Increase Wiresharks Effectiveness by Tapping your Network Data
Increase Wireshark’s Effectiveness by Tapping your Network Data Wednesday, April 2, 2008 Chris Bihary Managing Director | Network Critical SHARKFEST '08 Foothill College March 31 - April 2, 2008 SHARKFEST '08 | Foothill College | March 31 - April 2, 2008
Agenda • Introduction • Network Monitoring Basics • How do I connect Wireshark to my network? • What is Access Technology? • New Access Technology • Questions & Answers SHARKFEST '08 | Foothill College | March 31 - April 2, 2008
Introduction • • Chris Bihary, Network Critical • Managing Director, Americas • 716 -558 -7282 direct • chris. bihary@networkcritical. com Mark Manion, Network Critical • Channel Manager, West Coast • 716 -558 -7282 direct • mark. manion@networkcritical. com Sam Battaglia, Network Critical • Technical Manager • (716) 558 -0881 direct • samuel. battaglia@networkcritical. com SHARKFEST '08 Network Critical | Foothill College | March 31 - April 2, 2008
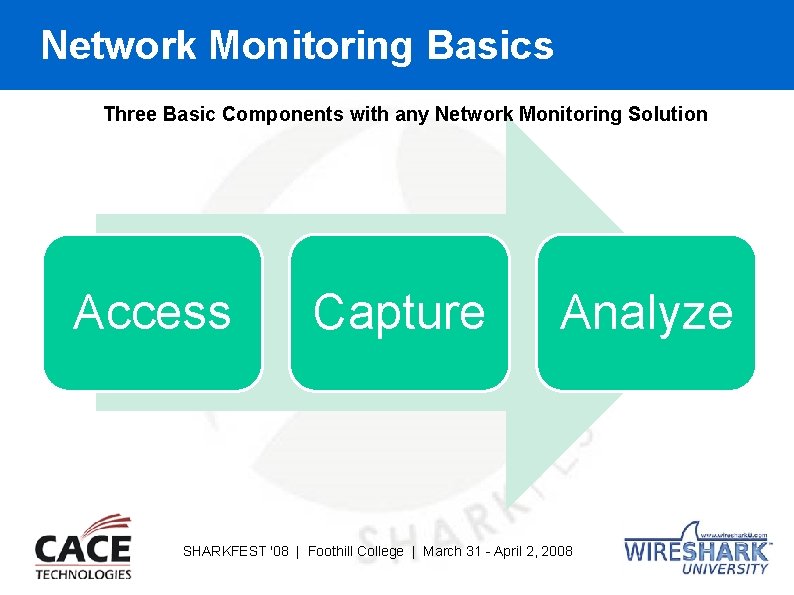
Network Monitoring Basics Three Basic Components with any Network Monitoring Solution Access Capture Analyze SHARKFEST '08 | Foothill College | March 31 - April 2, 2008
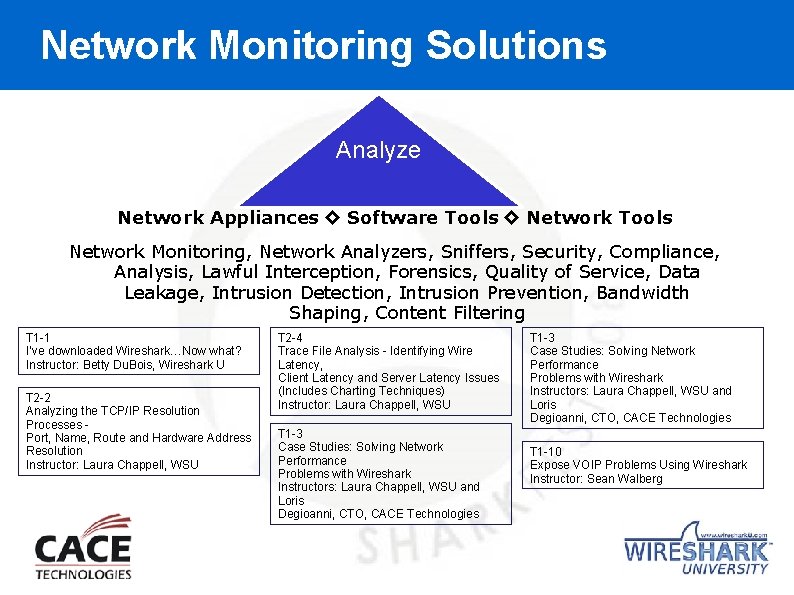
Network Monitoring Solutions Analyze Network Appliances ◊ Software Tools ◊ Network Tools Network Monitoring, Network Analyzers, Sniffers, Security, Compliance, Analysis, Lawful Interception, Forensics, Quality of Service, Data Leakage, Intrusion Detection, Intrusion Prevention, Bandwidth Shaping, Content Filtering T 1 -1 I’ve downloaded Wireshark…Now what? Instructor: Betty Du. Bois, Wireshark U T 2 -2 Analyzing the TCP/IP Resolution Processes Port, Name, Route and Hardware Address Resolution Instructor: Laura Chappell, WSU T 2 -4 Trace File Analysis - Identifying Wire Latency, Client Latency and Server Latency Issues (Includes Charting Techniques) Instructor: Laura Chappell, WSU T 1 -3 Case Studies: Solving Network Performance Problems with Wireshark Instructors: Laura Chappell, WSU and Loris Degioanni, CTO, CACE Technologies T 1 -10 Expose VOIP Problems Using Wireshark Instructor: Sean Walberg
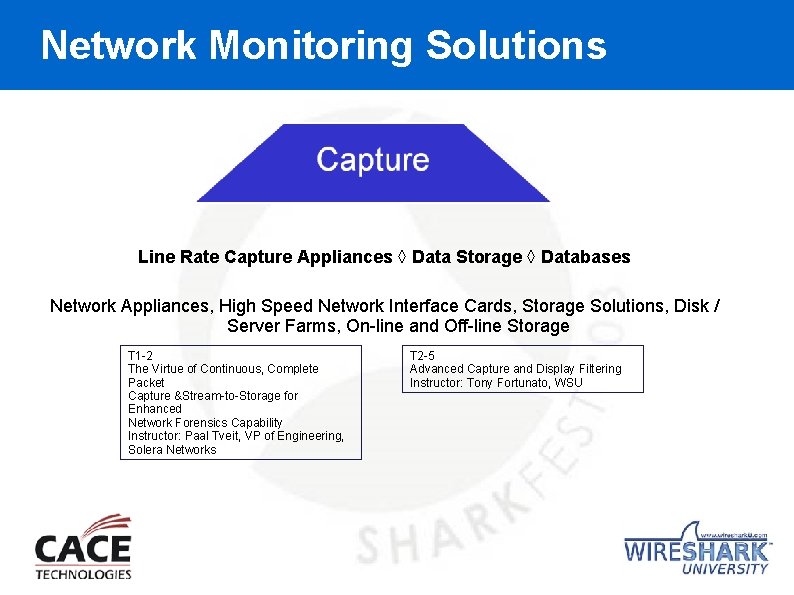
Network Monitoring Solutions Line Rate Capture Appliances ◊ Data Storage ◊ Databases Network Appliances, High Speed Network Interface Cards, Storage Solutions, Disk / Server Farms, On-line and Off-line Storage T 1 -2 The Virtue of Continuous, Complete Packet Capture &Stream-to-Storage for Enhanced Network Forensics Capability Instructor: Paal Tveit, VP of Engineering, Solera Networks T 2 -5 Advanced Capture and Display Filtering Instructor: Tony Fortunato, WSU
Network Monitoring Solutions How do I access the data on my Network?
Why worry about Network Access? A network appliance / software / network tool is only as good as the access it gets. Downtime can stem from poor management practices, often where access is an afterthought. A Gartner study found that the typical large business experienced an average of 87 hours of downtime a year, at $42, 000 per hour = $3. 6 million annually
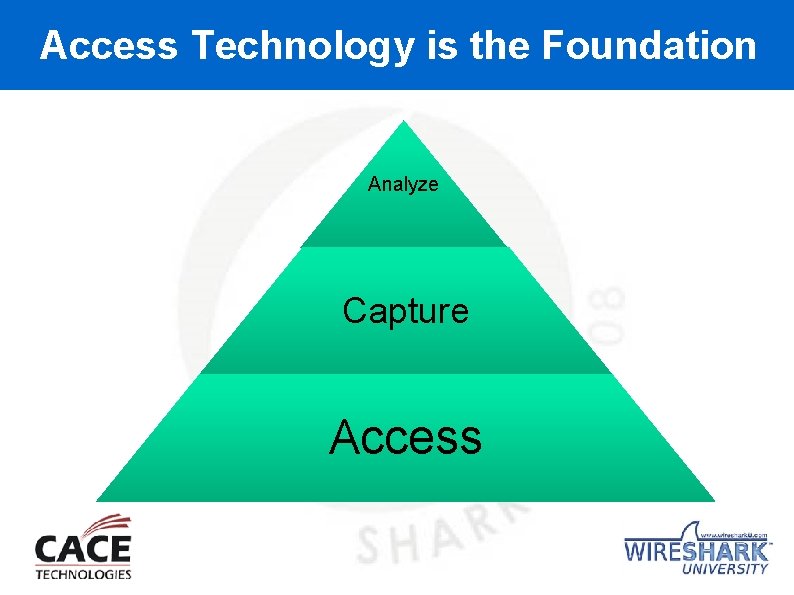
Access Technology is the Foundation Analyze Capture Access
How do I connect to Wireshark to the Network? 10/100 Hub SPAN or Mirrored Ports (switches) TAP – Traffic Access Point It’s simple, I need access to the data!
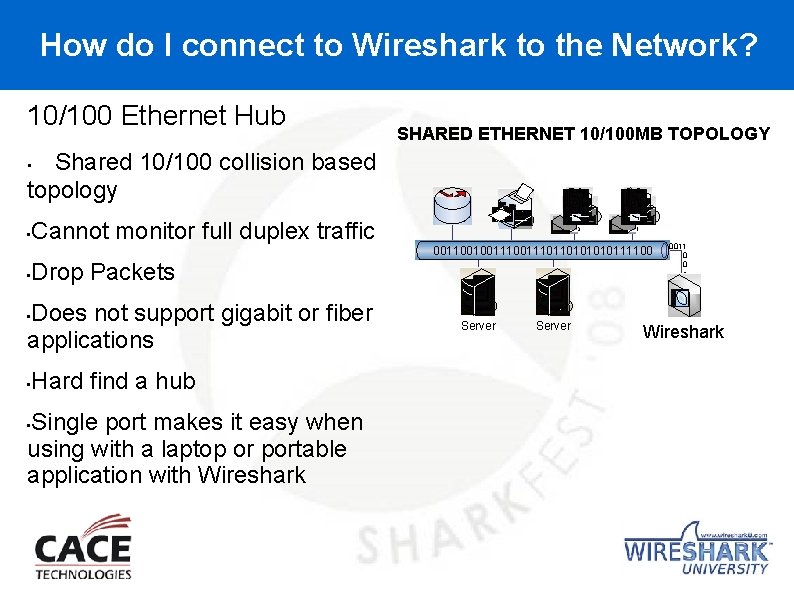
How do I connect to Wireshark to the Network? 10/100 Ethernet Hub SHARED ETHERNET 10/100 MB TOPOLOGY Shared 10/100 collision based topology • • ` Cannot monitor full duplex traffic ` 001100100111011010111100 • Drop Packets Does not support gigabit or fiber applications • • Hard find a hub Single port makes it easy when using with a laptop or portable application with Wireshark • Server 0011 0 0 1 1 1 0 Wireshark
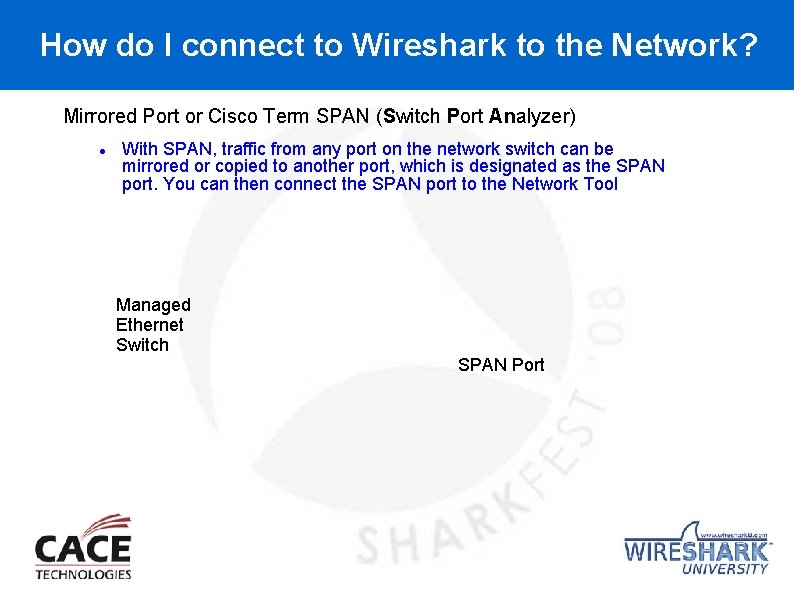
How do I connect to Wireshark to the Network? Mirrored Port or Cisco Term SPAN (Switch Port Analyzer) With SPAN, traffic from any port on the network switch can be mirrored or copied to another port, which is designated as the SPAN port. You can then connect the SPAN port to the Network Tool Managed Ethernet Switch SPAN Port
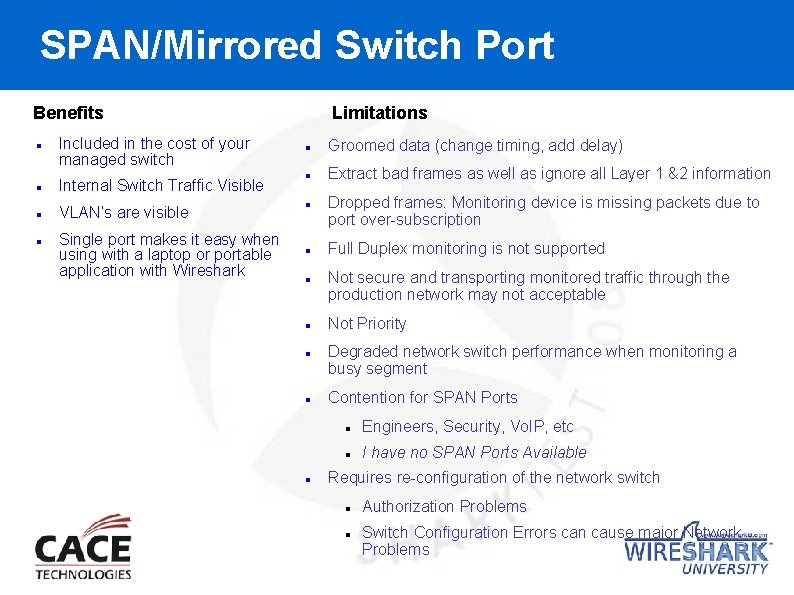
SPAN/Mirrored Switch Port Limitations Benefits Included in the cost of your managed switch Internal Switch Traffic Visible VLAN’s are visible Single port makes it easy when using with a laptop or portable application with Wireshark Groomed data (change timing, add delay) Extract bad frames as well as ignore all Layer 1 &2 information Dropped frames: Monitoring device is missing packets due to port over-subscription Full Duplex monitoring is not supported Not secure and transporting monitored traffic through the production network may not acceptable Not Priority Degraded network switch performance when monitoring a busy segment Contention for SPAN Ports Engineers, Security, Vo. IP, etc I have no SPAN Ports Available Requires re-configuration of the network switch Authorization Problems Switch Configuration Errors can cause major Network Problems
SPAN/Mirrored Switch Port Data Monitoring Access: SPAN Port or Passive TAP? What’s on your Network? Part 1 Is SPAN port a viable data access technology for today’s business critical networks especially with today’s access needs for Data Security Compliance and Lawful Intercept requirements? Not really, see why ! by Tim O’Neill from BT Solutions From Cisco’ on SPAN port usability –From Cisco’s White Paper – Using the Cisco Span port for SAN analysis “Cisco warns that the switch treats SPAN data with a lower priority than regular port-to-port data. In other words, if any resource under load must choose between passing normal traffic and SPAN data, the SPAN loses and the mirrored frames are arbitrarily discarded. This rule applies to preserving network traffic in any situation. For instance, when transporting remote SPAN traffic through an Inter Switch Link (ISL) which shares the ISL bandwidth with regular network traffic, the network traffic takes priority. If there is not enough capacity for the remote SPAN traffic, the switch drops it. Knowing that the SPAN port arbitrarily drops traffic under specific load conditions, what strategy should users adopt so as not to miss frames? According to Cisco, the best strategy is to make decisions based on the traffic levels of the configuration and when in doubt to use the SPAN port only for relatively low-throughput situations. “ Read the entire article by accessing http: //www. lovemytool. com/blog/2007/08/span-ports-or-t. html
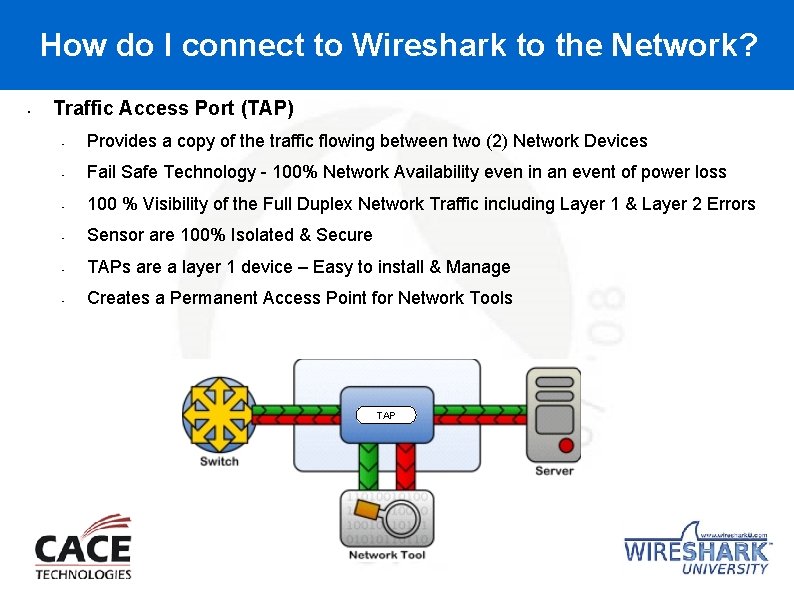
How do I connect to Wireshark to the Network? • Traffic Access Port (TAP) • Provides a copy of the traffic flowing between two (2) Network Devices • Fail Safe Technology - 100% Network Availability even in an event of power loss • 100 % Visibility of the Full Duplex Network Traffic including Layer 1 & Layer 2 Errors • Sensor are 100% Isolated & Secure • TAPs are a layer 1 device – Easy to install & Manage • Creates a Permanent Access Point for Network Tools TAP
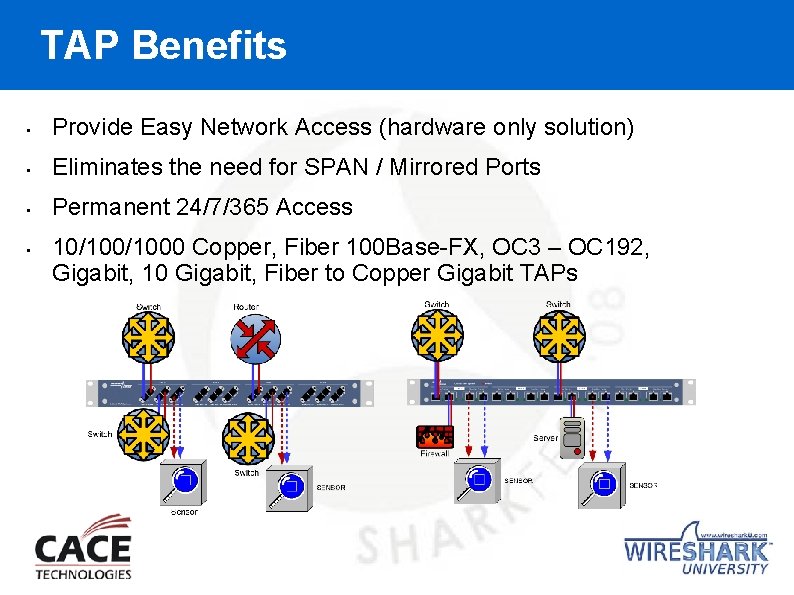
TAP Benefits • Provide Easy Network Access (hardware only solution) • Eliminates the need for SPAN / Mirrored Ports • Permanent 24/7/365 Access • 10/1000 Copper, Fiber 100 Base-FX, OC 3 – OC 192, Gigabit, 10 Gigabit, Fiber to Copper Gigabit TAPs
TAP Benefits • Simple Layer 1 Passive Hardware Device • Easy to Install • Provides Permanent Access • 100% Network Availability No Single Point of Failure • 100% Visibility to Network Traffic • Eliminate the need for a SPAN Port • Cost effective • Save $$$$, No Network Downtime Make your life easier when deploying & managing Wireshark
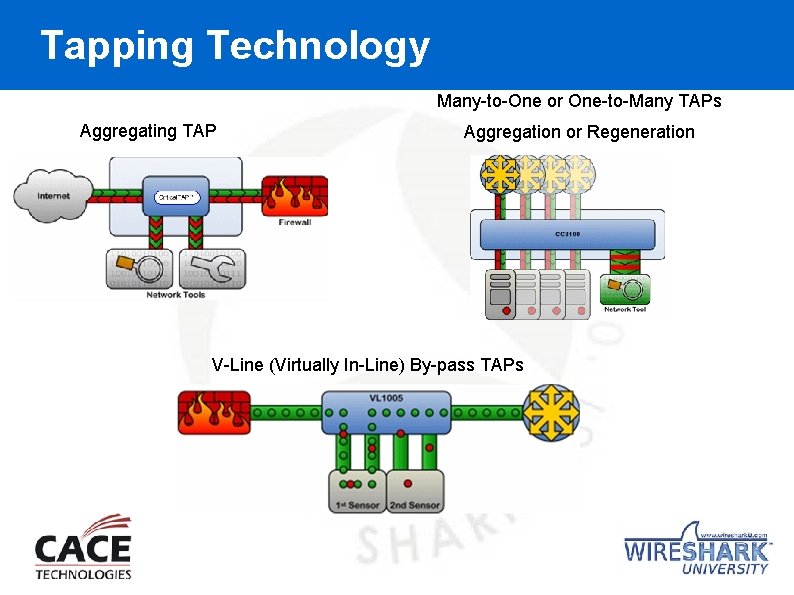
Tapping Technology Many-to-One or One-to-Many TAPs Aggregating TAP Aggregation or Regeneration V-Line (Virtually In-Line) By-pass TAPs
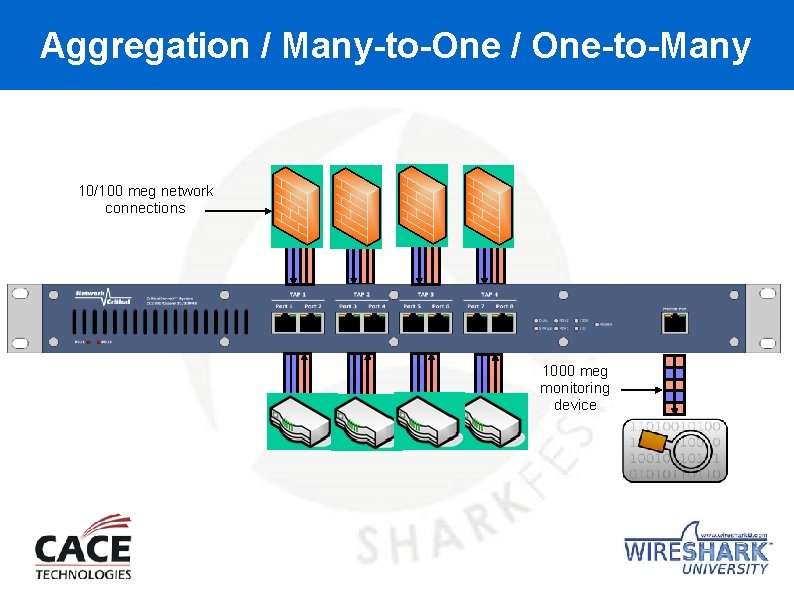
Aggregation / Many-to-One / One-to-Many 10/100 meg network connections CRITICALCONNEX™ MANY TO ONE 1000 meg monitoring device
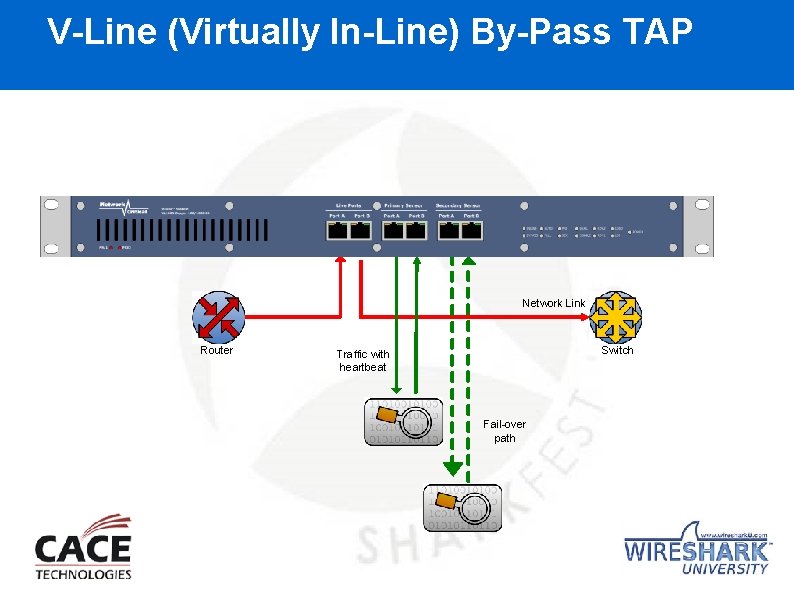
V-Line (Virtually In-Line) By-Pass TAP Network Link Router Switch Traffic with heartbeat Fail-over path
TAP Your Network for Wireshark • Easily connect your Wireshark Analyzer • 10/1000 Copper • Multi-mode Gigabit Fiber • Single Mode Gigabit Fiber • • Provide a single copper monitoring port for laptops & single port mobile devices Install & Monitor

TAP Your Network for Wireshark
Access Technology Solutions Building a Proper Infrastructure Access Solution Building a foundation to support the Monitoring Applications for enterprise customers Complex, High Availability, Multi-locations Zero Failure Point created by Access Equipment 100% Visibility to Network Traffic No Data Loss Data is not groomed, changed or effected No Network Latency created by Access Points Invisible, non-intrusive access to the network Secure Access Points Flexible Access Points support multiple Capture & Analysis Tools
Access Technology Solutions Building a Proper Infrastructure Access Solution Bandwidth on networks is not unlimited Allow Core Switches, Distribution Switches, Access Switches, and Router to be designed for Live Network Traffic Only Do not design a Access Point requiring re-transmission over the Live Network Build your infrastructure with Access Points from day one
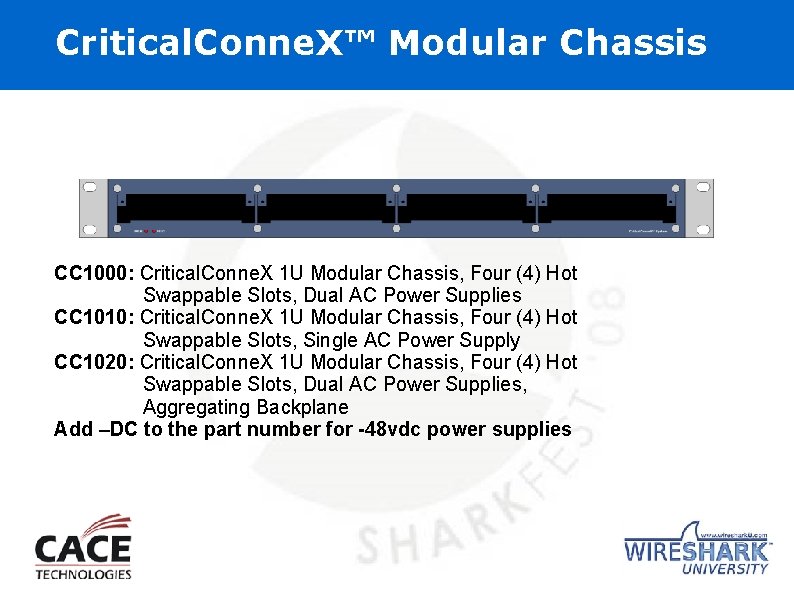
Critical. Conne. X™ Modular Chassis CC 1000: Critical. Conne. X 1 U Modular Chassis, Four (4) Hot Swappable Slots, Dual AC Power Supplies CC 1010: Critical. Conne. X 1 U Modular Chassis, Four (4) Hot Swappable Slots, Single AC Power Supply CC 1020: Critical. Conne. X 1 U Modular Chassis, Four (4) Hot Swappable Slots, Dual AC Power Supplies, Aggregating Backplane Add –DC to the part number for -48 vdc power supplies
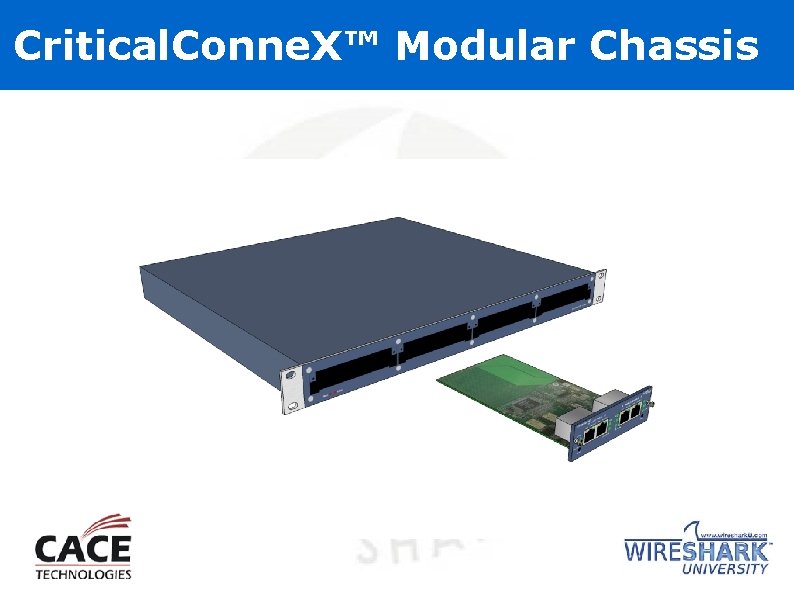
Critical. Conne. X™ Modular Chassis
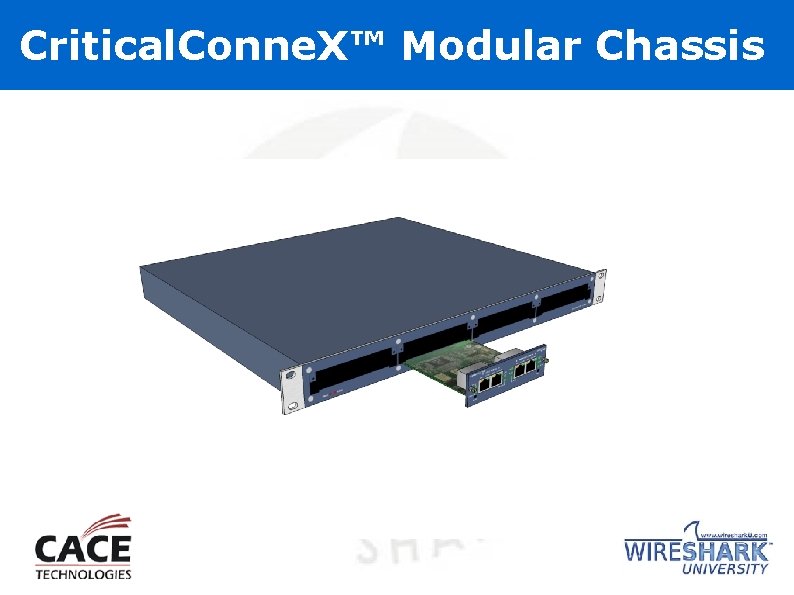
Critical. Conne. X™ Modular Chassis

Critical. Conne. X™ Modular Chassis
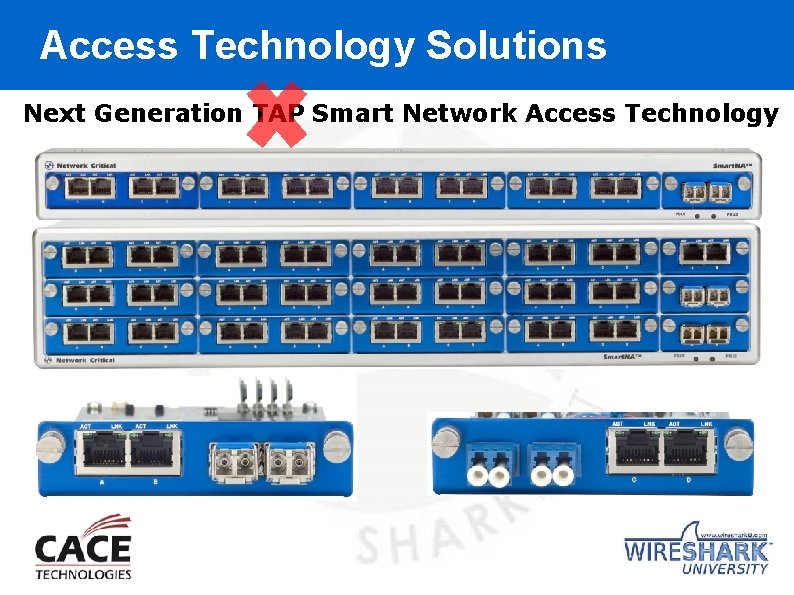
Access Technology Solutions Next Generation TAP Smart Network Access Technology
Any Questions? ANALYZE CAPTURE ACCESS
- Slides: 30