Inference Problem Access Control Policies Direct access n
Inference Problem
Access Control Policies Direct access n Information flow n Not addressed: indirect data access n Lecture 19 CSCE 522 - Farkas 2
Indirect Information Flow Channels Covert channels n Inference channels n Lecture 19 CSCE 522 - Farkas 3
Inference Channels Non-sensitive information Lecture 19 + Meta-data CSCE 522 - Farkas = Sensitive Information 4
Inference Channels Statistical Database Inferences n General Purpose Database Inferences n Lecture 19 CSCE 522 - Farkas 5
Statistical Databases n Goal: provide aggregate information about groups of individuals ¨ E. g. , n Security risk: specific information about a particular individual ¨ E. g. , n average grade point of students grade point of student John Smith Meta-data: ¨ Working knowledge about the attributes ¨ Supplementary knowledge (not stored in database) Lecture 19 CSCE 522 - Farkas 6
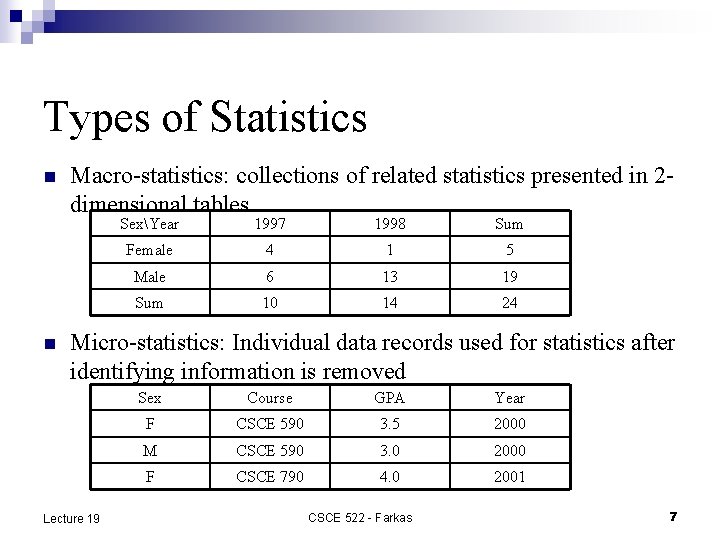
Types of Statistics n n Macro-statistics: collections of related statistics presented in 2 dimensional tables SexYear 1997 1998 Sum Female 4 1 5 Male 6 13 19 Sum 10 14 24 Micro-statistics: Individual data records used for statistics after identifying information is removed Lecture 19 Sex Course GPA Year F CSCE 590 3. 5 2000 M CSCE 590 3. 0 2000 F CSCE 790 4. 0 2001 CSCE 522 - Farkas 7
Statistical Compromise Exact compromise: find exact value of an attribute of an individual (e. g. , John Smith’s GPA is 3. 8) n Partial compromise: find an estimate of an attribute value corresponding to an individual (e. g. , John Smith’s GPA is between 3. 5 and 4. 0) n Lecture 19 CSCE 522 - Farkas 8
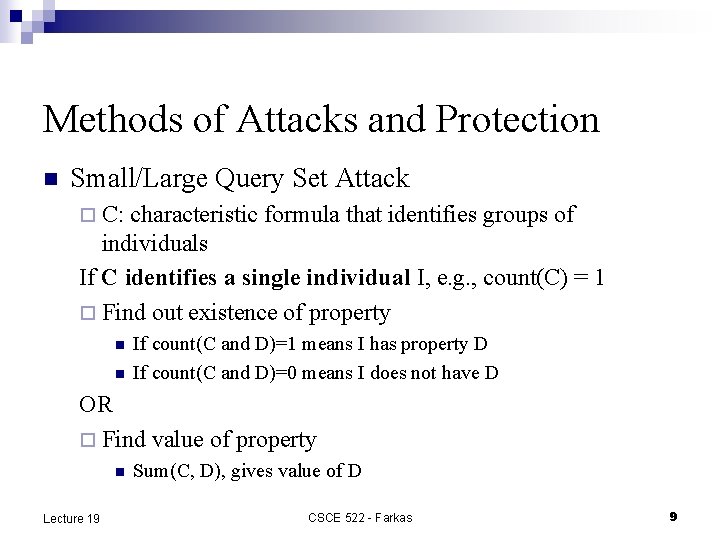
Methods of Attacks and Protection n Small/Large Query Set Attack ¨ C: characteristic formula that identifies groups of individuals If C identifies a single individual I, e. g. , count(C) = 1 ¨ Find out existence of property n n If count(C and D)=1 means I has property D If count(C and D)=0 means I does not have D OR ¨ Find value of property n Lecture 19 Sum(C, D), gives value of D CSCE 522 - Farkas 9
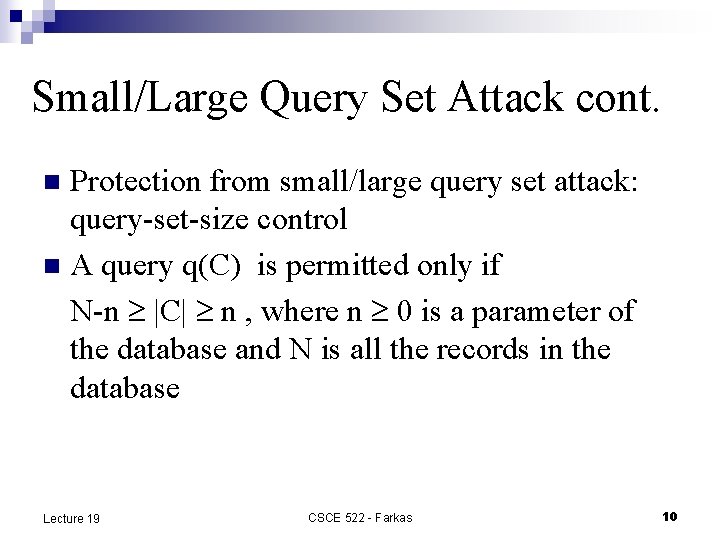
Small/Large Query Set Attack cont. Protection from small/large query set attack: query-set-size control n A query q(C) is permitted only if N-n |C| n , where n 0 is a parameter of the database and N is all the records in the database n Lecture 19 CSCE 522 - Farkas 10
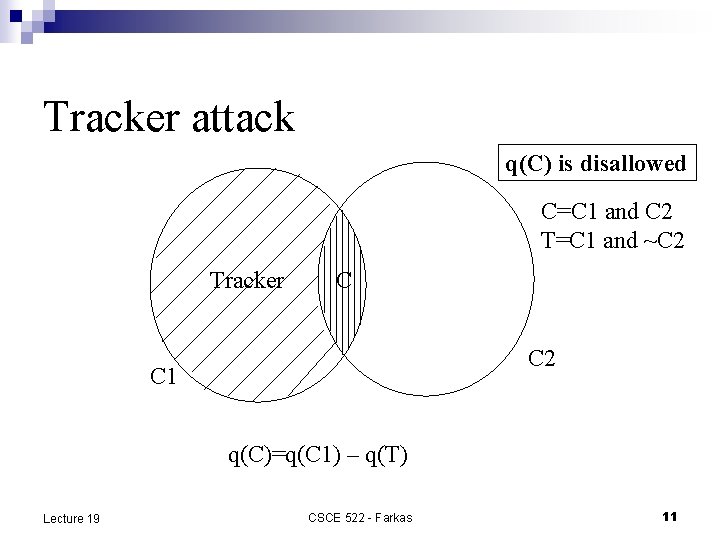
Tracker attack q(C) is disallowed C=C 1 and C 2 T=C 1 and ~C 2 Tracker C C 2 C 1 q(C)=q(C 1) – q(T) Lecture 19 CSCE 522 - Farkas 11
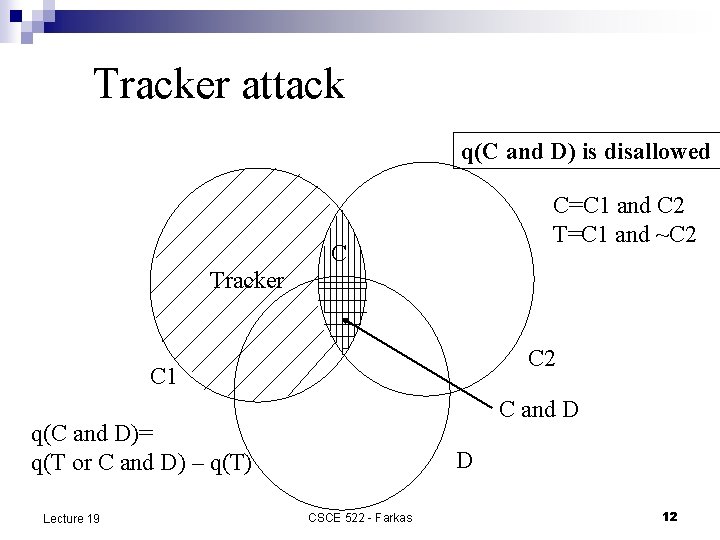
Tracker attack q(C and D) is disallowed C=C 1 and C 2 T=C 1 and ~C 2 C Tracker C 2 C 1 C and D q(C and D)= q(T or C and D) – q(T) Lecture 19 D CSCE 522 - Farkas 12
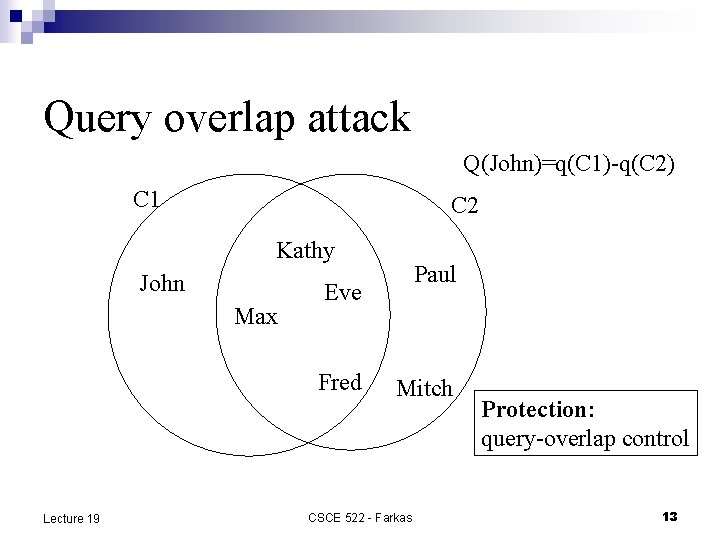
Query overlap attack Q(John)=q(C 1)-q(C 2) C 1 C 2 Kathy John Max Eve Fred Lecture 19 Paul Mitch CSCE 522 - Farkas Protection: query-overlap control 13
Insertion/Deletion Attack n Observing changes overtime ¨ q 1=q(C) ¨ insert(i) ¨ q 2=q(C) ¨ q(i)=q 2 -q 1 n Protection: insertion/deletion performed as pairs Lecture 19 CSCE 522 - Farkas 14
Statistical Inference Theory n Give unlimited number of statistics and correct statistical answers, all statistical databases can be compromised (Ullman) Lecture 19 CSCE 522 - Farkas 15
Privacy Preserving Data Mining Related to statistical DB privacy n We will cover it later in the semester n Lecture 19 CSCE 522 - Farkas 16
Inferences in General-Purpose Databases Queries based on sensitive data n Inference via database constraints n Inferences via updates n Lecture 19 CSCE 522 - Farkas 17
Queries based on sensitive data Sensitive information is used in selection condition but not returned to the user. n Example: Salary: secret, Name: public n Name Salary=$25, 000 n Protection: apply query of database views at different security levels Lecture 19 CSCE 522 - Farkas 18
How to mitigate this problem? Time of evaluation n Architecture n Lecture 19 CSCE 522 - Farkas 19
Database Constraints Integrity constraints n Database dependencies n Key integrity n Lecture 19 CSCE 522 - Farkas 20
Integrity Constraints C=A+B n A=public, C=public, and B=secret n B can be calculated from A and C, i. e. , secret information can be calculated from public data n Lecture 19 CSCE 522 - Farkas 21
Database Dependencies Metadata: n Functional dependencies n Multi-valued dependencies n Join dependencies n etc. Lecture 19 CSCE 522 - Farkas 22
Functional Dependency n n FD: A B, that is for any two tuples in the relation, if they have the same value for A, they must have the same value for B. Example: FD: Rank Salary Secret information: Name and Salary together Query 1: Name and Rank ¨ Query 2: Rank and Salary ¨ Combine answers for query 1 and 2 to reveal Name and Salary together ¨ n See slides in dissertation-farkas-rotated. pdf Lecture 19 CSCE 522 - Farkas 23
Key integrity Every tuple in the relation have a unique key n Users at different levels, see different versions of the database n Users might attempt to update data that is not visible for them n Lecture 19 CSCE 522 - Farkas 24
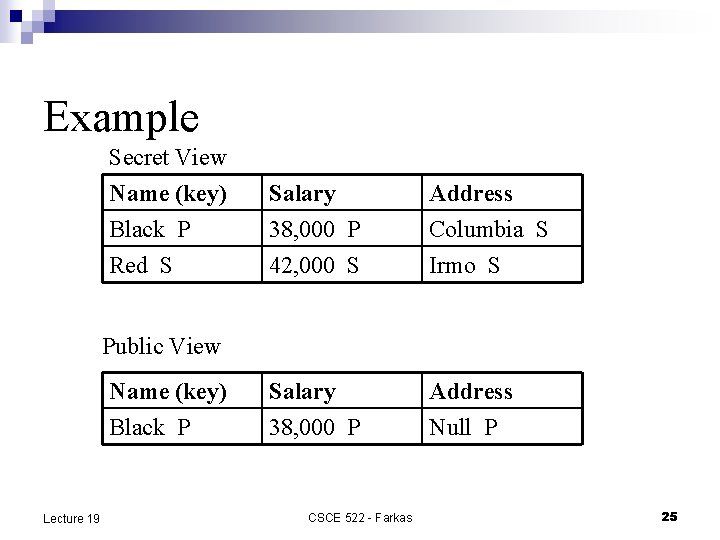
Example Secret View Name (key) Black P Red S Salary 38, 000 P 42, 000 S Address Columbia S Irmo S Salary 38, 000 P Address Null P Public View Name (key) Black P Lecture 19 CSCE 522 - Farkas 25
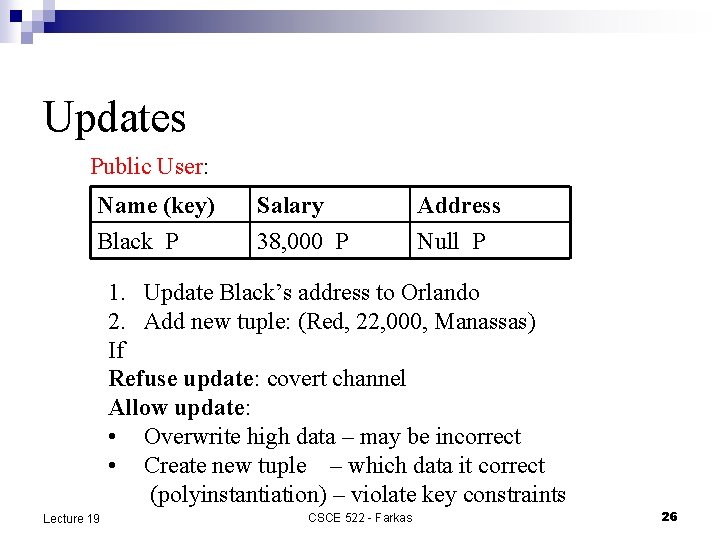
Updates Public User: Name (key) Black P Salary 38, 000 P Address Null P 1. Update Black’s address to Orlando 2. Add new tuple: (Red, 22, 000, Manassas) If Refuse update: covert channel Allow update: • Overwrite high data – may be incorrect • Create new tuple – which data it correct (polyinstantiation) – violate key constraints Lecture 19 CSCE 522 - Farkas 26
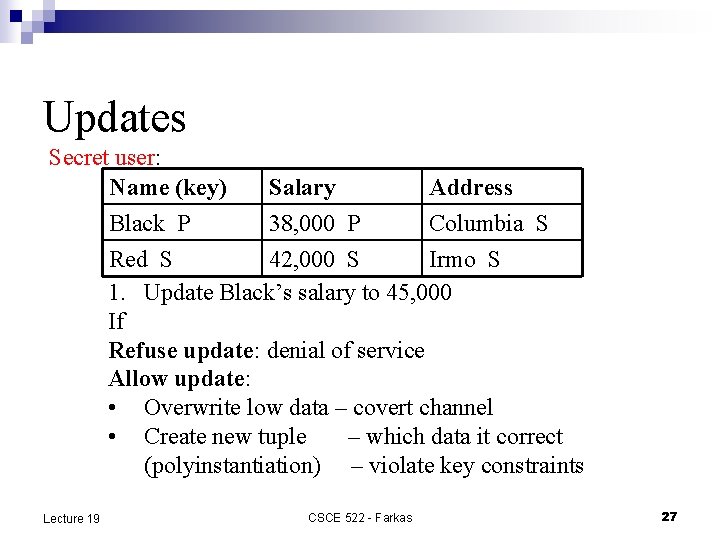
Updates Secret user: Name (key) Salary Address Black P 38, 000 P Columbia S Red S 42, 000 S Irmo S 1. Update Black’s salary to 45, 000 If Refuse update: denial of service Allow update: • Overwrite low data – covert channel • Create new tuple – which data it correct (polyinstantiation) – violate key constraints Lecture 19 CSCE 522 - Farkas 27
Inference Problem No general technique is available to solve the problem n Need assurance of protection n Hard to incorporate outside knowledge n Lecture 19 CSCE 522 - Farkas 28
- Slides: 28