IEEE 802 11 i Dohwan Kim Table of
IEEE 802. 11 i Dohwan Kim
Table of contents • WEP • WPA 1 • WPA 2 • Conclusion
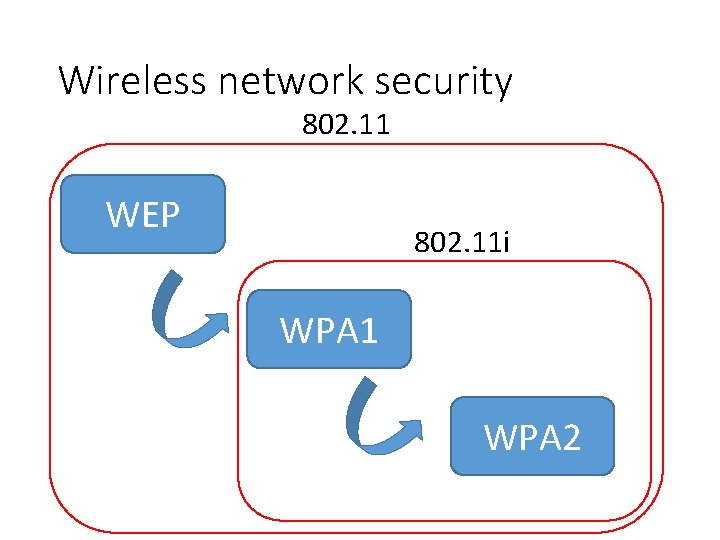
Wireless network security 802. 11 WEP 802. 11 i WPA 1 WPA 2
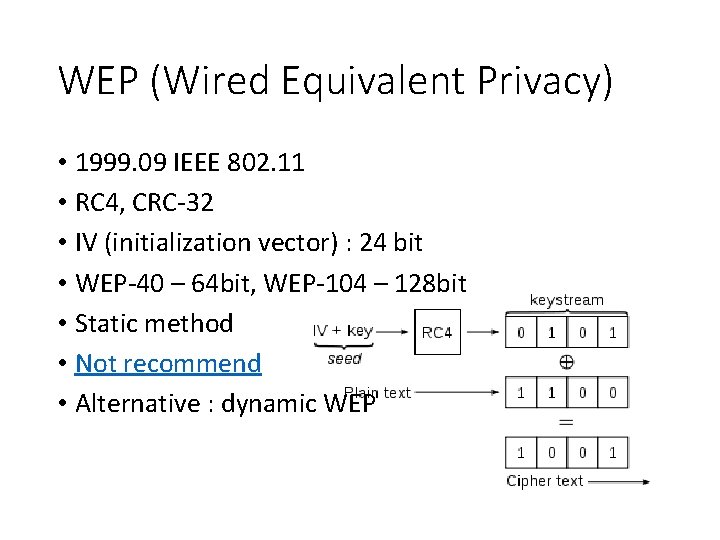
WEP (Wired Equivalent Privacy) • 1999. 09 IEEE 802. 11 • RC 4, CRC-32 • IV (initialization vector) : 24 bit • WEP-40 – 64 bit, WEP-104 – 128 bit • Static method • Not recommend • Alternative : dynamic WEP
WPA (Wi-Fi Protected Access) • Enterprise mode • Authentication : IEEE 802. 1 x/EAP • Encryption : TKIP/MIC • Personal mode • Authentication : PSK • Encryption : TKIP/MIC
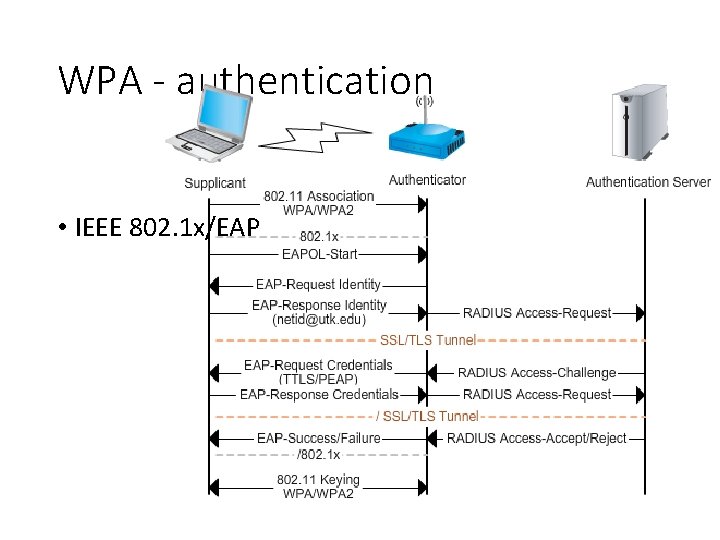
WPA - authentication • IEEE 802. 1 x/EAP
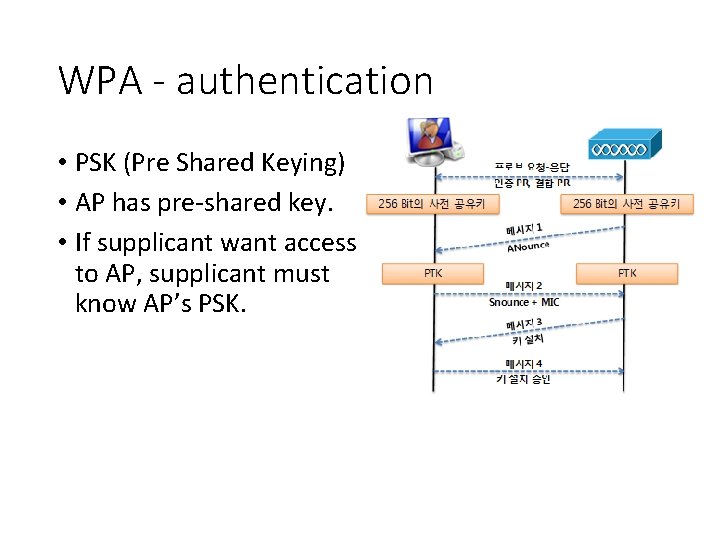
WPA - authentication • PSK (Pre Shared Keying) • AP has pre-shared key. • If supplicant want access to AP, supplicant must know AP’s PSK.
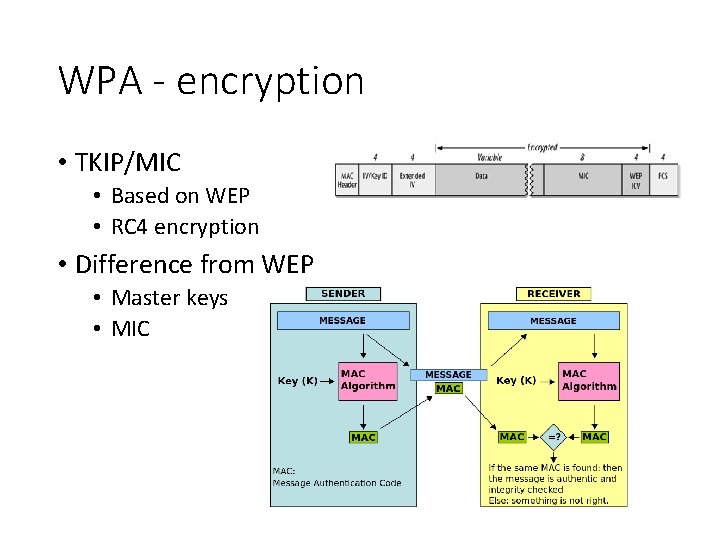
WPA - encryption • TKIP/MIC • Based on WEP • RC 4 encryption • Difference from WEP • Master keys • MIC
WPA 2 • Enterprise mode • Authentication : IEEE 802. 1 x/EAP • Encryption : AES-CCMP • Personal mode • Authentication : PSK • Encryption : AES-CCMP
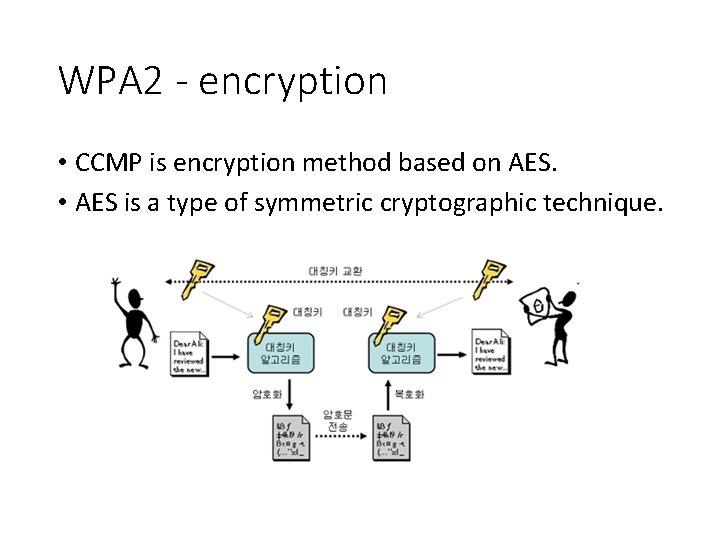
WPA 2 - encryption • CCMP is encryption method based on AES. • AES is a type of symmetric cryptographic technique.
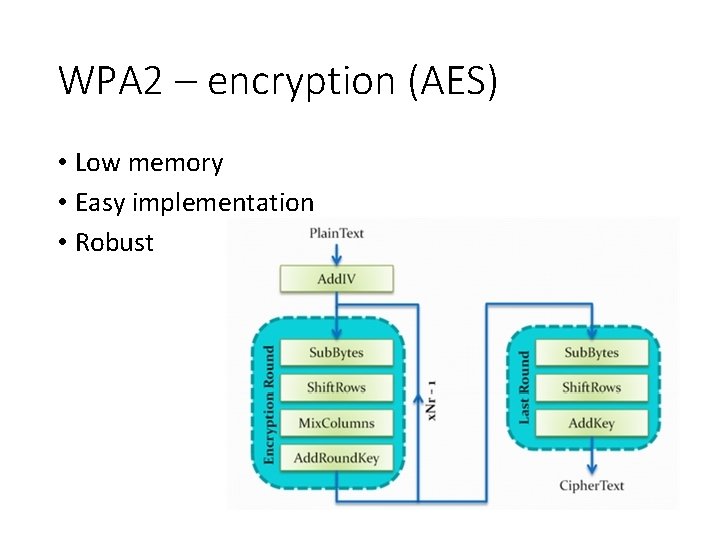
WPA 2 – encryption (AES) • Low memory • Easy implementation • Robust
Conclusion • WEP and WPA 1 (TKIP) is not recommended. • Drawback of AES is researched, so beyond AES receives attention.
- Slides: 12