Information Governance Data protection Security Objectives Understand the

Information Governance, Data protection & Security
Objectives • Understand the Principles of Information Governance and apply them to everyday practice • Know how to access Information Governance resources including national legislation, guidance, local policies and procedures • Know health and social care organisations’ responsibilities including: General Data Protection Regulations, confidentiality and the Caldicott Principles • Understand the principles of maintaining good client records • Know how to keep patient, staff & organisational information secure
Information When identifying an individual you should consider…. Personal information - Information about someone is ‘personal’ when it identifies the individual. It may be about a living or deceased person including patients, service users and staff. Sensitive information-This relates to information concerning a data subject's racial or ethnic origin, political opinions, religious beliefs, trade union activities, physical or mental health, sexual life, or details of criminal offences.
Information Confidential- Information a patient, service user or staff member has disclosed in confidence. This can include personal, sensitive or third party information. Anonymised- Information that does not identify an individual and cannot reasonably be used to determine their identity, therefore it cannot be personal or sensitive. Pseudonymised- Information in which individuals are distinguished by using a unique identifier. This does not reveal their ‘real world’ identity, but allows linking of data. ID 123
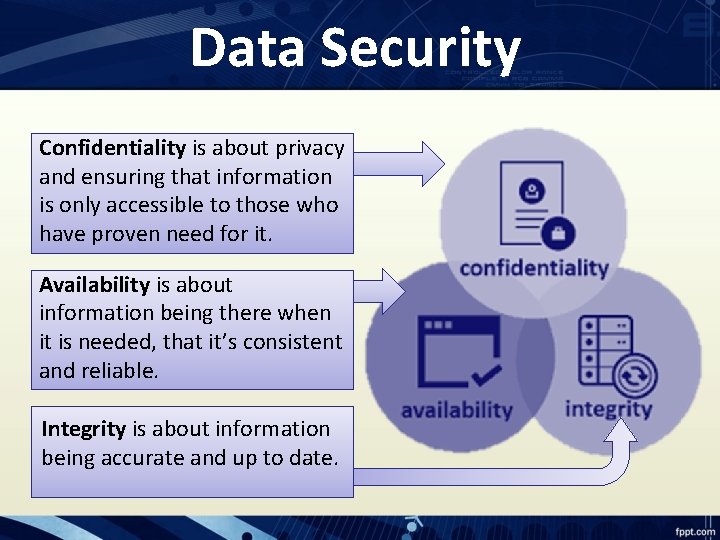
Data Security Confidentiality is about privacy and ensuring that information is only accessible to those who have proven need for it. Availability is about information being there when it is needed, that it’s consistent and reliable. Integrity is about information being accurate and up to date.
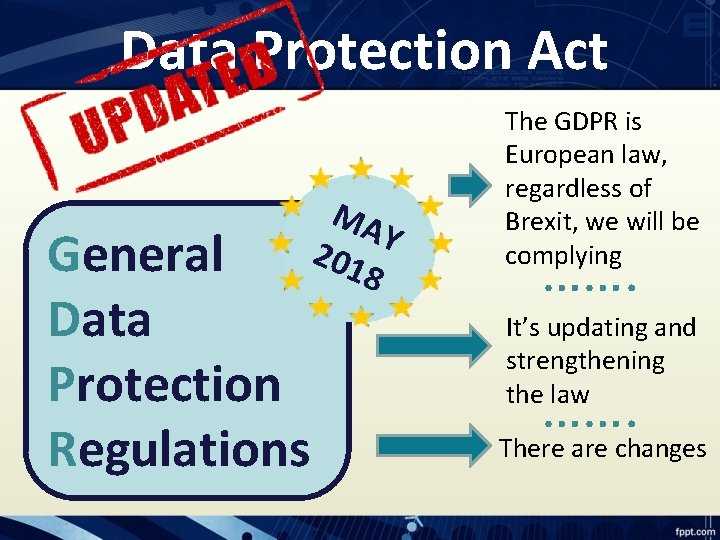
Data Protection Act General Data Protection Regulations MA Y 201 8 The GDPR is European law, regardless of Brexit, we will be complying ……. It’s updating and strengthening the law ……. There are changes
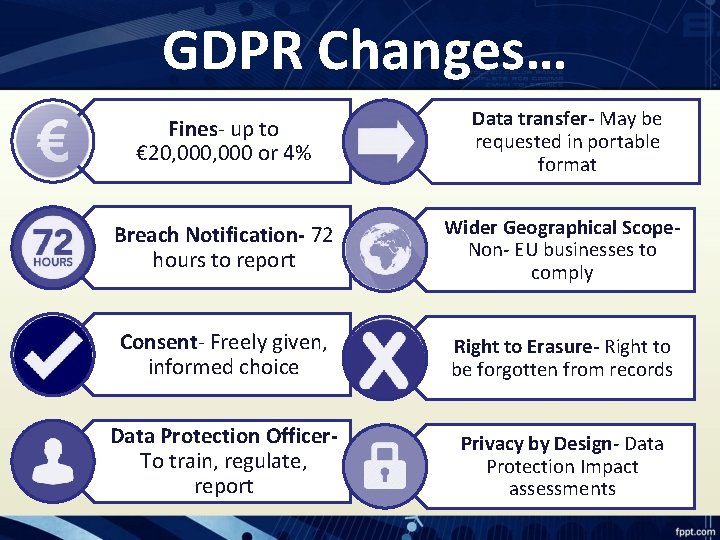
GDPR Changes… Fines- up to € 20, 000 or 4% Data transfer- May be requested in portable format Breach Notification- 72 hours to report Wider Geographical Scope. Non- EU businesses to comply Consent- Freely given, informed choice Right to Erasure- Right to be forgotten from records Data Protection Officer. To train, regulate, report Privacy by Design- Data Protection Impact assessments
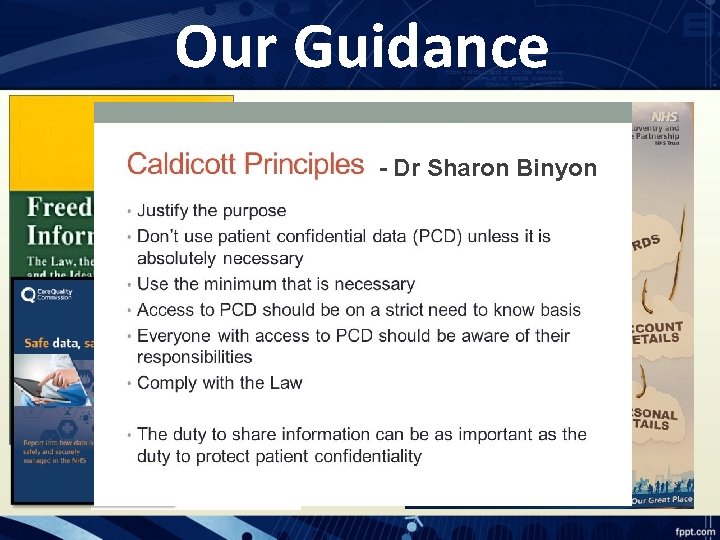
Our Guidance - Dr Sharon Binyon
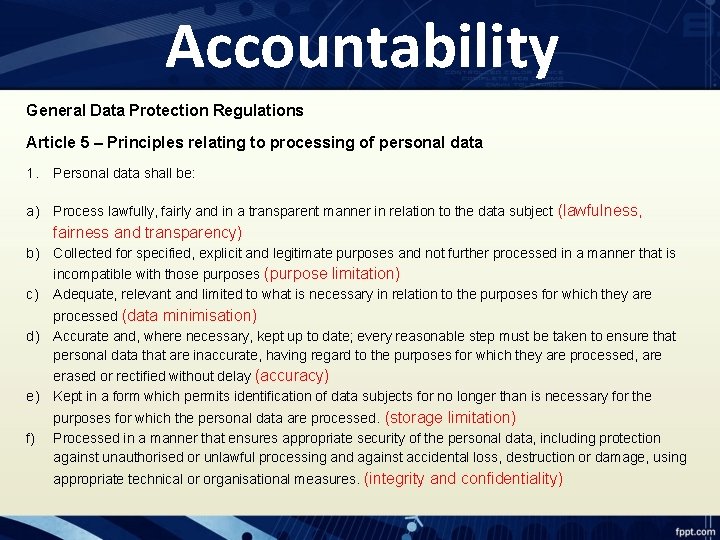
Accountability General Data Protection Regulations Article 5 – Principles relating to processing of personal data 1. Personal data shall be: a) Process lawfully, fairly and in a transparent manner in relation to the data subject (lawfulness, fairness and transparency) b) Collected for specified, explicit and legitimate purposes and not further processed in a manner that is incompatible with those purposes (purpose limitation) c) Adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed (data minimisation) d) Accurate and, where necessary, kept up to date; every reasonable step must be taken to ensure that personal data that are inaccurate, having regard to the purposes for which they are processed, are erased or rectified without delay (accuracy) e) Kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the personal data are processed. (storage limitation) f) Processed in a manner that ensures appropriate security of the personal data, including protection against unauthorised or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organisational measures. (integrity and confidentiality)
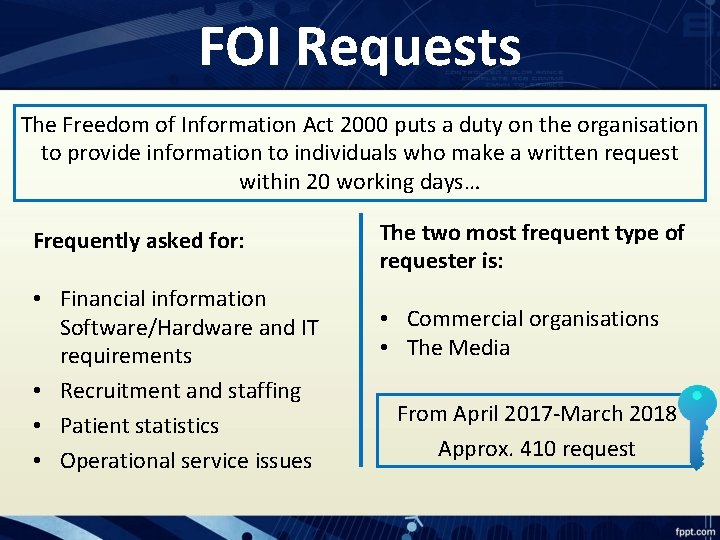
FOI Requests The Freedom of Information Act 2000 puts a duty on the organisation to provide information to individuals who make a written request within 20 working days… Frequently asked for: • Financial information Software/Hardware and IT requirements • Recruitment and staffing • Patient statistics • Operational service issues The two most frequent type of requester is: • Commercial organisations • The Media From April 2017 -March 2018 Approx. 410 request
Subject Access Requests All patients and staff continue to have the right to access to their personal and personal sensitive information… 1. 2. 3. 4. We must receive the request in writing 40 Calendar days has now reduced to 30 No Fee is able to be charged (previously £ 50) An appropriate clinician must review/ redact notes Records must be written in a professional manner and be factual Embarrassment is not a reason for non-disclosure
Record Keeping Poor quality information presents a risk to patients, service users, staff members and the organisation. We should consider… • • • Record as events occur Complete Free from duplication Quick and easy to locate Compliant with procedures Accurate

Social Media Professional with personal social media presenceconsider your professional reputation at all times Personal safety and privacyuse maximum privacy setting Confidentiality- do not discuss work related topics (staff or patient related Information) on social media
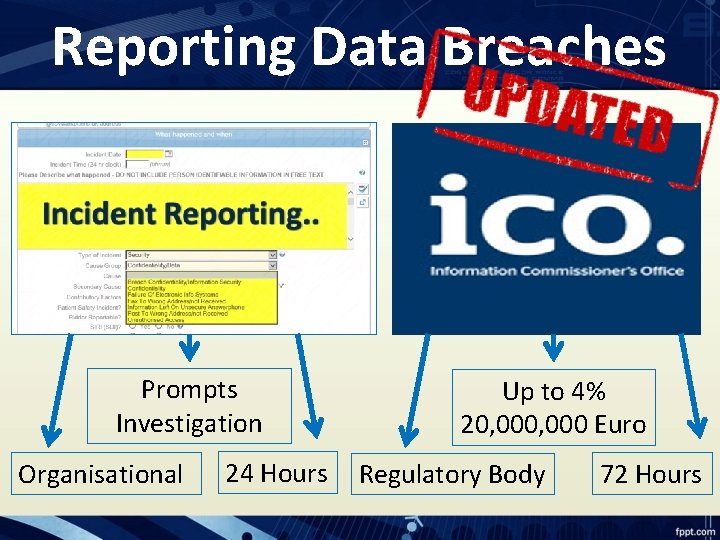
Reporting Data Breaches Prompts Investigation Organisational 24 Hours Up to 4% 20, 000 Euro Regulatory Body 72 Hours
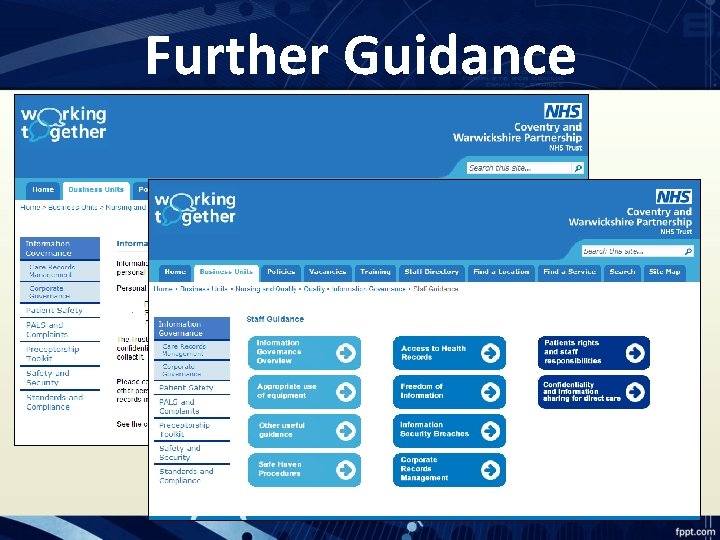
Further Guidance
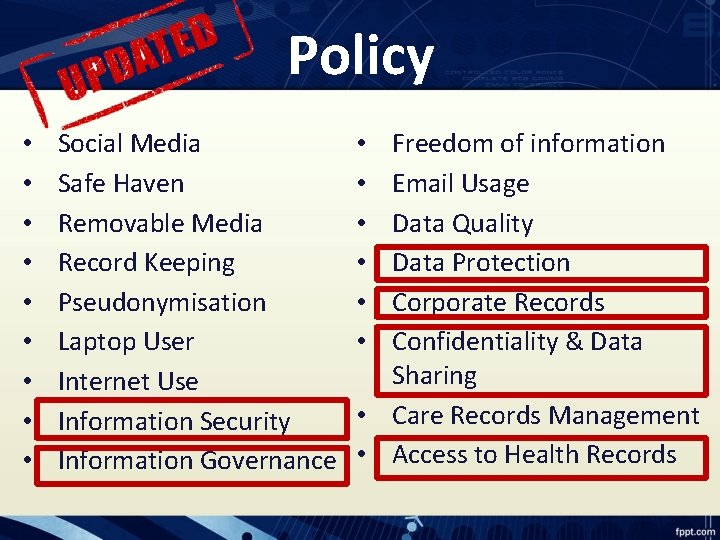
Policy • • • Social Media Safe Haven Removable Media Record Keeping Pseudonymisation Laptop User Internet Use Information Security Information Governance Freedom of information Email Usage Data Quality Data Protection Corporate Records Confidentiality & Data Sharing • Care Records Management • Access to Health Records • • •
Quiz Look at the Quiz sheet provided Work as a team to answer the questions You have 10 minutes to complete
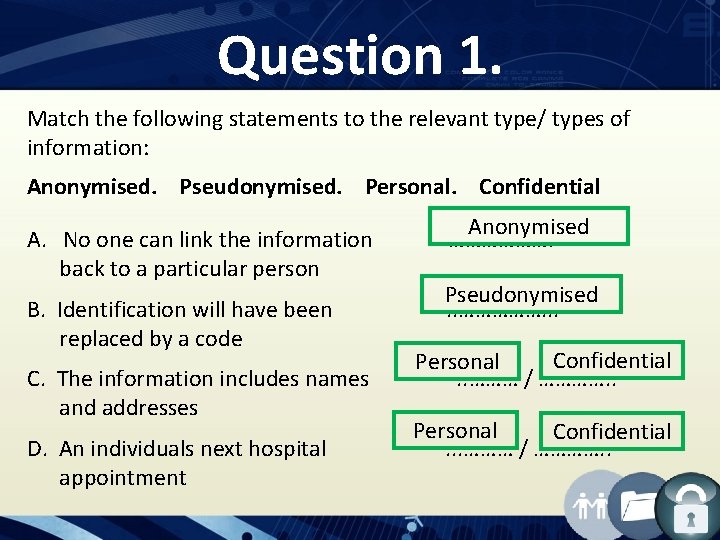
Question 1. Match the following statements to the relevant type/ types of information: Anonymised. Pseudonymised. Personal. Confidential A. No one can link the information back to a particular person B. Identification will have been replaced by a code C. The information includes names and addresses D. An individuals next hospital appointment Anonymised ………………. Pseudonymised. . ……………. . . Confidential Personal. . ……… / …………. . Personal Confidential. . . ……… / …………. .
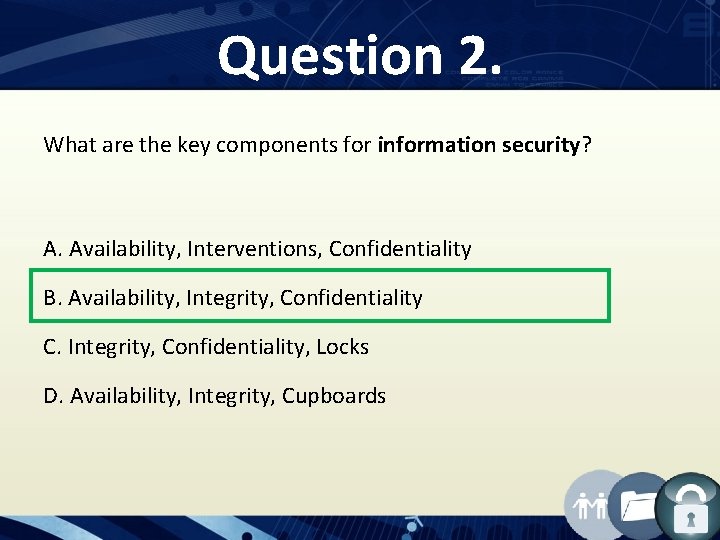
Question 2. What are the key components for information security? A. Availability, Interventions, Confidentiality B. Availability, Integrity, Confidentiality C. Integrity, Confidentiality, Locks D. Availability, Integrity, Cupboards
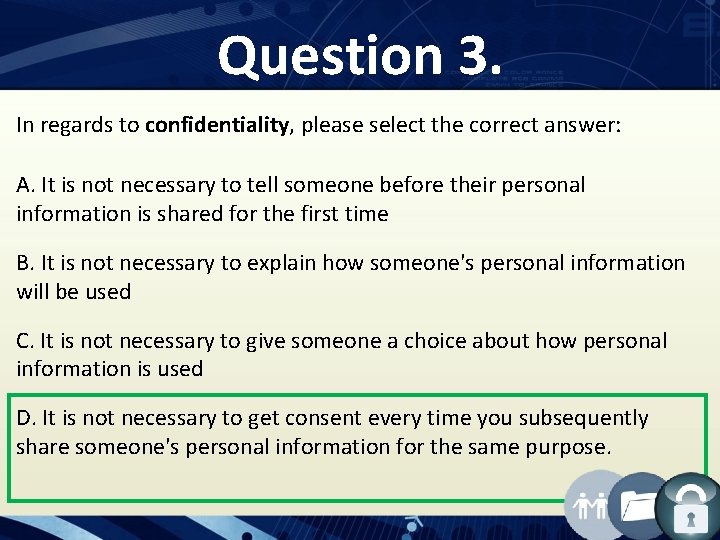
Question 3. In regards to confidentiality, please select the correct answer: A. It is not necessary to tell someone before their personal information is shared for the first time B. It is not necessary to explain how someone's personal information will be used C. It is not necessary to give someone a choice about how personal information is used D. It is not necessary to get consent every time you subsequently share someone's personal information for the same purpose.
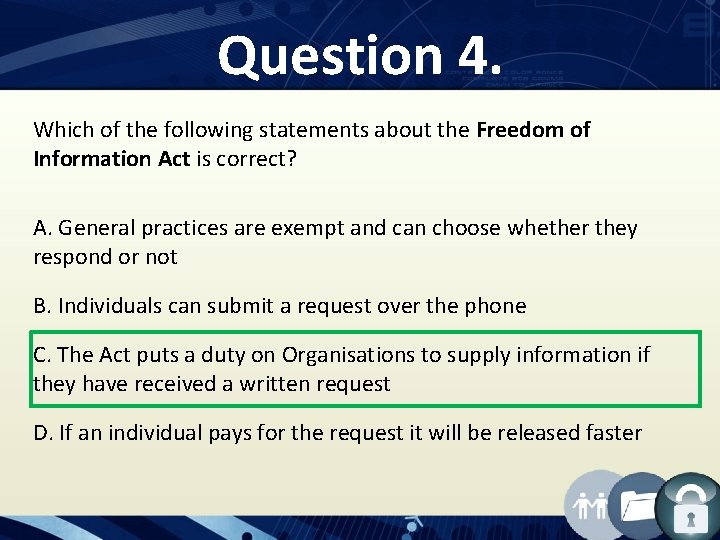
Question 4. Which of the following statements about the Freedom of Information Act is correct? A. General practices are exempt and can choose whether they respond or not B. Individuals can submit a request over the phone C. The Act puts a duty on Organisations to supply information if they have received a written request D. If an individual pays for the request it will be released faster
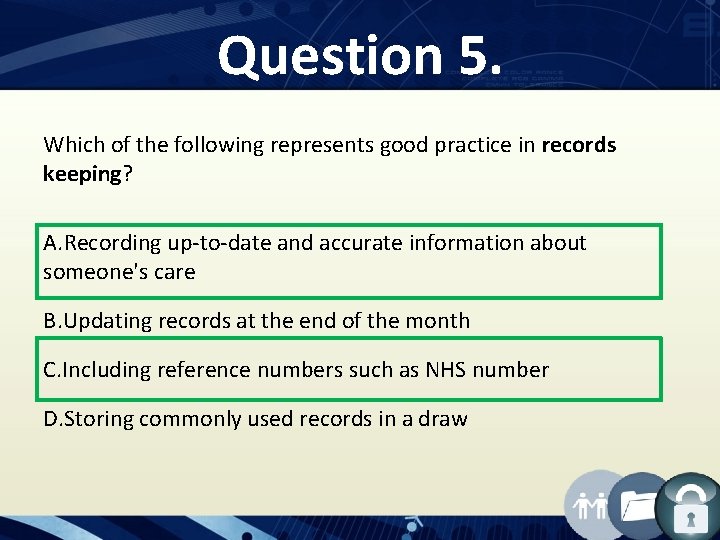
Question 5. Which of the following represents good practice in records keeping? A. Recording up-to-date and accurate information about someone's care B. Updating records at the end of the month C. Including reference numbers such as NHS number D. Storing commonly used records in a draw
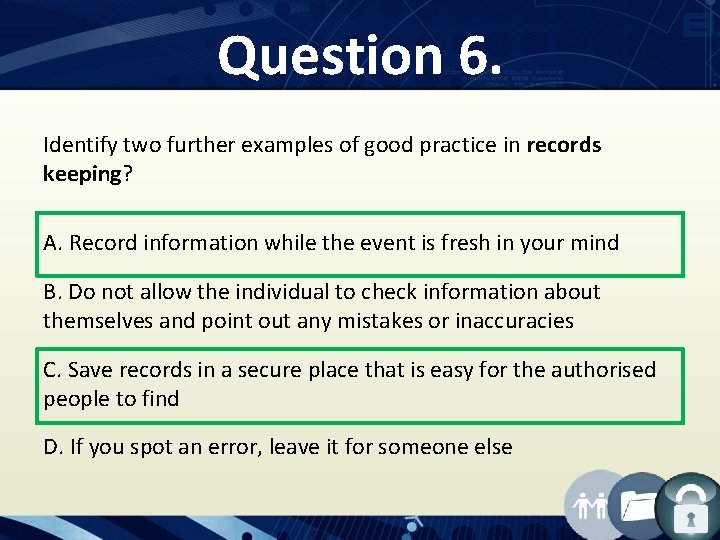
Question 6. Identify two further examples of good practice in records keeping? A. Record information while the event is fresh in your mind B. Do not allow the individual to check information about themselves and point out any mistakes or inaccuracies C. Save records in a secure place that is easy for the authorised people to find D. If you spot an error, leave it for someone else
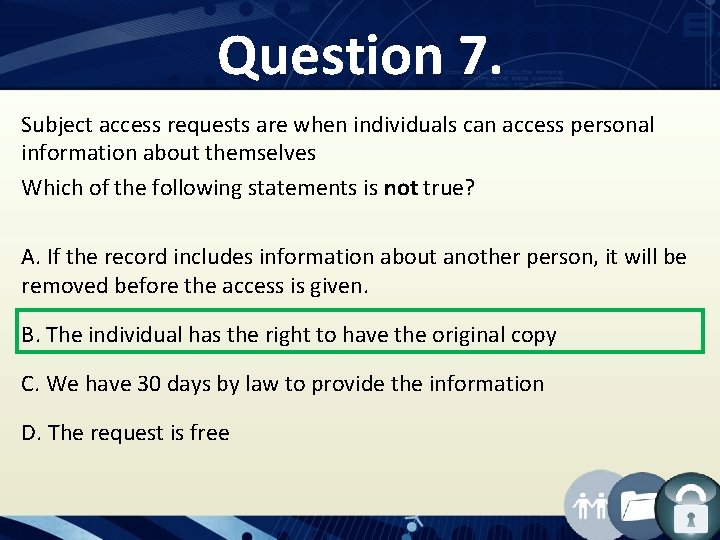
Question 7. Subject access requests are when individuals can access personal information about themselves Which of the following statements is not true? A. If the record includes information about another person, it will be removed before the access is given. B. The individual has the right to have the original copy C. We have 30 days by law to provide the information D. The request is free
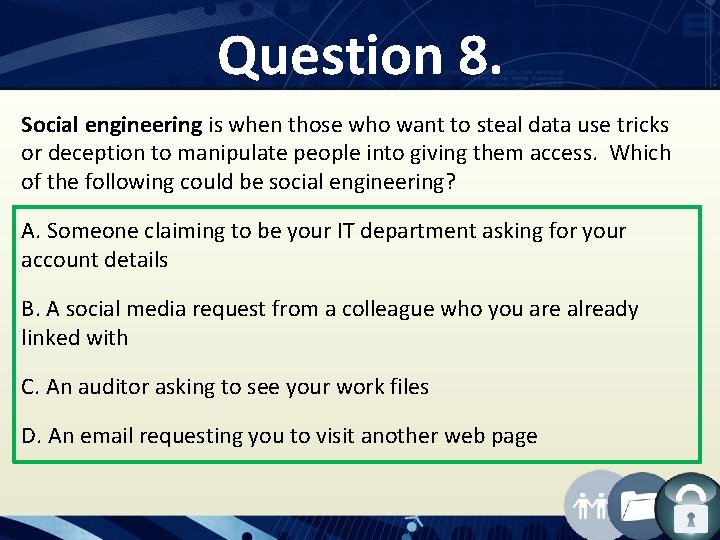
Question 8. Social engineering is when those who want to steal data use tricks or deception to manipulate people into giving them access. Which of the following could be social engineering? A. Someone claiming to be your IT department asking for your account details B. A social media request from a colleague who you are already linked with C. An auditor asking to see your work files D. An email requesting you to visit another web page
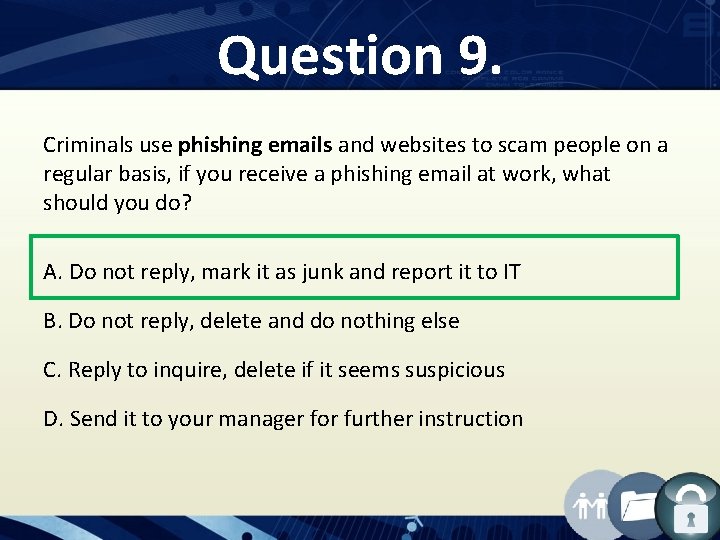
Question 9. Criminals use phishing emails and websites to scam people on a regular basis, if you receive a phishing email at work, what should you do? A. Do not reply, mark it as junk and report it to IT B. Do not reply, delete and do nothing else C. Reply to inquire, delete if it seems suspicious D. Send it to your manager for further instruction
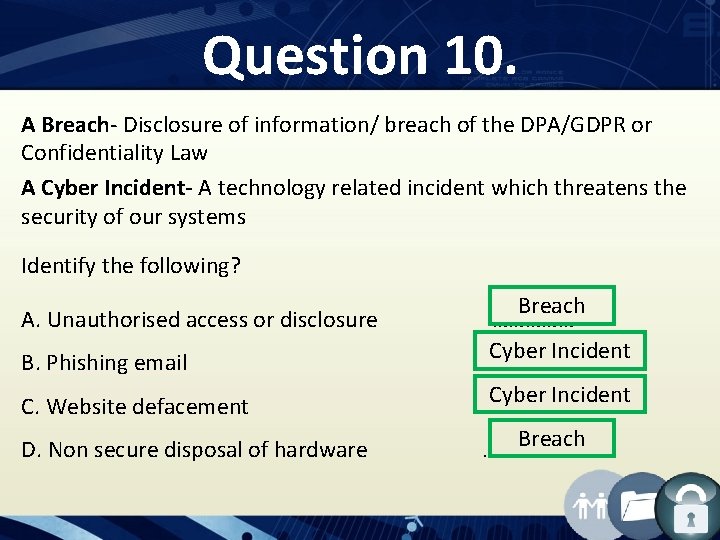
Question 10. A Breach- Disclosure of information/ breach of the DPA/GDPR or Confidentiality Law A Cyber Incident- A technology related incident which threatens the security of our systems Identify the following? A. Unauthorised access or disclosure B. Phishing email C. Website defacement D. Non secure disposal of hardware Breach …………… Cyber Incident …………… Breach ……………
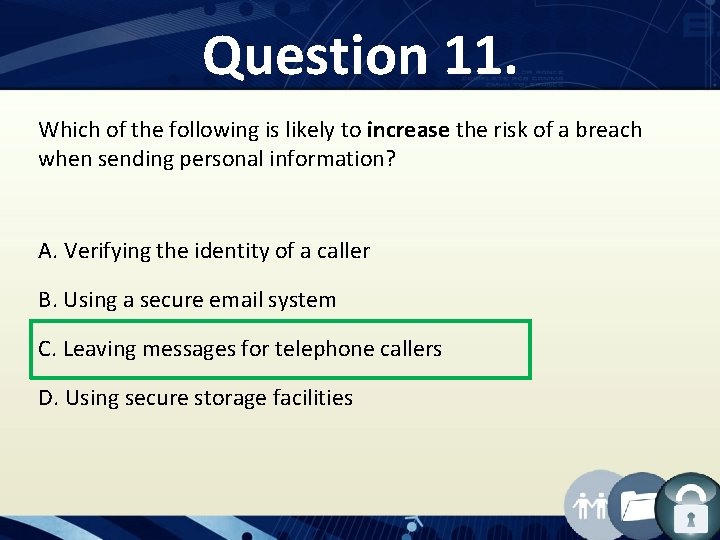
Question 11. Which of the following is likely to increase the risk of a breach when sending personal information? A. Verifying the identity of a caller B. Using a secure email system C. Leaving messages for telephone callers D. Using secure storage facilities
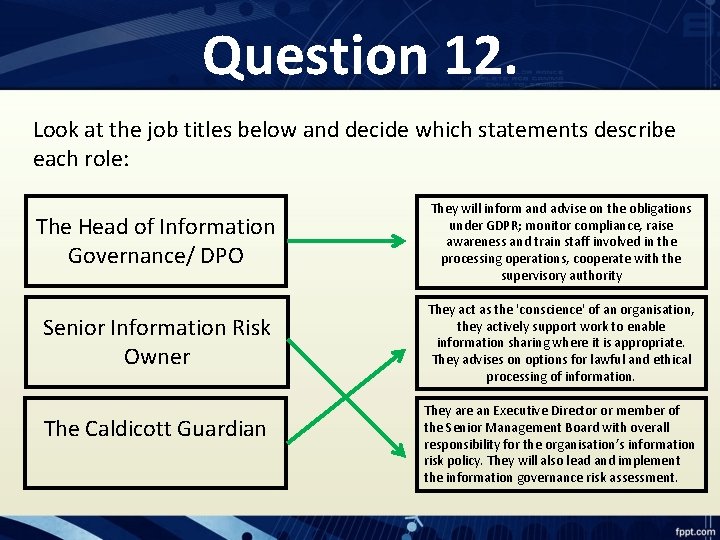
Question 12. Look at the job titles below and decide which statements describe each role: The Head of Information Governance/ DPO They will inform and advise on the obligations under GDPR; monitor compliance, raise awareness and train staff involved in the processing operations, cooperate with the supervisory authority Senior Information Risk Owner They act as the 'conscience' of an organisation, they actively support work to enable information sharing where it is appropriate. They advises on options for lawful and ethical processing of information. The Caldicott Guardian They are an Executive Director or member of the Senior Management Board with overall responsibility for the organisation’s information risk policy. They will also lead and implement the information governance risk assessment.
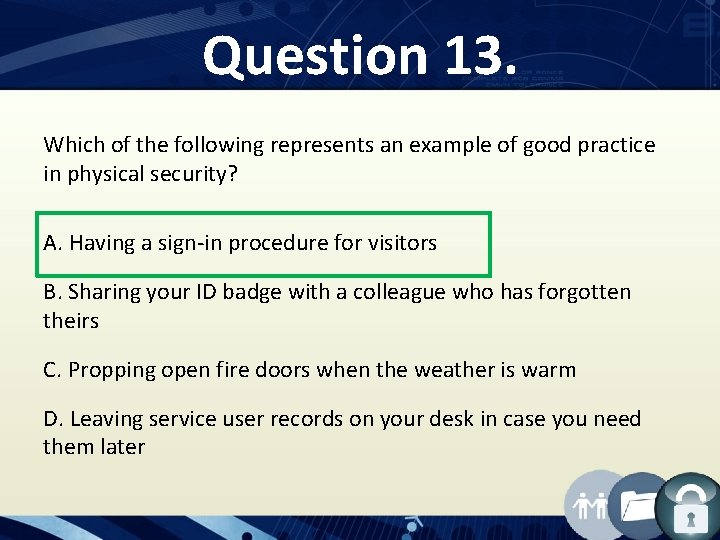
Question 13. Which of the following represents an example of good practice in physical security? A. Having a sign-in procedure for visitors B. Sharing your ID badge with a colleague who has forgotten theirs C. Propping open fire doors when the weather is warm D. Leaving service user records on your desk in case you need them later
Question 14. Which of the following statements best describes how to respond to an incident? A. All incidents should be reported B. An incident should be reported only if it results in personal information being revealed C. An incident should be reported only if it results in harm to a service user D. There is no need to report an incident
Question 15. Who is our organisations Caldicott Guardian? A. Dr Sharon Binyon B. Simon Gilby C. Naomi Wills D. Tim Molloy

Contacts: Head of Information Governance & DPO: • Becky Keough Information Governance Officers: • Jennifer Lewis • Sarah Davies • Merima Hadzic Caldicott Guardian: • Dr Sharon Binyon Senior Information Risk Owner: • Gale Hart Cyber security Manager: Care Records Manager: • Tim Molloy • Corinne Kavalieros
- Slides: 33