Implementing Data Encryption Opportunities and Challenges Beth E
Implementing Data Encryption Opportunities and Challenges Beth E. Binde Bruce T. Rights Harold W. Winshel Copyright Beth E. Binde, Bruce T. Rights and Harold W. Winshel 2008. This work is the intellectual property of the authors. Permission is granted for this material to be shared for non-commercial, educational purposes, provided that this copyright statement appears on the reproduced materials and notice is given that the copying is by permission of the authors. To disseminate otherwise or to republish requires written permission from the authors.
Implementing Data Encryption Housekeeping • Speaker backgrounds • Cell phones (as well as other devices that beep, chirp and otherwise distract) EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Agenda • Define terms • Why implement encryption? • Which encryption package to implement? • What concerns need to be addressed during implementation? • Product demonstration EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption What is data encryption? • Protecting data by concealing the meaning • Reduces impact of data theft • Helps protect Data At Rest EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Three states of data Data at rest Data in transit EDUCAUSE Mid-Atlantic Regional Conference Data in process
Implementing Data Encryption Why implement encryption? • Protect confidential data – Non-public personal information (NPPI) – Intellectual property • Regulatory requirements EDUCAUSE Mid-Atlantic Regional Conference
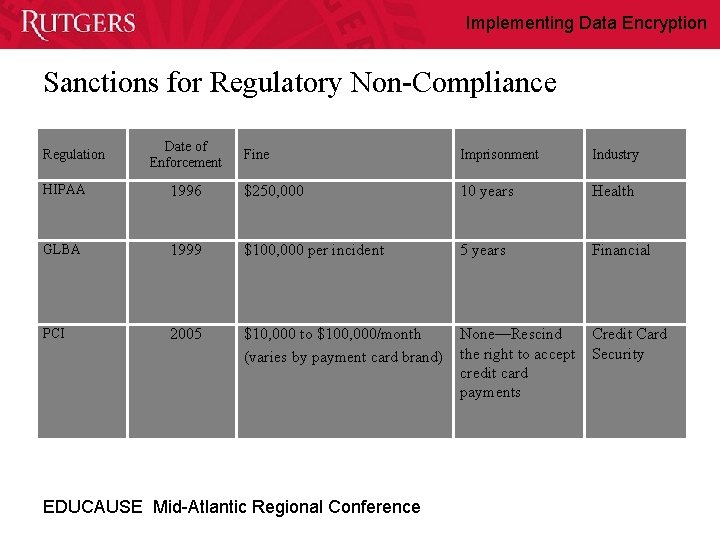
Implementing Data Encryption Sanctions for Regulatory Non-Compliance Regulation Date of Enforcement Fine Imprisonment Industry HIPAA 1996 $250, 000 10 years Health GLBA 1999 $100, 000 per incident 5 years Financial PCI 2005 $10, 000 to $100, 000/month (varies by payment card brand) None—Rescind the right to accept credit card payments Credit Card Security EDUCAUSE Mid-Atlantic Regional Conference
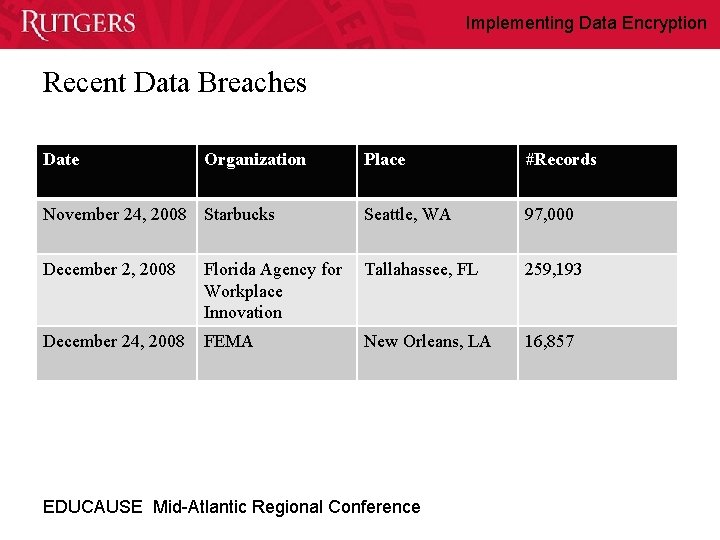
Implementing Data Encryption Recent Data Breaches Date Organization Place #Records November 24, 2008 Starbucks Seattle, WA 97, 000 December 2, 2008 Florida Agency for Workplace Innovation Tallahassee, FL 259, 193 December 24, 2008 FEMA New Orleans, LA 16, 857 EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption vs. Data Breach Pay now … or pay later EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Caution! • Don’t trust a secret or proprietary algorithm or roll your own – Public scrutiny by multiple experts finds the flaws – Public scrutiny beneficial • Protect keys – Keys essential for decryption – Even knowing the algorithm is not sufficient • Don’t rely on any single technology or measure for security EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Safeboot: Product of Choice • • • Gartner Magic Quadrant recommendation GSA SMARTBuy product Centrally managed Provides audit logs Supports Full Disk Encryption as well as Content Encryption (File/Folder Encryption) • Password recovery, both local and remote • Price EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Additional Product Features • • • Initial disk encryption operation runs in background Multiple permission levels (32!) Easy back up of managed systems Seamless integration following login process Pre-boot authentication EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Implementation: Precautions • Marginal disks are more likely to fail while being exercised during the encryption process – Backup prior to encryption (especially for deans, directors, department chairs and other entities above your pay grade) • Practice on a test machine • Provide training for systems administrators • Document, document and document EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Housekeeping: • I recently had a stroke, and it affects my verbal skills. • I have no problem understanding you but I may need to self-correct as I speak. I appreciate your patience. • I’ll try to speak slowly. EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Housekeeping (continued): • If I’m unclear, don’t hesitate to ask me to repeat it. • If, after three times, my repetition is still unclear, give up! • (Actually, feel free to see me after the session or email me. ) EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Implementation Precautions: • Don’t encrypt the Dean’s PC WITHOUT FIRST BACKING UP! • Don’t encrypt any PC without first backing up • Assume the hard drive may (will) fail EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Policy Objective: • If you have a clear business need for juicy stuff to be stored on your computer, you have to have authorization in writing. EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Implementation Objectives: • Initially, all notebooks with juicy stuff are to be encrypted. • “Juicy stuff” is, certainly among other things, defined as student social security numbers. • After that, all notebooks – regardless of content – are to be encrypted. • The reason: notebook PC’s travel a lot, are more subject to being stolen, are becoming more and more popular as opposed to desktop PC, etc. EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Concerns of Users: • Will I be locked out – on campus, or off campus? • Does encryption add a new risk to the data? – No. It adds a nominal amount of currently existing risk. – You should be backing up for data anyway. – Example: PC could be lost, stolen, or experience mechanical failure. • How long will it take to have a password reset? EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption If Encryption’s So Great, How Come Everyone Doesn’t Use It? • Lack of awareness of reporting requirements if a PC stolen or lost • Cost of purchase • Time – – Product evaluation and testing Installation and maintenance Staff training User education • Loss of data due to corruption of encrypted disks • Possible temporary lock out due to forgotten passwords EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Product Demonstrations • End user point of view • Administrator point of view EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Concluding thoughts • • What is encryption? Why do you need it? Encryption as part of an overall security posture Sharing experiences to help you EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Executive Summary EDUCAUSE Mid-Atlantic Regional Conference
Implementing Data Encryption Questions? • Beth Binde binde@rutgers. edu • Bruce Rights brights@rci. rutgers. edu • Harold Winshel winshel@camden. rutgers. edu EDUCAUSE Mid-Atlantic Regional Conference
- Slides: 24