Incident Management By MarcAndr Lger DESS MASc PHDcandidate
Incident Management By Marc-André Léger DESS, MASc, PHD(candidate) Winter 2008
Save the forest • If you really need to print… • Please do not print out more than one module at a time as it may evolve…
Session 2 Computer security policies
Security policy
Who Should Be Concerned • Managers • System designers • Users: what are the policy’s impacts on their actions, and what are the ramifications of not following policy • System administrators, support personnel who manage enforcement technologies and processes • Company lawyers: they may have to use the written policies in support of actions taken against employees in violation
Policy Hierarchy
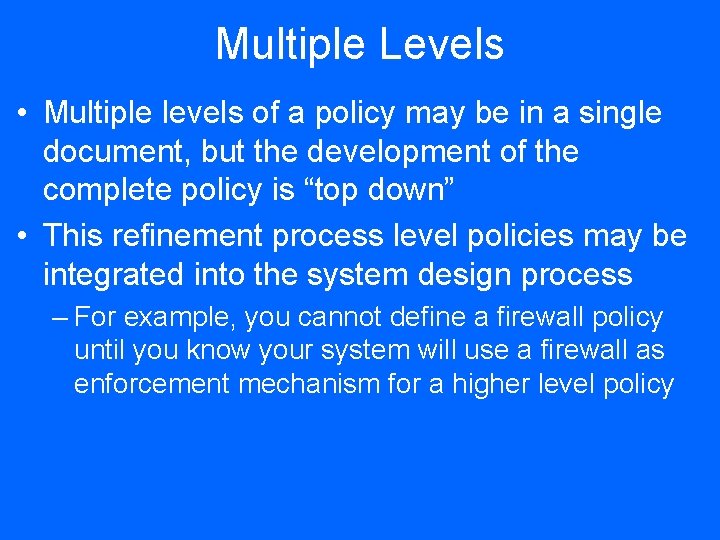
Multiple Levels • Multiple levels of a policy may be in a single document, but the development of the complete policy is “top down” • This refinement process level policies may be integrated into the system design process – For example, you cannot define a firewall policy until you know your system will use a firewall as enforcement mechanism for a higher level policy
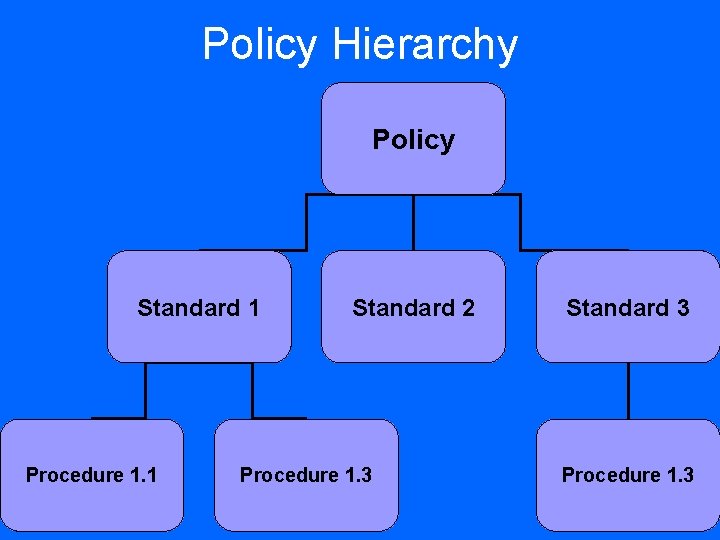
Policy Hierarchy Policy Standard 1 Procedure 1. 1 Standard 2 Procedure 1. 3 Standard 3 Procedure 1. 3
Example of Hierarchical Policies • High level: “company proprietary information shall be protected from release to unauthorized personnel”
Mid level procedural policy • All proprietary information shall have a committee responsible for its control • A member of that committee must authorize any distribution of that material • Enforcement: training, audit
Mid level technology policy • Proprietary information may only be stored on protected systems, accessible only to those with authorized access to the proprietary information • There shall be no externally initiated, automated means to retrieve information from the protected systems – Low level; e. g. , a firewall rule blocking incoming traffic on ports 20 (ftp data), 21 (ftp control), and 69 (tftp) – The firewall is the enforcement mechanism
Policy • Sets boundaries
Policy • Greek – Politeia: citizenship – Polis: city • Focused on creating sense of organisational citizenship amongst staff • Compliance with policy – good citizen of organisational city; entitled to benefits of city
Policy • Definition: Course of action adopted by a business, etc. * • Development – Core team – business representatives – Reviewed & approved by governing body * Oxford Dictionary of Current English, 1998
Policy • Communication mechanism – Executive level + Employees – Defines how discipline is viewed – Provides direction • Explains what organisational behaviour is supported – Specific actions prepared to take related to discipline – Actions to be taken when directives not followed • Not there to undermine way people work – Should educate employees, not scare them
3 P model • Prevent: provide proactive measures and awareness training • Protect: provide baseline processes to implement technology and controls • Punish: provide an incremental punitive process so you can enforce it at the appropriate time (cohersion)
Using standard • Standards can be usefull to help define what is allowed within the organisational boundary
Standards • Definition: – Object, quality or measure serving as basis to which others conform or should conform or by which others are judged – Level of excellence or quality required or specified • Development – Core team – subject matter experts
Standards • Standards are agreement between parties • Specific set of rules to operate more uniformly & effectively • Sets level of expectation • Ensures consistent operations – Minimise risk – Increase efficiency
Procedures • How we act within the organisational boundary • How we achieve rules set out in standards How to milk a cow… 1. 2. 3. 4. 5. Bring cow into barn Tell cow to stand still Fetch bucket and stool Sit on stool next to cow Squirt milk into bucket
Procedures • Definition(s) – Way of performing a task • OR – Series of actions conducted in a certain manner • Development – Individuals responsible for daily tasks
Procedures • Operational communication mechanism • Plans / steps addressing specifics of how to go about particular action • Transfer of knowledge between individuals who perform same job • Reflect best practices / repetitive actions followed
Procedures • Provide detail to enable performance of function without having to ask: – What – Where – Who
Examples • Policy Statement – All users will be authenticated with passwords that are changed on a periodic basis before being allowed access to the organisation’s information resources.
Examples • Standard Statements – All passwords will be a minimum length of seven characters and contain alphabetical, numeric and special characters. – User passwords will be changed every thirty days. – The last ten passwords will be stored to prevent re -utilisation thereof.
Examples • Procedure Statement – To assign a password to a new user id, select the User ID in the User Manager and right-click to view its properties. – Select the password field and enter a password that conforms to the organisation’s password standards.
Drivers • Compliance – Laws & regulations • Audit requirements – Against which audit can be conducted • Good practice – Industry standards • Risk management – Manage risks related to employee behaviour
Policy Lifecycle
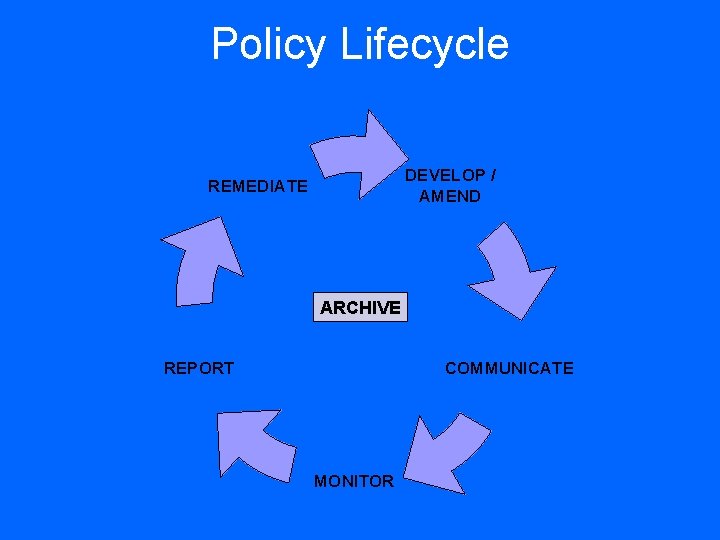
Policy Lifecycle DEVELOP / AMEND REMEDIATE ARCHIVE REPORT COMMUNICATE MONITOR
Policy Lifecycle • Develop / Amend – Acquire senior level sponsorship & sign-off – Involve stakeholders in formulation – Ensure consistency with other policies
Policy Lifecycle • Communicate – Use existing channels – Avoid jargon – Include third parties
Policy Lifecycle • Monitor – Gather data related to compliance with policy – Aggregate data – Analyse data
Policy Lifecycle • Report – Provide organisational wide view of policy compliance – Identify breaches for investigation – Report to executive stakeholders
Policy Lifecycle • Remediate – Understand problematic areas – Revise policy on periodic basis – Address policies that are impractical
Policy Lifecycle • Archive – Adopt strict version control – Archive in case of legal or employment-related action – Process as official records
Common Problems • Fail to impact users ‘on the ground’ • Difficult to reflect organisation’s vision & mission • Difficult to entrench in daily operations – nuisance factor • Users ignorant of policy’s existence • Users do not fully understand document • Too long or too technical
Effective Policies • • • Understandable Meaningful & practical Implementable, enforceable & realistic Inviting document Addresses users directly Convincing
Effective Policies • Incorporates: – Nature of organisation – Organisational risk appetite – Organisational culture
Policy Development
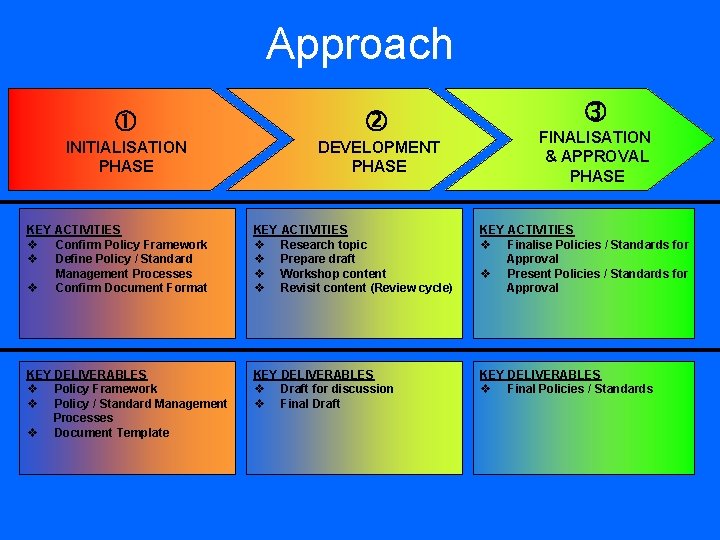
Approach INITIALISATION PHASE DEVELOPMENT PHASE FINALISATION & APPROVAL PHASE KEY ACTIVITIES Confirm Policy Framework Define Policy / Standard Management Processes Confirm Document Format KEY ACTIVITIES Research topic Prepare draft Workshop content Revisit content (Review cycle) KEY ACTIVITIES Finalise Policies / Standards for Approval Present Policies / Standards for Approval KEY DELIVERABLES Policy Framework Policy / Standard Management Processes Document Template KEY DELIVERABLES Draft for discussion Final Draft KEY DELIVERABLES Final Policies / Standards
Approach • Content Development – No ‘cut & paste’ – Developed in conjunction with stakeholder representation – not only technical staff – Wording of principle statements very important
Key Success Factors • Styling – Consistent with overall communication style – Fit in with organisational culture – User-friendly & clear – no ‘thou shallt nots’ • Formatting – Short, easy to read (1 - 5 pages) – Visual impact
Key Success Factors • Writing style – Reflect organisational culture & industry – Clear, comprehensive – no ambiguity – Avoid specific references to technology
Key Success Factors • Presentation – Fun & attractive – Short, concise, to the point – Main document – brief, interesting cartoons, dialogue – Supplementary policies, standards & guidelines to support & detail specific topics – Quality deliverable - underlines importance
Key Success Factors • Commitment – Buy-in from top management vital – people live by example – Change of attitude & behaviour starts at top – Truly effective policy has support from all levels in organisation

Key Success Factors • Governance Processes – Content Review • All stakeholders – Quality Assurance
Policy Communication

Communication • Dissemination – Users need to know about policy – Various methods • • Paper-based or electronic copies Published on internal communication sites Summarised policy on colourful brochures Awareness sessions – Creativity very important – marketing-drive

Policy Monitoring & Reporting
Monitoring & Reporting • Monitoring / Auditing – Internal / External Audits – Employee Surveys / Competitions – Key Performance Indicators (KPIs) • Disciplinary Action
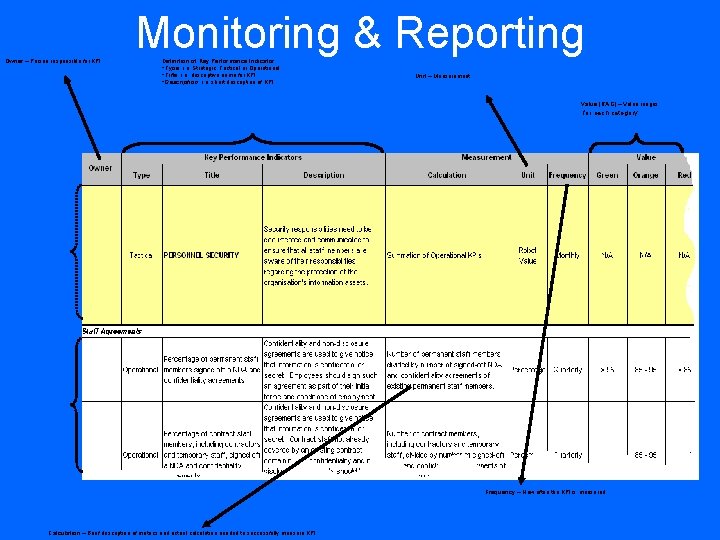
Monitoring & Reporting Owner – Person responsible for KPI Definition of Key Performance Indicator Type, i. e. Strategic, Tactical or Operational Title, i. e. descriptive name for KPI Description, i. e. short description of KPI - Unit – Measurement Value (RAG) – Value ranges for each category Frequency – How often the KPI is measured Calculation – Brief description of metrics and actual calculation needed to successfully measure KPI

Policy Remediation
Remediation • Maintenance – Living document – Grow & develop with organisation – Advantages of regular updates • In touch with organisational developments • Ensures document does not become static & outdated – Change Management
Information Security & Acceptable Usage Policy
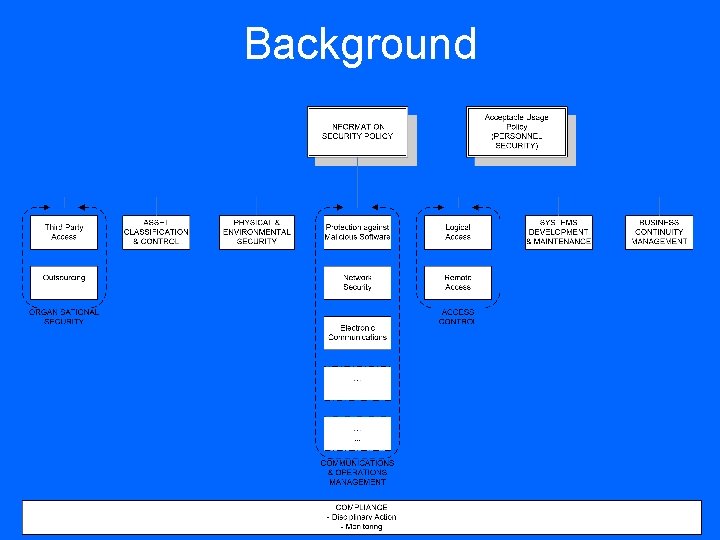
Background
Background • Importance of Information Security Policy – Explains need for information security to all role players – Explains information security concepts & methods – Outlines roles & responsibilities of information security organisation – Guides selection, use & management of appropriate controls • Tools & Technology • Processes
Background • Importance of Acceptable Usage Policy – Explains information security rules & boundaries to everyday users – Guides behaviour, use & management of information – Explains what may / may not be done with organisation’s information – Outlines roles & responsibilities users – Supports Information Security Policy
Structure 1. Introduction 2. Executive Management Commitment 3. Compliance Statement 4. Policy Principles 5. Roles & Responsibilities 6. Appendices
Content • Introduction – Need for Information Security • Brief, introductory, emphasises organisation’s dependence on information – Objectives & Benefits of Information Security • Linked to overall business strategy, goals, objectives, nature of business – Definition of Information Security • Brief, understandable, uniform understanding
Content • Management Commitment – Demonstrates intention of succeeding with Information Security • Approval of Policy (Signature) – Prominent placing, highest signatory in organisation
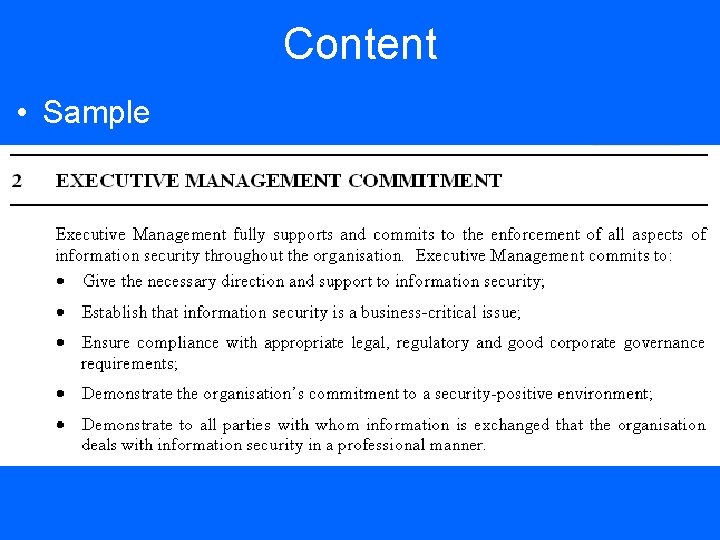
Content • Sample
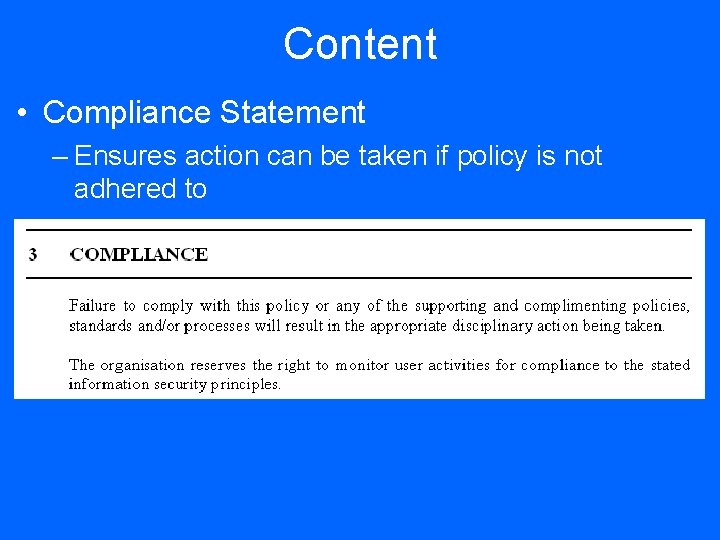
Content • Compliance Statement – Ensures action can be taken if policy is not adhered to
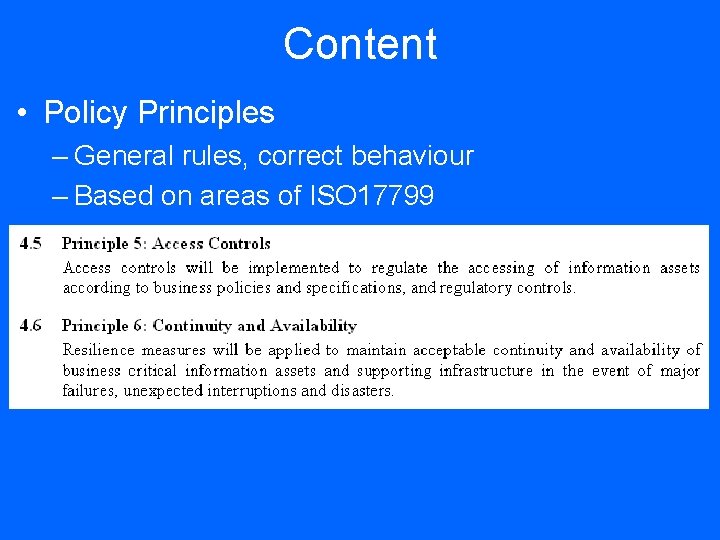
Content • Policy Principles – General rules, correct behaviour – Based on areas of ISO 17799
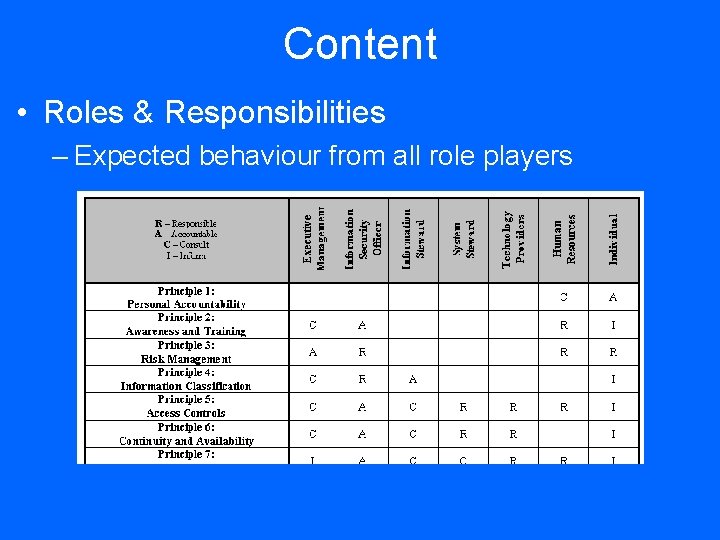
Content • Roles & Responsibilities – Expected behaviour from all role players
Content • Appendices – User Declaration – Abridged version of policy – Glossary – Cross-references to other policies, standards, procedures
Content • General Elements – Reference Number – Release Date – Version – Policy Review Statement • Forces continuous improvement to implementation of policy – Statement of Applicability
Development Guidance • International Information Security Standards & Code of Practices – BS 7799 / ISO 17799 / ISO 27001 – BSI IT Baseline Protection Manual – COBIT – ISO 13335 -1 – ISF’s Standard of Good Practice
Information security policy Based on ISO/IEC 27002(2005) Section 5. 1
ISO 27002 Control Objective • To provide management direction and support for information security in accordance with business requirements and relevant laws and regulations.
Information security policy document ISO/IEC 27002(2005) Control 5. 1. 1
ISO 27002 Control • An information security policy document should be approved by management, and published and communicated to all employees and relevant external parties.
Implementation guidance • The information security policy document should state management commitment and set out the organization’s approach to managing information security.
Other information • The information security policy might be a part of a general policy document. • If the information security policy is distributed outside the organisation, care should be taken not to disclose sensitive information.
Review of the information security policy ISO/IEC 27002(2005) Control 5. 1. 2
ISO 27002 Control • The information security policy should be reviewed at planned intervals or if significant changes occur to ensure its continuing suitability, adequacy, and effectiveness.
Implementation guidance • The information security policy should have an owner who has approved management responsibility for the development, review, and evaluation of the security policy. • The review should include assessing opportunities for improvement of the organization’s information security policy and approach to managing information security in response to changes to the organizational environment, business circumstances, legal conditions, or technical environment. The review of the information security policy should take account of the results of management reviews. • There should be defined management review procedures, including a schedule or period of the review.
Input • The input to the management review should include information on: a) feedback from interested parties; b) results of independent reviews (see 6. 1. 8); c) status of preventive and corrective actions (see 6. 1. 8 and 15. 2. 1); d) results of previous management reviews; e) process performance and information security policy compliance; f) changes that could affect the organization’s approach to managing information security, including changes to the organizational environment, business circumstances, resource availability, contractual, regulatory, and legal conditions, or to the technical environment; g) trends related to threats and vulnerabilities; h) reported information security incidents (see 13. 1); i) recommendations provided by relevant authorities (see 6. 1. 6).
Output • The output from the management review should include any decisions and actions related to: a) improvement of the organization’s approach to managing information security and its processes; b) improvement of control objectives and controls; c) improvement in the allocation of resources and/or responsibilities. • A record of the management review should be maintained. • Management approval for the revised policy should be obtained.
End of this session
- Slides: 79