Infocom paper presentation SpaceEfficient TCAMbased Classification Using Gray
Infocom paper presentation Space-Efficient TCAM-based Classification Using Gray Coding Anat Bremler – Barr Danny Hendler Interdisciplianry Center Ben-Gurion University
Packet Classification
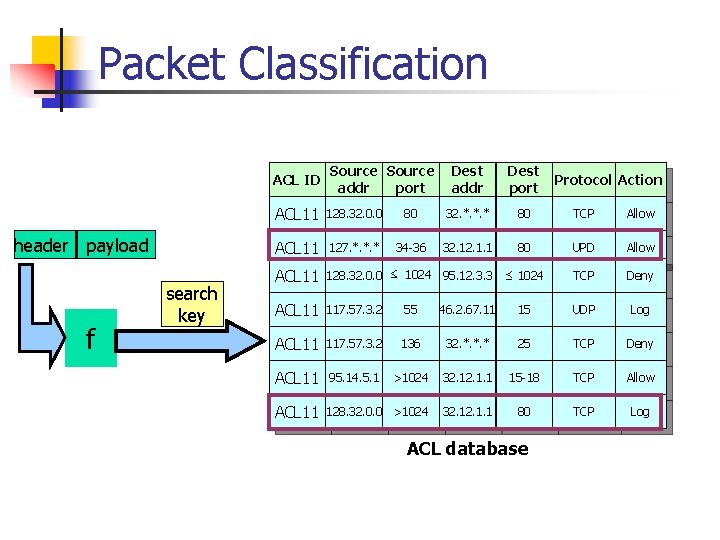
Packet Classification ACL ID header payload f search key Source addr port Dest addr Dest port Protocol Action ACL 11 128. 32. 0. 0 80 32. *. *. * 80 TCP Allow ACL 11 127. *. *. * 34 -36 32. 1. 1 80 UPD Allow ACL 11 128. 32. 0. 0 ≤ 1024 95. 12. 3. 3 ≤ 1024 TCP Deny ACL 11 117. 57. 3. 2 55 46. 2. 67. 11 15 UDP Log ACL 11 117. 57. 3. 2 136 32. *. *. * 25 TCP Deny ACL 11 95. 14. 5. 1 >1024 32. 1. 1 15 -18 TCP Allow ACL 11 128. 32. 0. 0 >1024 32. 1. 1 80 TCP Log ACL database
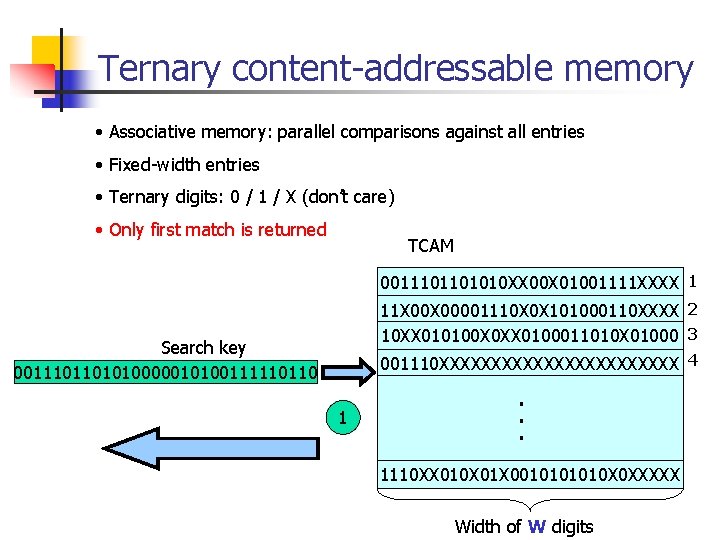
Ternary content-addressable memory • Associative memory: parallel comparisons against all entries • Fixed-width entries • Ternary digits: 0 / 1 / X (don’t care) • Only first match is returned TCAM 0011101101010 XX 00 X 01001111 XXXX 1 11 X 00001110 X 0 X 101000110 XXXX 2 10 XX 010100 X 0 XX 0100011010 X 01000 3 Search key 0011101101010000010100111110110 001110 XXXXXXXXXXXX 4 1 . . . 1110 XX 010 X 01 X 001010 X 0 XXXXX Width of W digits
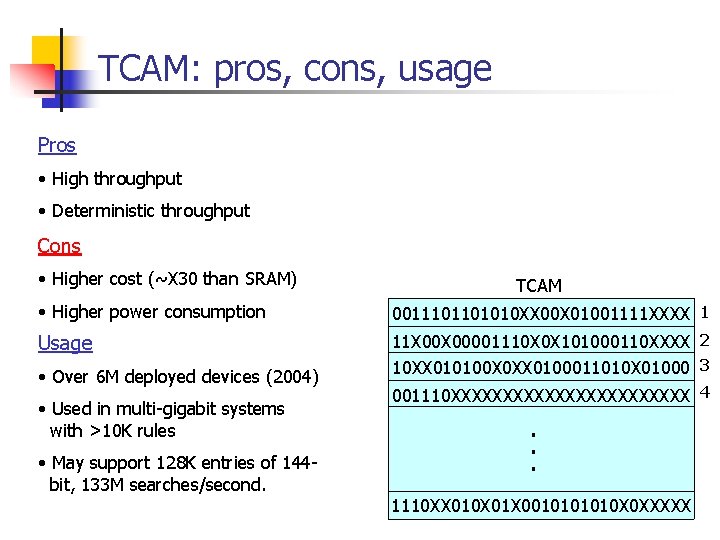
TCAM: pros, cons, usage Pros • High throughput • Deterministic throughput Cons • Higher cost (~X 30 than SRAM) TCAM • Higher power consumption 0011101101010 XX 00 X 01001111 XXXX 1 Usage 11 X 00001110 X 0 X 101000110 XXXX 2 10 XX 010100 X 0 XX 0100011010 X 01000 3 • Over 6 M deployed devices (2004) • Used in multi-gigabit systems with >10 K rules • May support 128 K entries of 144 bit, 133 M searches/second. 001110 XXXXXXXXXXXX 4 . . . 1110 XX 010 X 01 X 001010 X 0 XXXXX
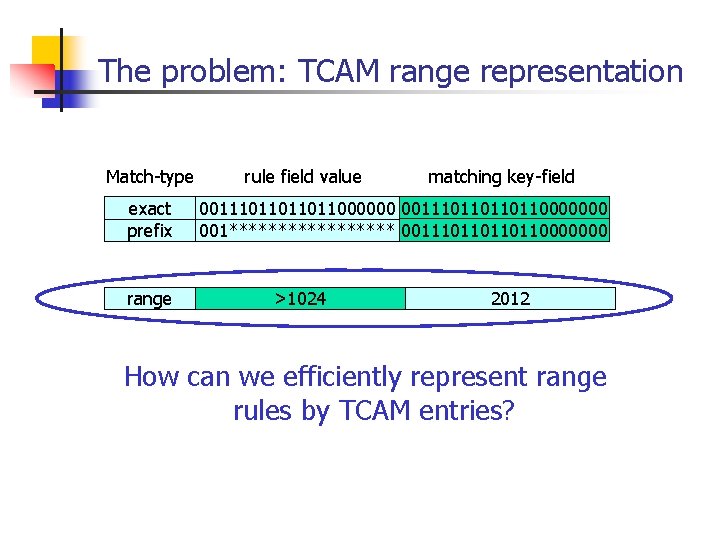
The problem: TCAM range representation Match-type exact prefix range rule field value matching key-field 001110110110110000000 001********* 001110110000000 >1024 2012 How can we efficiently represent range rules by TCAM entries?
![Basic approach: prefix expansion Representing [1, 6] 0 1 TCAM entries: 001, 01*, 10*, Basic approach: prefix expansion Representing [1, 6] 0 1 TCAM entries: 001, 01*, 10*,](http://slidetodoc.com/presentation_image/dc365bdf0834264edda2087a0adffcbf/image-7.jpg)
Basic approach: prefix expansion Representing [1, 6] 0 1 TCAM entries: 001, 01*, 10*, 110 001 010 011 100 [1, 6] Prefix expansion is inefficient • A range over W-bits may expand to 2 W-2 entries • For 2 range-fields, may expand to (2 W-2)2 • Expansion factor of up to 6 on real-world databases !!! 101 110 111
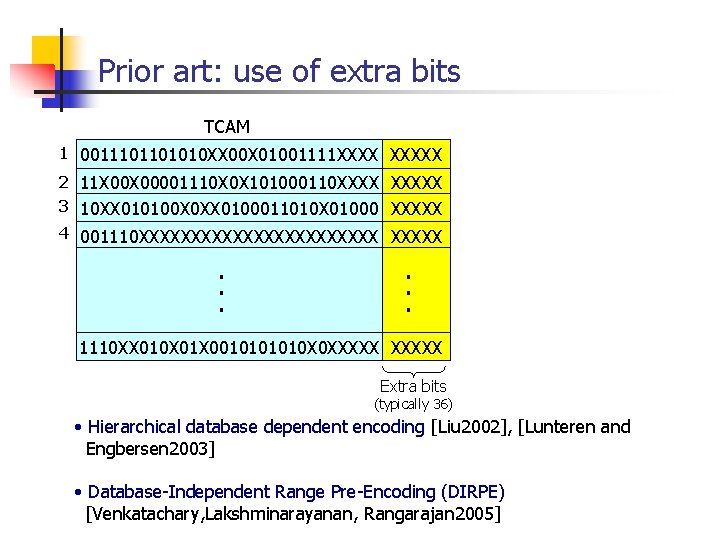
Prior art: use of extra bits TCAM 1 0011101101010 XX 00 X 01001111 XXXXX 2 11 X 00001110 X 0 X 101000110 XXXXX 3 10 XX 010100 X 0 XX 0100011010 X 01000 XXXXX 4 001110 XXXXXXXXXXXX . . . 1110 XX 010 X 01 X 001010 X 0 XXXXX Extra bits (typically 36) • Hierarchical database dependent encoding [Liu 2002], [Lunteren and Engbersen 2003] • Database-Independent Range Pre-Encoding (DIRPE) [Venkatachary, Lakshminarayanan, Rangarajan 2005]
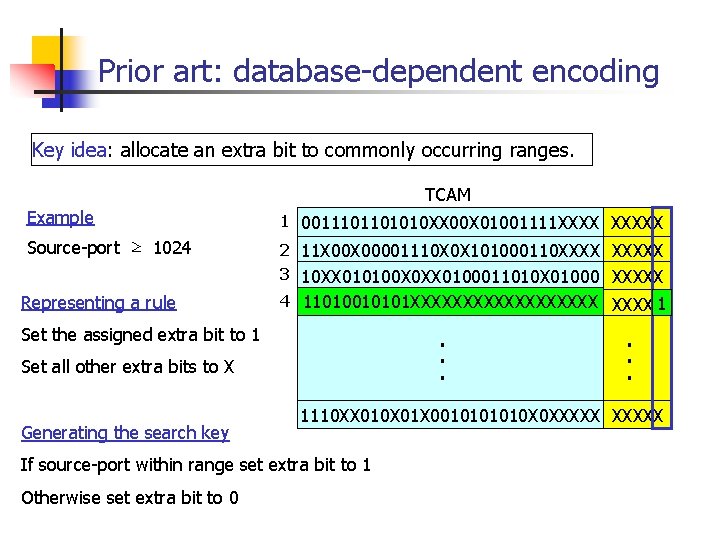
Prior art: database-dependent encoding Key idea: allocate an extra bit to commonly occurring ranges. TCAM Example 1 0011101101010 XX 00 X 01001111 XXXXX Source-port ≥ 1024 2 11 X 00001110 X 0 X 101000110 XXXXX 3 10 XX 010100 X 0 XX 0100011010 X 01000 XXXXX Representing a rule 4 001110 XXXXXXXXXXXX 11010010101 XXXXXXXXX 1 . . . Set the assigned extra bit to 1 Set all other extra bits to X Generating the search key 1110 XX 010 X 01 X 001010 X 0 XXXXX If source-port within range set extra bit to 1 Otherwise set extra bit to 0 . . .
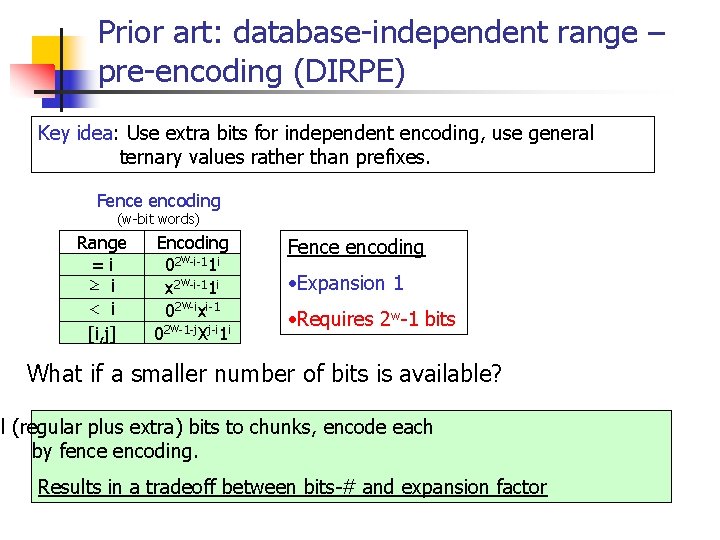
Prior art: database-independent range – pre-encoding (DIRPE) Key idea: Use extra bits for independent encoding, use general ternary values rather than prefixes. Fence encoding (w-bit words) Range =i ≥ i < i [i, j] Encoding 02 w-i-11 i x 2 w-i-11 i 02 w-ixi-1 02 w-1 -j. Xj-i 1 i Fence encoding • Expansion 1 • Requires 2 w-1 bits What if a smaller number of bits is available? ll (regular plus extra) bits to chunks, encode each by fence encoding. Results in a tradeoff between bits-# and expansion factor
![An Observation: The problem is equivalent to the DNF expression minimization problem R=[10, 11] An Observation: The problem is equivalent to the DNF expression minimization problem R=[10, 11]](http://slidetodoc.com/presentation_image/dc365bdf0834264edda2087a0adffcbf/image-11.jpg)
An Observation: The problem is equivalent to the DNF expression minimization problem R=[10, 11] b 1 b 0 + b 1 b’ 0 ≈ b 1 The general problem is NP-complete. “Computing the minimum DNF representation of boolean functions defined by interval” [Schieber, Geist, Zacks, 2005] • A linear-time algorithm for finding minimum-size DNF expression for any range of binary-coded numbers • Worst-case expansion for binary-encoded numbers is 2 W-4 Thanks to Ronny Roth for the reference to the paper
Talk outline n n n Definitions Problem definition, prior art The Short Range Gray Encoding Algorithm Experimental results Open questions
Our solution: Short-Range Gray Encoding (SRGE) Gain without pain: Range expansion reduction can be obtained without the use of extra bits by changing the encoding scheme (SRGE) SRGE can be combined with database-dependent scheme: the Hybrid-SRGE scheme Hybrid-SRGE yields range-expansion of only 1. 02 on real databases
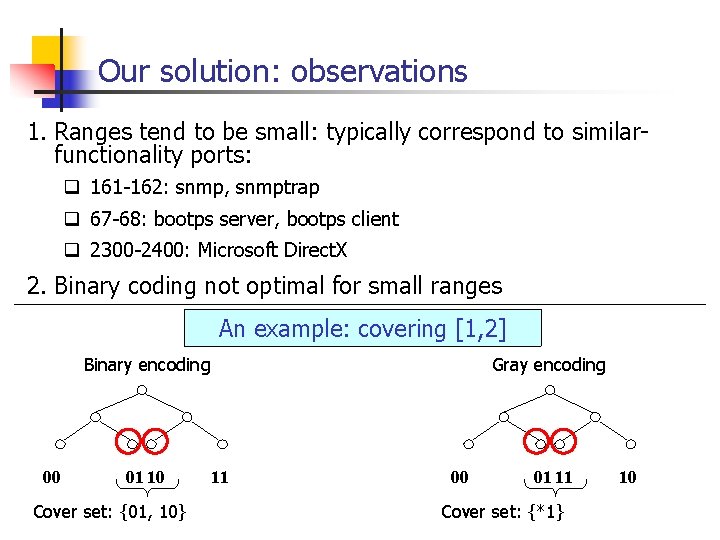
Our solution: observations 1. Ranges tend to be small: typically correspond to similarfunctionality ports: q 161 -162: snmp, snmptrap q 67 -68: bootps server, bootps client q 2300 -2400: Microsoft Direct. X 2. Binary coding not optimal for small ranges An example: covering [1, 2] Gray encoding Binary encoding 00 01 10 Cover set: {01, 10} 11 00 01 11 Cover set: {*1} 10
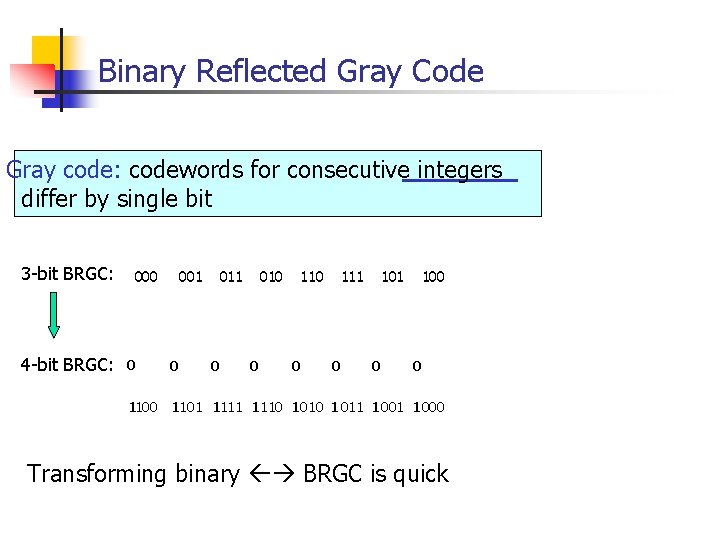
Binary Reflected Gray Code Gray code: codewords for consecutive integers differ by single bit 3 -bit BRGC: 4 -bit BRGC: 000 001 010 111 100 0 0 1101 1110 1010 1 011 1 001 1000 0 0 0 Transforming binary BRGC is quick
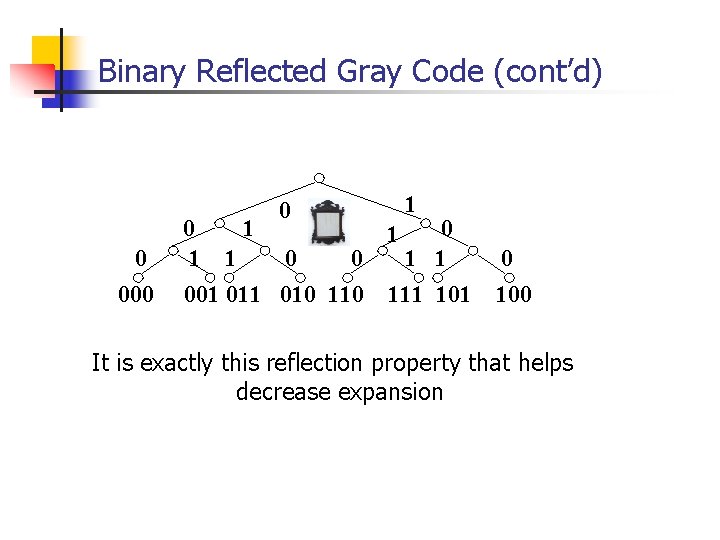
Binary Reflected Gray Code (cont’d) 0 0 000 1 0 1 1 1 0 0 1 1 001 010 111 101 0 100 It is exactly this reflection property that helps decrease expansion
![The SRGE algorithm Need to find minimum cover of [s, e] using gray coding. The SRGE algorithm Need to find minimum cover of [s, e] using gray coding.](http://slidetodoc.com/presentation_image/dc365bdf0834264edda2087a0adffcbf/image-17.jpg)
The SRGE algorithm Need to find minimum cover of [s, e] using gray coding. Find the least common ancestor p of point s and e p s e
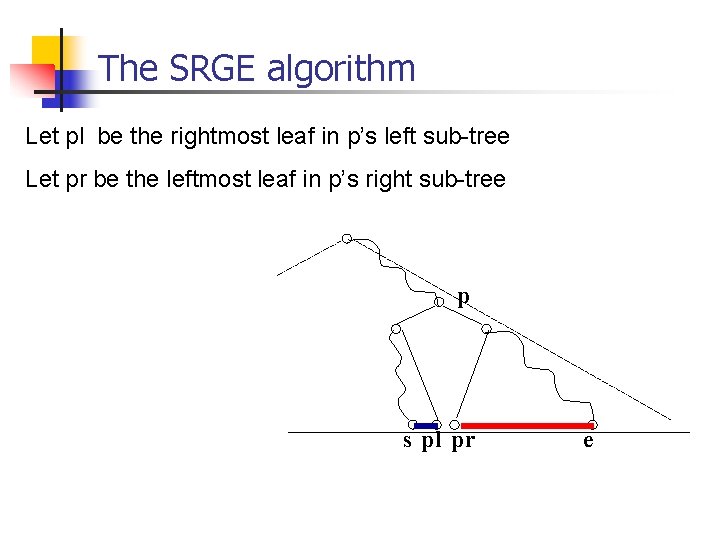
The SRGE algorithm Let pl be the rightmost leaf in p’s left sub-tree Let pr be the leftmost leaf in p’s right sub-tree p s pl pr e
![The SRGE algorithm First, we handle the smaller of: [s, pl], [e, pr] p The SRGE algorithm First, we handle the smaller of: [s, pl], [e, pr] p](http://slidetodoc.com/presentation_image/dc365bdf0834264edda2087a0adffcbf/image-19.jpg)
The SRGE algorithm First, we handle the smaller of: [s, pl], [e, pr] p s pl pr e
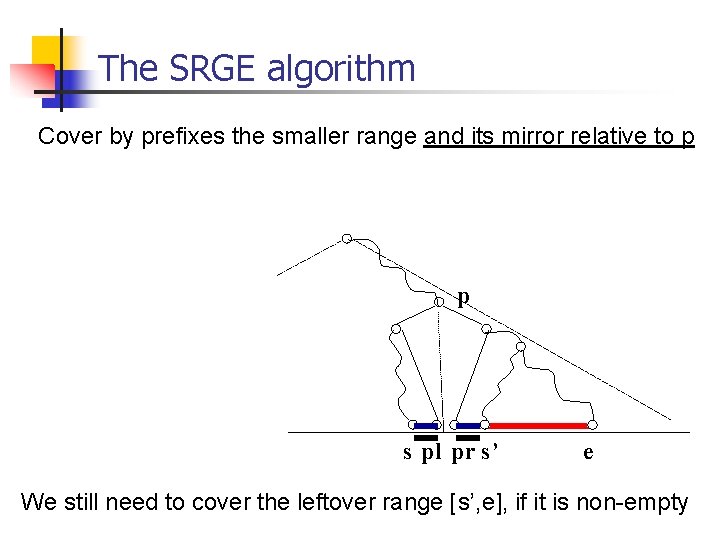
The SRGE algorithm Cover by prefixes the smaller range and its mirror relative to p p s pl pr s’ e We still need to cover the leftover range [s’, e], if it is non-empty
![The SRGE algorithm Repeat the previous procedure for the leftover: [s', e] • find The SRGE algorithm Repeat the previous procedure for the leftover: [s', e] • find](http://slidetodoc.com/presentation_image/dc365bdf0834264edda2087a0adffcbf/image-21.jpg)
The SRGE algorithm Repeat the previous procedure for the leftover: [s', e] • find their least common ancestor p’ • let pl' be the rightmost leaf in the left sub-tree of p' • let pr' be the leftmost leaf in the right sub-tree of p' p p’ s pr s' pl’ pr’ e
![The SRGE algorithm Two cases to consider: 1) |[pr', e]| > |[s', pl']|: q The SRGE algorithm Two cases to consider: 1) |[pr', e]| > |[s', pl']|: q](http://slidetodoc.com/presentation_image/dc365bdf0834264edda2087a0adffcbf/image-22.jpg)
The SRGE algorithm Two cases to consider: 1) |[pr', e]| > |[s', pl']|: q Cover [pr', e] by prefixes q The mirror of [pr', e] (relative to p') covers [s', pl'] p p’ s pr s’ pl’ pr’ e
![The SRGE algorithm 2) |[s', pl']|>|[pr', e']|: q Cover [pr', e] by prefixes. q The SRGE algorithm 2) |[s', pl']|>|[pr', e']|: q Cover [pr', e] by prefixes. q](http://slidetodoc.com/presentation_image/dc365bdf0834264edda2087a0adffcbf/image-23.jpg)
The SRGE algorithm 2) |[s', pl']|>|[pr', e']|: q Cover [pr', e] by prefixes. q Cover [s', pl'] by a single prefix, corresponding to left sub-tree of p ’ p p’ q ql s pr s’ pl’ pr’ e
Hybrid-SRGE • For each unique range, compute total number of redundant entries under SRGE • Deal with the most expensive ranges by using standard database-dependent encoding
Talk outline n n n Definitions Problem definition, prior art The Short Range Gray Encoding Algorithm Experimental results Future work
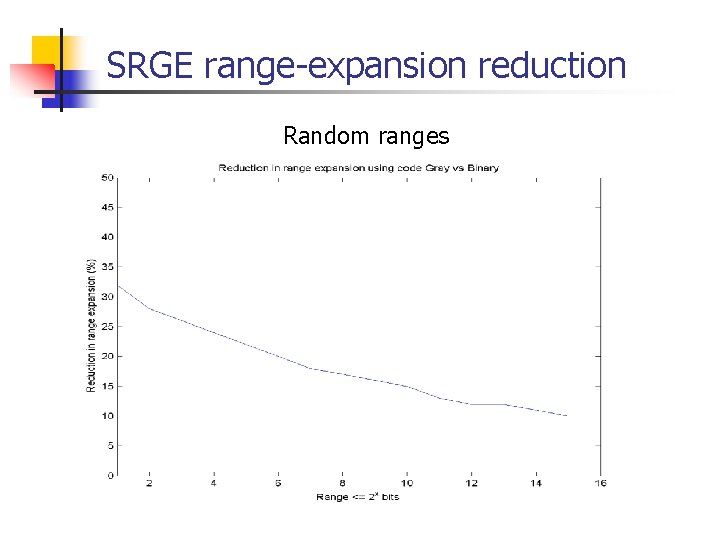
SRGE range-expansion reduction Random ranges
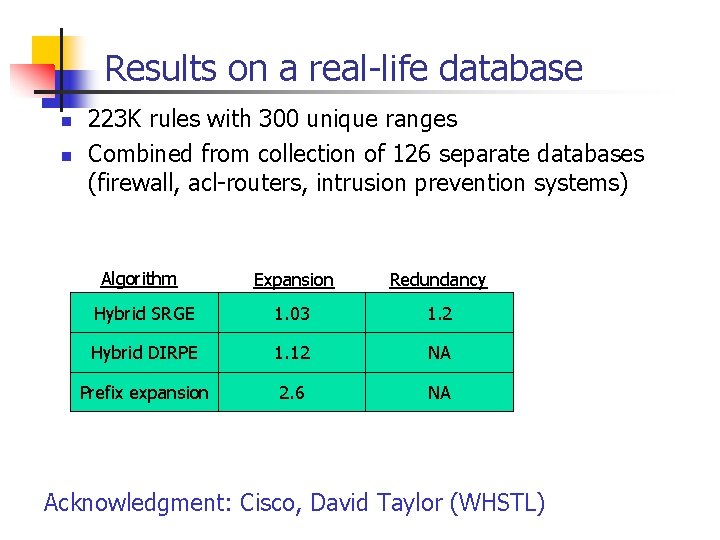
Results on a real-life database n n 223 K rules with 300 unique ranges Combined from collection of 126 separate databases (firewall, acl-routers, intrusion prevention systems) Algorithm Expansion Redundancy Hybrid SRGE 1. 03 1. 2 Hybrid DIRPE 1. 12 NA Prefix expansion 2. 6 NA Acknowledgment: Cisco, David Taylor (WHSTL)
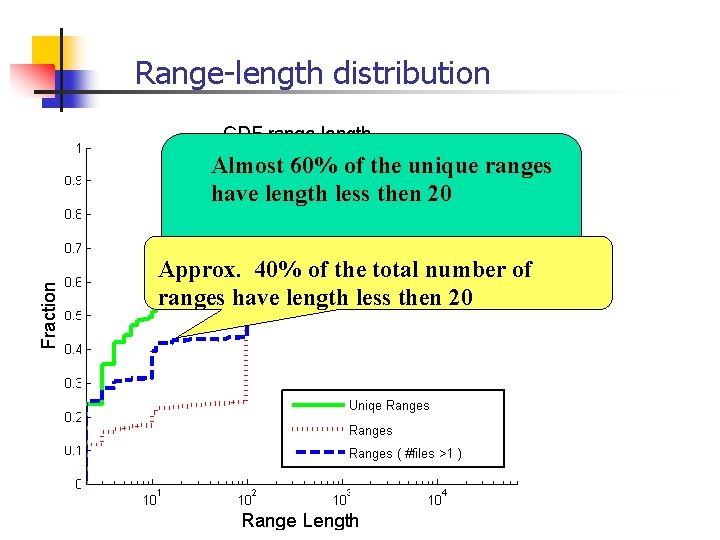
Range-length distribution Almost 60% of the unique ranges have length less then 20 Approx. 40% of the total number of ranges have length less then 20
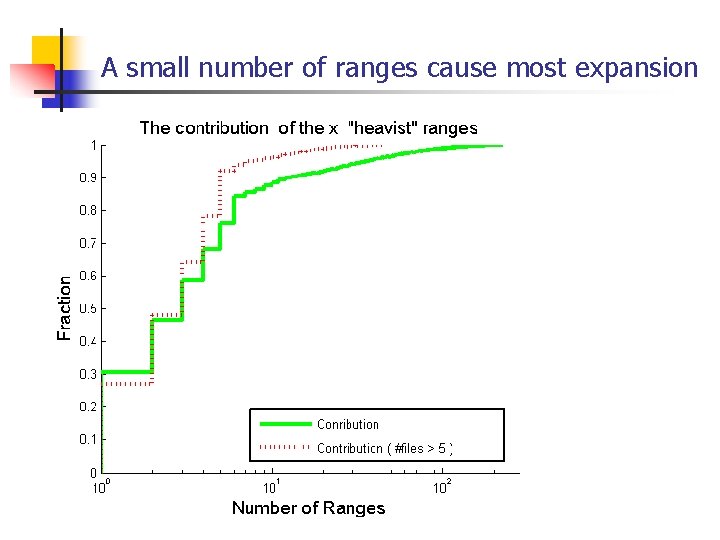
A small number of ranges cause most expansion
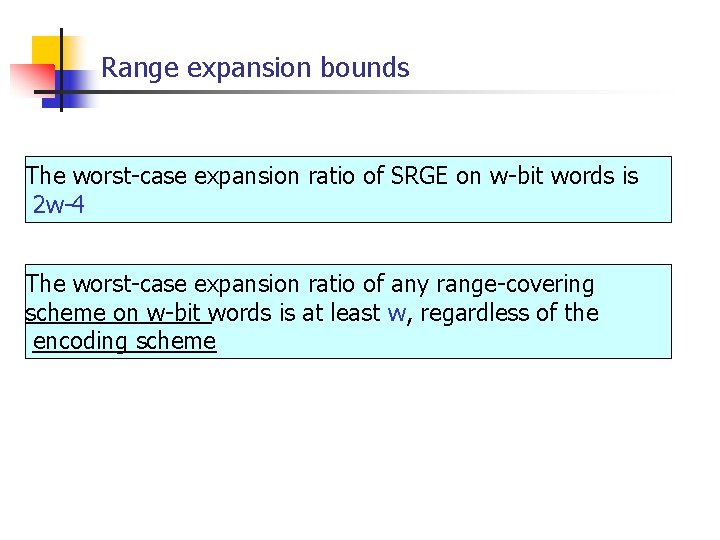
Range expansion bounds The worst-case expansion ratio of SRGE on w-bit words is 2 w-4 The worst-case expansion ratio of any range-covering scheme on w-bit words is at least w, regardless of the encoding scheme
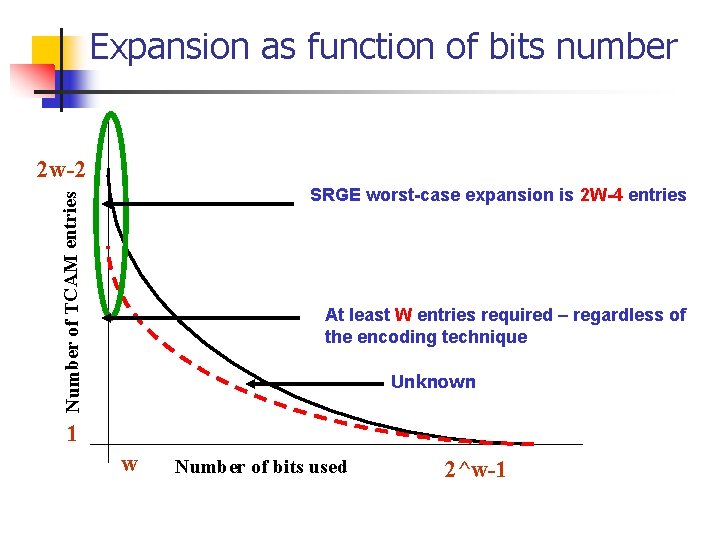
Expansion as function of bits number 2 w-2 Number of TCAM entries SRGE worst-case expansion is 2 W-4 entries At least W entries required – regardless of the encoding technique Unknown 1 w Number of bits used 2^w-1
Future work n n n Algorithms that combine RAM/TCAM What encoding scheme minimizes worst-case expansion ratio? What is its expansion ratio? Finding efficient TCAM algorithms for other applications (e. g. , intrusion detection)
- Slides: 32