Implementation of Protected Extensible Protocol PEAP An IEEE
Implementation of Protected Extensible Protocol (PEAP) – An IEEE 802. 1 x wireless LAN standard for authentication Master Thesis Proposal By Nirmala Bulusu Advisor – Dr. Edward Chow
What is PEAP ? Ø PEAP is an 802. 1 x authentication protocol typically designed for access control in wireless LANs Ø It makes use of two well known protocols • Extensible Authentication Protocol • Transport Layer Security
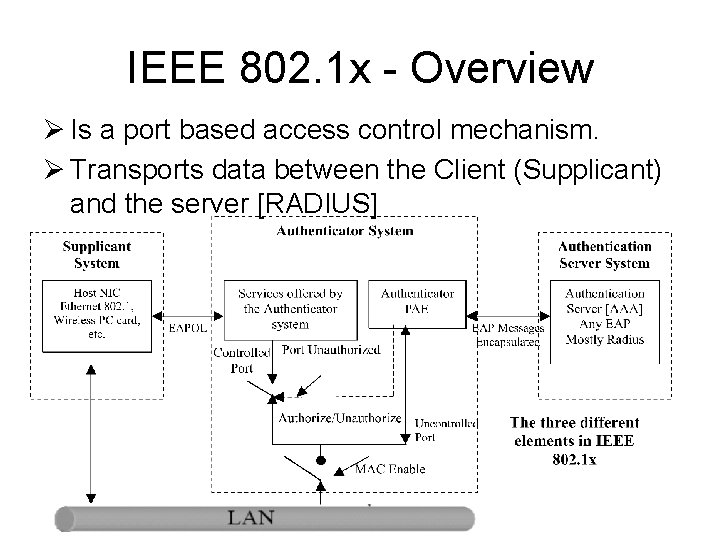
IEEE 802. 1 x - Overview Ø Is a port based access control mechanism. Ø Transports data between the Client (Supplicant) and the server [RADIUS]
What is EAP ? • Protocol for communication between Supplicant and an Authenticator • EAP messages encrypted directly over a LAN medium – EAPOL defined • Access Point [Authenticator] forwards these EAP messages encapsulated in RADIUS packets to RADIUS server • EAP allows authenticator to serve only as an carrier without needing to know the EAP authentication protocol type.
![EAP–TLS Ø Transport Layer Security [TLS] exchange of messages provides mutual authentication with both EAP–TLS Ø Transport Layer Security [TLS] exchange of messages provides mutual authentication with both](http://slidetodoc.com/presentation_image_h2/048f7630863b8cdb1eb10b441e267148/image-5.jpg)
EAP–TLS Ø Transport Layer Security [TLS] exchange of messages provides mutual authentication with both client and server validating each other via certificates. Ø Imposes substantial administrative burden • Requires a full fledged PKI infrastructure support established. • The client certificates must be managed, revoked and distributed
Need for PEAP Ø Wireless AP broadcasts all traffic hence can easily collect data if within the broadcast range • PEAP answers this by transmitting user-sensitive data in an encrypted channel - the established TLS tunnel Ø Wireless Encryption seen to be weak • Using PEAP the data within the tunnel cannot be decrypted without the TLS master secret and the key is not shared with the Access point Ø With PEAP only server side PKI infrastructure based digital certificates are used to authenticate EAP servers.
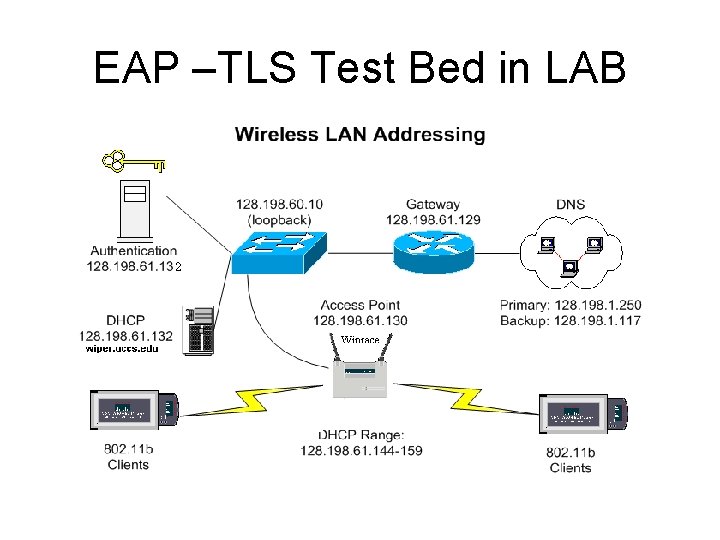
EAP –TLS Test Bed in LAB
Goal of Thesis Ø Implement a basic server-side working model of the PEAP protocol on a Linux Server based on the IETF internet draft proposal [www. ietf. org/internet-drafts/ draftjosefsson-pppext-eap-tls-eap-06. txt ] Ø Perform a comparison between the two 802. 1 x EAP standards – TTLS and PEAP. Ø Deliverables • A thesis report documenting the implementation details of the PEAP module on freeradius and xsupplicant. Should also include the configuration details of the wireless network set-up and lessons learned in this thesis project. • The source code of the PEAP module.
Thesis Plan Ø Work Done Till Date • Installing and Configuring the Client Side software – Xsupplicant [www. open 1 x. org] • Installing and configuring Radius Server - Free. Radius [www. freeradius. org] • Installing and configuring Open. SSL. [www. openssl. org] • Set-up a test bench to test EAP-TLS with the above configured software. • Running Xsupplicant, Cisco AP-1200 and Free. Radius with EAP type set to TLS. Successfully established the Authentication.
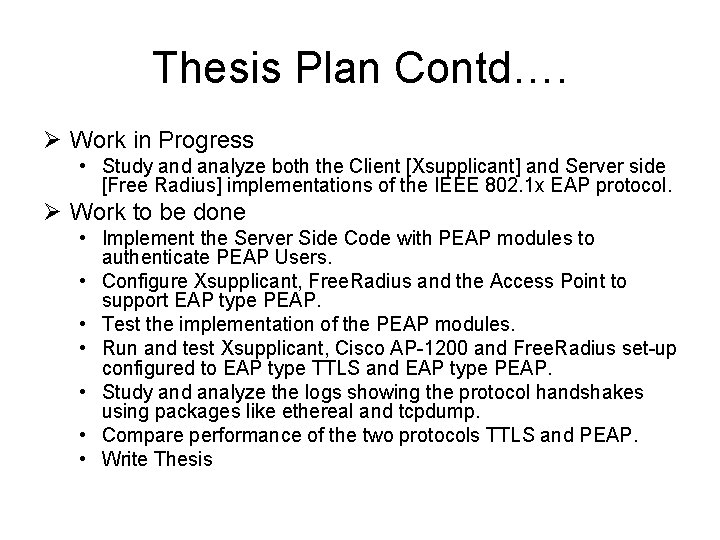
Thesis Plan Contd…. Ø Work in Progress • Study and analyze both the Client [Xsupplicant] and Server side [Free Radius] implementations of the IEEE 802. 1 x EAP protocol. Ø Work to be done • Implement the Server Side Code with PEAP modules to authenticate PEAP Users. • Configure Xsupplicant, Free. Radius and the Access Point to support EAP type PEAP. • Test the implementation of the PEAP modules. • Run and test Xsupplicant, Cisco AP-1200 and Free. Radius set-up configured to EAP type TTLS and EAP type PEAP. • Study and analyze the logs showing the protocol handshakes using packages like ethereal and tcpdump. • Compare performance of the two protocols TTLS and PEAP. • Write Thesis
![References [1] Protected EAP (IETF draft, work in progress) March 2003: http: //www. globecom. References [1] Protected EAP (IETF draft, work in progress) March 2003: http: //www. globecom.](http://slidetodoc.com/presentation_image_h2/048f7630863b8cdb1eb10b441e267148/image-11.jpg)
References [1] Protected EAP (IETF draft, work in progress) March 2003: http: //www. globecom. net/ietf/draft-josefsson-pppext-eap-tls-eap-06. html [2] IEEE 802. 1 X Port Based Network Access Control, by Paul Congdon: http: //www. ieee 802. org/1/files/public/docs 2000/P 8021 XOverview. PDF [3] The Unofficial 802. 11 Security Web Page. Security analyses of 802. 11 http: //www. drizzle. com/~aboba/IEEE/ [4] PPP Extensible Authentication Protocol http: //www. ietf. org/rfc 2284. txt [5] PPP EAP-TLS Authentication Protocol http: //www. ietf. org/rfc 2284. txt [6] PEAP – Product Documentation http: //www. microsoft. com/technet/treeview/default. asp? url=/technet/prodtechnol/wind owsserver 2003/proddocs/entserver/sag_ias_protocols_peap. asp
- Slides: 11