Information Protection and Recovery with Reversible Data Hiding
Information Protection and Recovery with Reversible Data Hiding Hsiang-Cheh Huang, Yu-Hsiu Huang, Jeng-Shyang Pan, Yuh-Yih Lu National University of Kaohsiung, Taiwan, R. O. C. Intelligent Information Hiding and Multimedia Signal Processing, 2007. IIHMSP 2007. Third International Conference on Volume 2, 26 -28 Nov. 2007 Page(s): 461 - 464 Reporter 10/25/2021 : Chien-Ting Kuo
Outline 1. Introduction n 2. Preliminaries n 3. Proposed Algorithm n 4. Experimental Results n 5. Conclusions n 2
1. Introduction For reversible data hiding, both the hidden data and the original multimedia content can be extracted n we employ the reversible data hiding techniques to hide the information to be mosaicked in advance. n 3
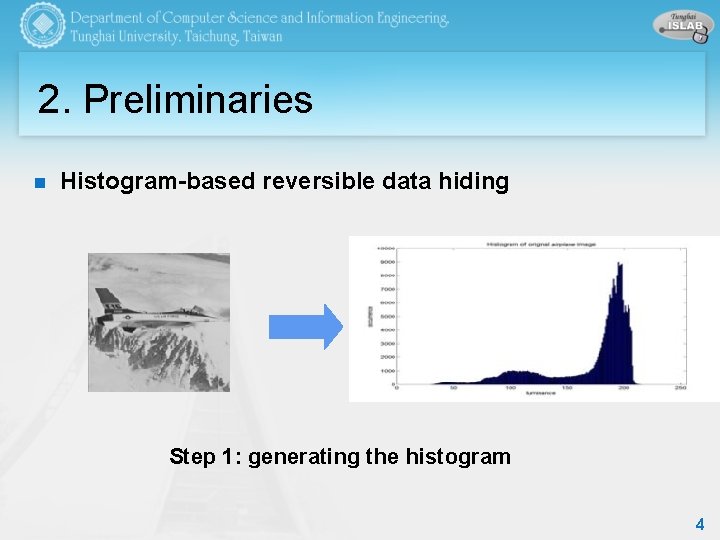
2. Preliminaries n Histogram-based reversible data hiding Step 1: generating the histogram 4
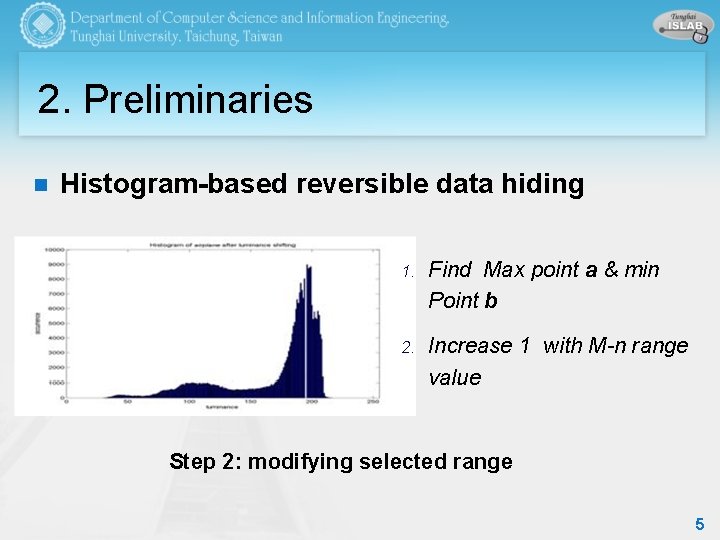
2. Preliminaries n Histogram-based reversible data hiding 1. Find Max point a & min Point b 2. Increase 1 with M-n range value Step 2: modifying selected range 5
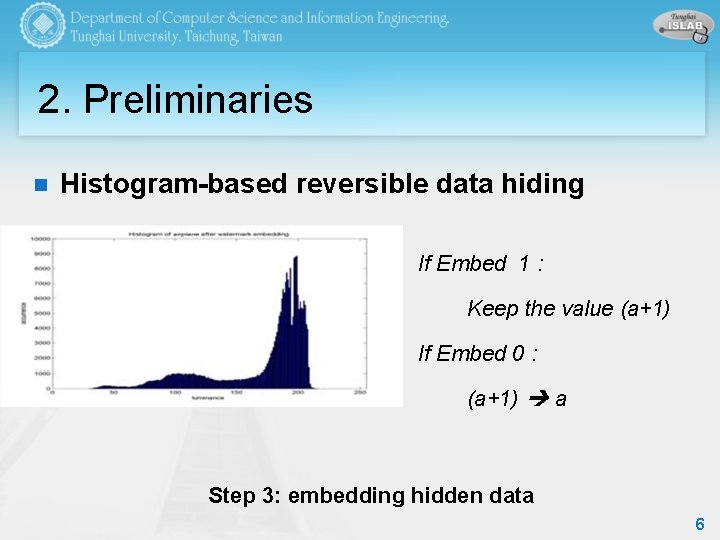
2. Preliminaries n Histogram-based reversible data hiding If Embed 1 : Keep the value (a+1) If Embed 0 : (a+1) a Step 3: embedding hidden data 6
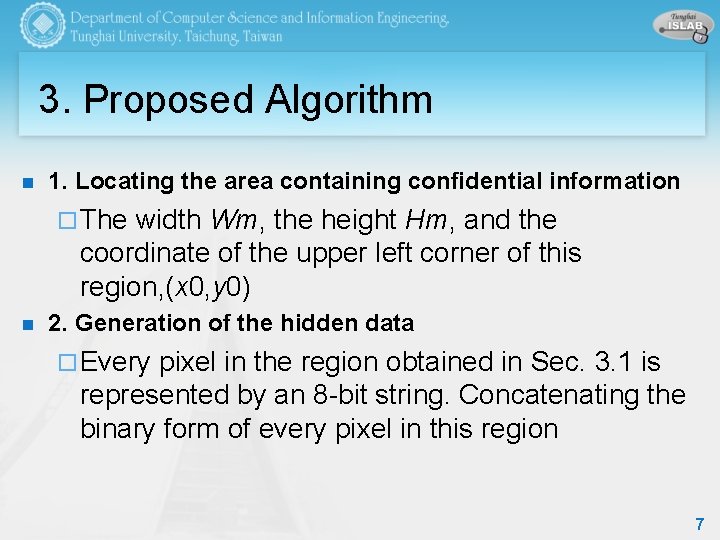
3. Proposed Algorithm n 1. Locating the area containing confidential information ¨ The width Wm, the height Hm, and the coordinate of the upper left corner of this region, (x 0, y 0) n 2. Generation of the hidden data ¨ Every pixel in the region obtained in Sec. 3. 1 is represented by an 8 -bit string. Concatenating the binary form of every pixel in this region 7
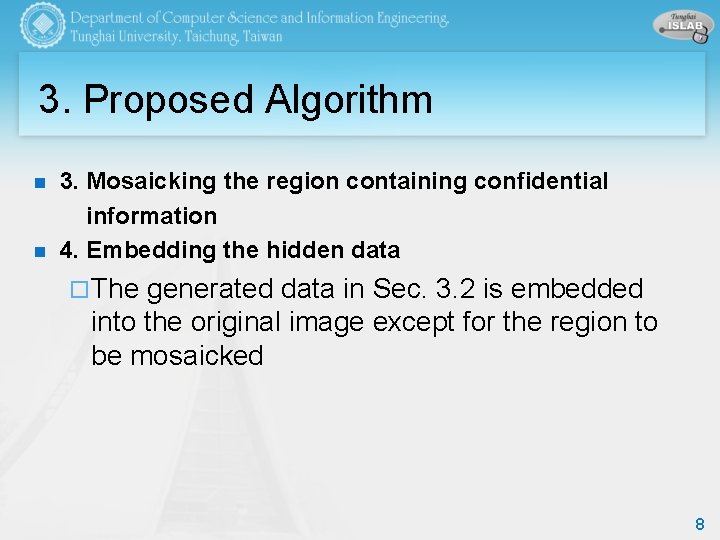
3. Proposed Algorithm n n 3. Mosaicking the region containing confidential information 4. Embedding the hidden data ¨ The generated data in Sec. 3. 2 is embedded into the original image except for the region to be mosaicked 8
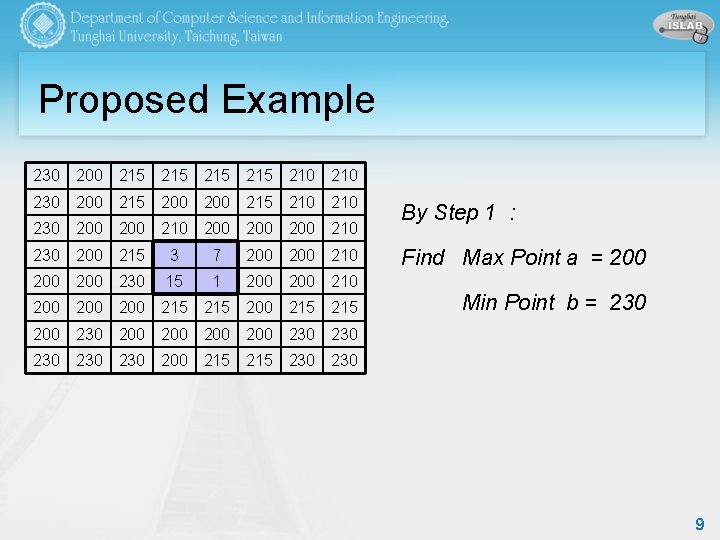
Proposed Example 230 200 215 215 210 230 200 215 210 230 200 210 200 200 210 230 200 215 3 7 200 210 200 230 15 1 200 210 200 200 215 215 By Step 1 : Find Max Point a = 200 Min Point b = 230 200 200 200 230 230 230 200 215 230 9
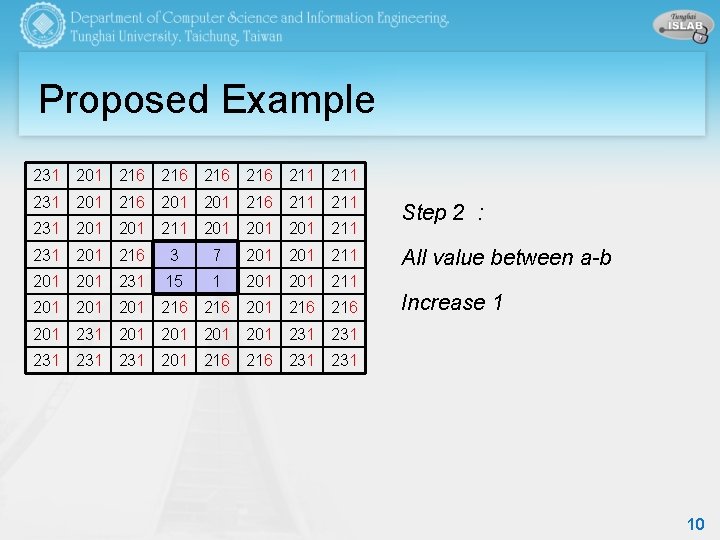
Proposed Example 231 201 216 216 211 231 201 216 211 231 201 211 201 201 211 231 201 216 3 7 201 211 201 231 15 1 201 211 201 201 216 216 Step 2 : All value between a-b Increase 1 201 231 201 201 231 231 231 201 216 231 10
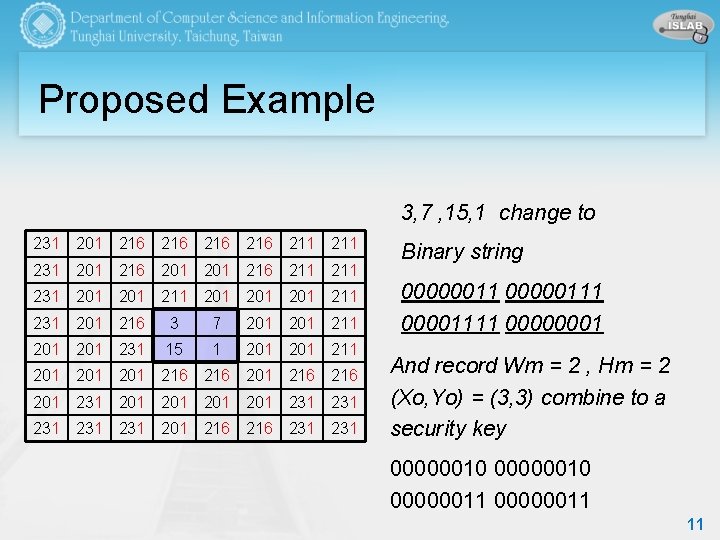
Proposed Example 3, 7 , 15, 1 change to 231 201 216 216 211 231 201 216 211 231 201 211 201 201 211 231 201 216 3 7 201 211 201 231 15 1 201 211 201 201 216 216 201 231 201 201 231 231 231 201 216 231 Binary string 000000111 00001111 00000001 And record Wm = 2 , Hm = 2 (Xo, Yo) = (3, 3) combine to a security key 00000010 00000011 11
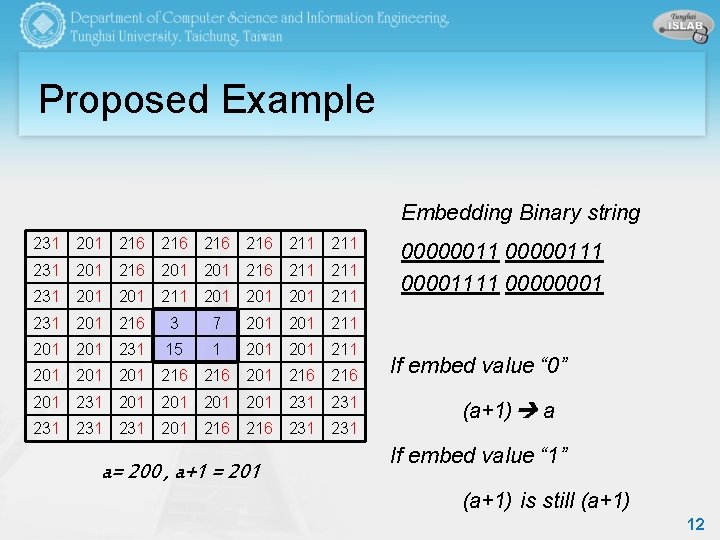
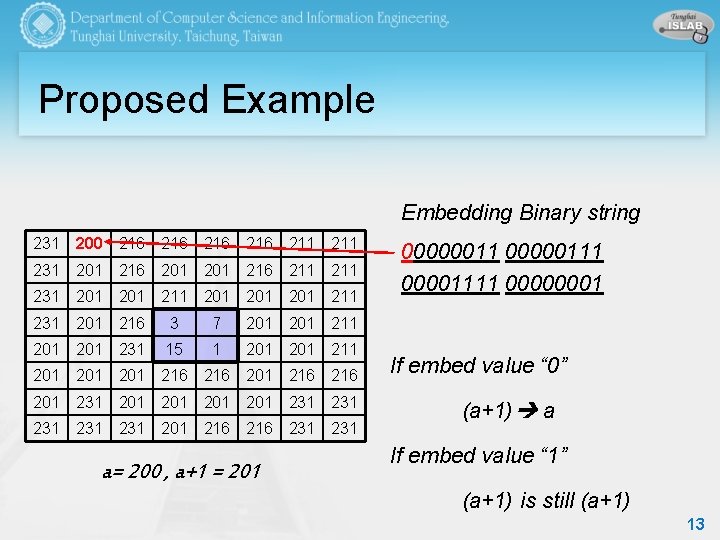
Proposed Example Embedding Binary string 231 201 216 216 211 231 201 216 211 231 201 211 201 201 211 231 201 216 3 7 201 211 201 231 15 1 201 211 201 201 216 216 201 231 201 201 231 231 231 201 216 231 a= 200 , a+1 = 201 000000111 00001111 00000001 If embed value “ 0” (a+1) a If embed value “ 1” (a+1) is still (a+1) 12
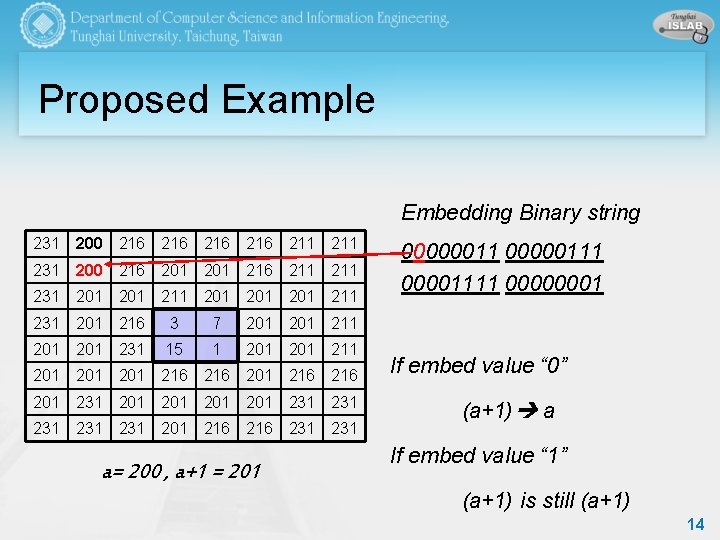
Proposed Example Embedding Binary string 231 200 216 216 211 231 201 216 211 231 201 211 201 201 211 231 201 216 3 7 201 211 201 231 15 1 201 211 201 201 216 216 201 231 201 201 231 231 231 201 216 231 a= 200 , a+1 = 201 000000111 00001111 00000001 If embed value “ 0” (a+1) a If embed value “ 1” (a+1) is still (a+1) 13
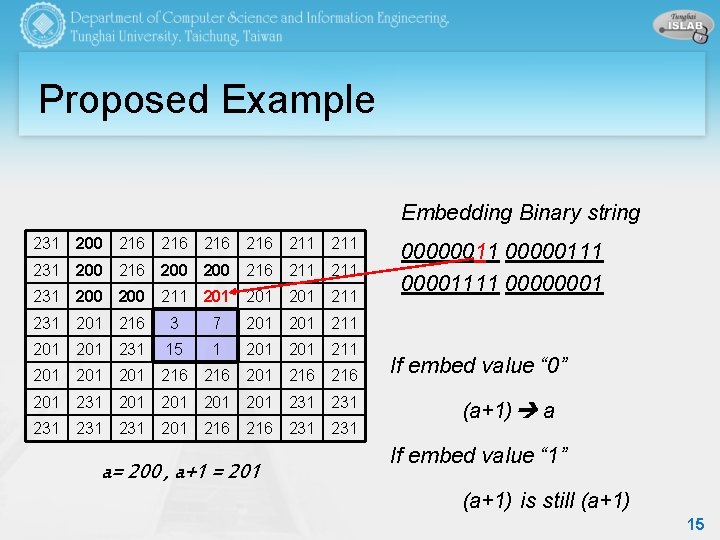
Proposed Example Embedding Binary string 231 200 216 216 211 231 200 216 201 216 211 231 201 211 201 201 211 231 201 216 3 7 201 211 201 231 15 1 201 211 201 201 216 216 201 231 201 201 231 231 231 201 216 231 a= 200 , a+1 = 201 000000111 00001111 00000001 If embed value “ 0” (a+1) a If embed value “ 1” (a+1) is still (a+1) 14
Proposed Example Embedding Binary string 231 200 216 216 211 231 200 216 211 231 200 211 201 201 211 231 201 216 3 7 201 211 201 231 15 1 201 211 201 201 216 216 201 231 201 201 231 231 231 201 216 231 a= 200 , a+1 = 201 000000111 00001111 00000001 If embed value “ 0” (a+1) a If embed value “ 1” (a+1) is still (a+1) 15
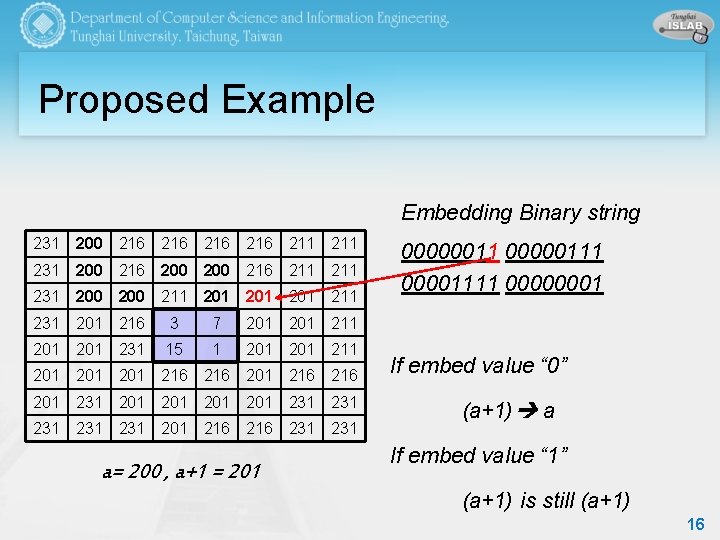
Proposed Example Embedding Binary string 231 200 216 216 211 231 200 216 211 231 200 211 201 201 211 231 201 216 3 7 201 211 201 231 15 1 201 211 201 201 216 216 201 231 201 201 231 231 231 201 216 231 a= 200 , a+1 = 201 000000111 00001111 00000001 If embed value “ 0” (a+1) a If embed value “ 1” (a+1) is still (a+1) 16
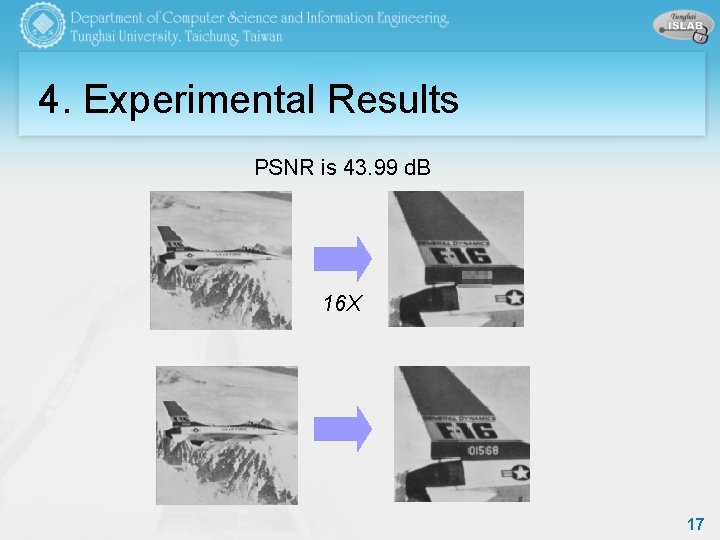
4. Experimental Results PSNR is 43. 99 d. B 16 X 17
5. Conclusion we discussed about hiding the secret information within an image with reversible data hiding. n The both original and secret information can be perfectly recovered and retrieved. n Simulation results demonstrate their applicability. n 18
Q&A
- Slides: 19