Image Sharing By Chinese Remainder Theorem Group S
Image Sharing By Chinese Remainder Theorem Group S: S 1, S 2, S 3 Institute of Information Systems & Applications National Tsing Hua University Hsinchu 30013, Taiwan E-mail: 104062613@m 104. nthu. edu. tw
Abstract (摘要) Due to the rapid growth of information acquisition in the era of the Internet of Things (Io. T) and Cloud Computing, the concern about the security of private information raises a lot of interests. This proposal aims to investigate image sharing based on the concept of (k, n)-threshold strategy according to the Chinese remainder theorem (CRT). A secret image is distributed into n noise-like shadow images preserved by n participants instead of a single carrier. Collecting at least k out of n shadows can reveal the secret image, but fewer than k shadow images could not. We’ll discuss existing CRT-based sharing methods, proposes a simple CRT-based method and illustrates (3, 5)-threshold results for RGB color images.
Motivation and Problem Statement • To avoid the information is carried by only a single individual • Secret data are partitioned into n shadows which are distributed to n participants • By collecting at least k out of n shadows, we can completely recover the original data (information) • A (k, n)-threshold technique based on Chinese Remainder Theorem is adopted and implemented.
Background Review • The secret value S is used to generate n shadows • Any k or more shadows can recover the secret value S • Fewer than k shadows cannot reveal the secret value S • Commonly used (k, n)-threshold schemes for sharing • (1) Shamir [Sham 1979] • (2) Blakley [Blak 1979] • (3) Asmuth and Bloom [Asmu 1983]
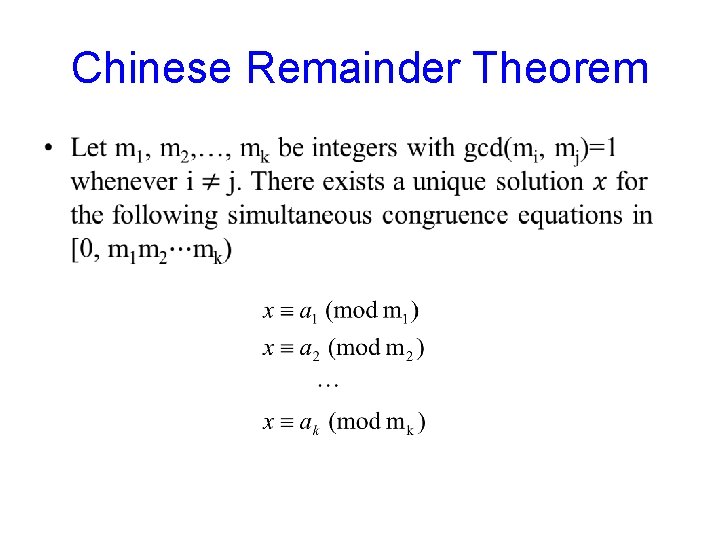
Chinese Remainder Theorem •
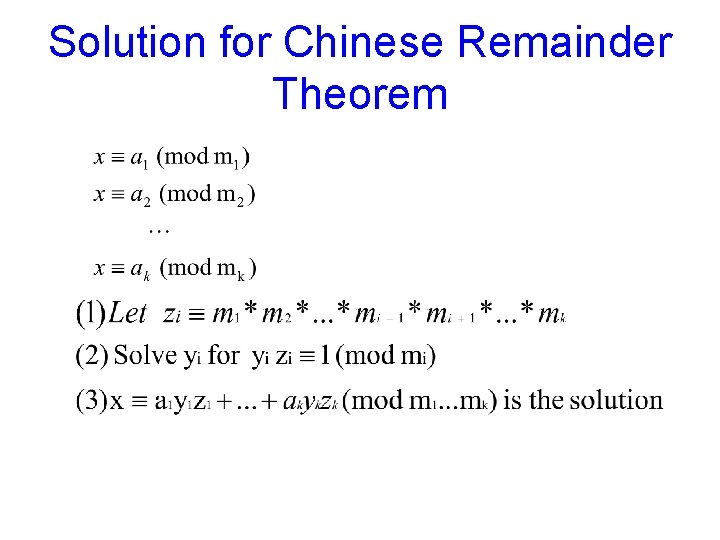
Solution for Chinese Remainder Theorem
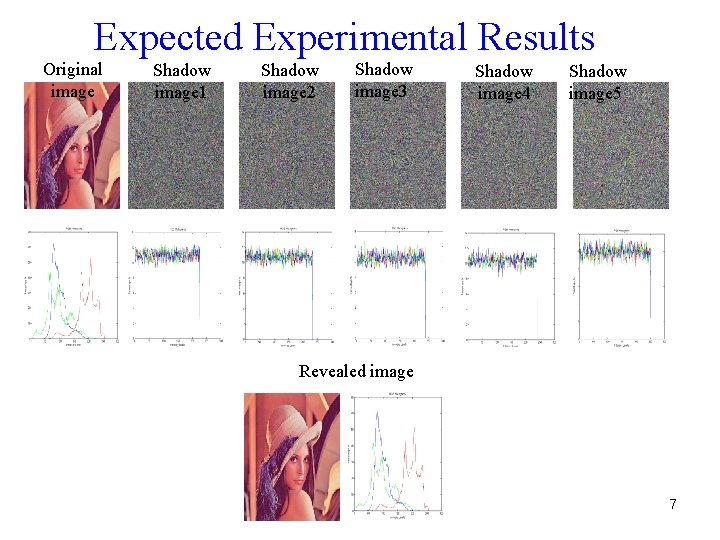
Expected Experimental Results Original image Shadow image 1 Shadow image 2 Shadow image 3 Shadow image 4 Shadow image 5 Revealed image 7
![Major References [1] C. C. Thien and J. C. Lin, ”Secret image sharing, ” Major References [1] C. C. Thien and J. C. Lin, ”Secret image sharing, ”](http://slidetodoc.com/presentation_image/7fd3be39c76f9b2bdd78c89619fed7e7/image-8.jpg)
Major References [1] C. C. Thien and J. C. Lin, ”Secret image sharing, ” Compuers & Graphics, vol. 26, no. 1, 765 -771, 2002. [2] M. H. Tsai and C. C. Chen, ”A Study on Secret Image Sharing, ” The Sixth International Workshop on Image Media Quality and Its Applications, 135 -139, Tokyo, Japan, September 12 -13, 2013. [3] M. Ulutas, V. V. Nabiyev, and G. Ulutas, ”A New Secret Sharing Technique Based on Asmuth Bloom’s Scheme, ” IEEE International Conference on Application of Information and Communication Technologies, 1 -5, Baku, Oct. 14 -16, 2009. [4]https: //en. wikipedia. org/wiki/Secret_sharing_using_the_Chinese_rem ainder_theorem
- Slides: 8