INFORMATION SECURITY and CRYPTOGRAPHY INFORMATION SECURITY and CRYPTOGRAPHY


- Slides: 44

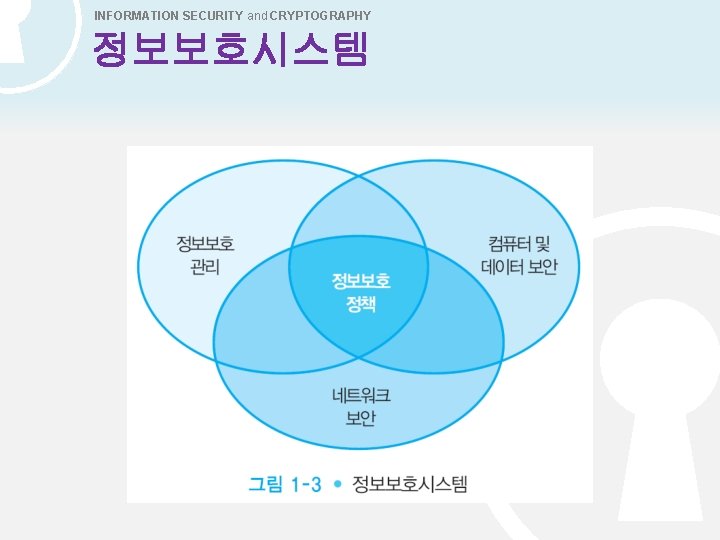
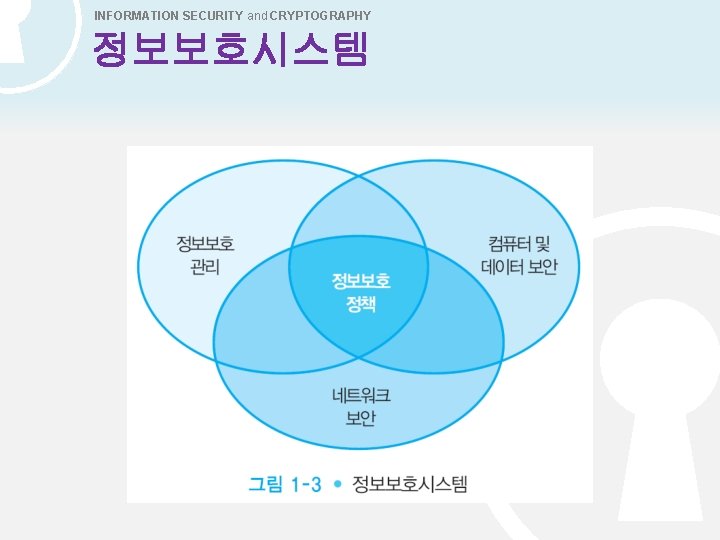
INFORMATION SECURITY and CRYPTOGRAPHY 정보보호시스템
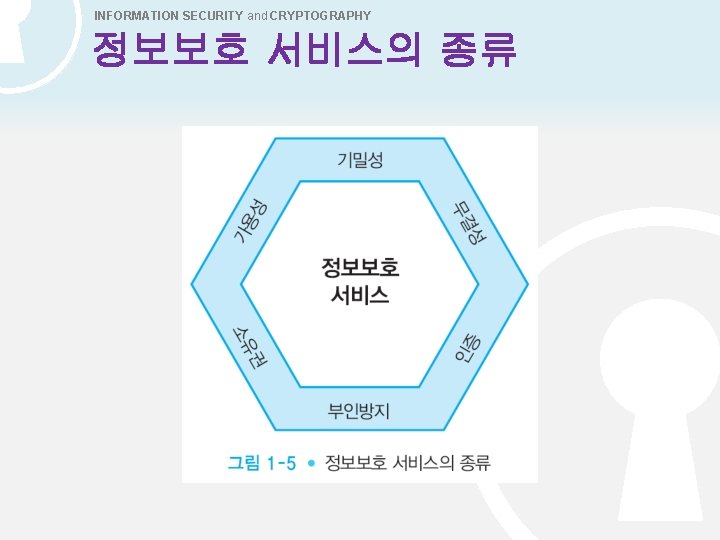
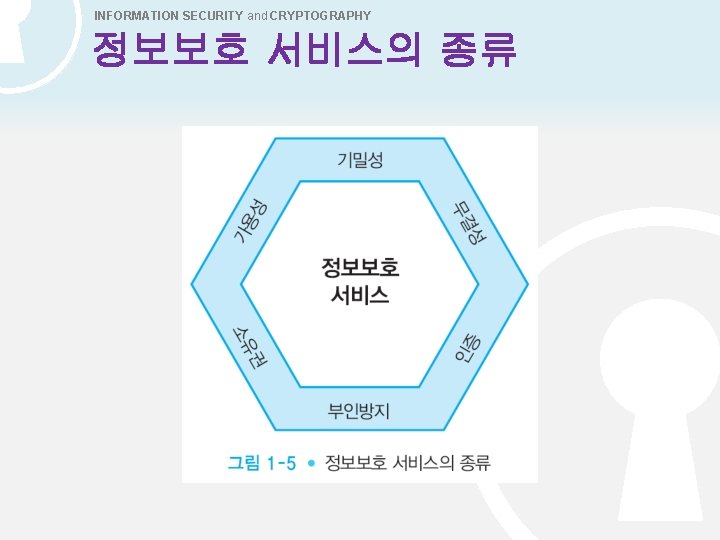
INFORMATION SECURITY and CRYPTOGRAPHY 정보보호 서비스의 종류
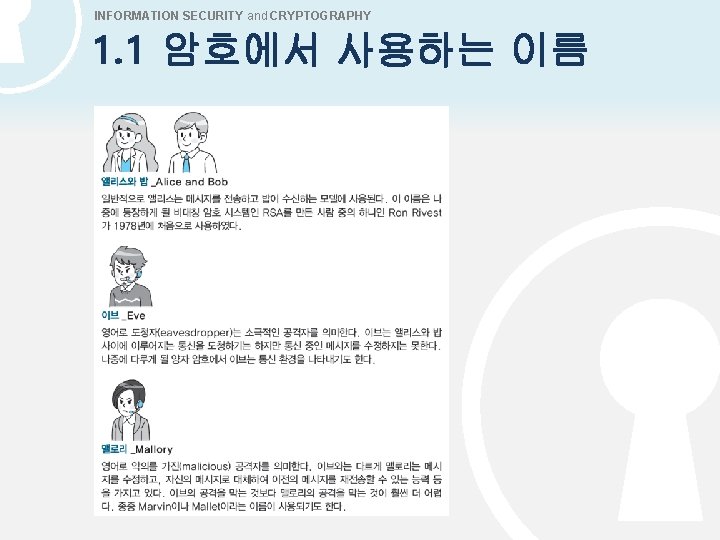
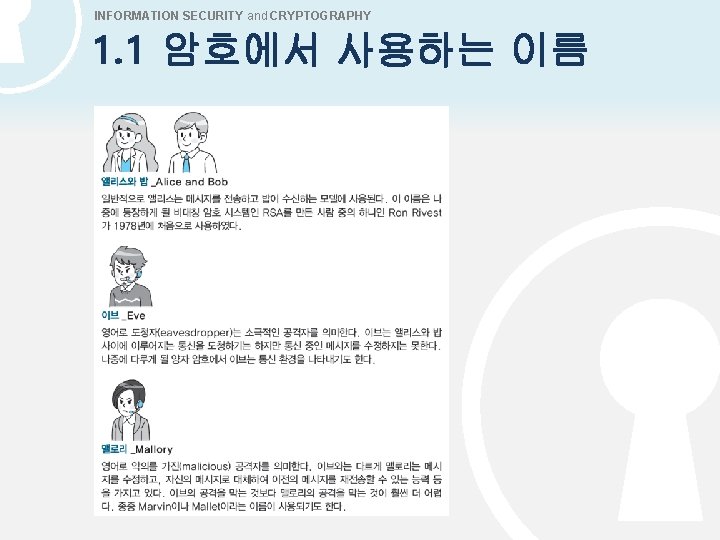
INFORMATION SECURITY and CRYPTOGRAPHY 1. 1 암호에서 사용하는 이름
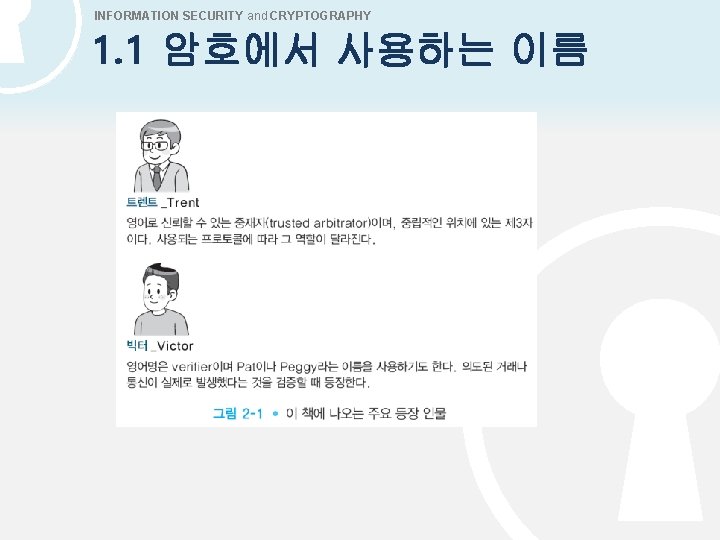
INFORMATION SECURITY and CRYPTOGRAPHY 1. 1 암호에서 사용하는 이름
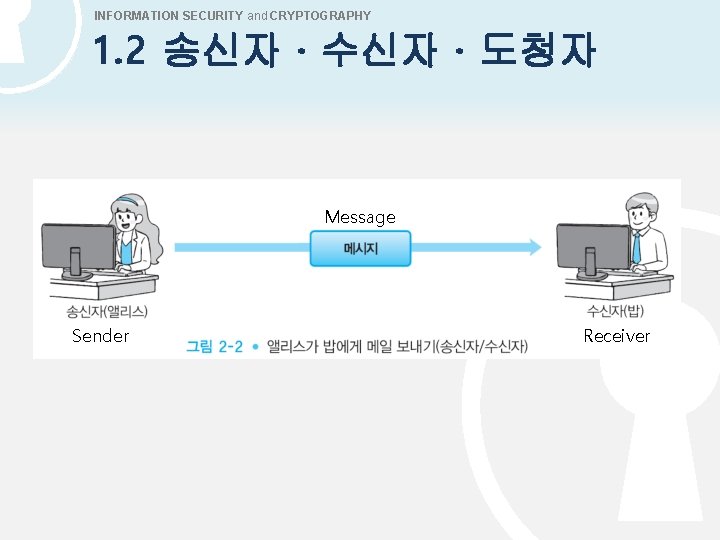
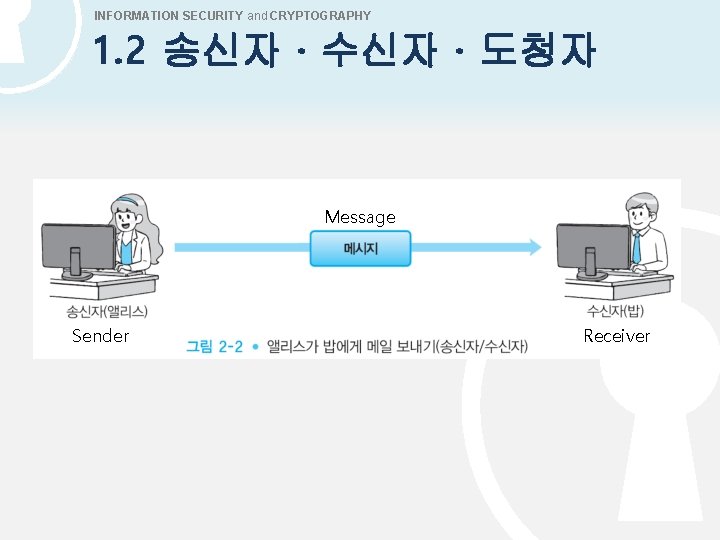
INFORMATION SECURITY and CRYPTOGRAPHY 1. 2 송신자 · 수신자 · 도청자 Message Sender Receiver
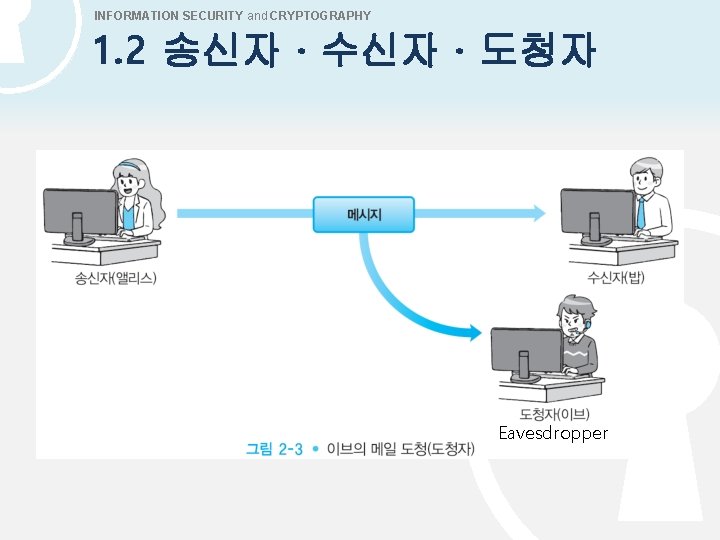
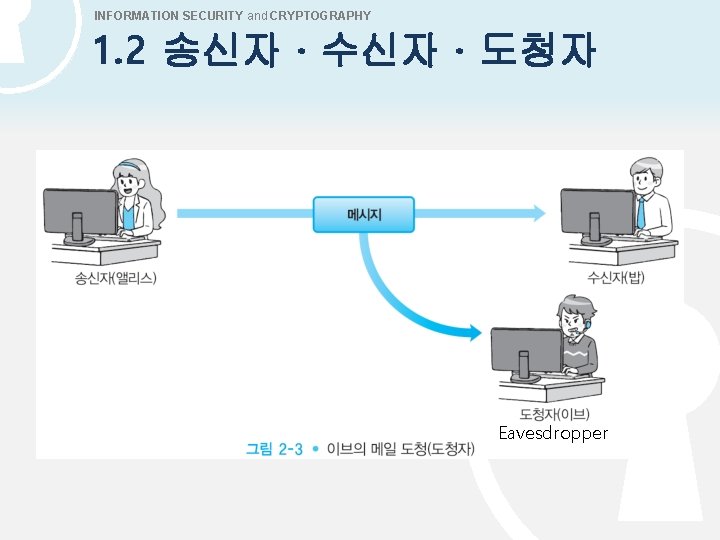
INFORMATION SECURITY and CRYPTOGRAPHY 1. 2 송신자 · 수신자 · 도청자 Eavesdropper
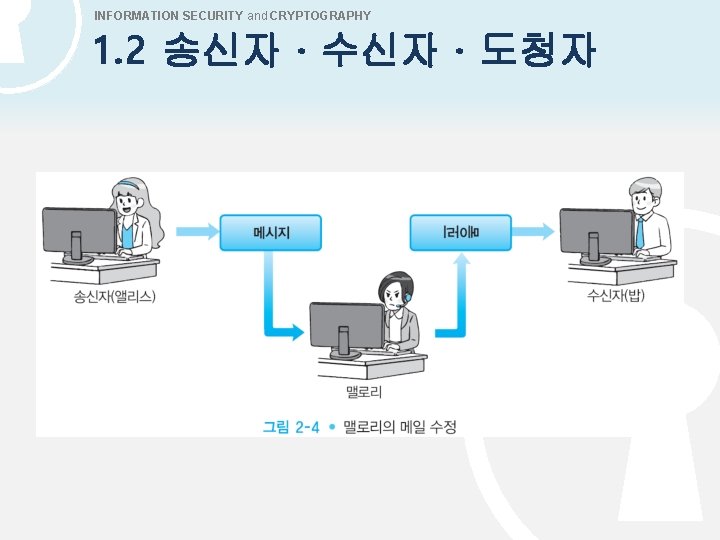
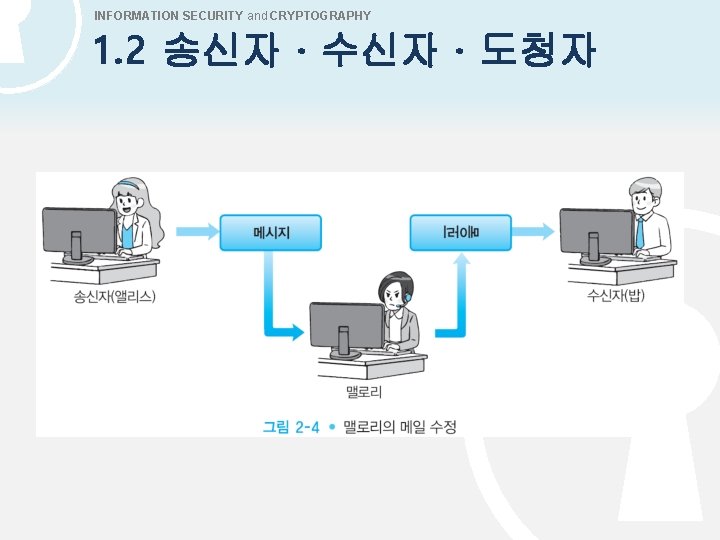
INFORMATION SECURITY and CRYPTOGRAPHY 1. 2 송신자 · 수신자 · 도청자
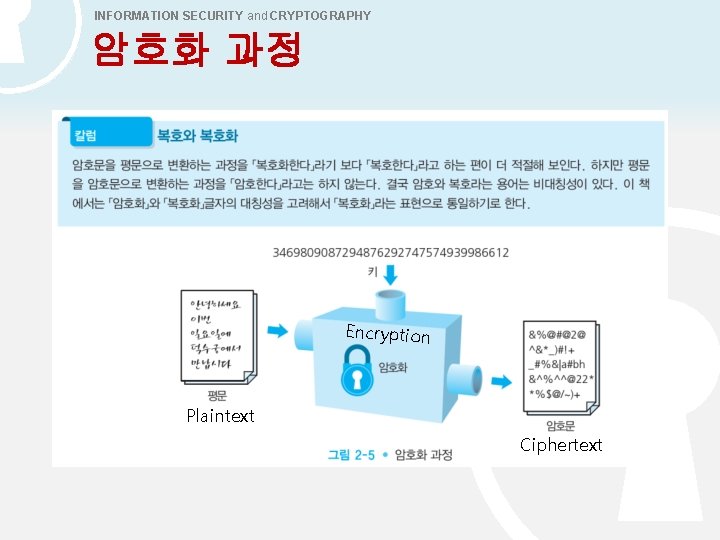
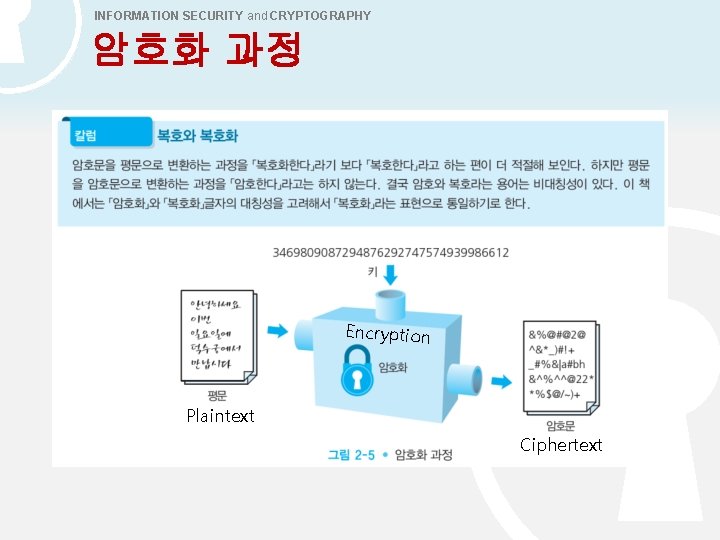
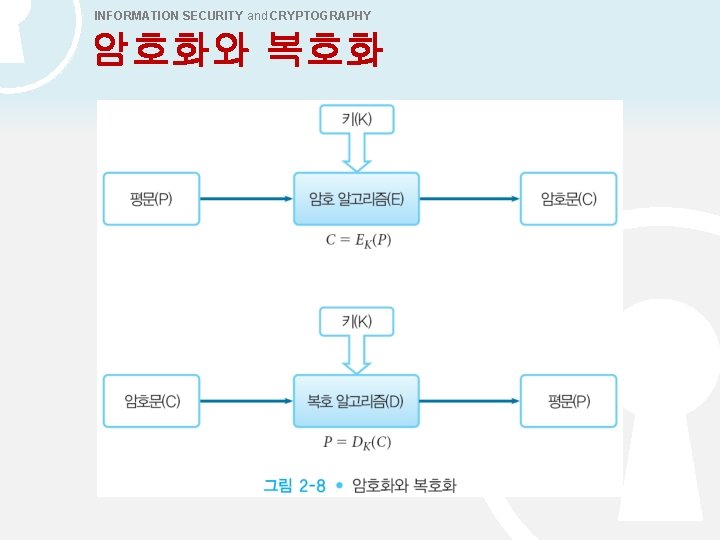
INFORMATION SECURITY and CRYPTOGRAPHY 암호화 과정 Encryption Plaintext Ciphertext
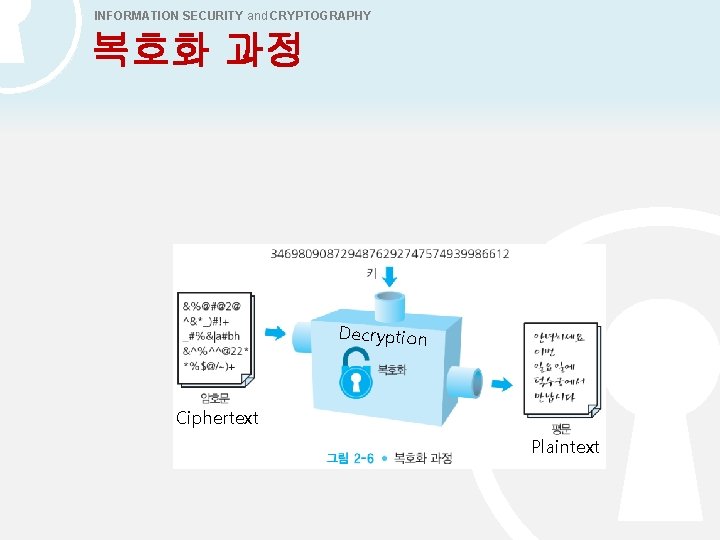
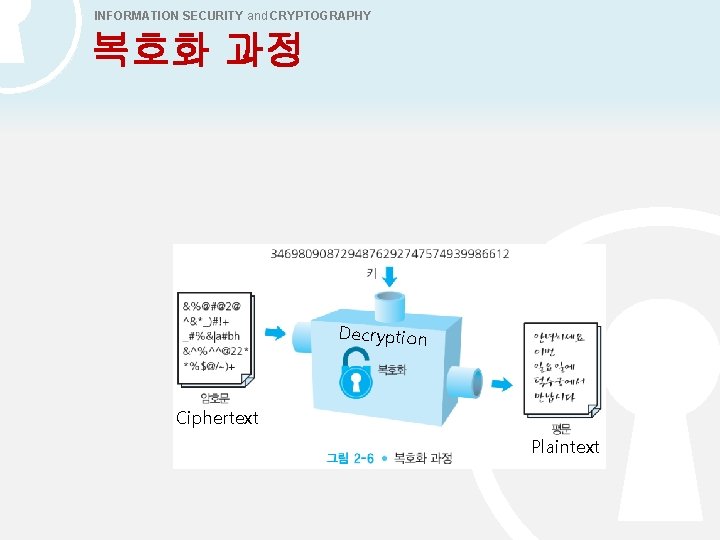
INFORMATION SECURITY and CRYPTOGRAPHY 복호화 과정 Decryption Ciphertext Plaintext
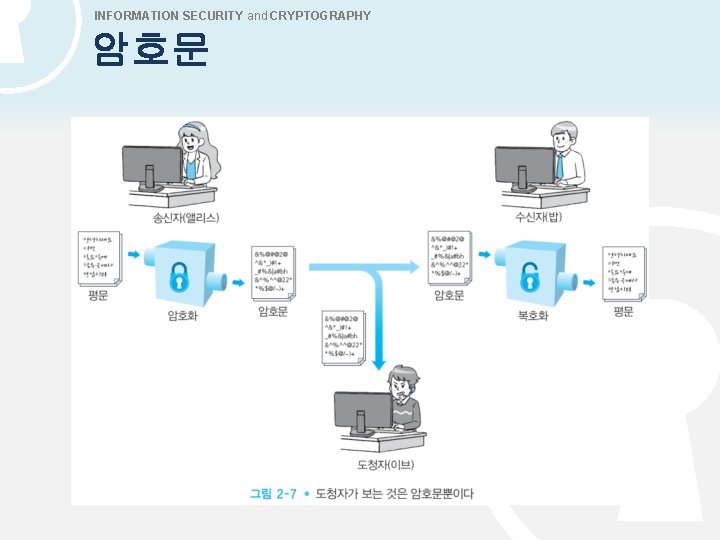
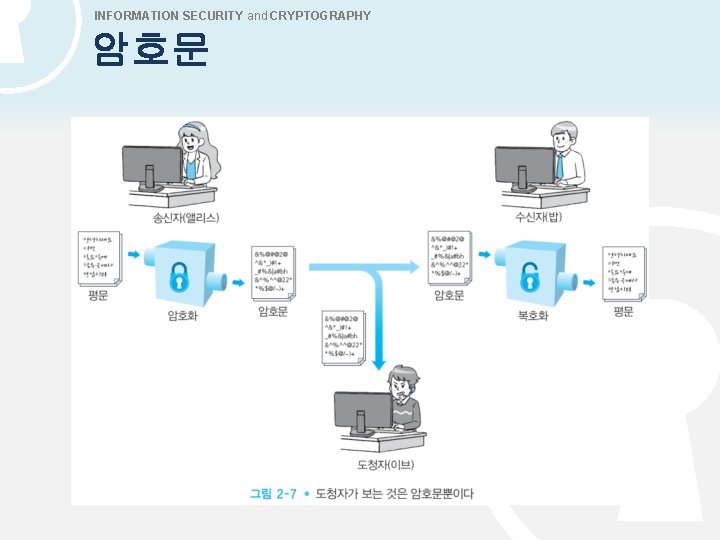
INFORMATION SECURITY and CRYPTOGRAPHY 암호문
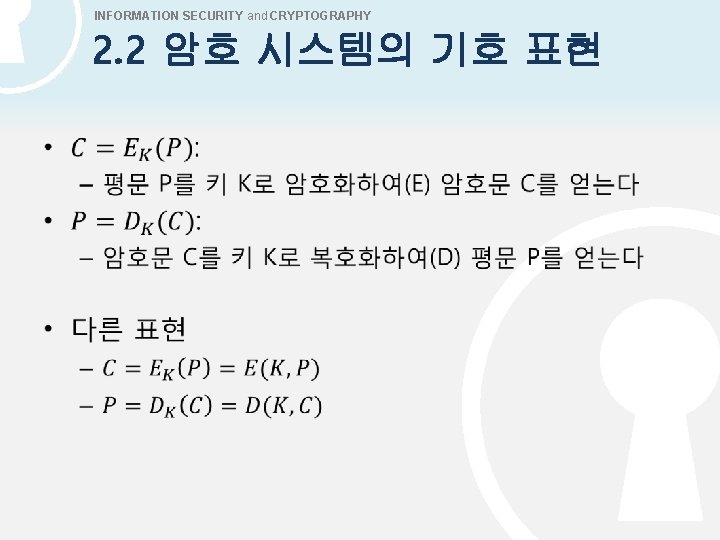
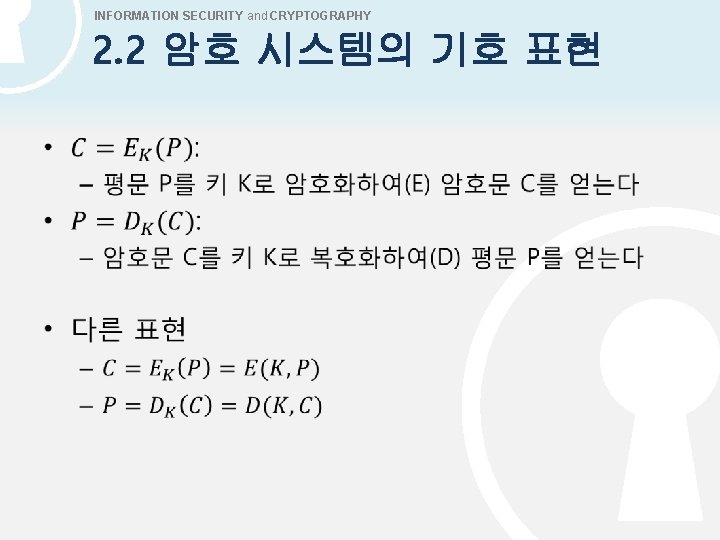
INFORMATION SECURITY and CRYPTOGRAPHY 2. 2 암호 시스템의 기호 표현 •
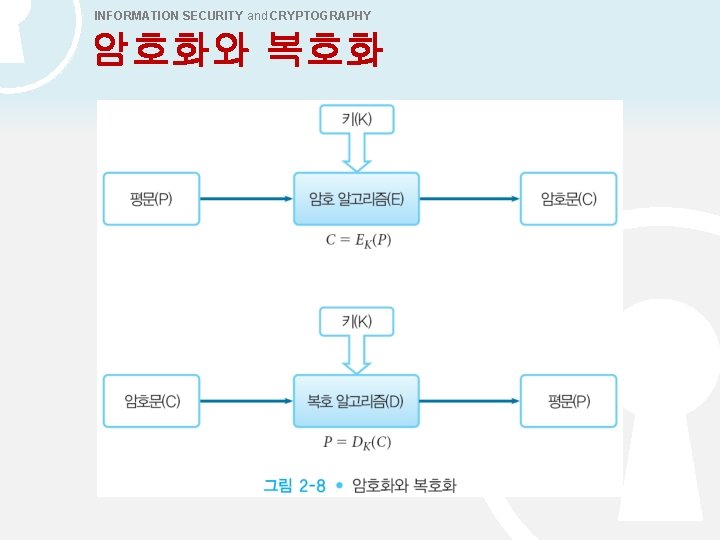
INFORMATION SECURITY and CRYPTOGRAPHY 암호화와 복호화
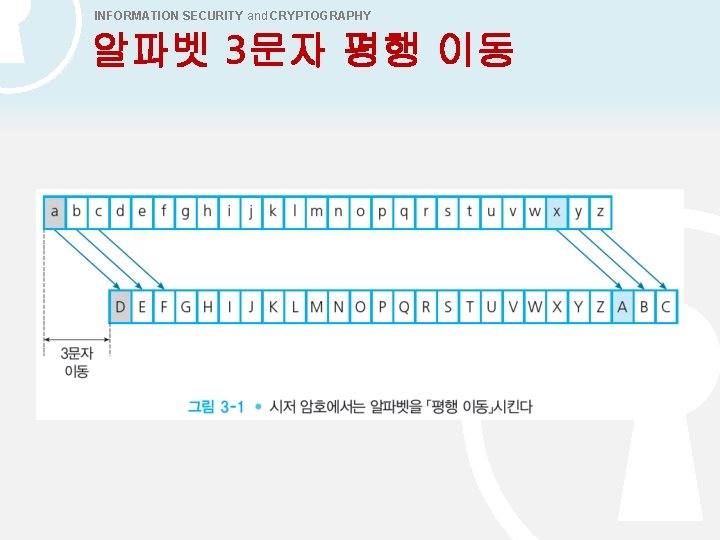
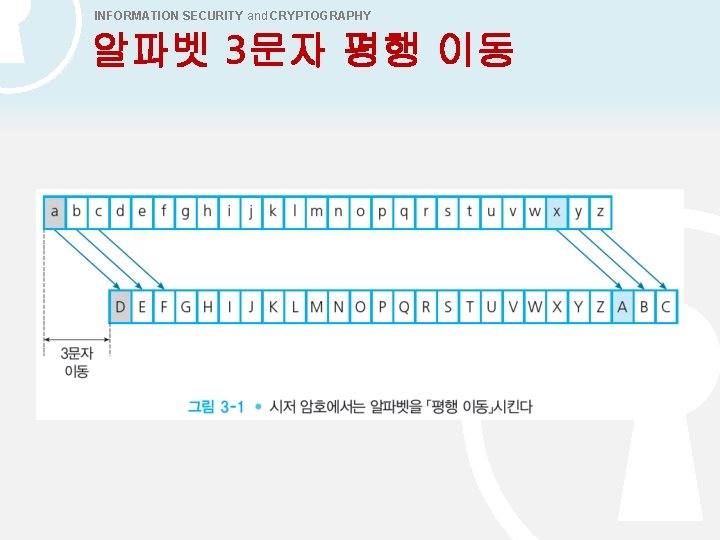
INFORMATION SECURITY and CRYPTOGRAPHY 알파벳 3문자 평행 이동
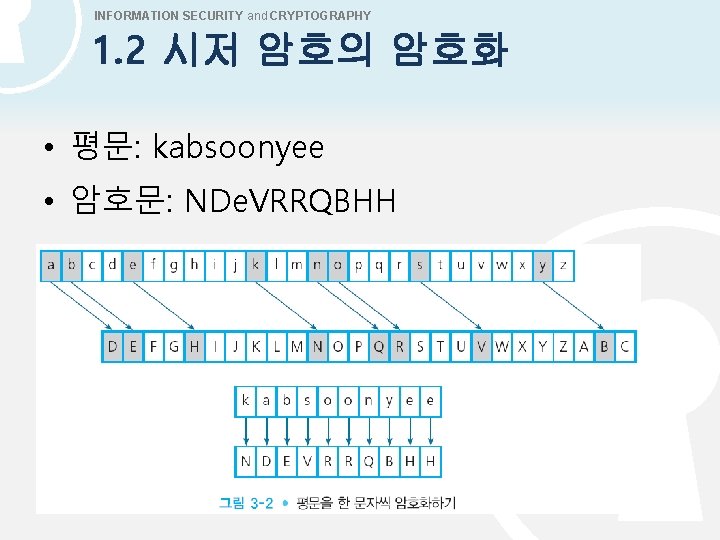
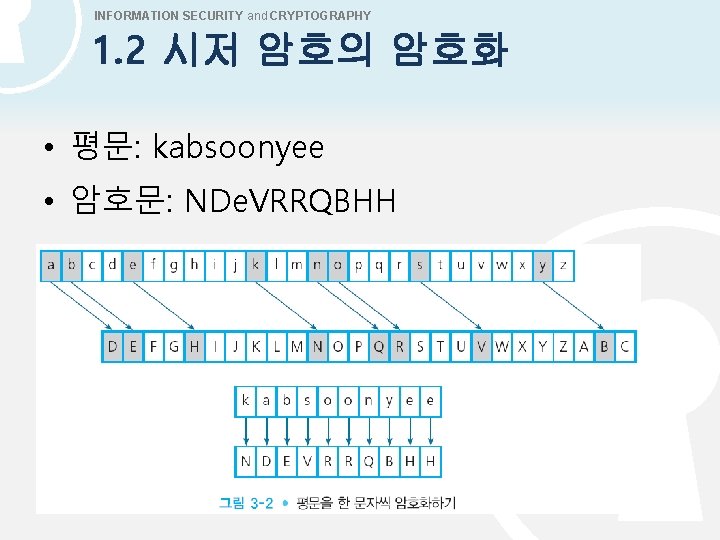
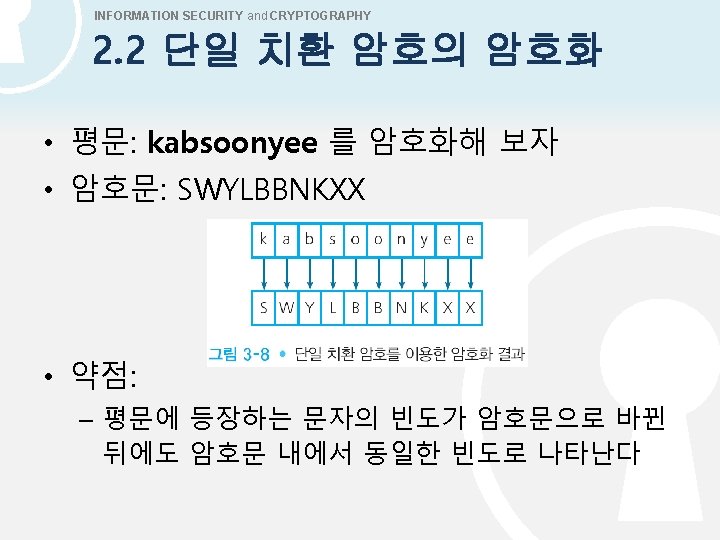
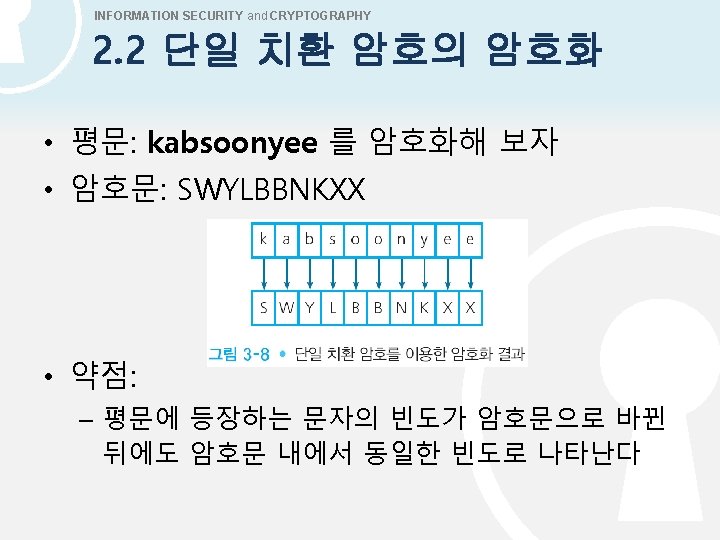
INFORMATION SECURITY and CRYPTOGRAPHY 1. 2 시저 암호의 암호화 • 평문: kabsoonyee • 암호문: NDe. VRRQBHH
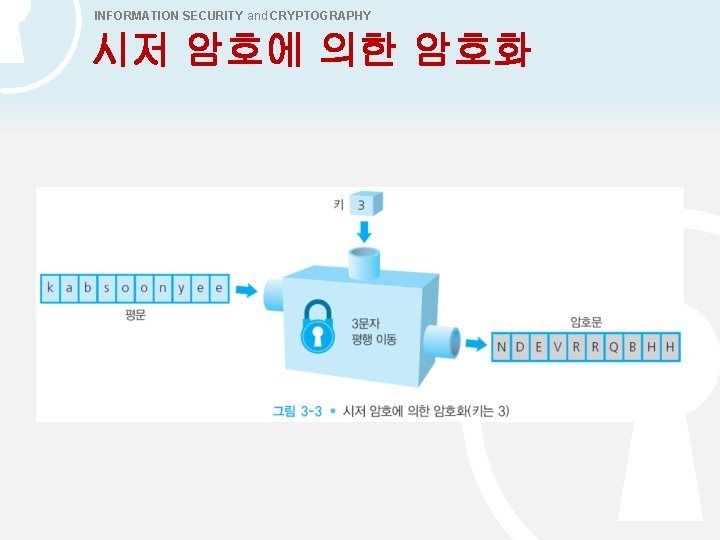
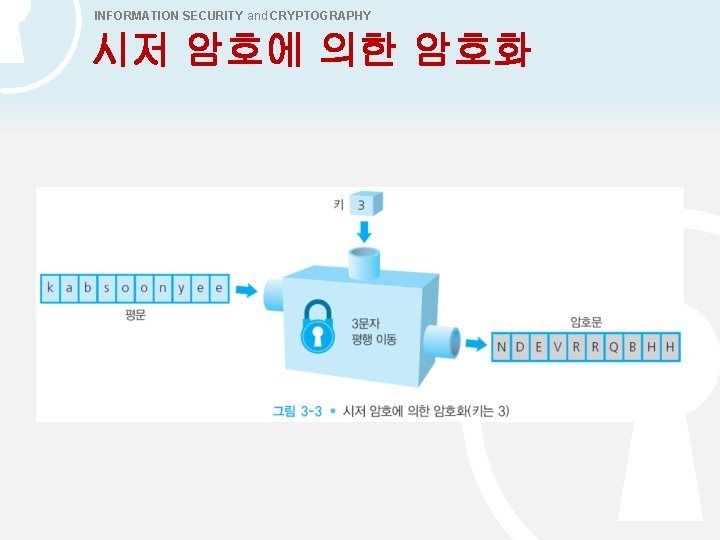
INFORMATION SECURITY and CRYPTOGRAPHY 시저 암호에 의한 암호화
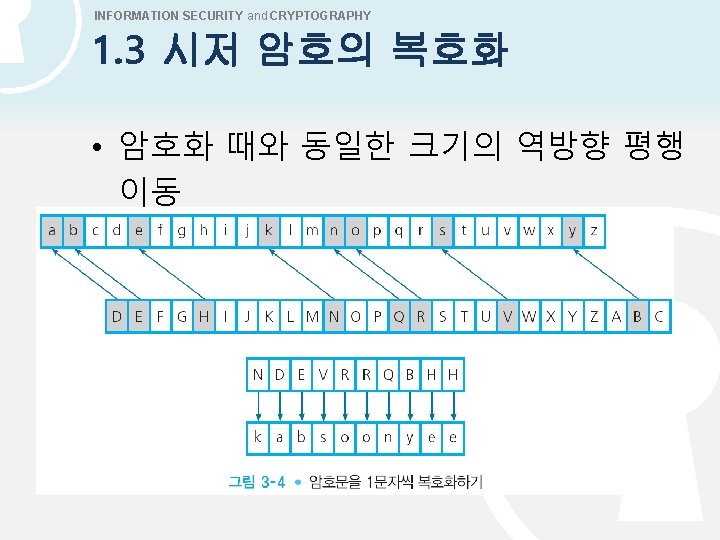

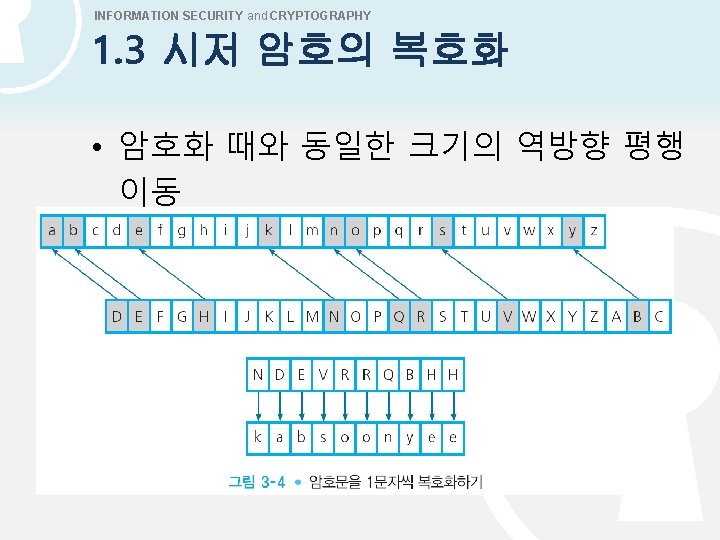
INFORMATION SECURITY and CRYPTOGRAPHY 시저 암호에 의한 복호화
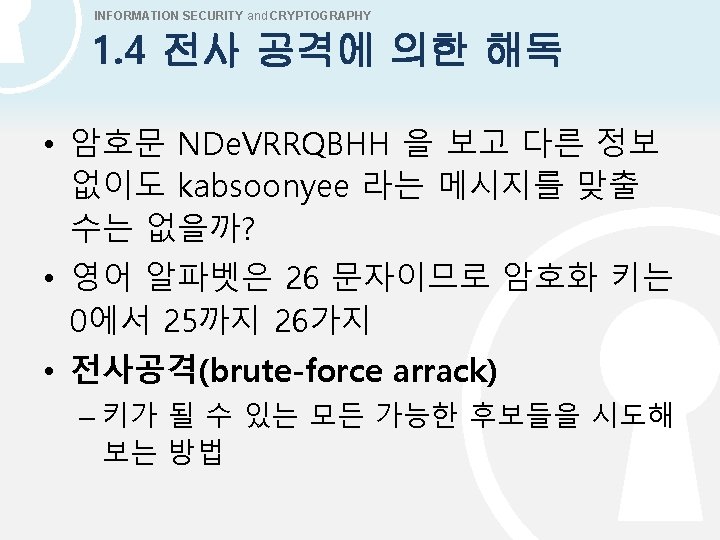
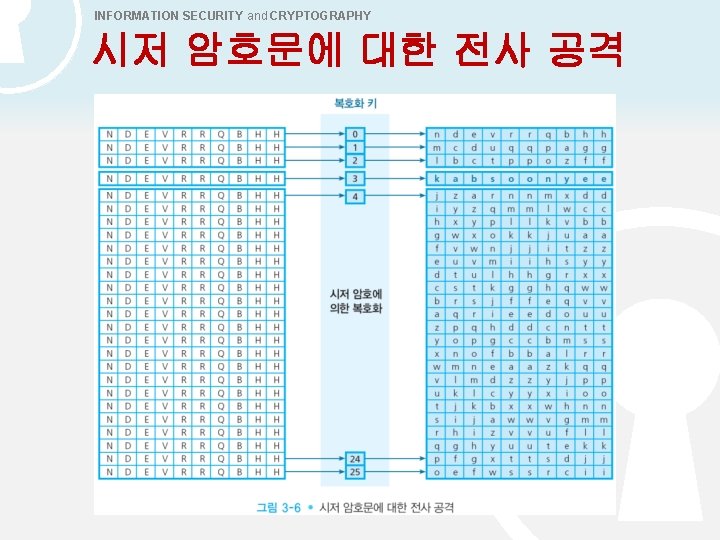
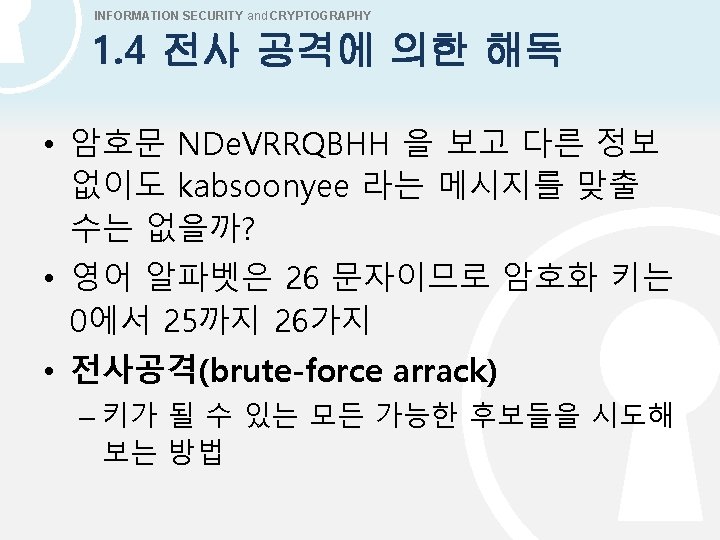
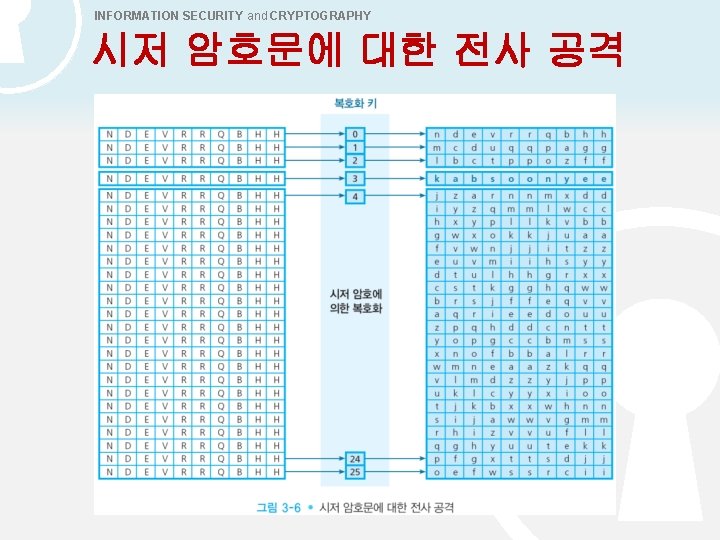
INFORMATION SECURITY and CRYPTOGRAPHY 시저 암호문에 대한 전사 공격
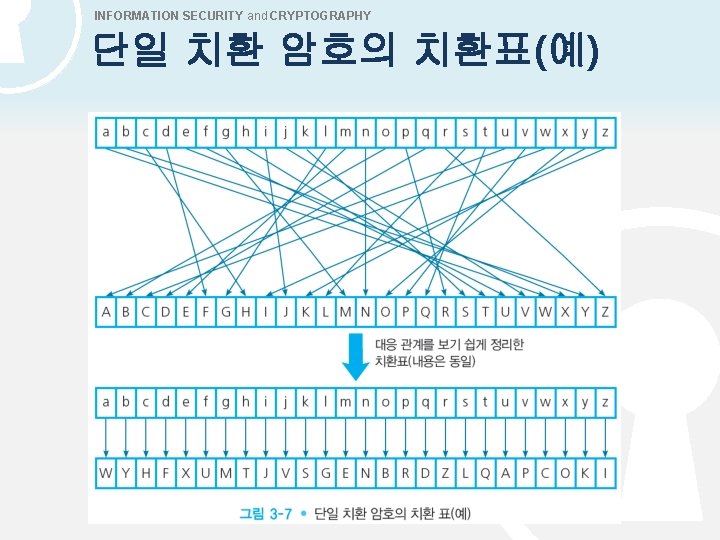
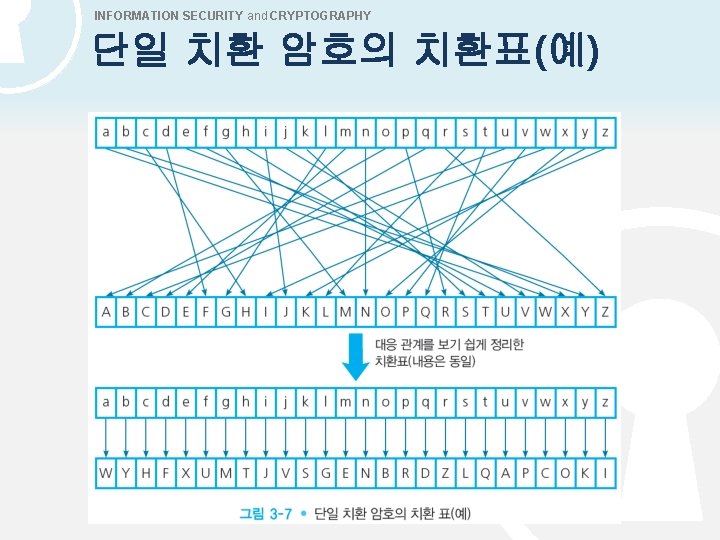
INFORMATION SECURITY and CRYPTOGRAPHY 단일 치환 암호의 치환표(예)
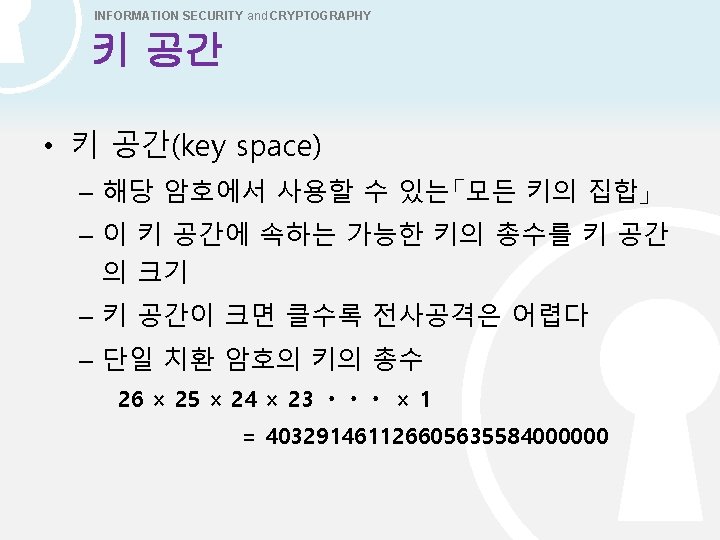
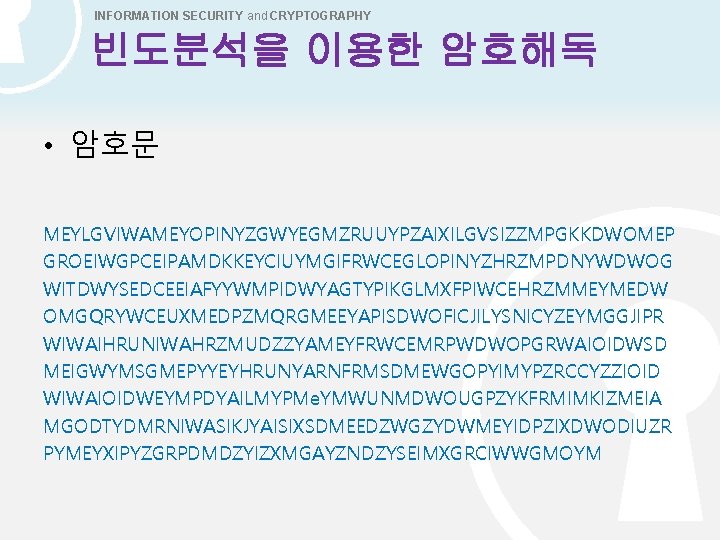
INFORMATION SECURITY and CRYPTOGRAPHY 빈도분석을 이용한 암호해독 • 암호문 MEYLGVIWAMEYOPINYZGWYEGMZRUUYPZAIXILGVSIZZMPGKKDWOMEP GROEIWGPCEIPAMDKKEYCIUYMGIFRWCEGLOPINYZHRZMPDNYWDWOG WITDWYSEDCEEIAFYYWMPIDWYAGTYPIKGLMXFPIWCEHRZMMEYMEDW OMGQRYWCEUXMEDPZMQRGMEEYAPISDWOFICJILYSNICYZEYMGGJIPR WIWAIHRUNIWAHRZMUDZZYAMEYFRWCEMRPWDWOPGRWAIOIDWSD MEIGWYMSGMEPYYEYHRUNYARNFRMSDMEWGOPYIMYPZRCCYZZIOID WIWAIOIDWEYMPDYAILMYPMe. YMWUNMDWOUGPZYKFRMIMKIZMEIA MGODTYDMRNIWASIKJYAISIXSDMEEDZWGZYDWMEYIDPZIXDWODIUZR PYMEYXIPYZGRPDMDZYIZXMGAYZNDZYSEIMXGRCIWWGMOYM
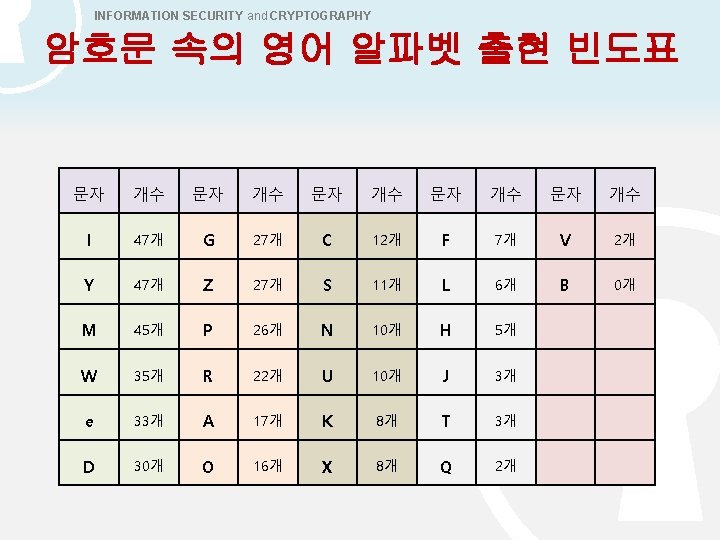
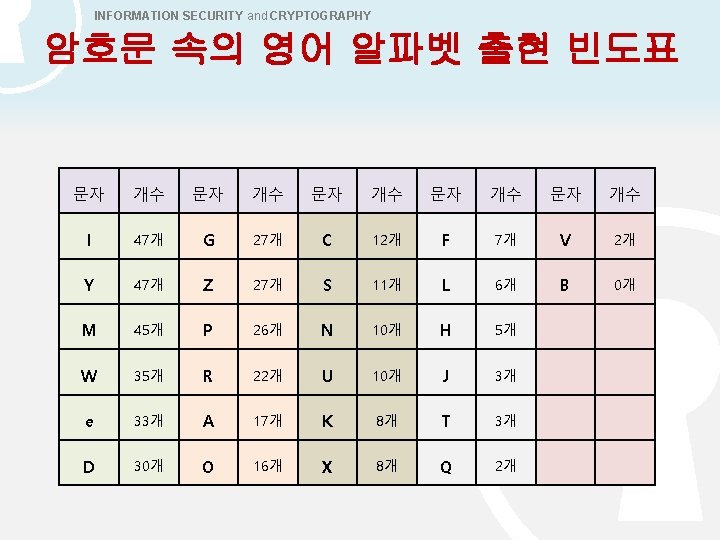
INFORMATION SECURITY and CRYPTOGRAPHY 암호문 속의 영어 알파벳 출현 빈도표 문자 개수 문자 개수 I 47개 G 27개 C 12개 F 7개 V 2개 Y 47개 Z 27개 S 11개 L 6개 B 0개 M 45개 P 26개 N 10개 H 5개 W 35개 R 22개 U 10개 J 3개 e 33개 A 17개 K 8개 T 3개 D 30개 O 16개 X 8개 Q 2개
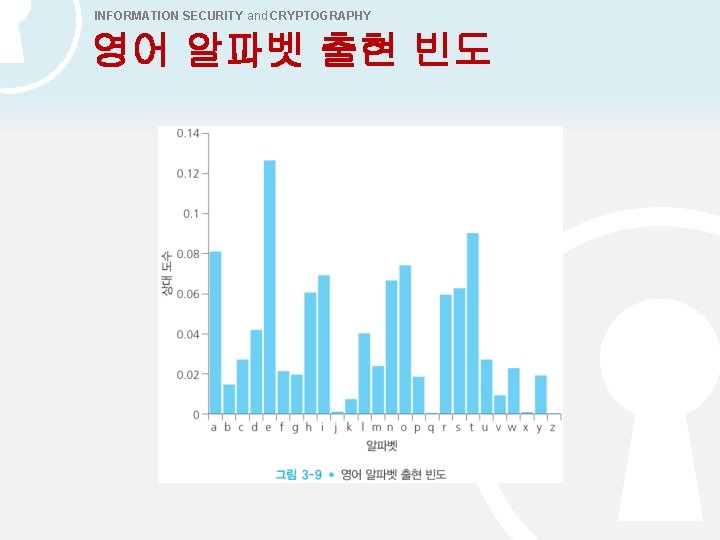
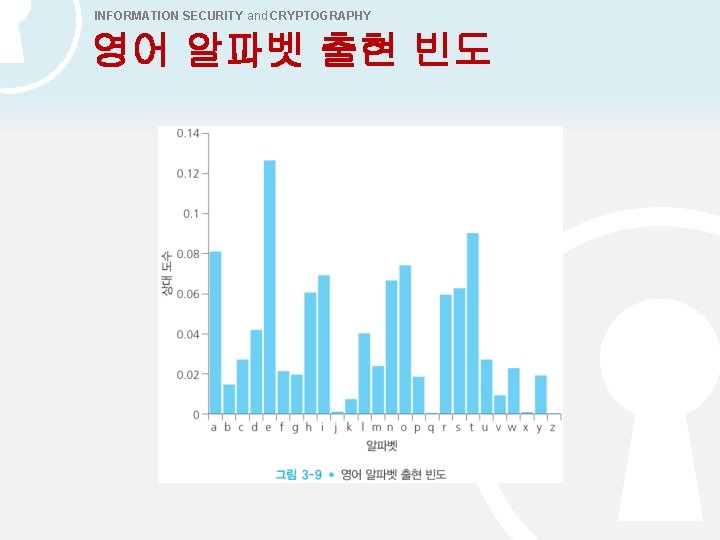
INFORMATION SECURITY and CRYPTOGRAPHY 영어 알파벳 출현 빈도
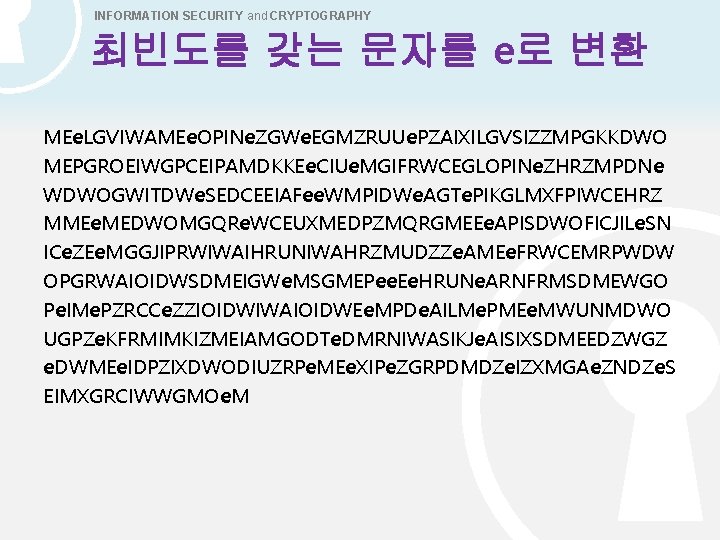
INFORMATION SECURITY and CRYPTOGRAPHY 최빈도를 갖는 문자를 e로 변환 MEe. LGVIWAMEe. OPINe. ZGWe. EGMZRUUe. PZAIXILGVSIZZMPGKKDWO MEPGROEIWGPCEIPAMDKKEe. CIUe. MGIFRWCEGLOPINe. ZHRZMPDNe WDWOGWITDWe. SEDCEEIAFee. WMPIDWe. AGTe. PIKGLMXFPIWCEHRZ MMEe. MEDWOMGQRe. WCEUXMEDPZMQRGMEEe. APISDWOFICJILe. SN ICe. ZEe. MGGJIPRWIWAIHRUNIWAHRZMUDZZe. AMEe. FRWCEMRPWDW OPGRWAIOIDWSDMEIGWe. MSGMEPee. Ee. HRUNe. ARNFRMSDMEWGO Pe. IMe. PZRCCe. ZZIOIDWIWAIOIDWEe. MPDe. AILMe. PMEe. MWUNMDWO UGPZe. KFRMIMKIZMEIAMGODTe. DMRNIWASIKJe. AISIXSDMEEDZWGZ e. DWMEe. IDPZIXDWODIUZRPe. MEe. XIPe. ZGRPDMDZe. IZXMGAe. ZNDZe. S EIMXGRCIWWGMOe. M
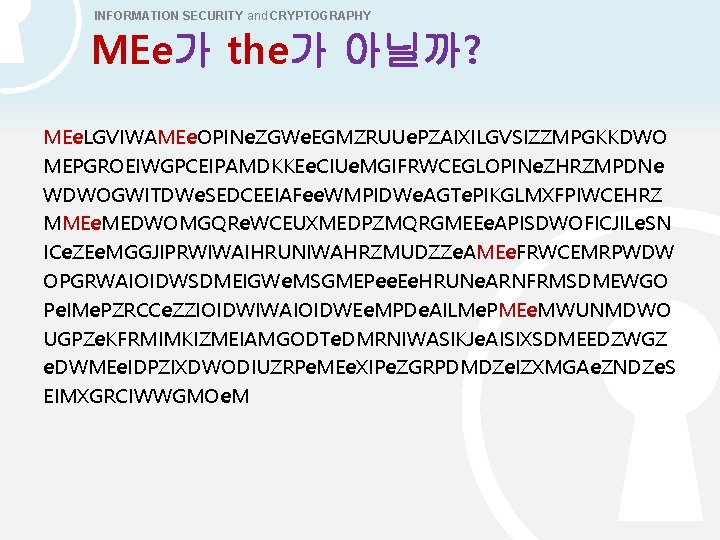
INFORMATION SECURITY and CRYPTOGRAPHY MEe가 the가 아닐까? MEe. LGVIWAMEe. OPINe. ZGWe. EGMZRUUe. PZAIXILGVSIZZMPGKKDWO MEPGROEIWGPCEIPAMDKKEe. CIUe. MGIFRWCEGLOPINe. ZHRZMPDNe WDWOGWITDWe. SEDCEEIAFee. WMPIDWe. AGTe. PIKGLMXFPIWCEHRZ MMEe. MEDWOMGQRe. WCEUXMEDPZMQRGMEEe. APISDWOFICJILe. SN ICe. ZEe. MGGJIPRWIWAIHRUNIWAHRZMUDZZe. AMEe. FRWCEMRPWDW OPGRWAIOIDWSDMEIGWe. MSGMEPee. Ee. HRUNe. ARNFRMSDMEWGO Pe. IMe. PZRCCe. ZZIOIDWIWAIOIDWEe. MPDe. AILMe. PMEe. MWUNMDWO UGPZe. KFRMIMKIZMEIAMGODTe. DMRNIWASIKJe. AISIXSDMEEDZWGZ e. DWMEe. IDPZIXDWODIUZRPe. MEe. XIPe. ZGRPDMDZe. IZXMGAe. ZNDZe. S EIMXGRCIWWGMOe. M
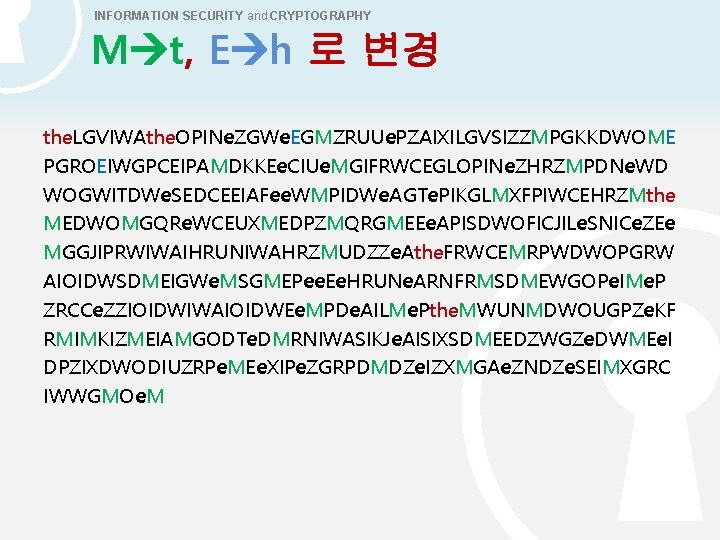
INFORMATION SECURITY and CRYPTOGRAPHY M t, E h 로 변경 the. LGVIWAthe. OPINe. ZGWe. EGMZRUUe. PZAIXILGVSIZZMPGKKDWOME PGROEIWGPCEIPAMDKKEe. CIUe. MGIFRWCEGLOPINe. ZHRZMPDNe. WD WOGWITDWe. SEDCEEIAFee. WMPIDWe. AGTe. PIKGLMXFPIWCEHRZMthe MEDWOMGQRe. WCEUXMEDPZMQRGMEEe. APISDWOFICJILe. SNICe. ZEe MGGJIPRWIWAIHRUNIWAHRZMUDZZe. Athe. FRWCEMRPWDWOPGRW AIOIDWSDMEIGWe. MSGMEPee. Ee. HRUNe. ARNFRMSDMEWGOPe. IMe. P ZRCCe. ZZIOIDWIWAIOIDWEe. MPDe. AILMe. Pthe. MWUNMDWOUGPZe. KF RMIMKIZMEIAMGODTe. DMRNIWASIKJe. AISIXSDMEEDZWGZe. DWMEe. I DPZIXDWODIUZRPe. MEe. XIPe. ZGRPDMDZe. IZXMGAe. ZNDZe. SEIMXGRC IWWGMOe. M
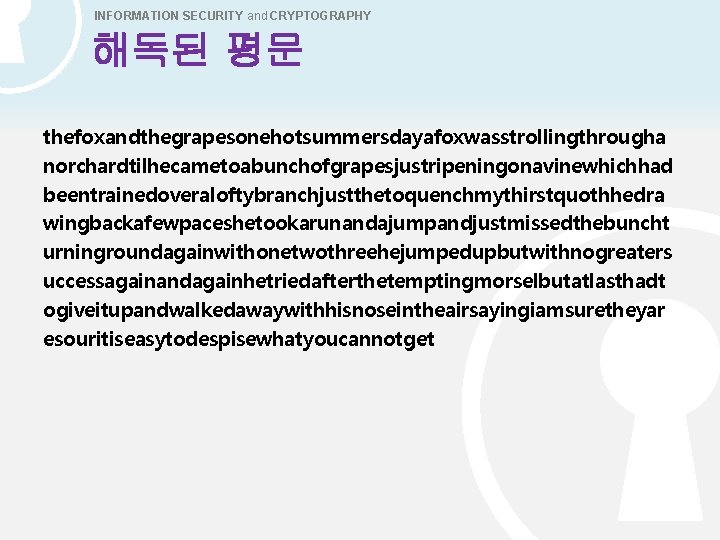
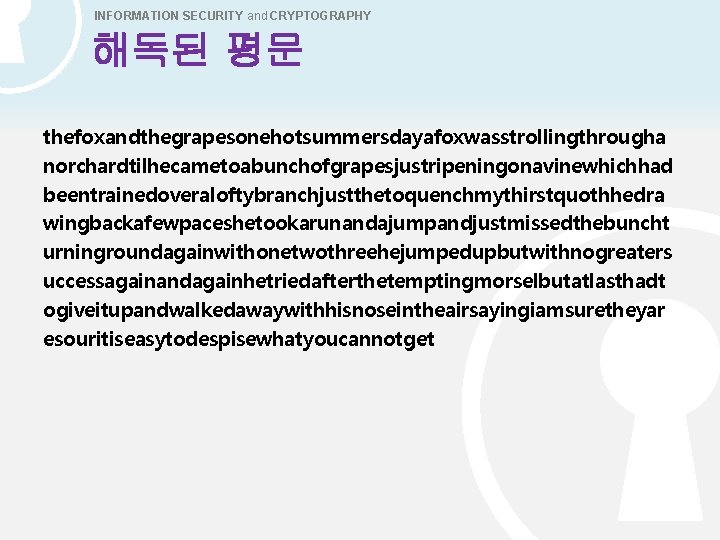
INFORMATION SECURITY and CRYPTOGRAPHY 해독된 평문 thefoxandthegrapesonehotsummersdayafoxwasstrollingthrougha norchardtilhecametoabunchofgrapesjustripeningonavinewhichhad beentrainedoveraloftybranchjustthetoquenchmythirstquothhedra wingbackafewpaceshetookarunandajumpandjustmissedthebuncht urningroundagainwithonetwothreehejumpedupbutwithnogreaters uccessagainandagainhetriedafterthetemptingmorselbutatlasthadt ogiveitupandwalkedawaywithhisnoseintheairsayingiamsuretheyar esouritiseasytodespisewhatyoucannotget
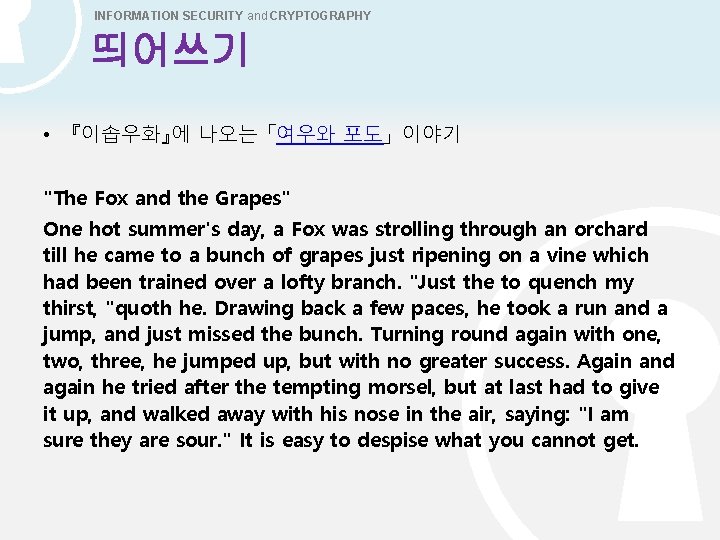
INFORMATION SECURITY and CRYPTOGRAPHY 띄어쓰기 • 『이솝우화』에 나오는 「여우와 포도」 이야기 "The Fox and the Grapes" One hot summer's day, a Fox was strolling through an orchard till he came to a bunch of grapes just ripening on a vine which had been trained over a lofty branch. "Just the to quench my thirst, "quoth he. Drawing back a few paces, he took a run and a jump, and just missed the bunch. Turning round again with one, two, three, he jumped up, but with no greater success. Again and again he tried after the tempting morsel, but at last had to give it up, and walked away with his nose in the air, saying: "I am sure they are sour. " It is easy to despise what you cannot get.
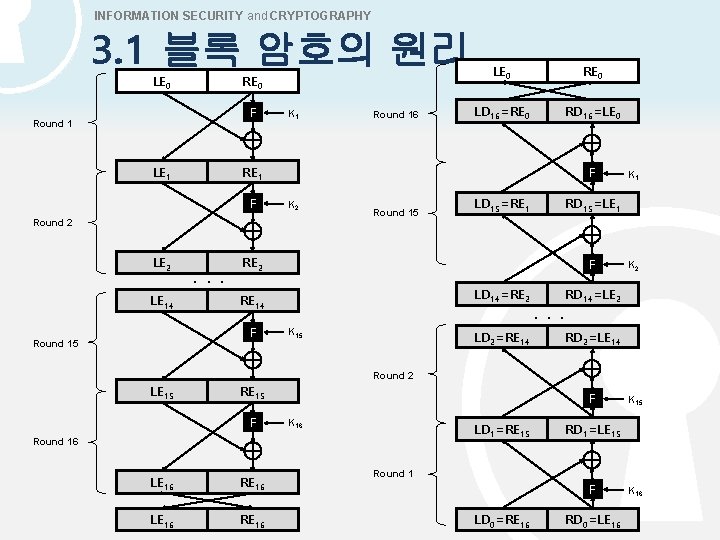
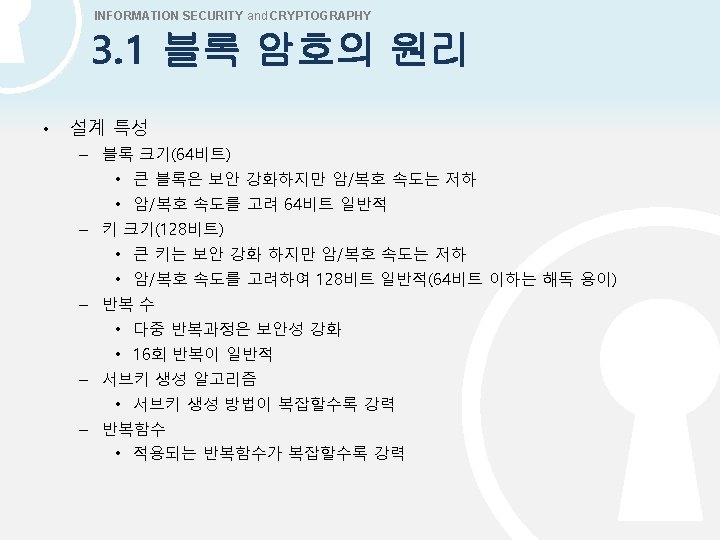
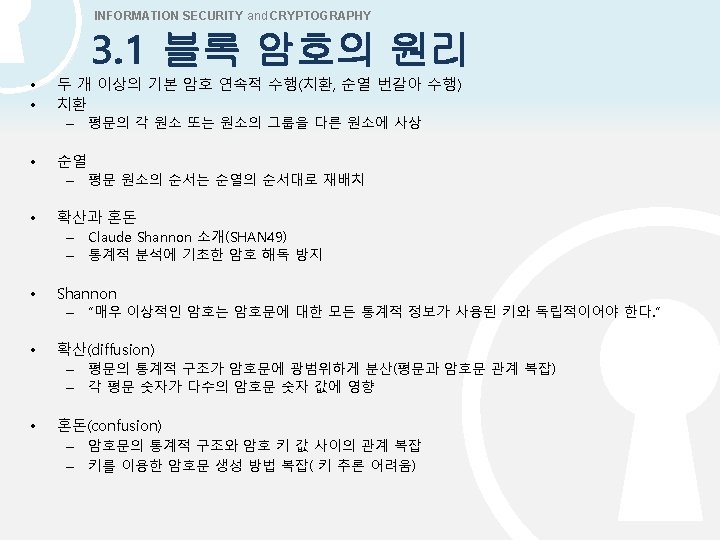
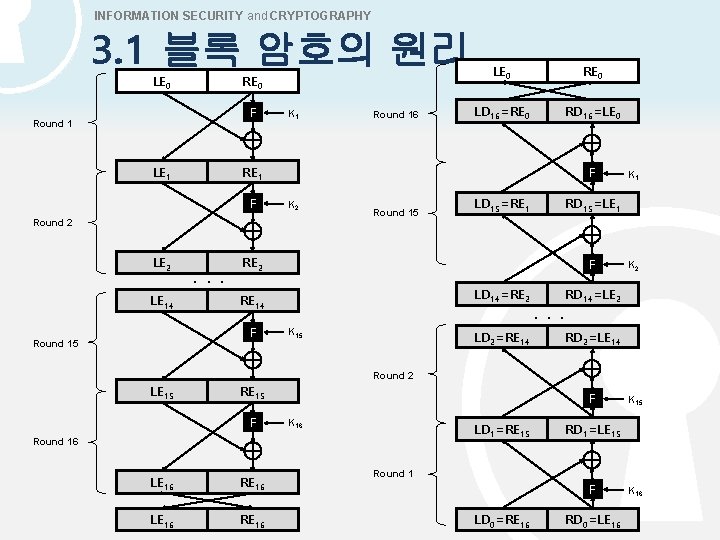
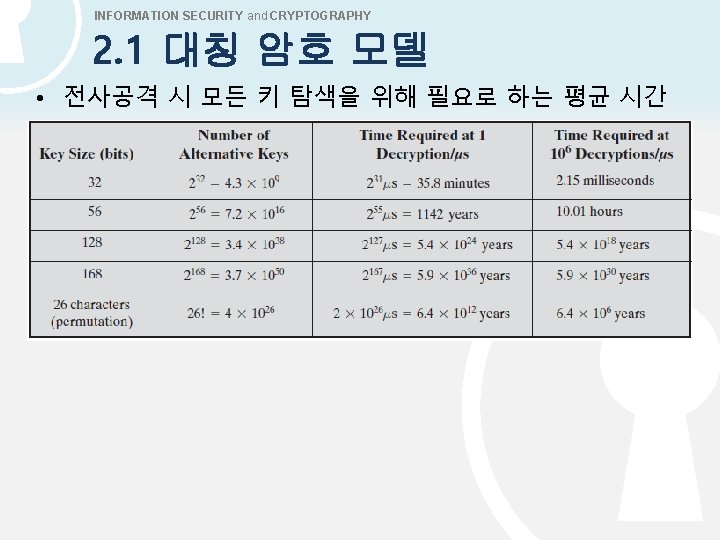
INFORMATION SECURITY and CRYPTOGRAPHY 3. 1 블록 암호의 원리 LE 0 RE 0 F Round 1 LE 1 K 1 RD 16=LE 0 K 2 . . . Round 15 LD 15=RE 1 F LD 14=RE 2 RE 14 K 15 LD 2=RE 14 K 1 RD 15=LE 1 RE 2 F Round 15 LD 16=RE 0 F Round 2 LE 14 RE 0 RE 1 F LE 2 Round 16 LE 0 K 2 RD 14=LE 2 . . . RD 2=LE 14 Round 2 LE 15 RE 15 F F K 16 LD 1=RE 15 Round 16 LE 16 RE 16 K 15 RD 1=LE 15 Round 1 F LD 0=RE 16 RD 0=LE 16 K 16