Imperva Breach Prevention Protect enterprise data from insider

Imperva Breach Prevention Protect enterprise data from insider threats Piotr Motłoch October 2016 © 2016 Imperva, Inc. All rights reserved. <szydera warning>
People are the WEAK LINK

Compromised Careless Malicious
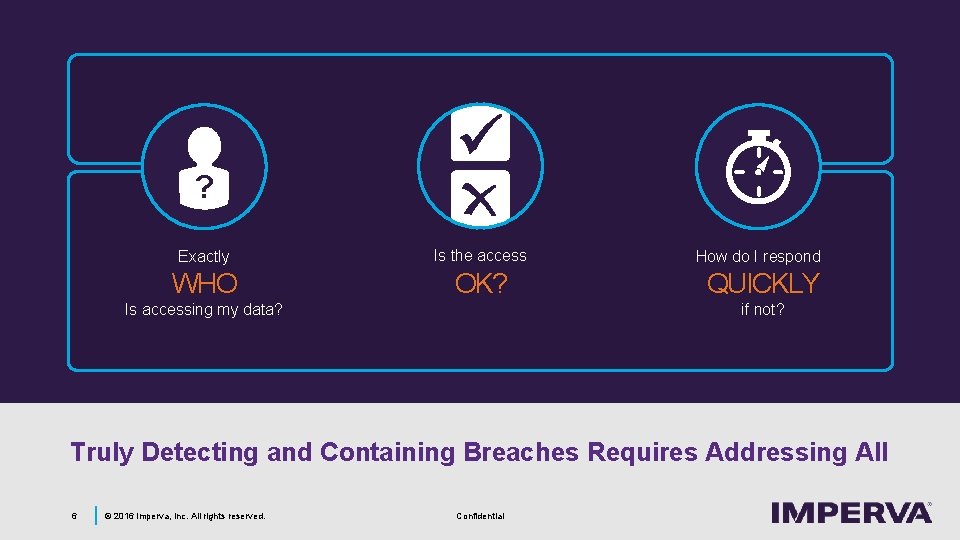
? Exactly Is the access WHO OK? How do I respond QUICKLY if not? Is accessing my data? Truly Detecting and Containing Breaches Requires Addressing All 6 © 2016 Imperva, Inc. All rights reserved. Confidential
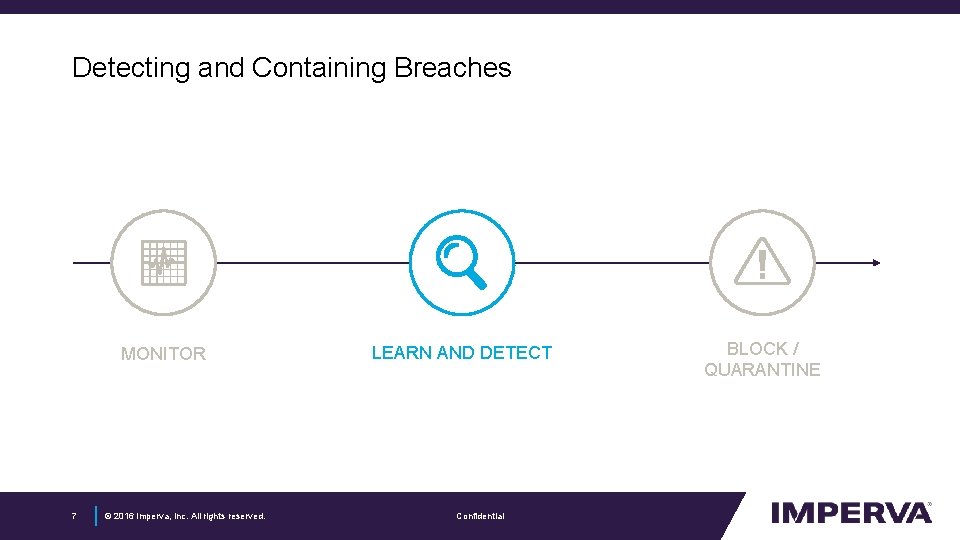
Detecting and Containing Breaches MONITOR 7 © 2016 Imperva, Inc. All rights reserved. LEARN AND DETECT Confidential BLOCK / QUARANTINE
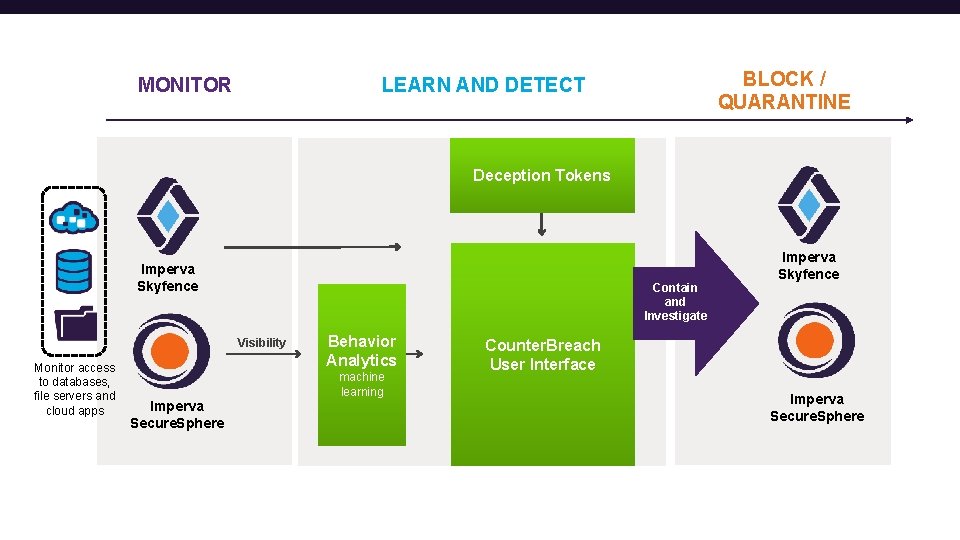
MONITOR BLOCK / QUARANTINE LEARN AND DETECT Deception Tokens Imperva Skyfence Contain and Investigate Visibility Monitor access to databases, file servers and cloud apps Behavior Analytics machine learning Imperva Secure. Sphere Imperva Skyfence Counter. Breach User Interface Imperva Secure. Sphere
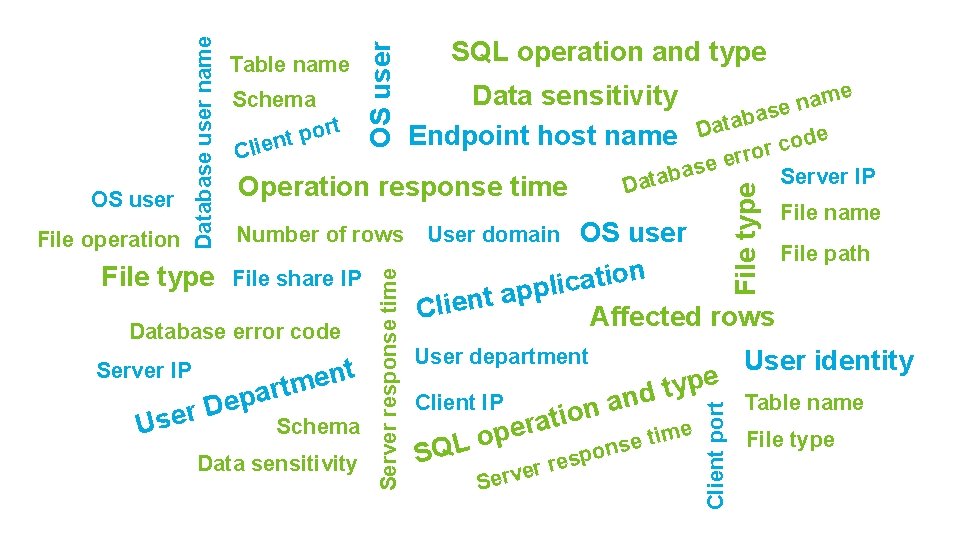
SQL operation and type File share IP Database error code Server IP t n e tm epar D r e s U Schema Data sensitivity File type Operation response time Number of rows me a n e s a b Data e d o c rror e e as b Server IP a t Da Data sensitivity Endpoint host name OS user ication User domain l p p a t Clien User department SQL e p y t nd a n o i t a r e e p o e tim Client IP ns o p s e r r e v Ser File name File path Affected rows Client port OS user Schema rt o p t Clien Server response time File operation Database user name OS user Table name User identity Table name File type
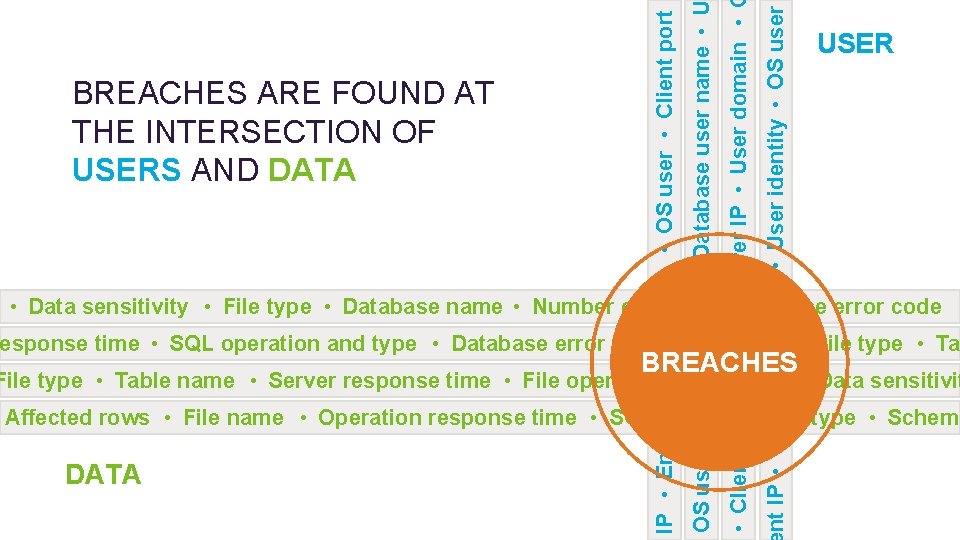
nt IP • User department • User identity • OS user • File share IP • Database user name • U Client port • Client application • Server IP • User domain • File type IP • Endpoint host name • OS user • Client port OS user Database user name Table name SQL operation and type USER BREACHES ARE FOUND AT me Data sensitivity Schema a n e s a b t ata r D o e p THE INTERSECTION OF Endpoint host name d t o n c e i l C rror e e as USERS AND DATA b Server IP a t a D Operation response time OS user File operation File type Number of rows OS user ication User domain File name File path 10 Server response time File share IP l p p a t en • Number • Data sensitivity • File type • Database of rows • Database error code Cliname Affected rows Database error code esponse time • SQL operation and type • Database error code • Schema • File type • Ta User department User identity BREACHES Server IP t n e path • Data sensitivit e response time • File operationty • p. File type • Table name • Server m t r a d p n Client IP Table name e a D n r o Affected rows • Operation response rtime and type • Schema ti • SQL operation a Us • e. File name. Schema e e p tim File type o e s L n Q o S sp e Data sensitivity r r e DATA Serv
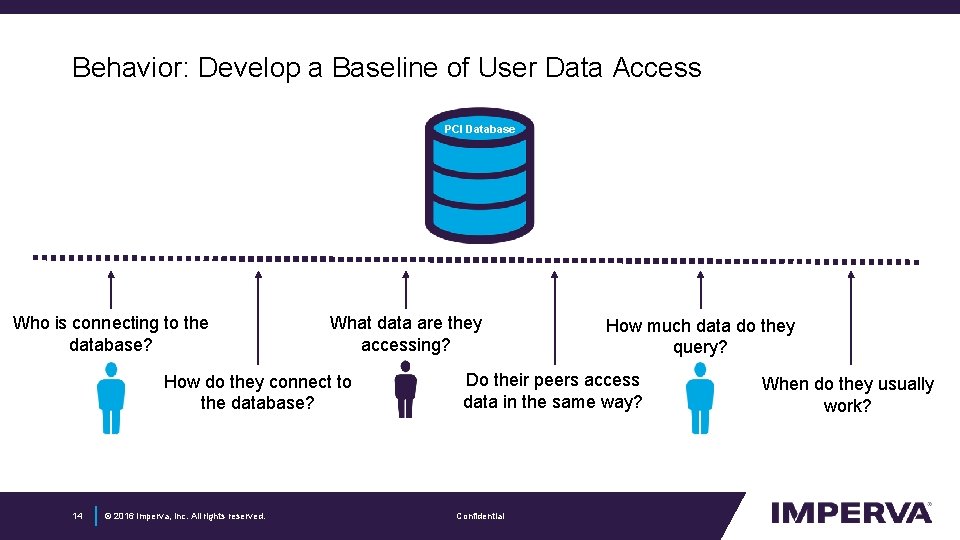
Behavior: Develop a Baseline of User Data Access PCI Database Who is connecting to the database? What data are they accessing? How do they connect to the database? 14 © 2016 Imperva, Inc. All rights reserved. How much data do they query? Do their peers access data in the same way? Confidential When do they usually work?
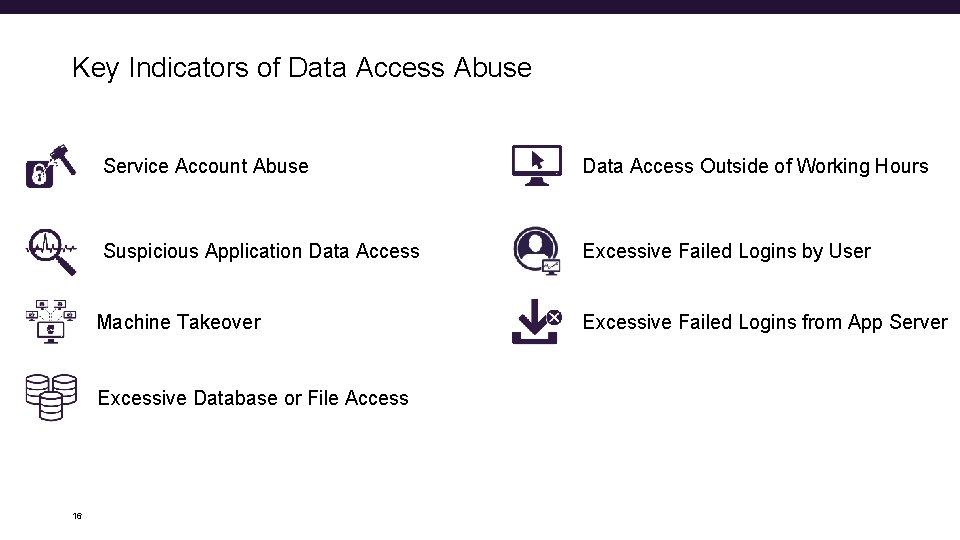
Key Indicators of Data Access Abuse Service Account Abuse Data Access Outside of Working Hours Suspicious Application Data Access Excessive Failed Logins by User Machine Takeover Excessive Database or File Access 16 Excessive Failed Logins from App Server
Findings in Customer Environments 21 © 2016 Imperva, Inc. All rights reserved. Confidential
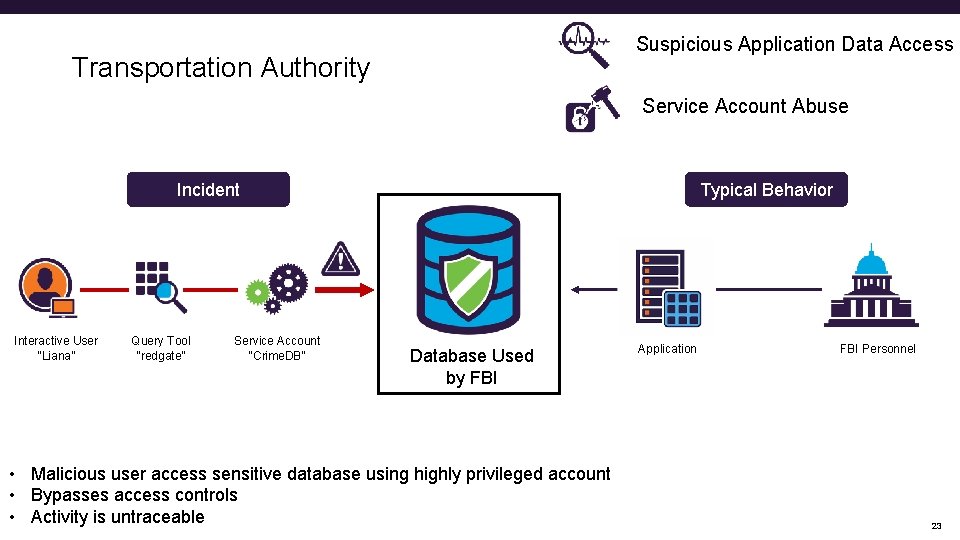
Suspicious Application Data Access Transportation Authority Service Account Abuse Incident Interactive User “Liana” Query Tool “redgate” Service Account “Crime. DB” Typical Behavior Database Used by FBI • Malicious user access sensitive database using highly privileged account • Bypasses access controls • Activity is untraceable Application FBI Personnel 23
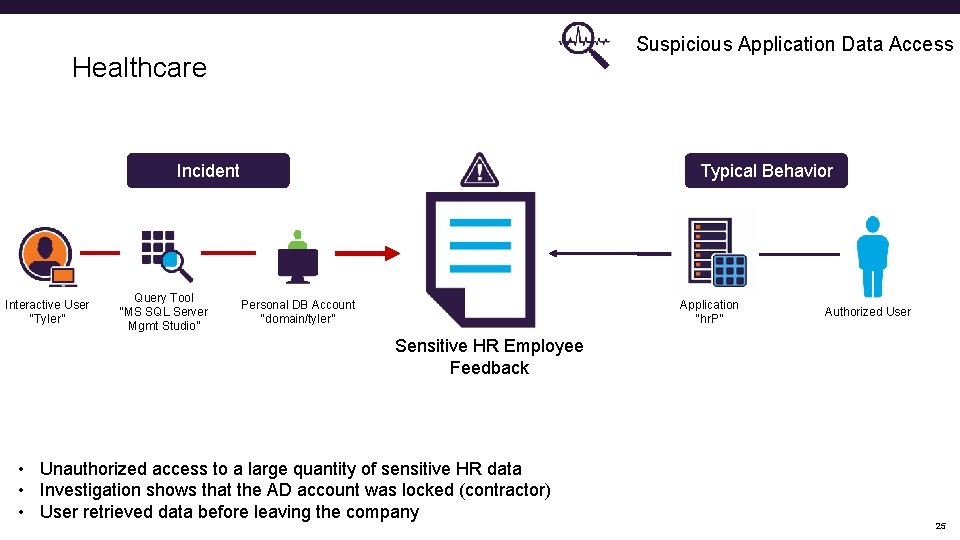
Suspicious Application Data Access Healthcare Incident Interactive User “Tyler” Query Tool “MS SQL Server Mgmt Studio” Typical Behavior Personal DB Account “domain/tyler” Application “hr. P” Authorized User Sensitive HR Employee Feedback • Unauthorized access to a large quantity of sensitive HR data • Investigation shows that the AD account was locked (contractor) • User retrieved data before leaving the company 25
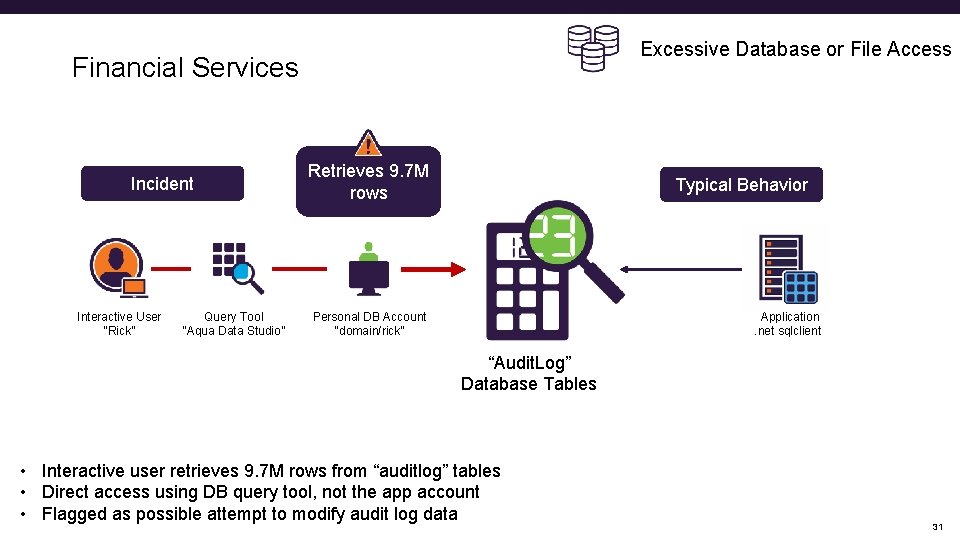
Excessive Database or File Access Financial Services Incident Interactive User “Rick” Query Tool “Aqua Data Studio” Retrieves 9. 7 M rows Typical Behavior Personal DB Account “domain/rick” Application. net sqlclient “Audit. Log” Database Tables • Interactive user retrieves 9. 7 M rows from “auditlog” tables • Direct access using DB query tool, not the app account • Flagged as possible attempt to modify audit log data 31
Counter. Breach Deception Tokens 32 © 2016 Imperva, Inc. All rights reserved. Confidential
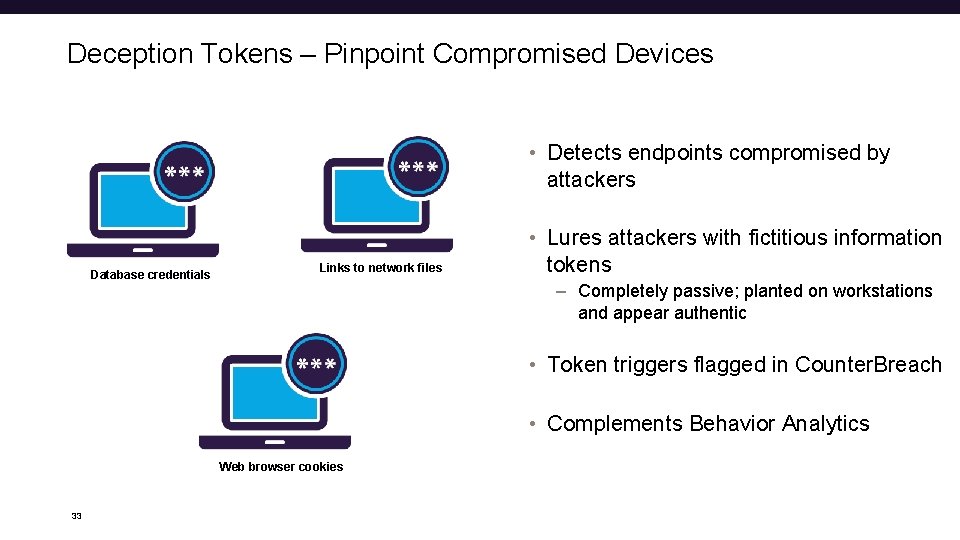
Deception Tokens – Pinpoint Compromised Devices • Detects endpoints compromised by attackers Database credentials Links to network files • Lures attackers with fictitious information tokens – Completely passive; planted on workstations and appear authentic • Token triggers flagged in Counter. Breach • Complements Behavior Analytics Web browser cookies 33
Product Tour Counter. Breach 35 © 2016 Imperva, Inc. All rights reserved. Confidential
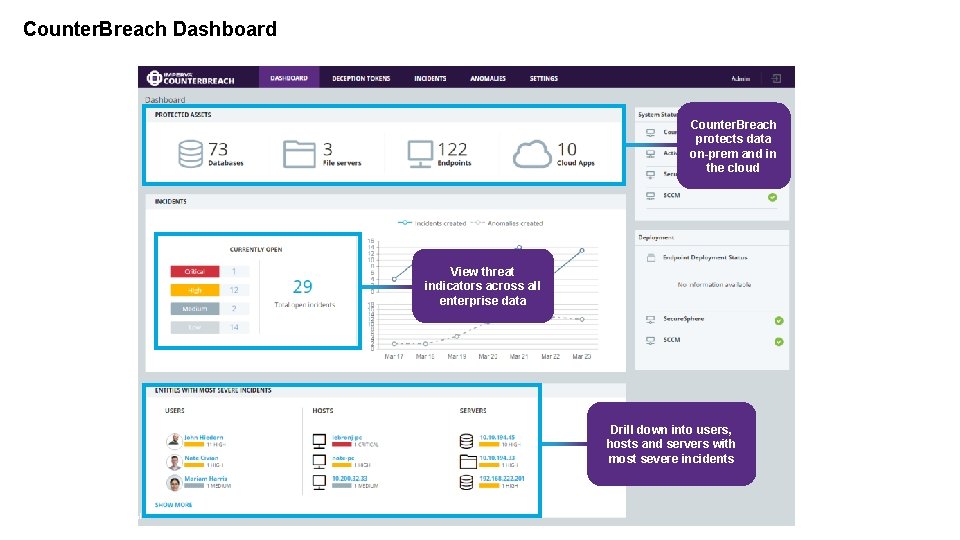
Counter. Breach Dashboard Counter. Breach protects data on-prem and in the cloud ` ` View threat indicators across all enterprise data Drill down into users, hosts and servers with most severe incidents 36 Confidential
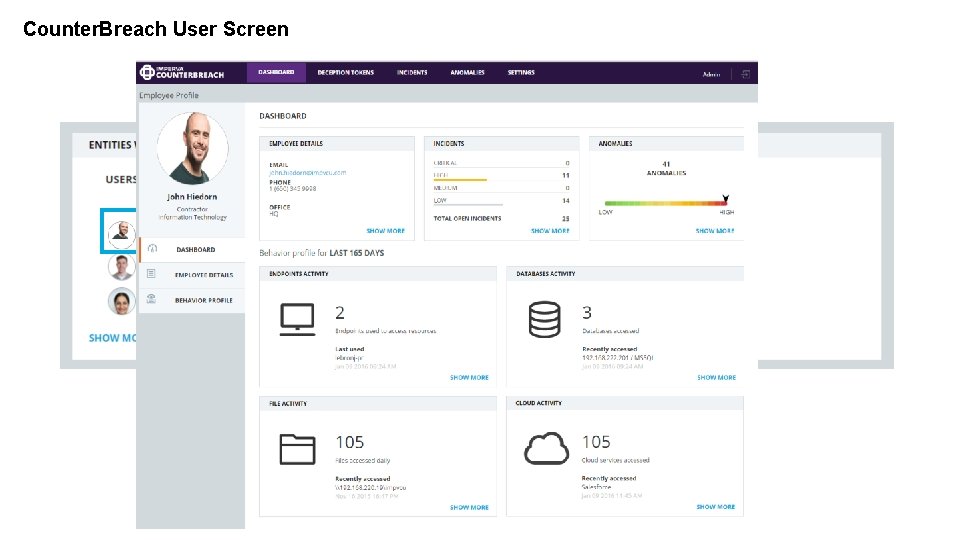
Counter. Breach User Screen Click a user to see their behavior across data assets ` 37 Confidential
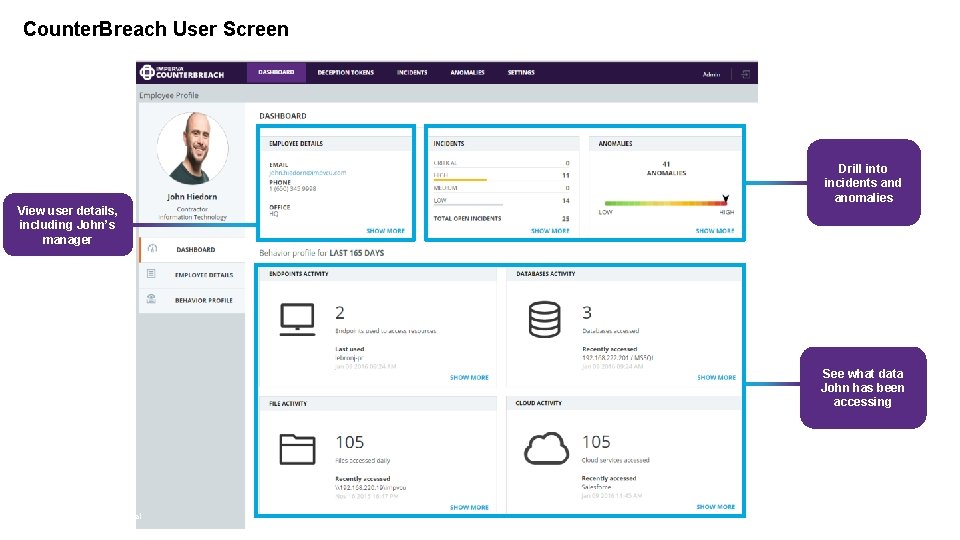
Counter. Breach User Screen ` ` View user details, including John’s manager ` 38 Confidential Drill into incidents and anomalies See what data John has been accessing
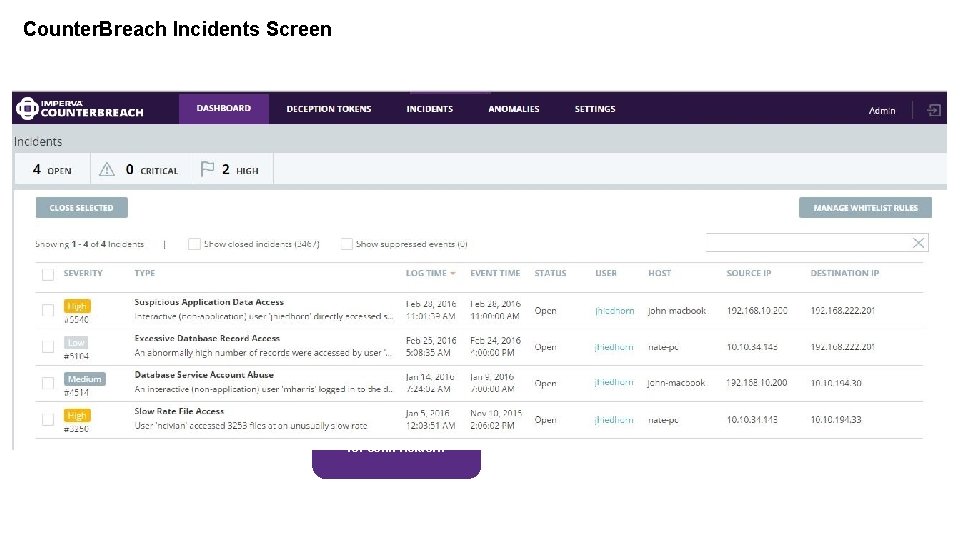
Counter. Breach Incidents Screen ` View all open incidents for John Heidorn
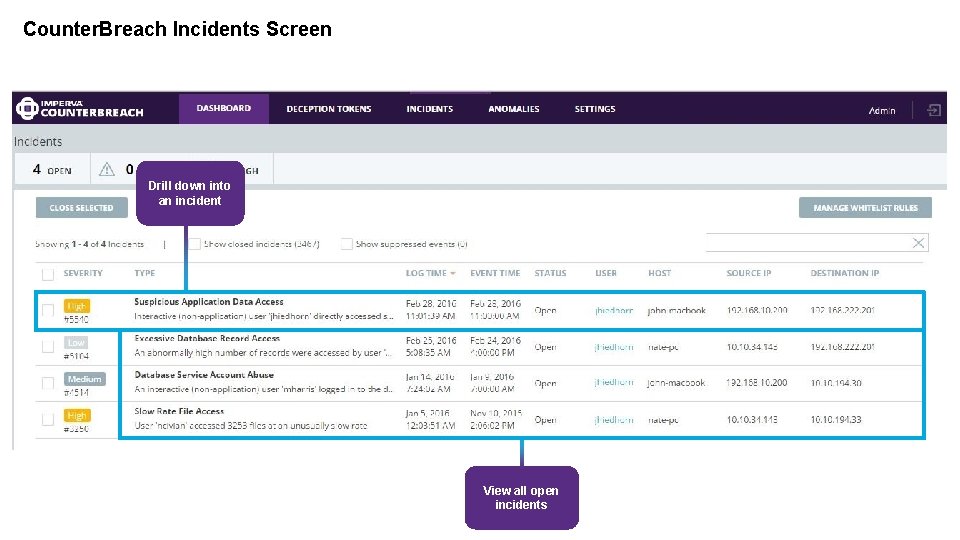
Counter. Breach Incidents Screen Drill down into an incident ` ` View all open incidents
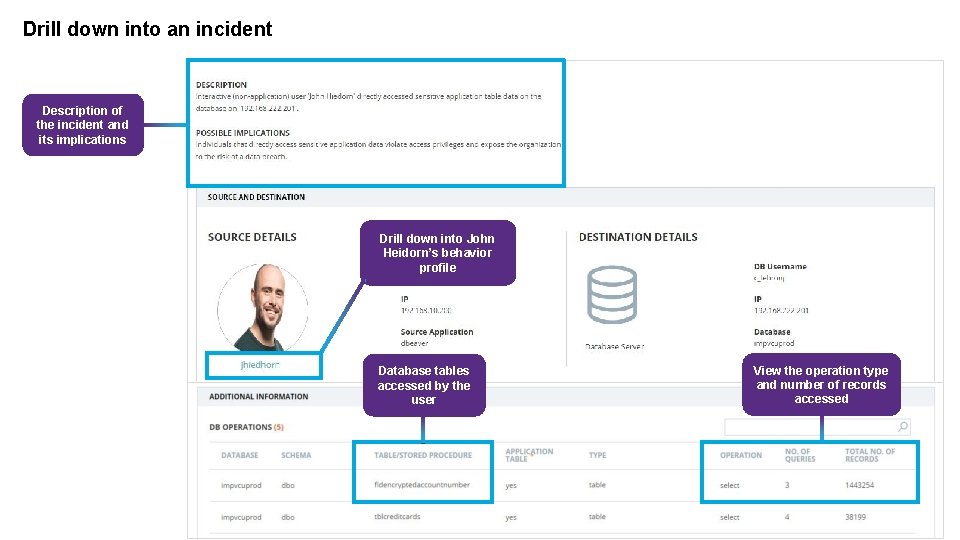
Drill down into an incident Description of the incident and its implications ` Drill down into John Heidorn’s behavior profile ` Database tables accessed by the user ` View the operation type and number of records accessed `
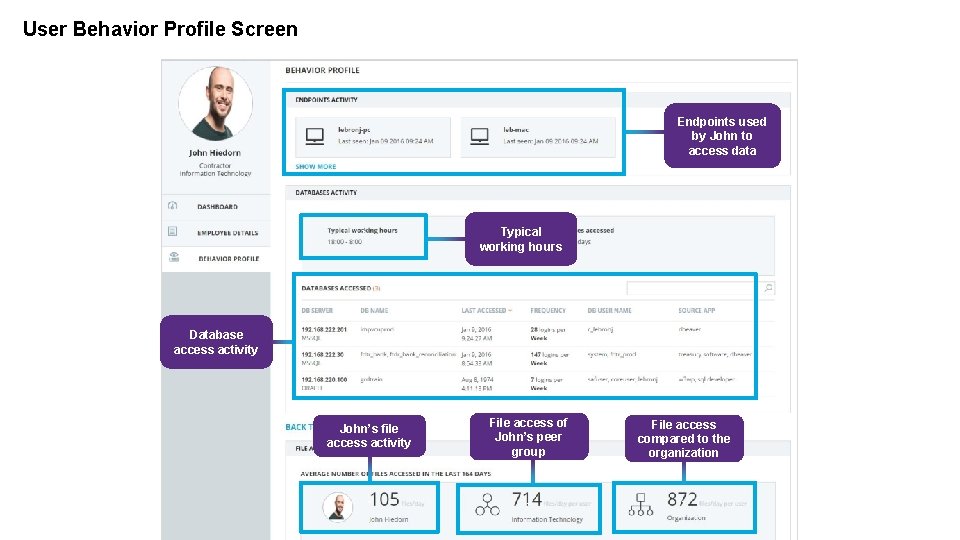
User Behavior Profile Screen Endpoints used by John to access data ` Typical working hours ` ` Database access activity John’s file access activity File access of John’s peer group File access compared to the organization ` ` `
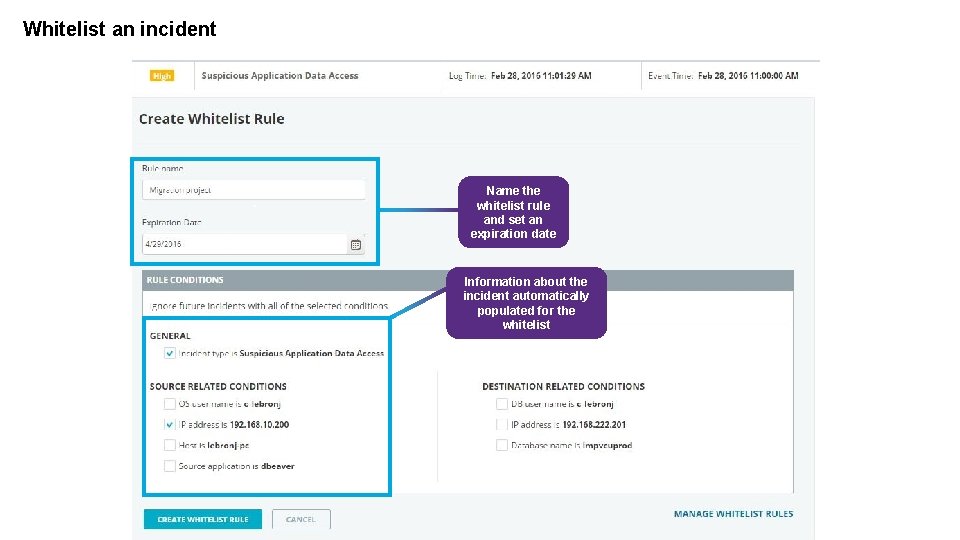
Whitelist an incident Name the whitelist rule and set an expiration date ` Information about the incident automatically populated for the whitelist `

- Slides: 26