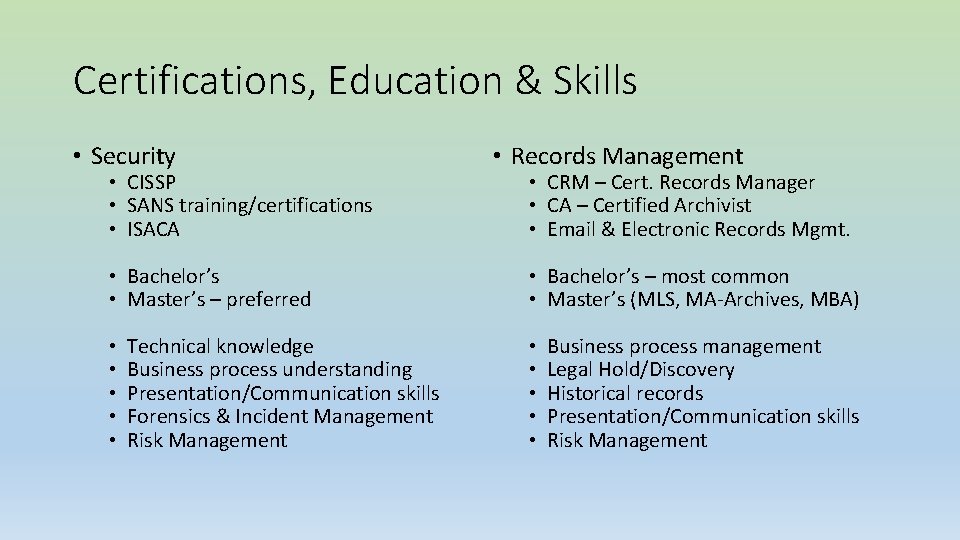
Certifications, Education & Skills • Security • CISSP • SANS training/certifications • ISACA • Bachelor’s • Master’s – preferred • • • Technical knowledge Business process understanding Presentation/Communication skills Forensics & Incident Management Risk Management • Records Management • CRM – Cert. Records Manager • CA – Certified Archivist • Email & Electronic Records Mgmt. • Bachelor’s – most common • Master’s (MLS, MA-Archives, MBA) • • • Business process management Legal Hold/Discovery Historical records Presentation/Communication skills Risk Management
Poll Question • Do you have a records management program that includes policies and procedures implemented and active? A. Yes B. No C. Have policies and procedures , but they are not enforced and promulgated Poll. Ev. com/spc 2015 rm or text SPC 2015 RM to 37607
Poll Question Records management is situated under? A. B. C. D. E. Information technology Business and finance Legal and/or compliance Library Other Poll. Ev. com/spc 2015 rm or text SPC 2015 RM to 37607
Poll Question • At your institution, records management includes these areas and people A. B. C. D. Only business Business and education All employees with the exception of faculty are required to comply Everyone and all department Poll. Ev. com/spc 2015 rm or text SPC 2015 RM to 37607
Poll Questions • Records Management can cohabitate peacefully with Information Security A. B. C. D. Yes No Maybe Still No Clue
Records Management Resources • ARMA International – http: //arma. org/ • Generally Accepted Record Keeping Principals: http: //www. arma. org/r 2/generally-accepted-br-recordkeeping-principles • AIIM - http: //www. aiim. org/ • MER – Managing Electronic Records Conference: http: //www. merconference. com/ • May 18 -20, 2015 - Chicago
Information Security and Records Management: Are they a good marriage? Questions? • Theresa Semmens Theresa. Semmens@ndsu. edu • Kathy Kimball krk 6 p@virginia. edu • Caroline Walters cw 8 de@virginia. edu Thank you