Information Governance Incident Avoidance and Reporting Presented by
Information Governance Incident Avoidance and Reporting Presented by: Doreen Todd, Data Protection Officer
Agenda 1. Definition of a Data Breach/possible causes 2. Data Breaches and Security 3. UK Regulator/Incident Reporting 4. Questions/Quiz
1. Definition of a Data Breach/possible causes
What is a personal data breach? • A breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, personal data. This includes breaches that are the result of both accidental and deliberate causes. It also means that a breach is more than just about losing personal data.
Personal data breaches can include: • Access by an unauthorised third party; • Deliberate or accidental action by a controller or processor; • Sending personal data to the wrong person; • Sending an email via non encrypted method • Computer devices containing personal data lost or stolen; • Alteration of personal data without permission; and • Loss of availability of personal data.
Incidents in BEH • Patient information stolen from the boot of a car • Excessive patient information inappropriately shared with another organisation • Sensitive information posted to the wrong address • Sensitive information sent to another individual for the past 4 years • Confidential information sent from NHS mail to a hot mail account • Confidential information sent to the wrong email address
Possible causes of data breaches • • • Insufficient resources Competing demands Meeting deadlines Lack of training Intent
2. Data Breaches and Security
What level of security is needed ? • Not defined in the GDPR • The GDPR requires the Trust to have a level of security that is ‘appropriate’ to the risks presented by what you do with information. • Considering this in relation to the state of the art and costs of implementation, as well as the nature, scope, context and purpose of your processing.
Why worry about information security • • • Identity fraud Fake credit card applications Fake applications for tax credit Mortgage fraud Exposure of an addresses of service personnel, police and prison officers, and those at risk of domestic violence
• NHS mail to NHS mail - secure • NHS mail to the police - secure • NHS mail to. gov. uk – debate over the security • NHS mail to hotmail – not secure • Use NHS mail [secure] if there is any doubt

3. UK Regulator/Incident Reporting
Information Commissioner • The UK’s independent authority set up to uphold information rights in the public interest, promoting openness by public bodies and data privacy for individuals • Every year they receive tens of thousands of enquiries, written concerns and complaints
Breach Notification • Breach notification mandatory where a data breach is likely to result in a risk to individuals • Significant penalties for getting it wrong – up to £ 17 m in some cases • Must be reported to the ICO within 72 hours of first having become aware of a suspected breach
Incident Reporting It’s important to report weaknesses and potential issues. This is PROACTIVE. It helps cut down complaints and improves what we do BEFORE an incident occurs. It also helps identify patterns and trends Report via Ulysses within 24 hours
ICO Taking Action • July 2019 BA faces record £ 183 m fine for data breach after users of their website were diverted to a fraudulent site. • April 2019 Newham Council fined £ 145, 000 for disclosing personal information of more than 200 people who featured on a police intelligence database. • March 2019 A former administrator at an NHS Trust prosecuted for accessing medical records relating to 7 family members without authorisation • May 2018 Medical Centre fined £ 35, 000 after leaving highly sensitive medical information in an empty building. The information included medical records, prescriptions, which had been left unsecured in the building for more than 18 months.
What if you don’t have all the required information available yet? • It will not always be possible to investigate a breach fully within 72 hours to understand exactly what’s happened and what needs to be done to mitigate it. • Provide the required information in phases, as long as this is done without undue further delay. • Prioritise the investigation, give it adequate resources, and expedite it urgently. • Must notify the ICO of the breach when you become aware of it, and submit further information as soon as possible.
Informing individuals • If a breach is likely to result in a high risk to the rights and freedoms of individuals, you must inform those concerned directly as soon as possible. • The Trust will need to assess both the severity of the potential or actual impact on individuals as a result of a breach and the likelihood of this occurring. • One of the main reasons for informing individuals is to help them take steps to protect themselves from the effects of a breach.
Mitigation • Remember the 5 second rule • Take time to check before you send/push the button • If in doubt - don’t act • Seek advice if unsure • Report without delay • Keep up to date with IG Training
Useful Contacts • Caldicott Guardian Patient related queries • Senior Information Risk Owner (SIRO) Risks that cant be mitigated • Data Protection Officer Any of the above
4. Any Questions and Quiz
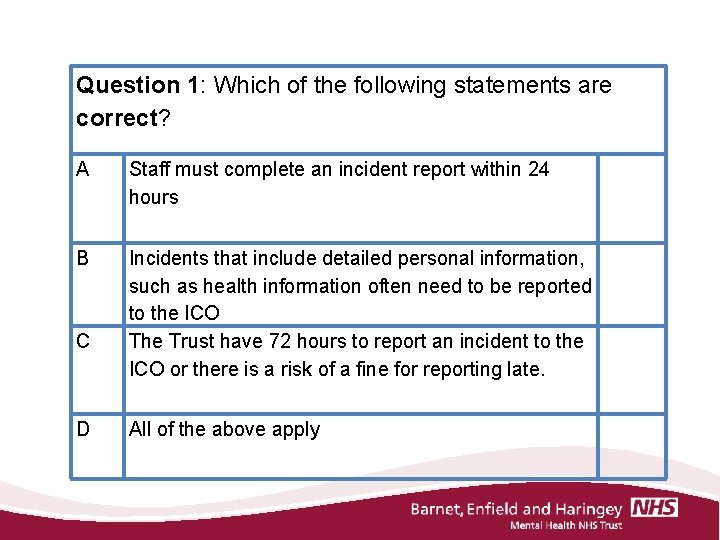
Question 1: Which of the following statements are correct? A Staff must complete an incident report within 24 hours B Incidents that include detailed personal information, such as health information often need to be reported to the ICO The Trust have 72 hours to report an incident to the ICO or there is a risk of a fine for reporting late. C D All of the above apply
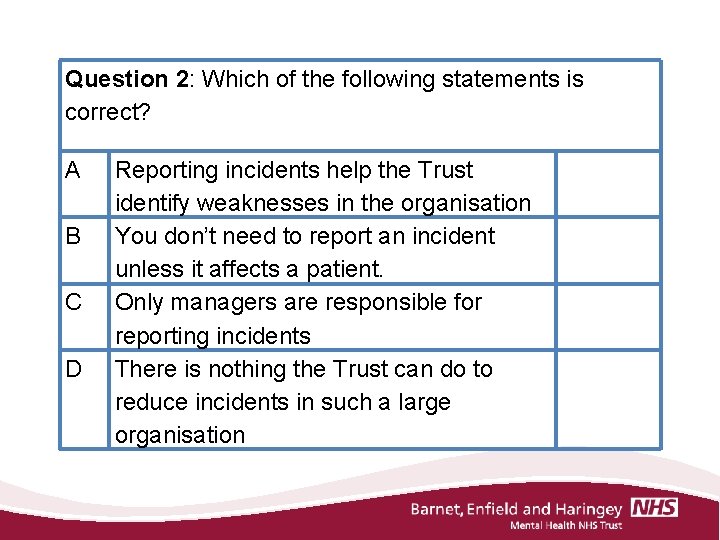
Question 2: Which of the following statements is correct? A B C D Reporting incidents help the Trust identify weaknesses in the organisation You don’t need to report an incident unless it affects a patient. Only managers are responsible for reporting incidents There is nothing the Trust can do to reduce incidents in such a large organisation
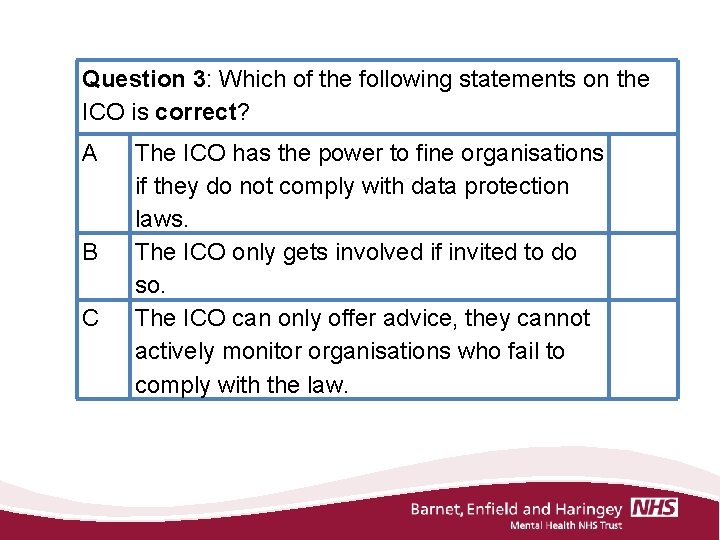
Question 3: Which of the following statements on the ICO is correct? A B C The ICO has the power to fine organisations if they do not comply with data protection laws. The ICO only gets involved if invited to do so. The ICO can only offer advice, they cannot actively monitor organisations who fail to comply with the law.
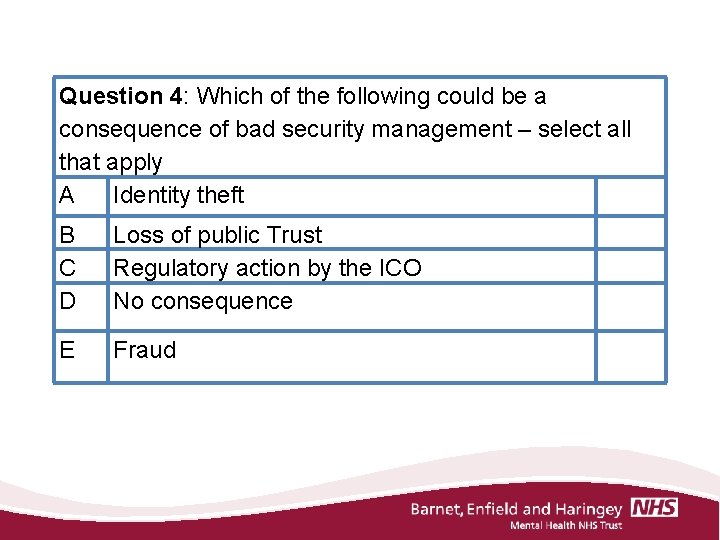
Question 4: Which of the following could be a consequence of bad security management – select all that apply A Identity theft B C D Loss of public Trust Regulatory action by the ICO No consequence E Fraud
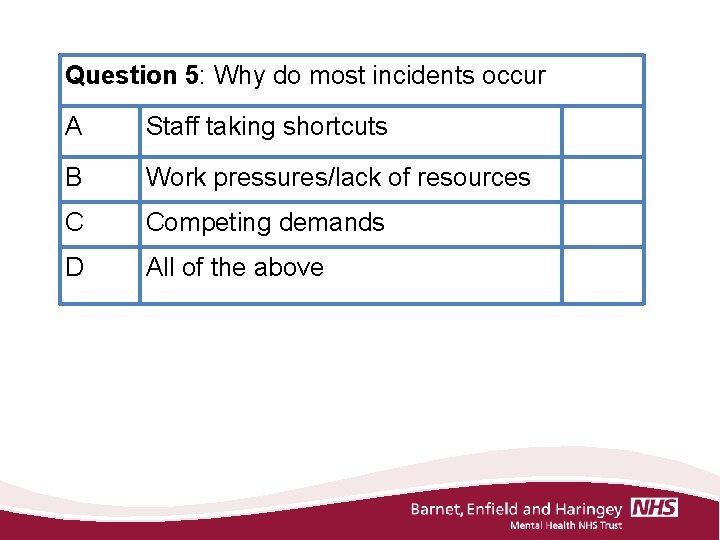
Question 5: Why do most incidents occur A Staff taking shortcuts B Work pressures/lack of resources C Competing demands D All of the above
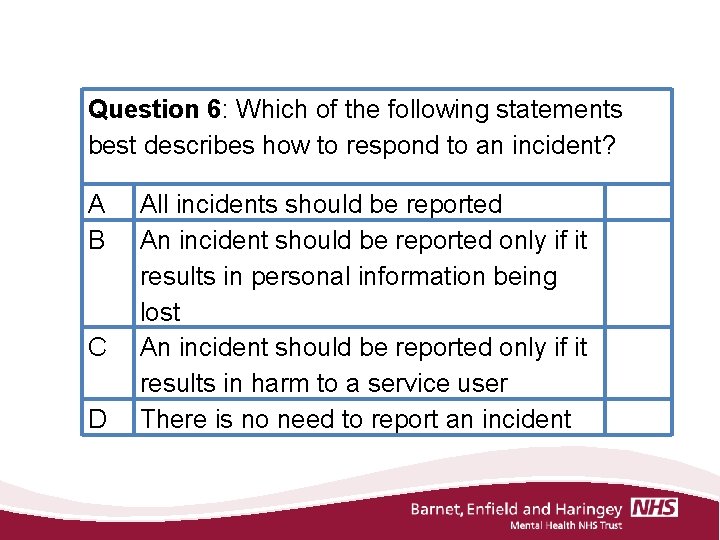
Question 6: Which of the following statements best describes how to respond to an incident? A B C D All incidents should be reported An incident should be reported only if it results in personal information being lost An incident should be reported only if it results in harm to a service user There is no need to report an incident
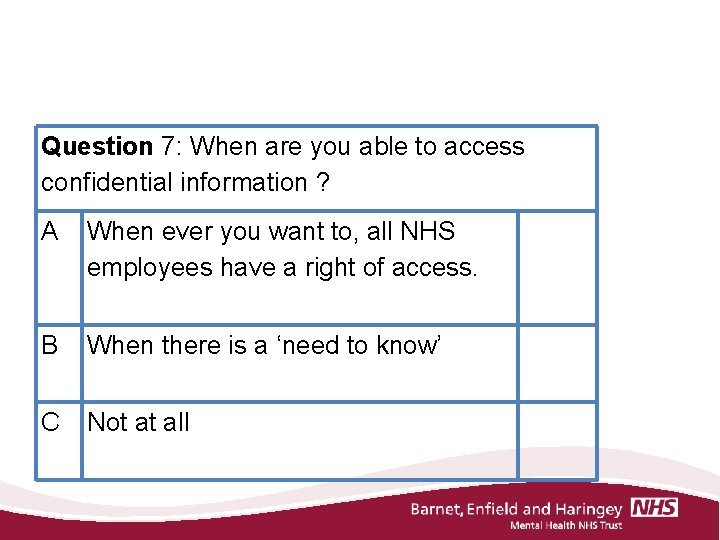
Question 7: When are you able to access confidential information ? A When ever you want to, all NHS employees have a right of access. B When there is a ‘need to know’ C Not at all
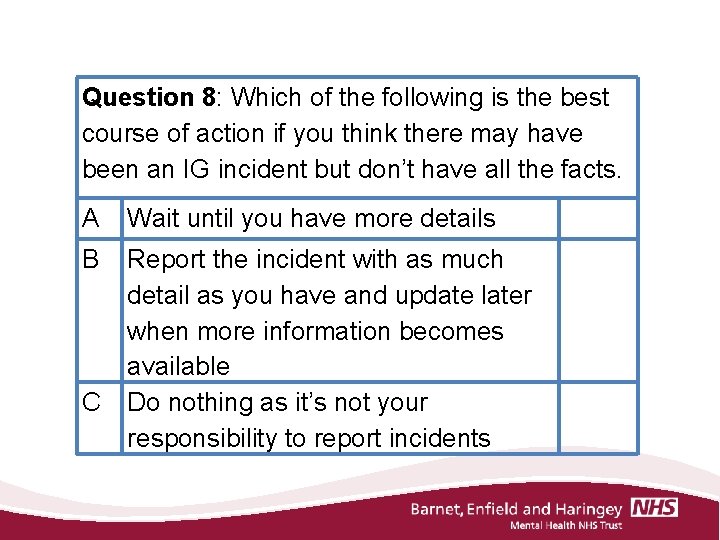
Question 8: Which of the following is the best course of action if you think there may have been an IG incident but don’t have all the facts. A Wait until you have more details B Report the incident with as much detail as you have and update later when more information becomes available Do nothing as it’s not your responsibility to report incidents C
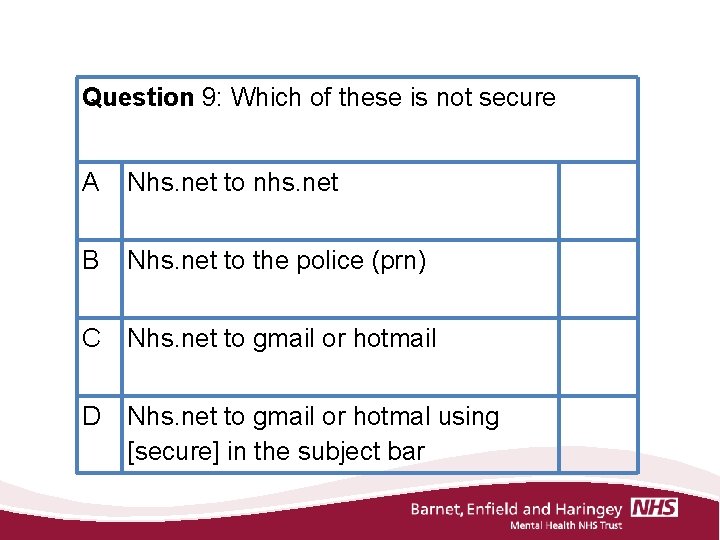
Question 9: Which of these is not secure A Nhs. net to nhs. net B Nhs. net to the police (prn) C Nhs. net to gmail or hotmail D Nhs. net to gmail or hotmal using [secure] in the subject bar
Thank you for your time
- Slides: 31