Identitys Role in your Zero Trust strategy The


- Slides: 10

Identity’s Role in your Zero Trust strategy
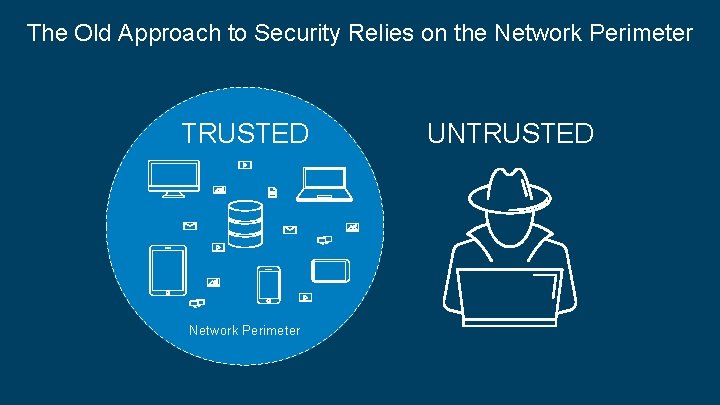
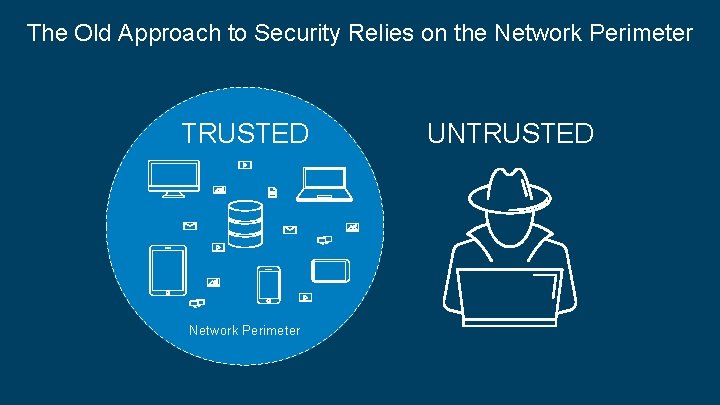
The Old Approach to Security Relies on the Network Perimeter TRUSTED Network Perimeter © Okta and/or its affiliates. All rights reserved. Okta Confidential 2 UNTRUSTED
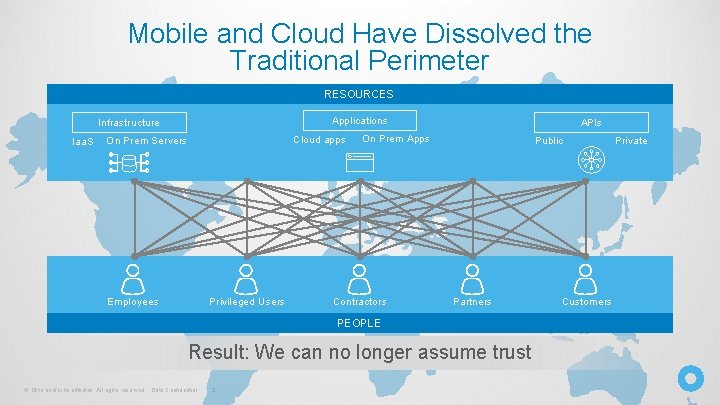
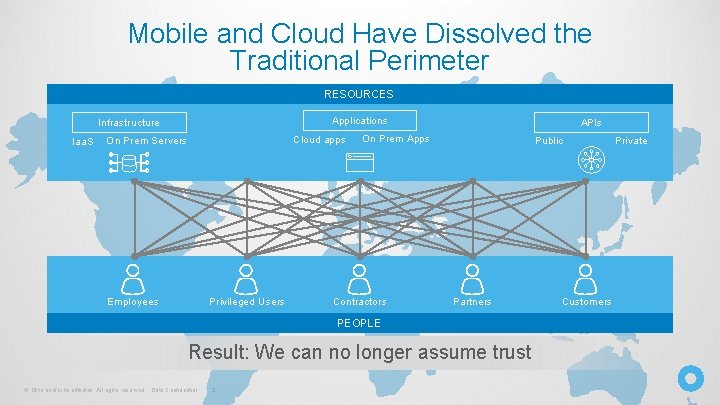
Mobile and Cloud Have Dissolved the Traditional Perimeter RESOURCES Applications Infrastructure Iaa. S Cloud apps On Prem Servers Employees Privileged Users APIs On Prem Apps Contractors Public Partners PEOPLE Result: We can no longer assume trust © Okta and/or its affiliates. All rights reserved. Okta Confidential 3 Customers Private
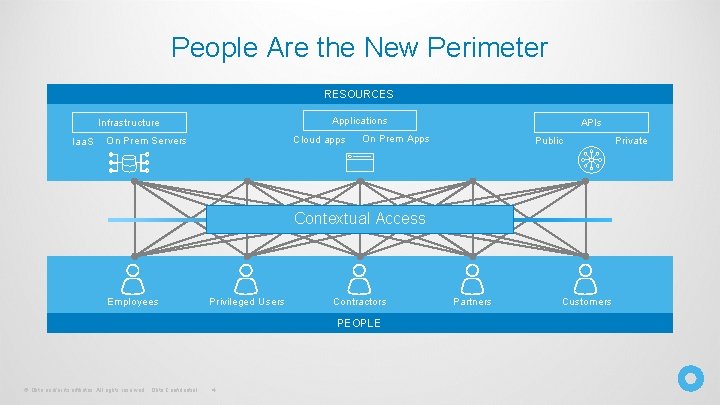
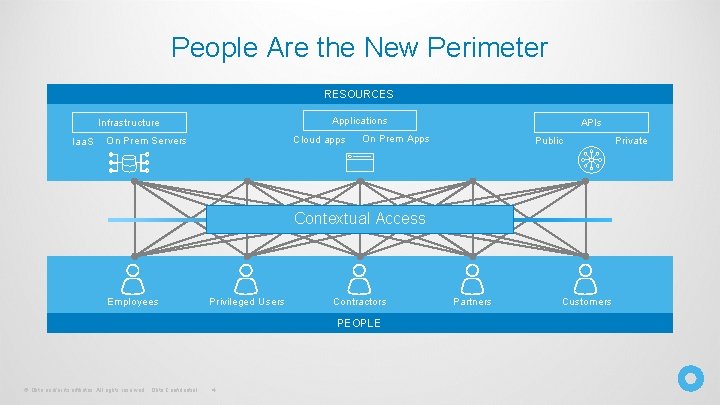
People Are the New Perimeter RESOURCES Applications Infrastructure Iaa. S Cloud apps On Prem Servers APIs On Prem Apps Public Contextual Access Employees Privileged Users Contractors PEOPLE © Okta and/or its affiliates. All rights reserved. Okta Confidential 4 Partners Customers Private
When People are the Perimeter, Identity Becomes the Foundation of a Zero Trust Strategy © Okta and/or its affiliates. All rights reserved. Okta Confidential 5
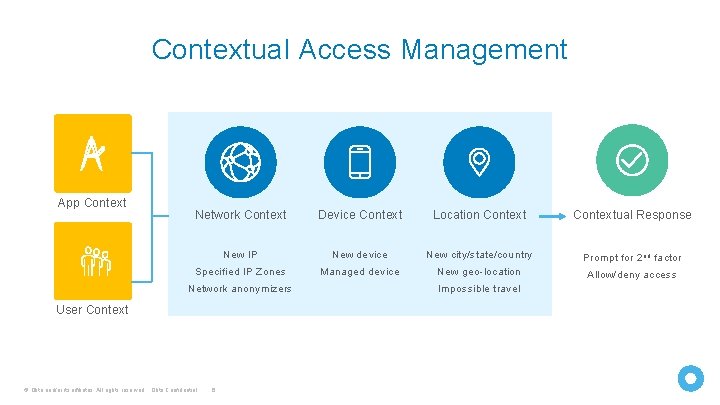
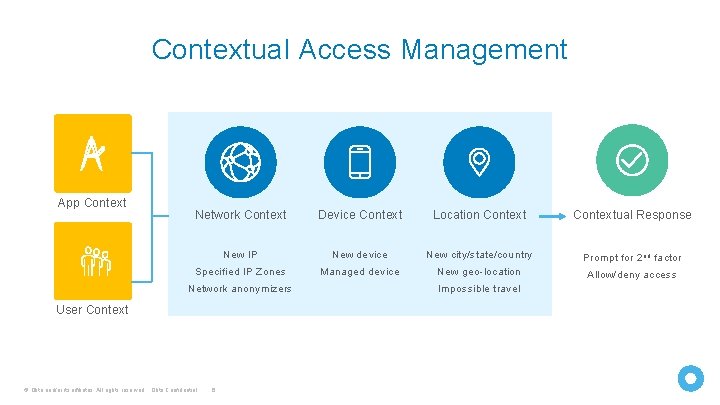
Contextual Access Management App Context Network Context Device Context Location Contextual Response New IP New device New city/state/country Prompt for 2 nd factor Specified IP Zones Managed device New geo-location Allow/deny access Network anonymizers User Context © Okta and/or its affiliates. All rights reserved. Okta Confidential 6 Impossible travel
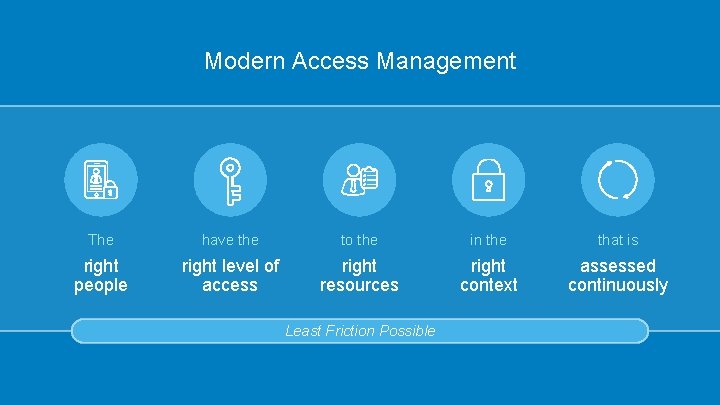
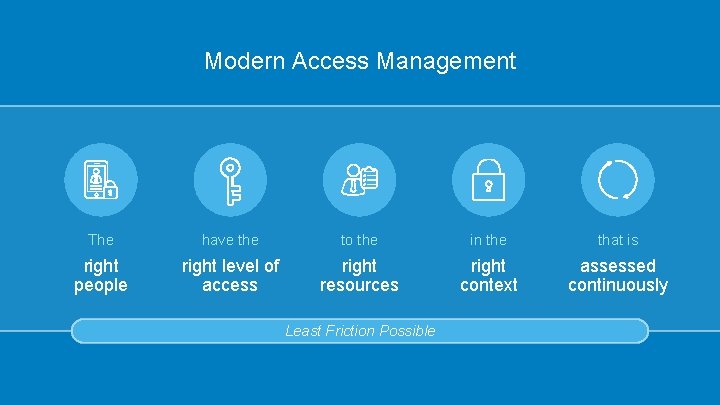
Modern Access Management The have the to the in the that is right people right level of access right resources right context assessed continuously Least Friction Possible
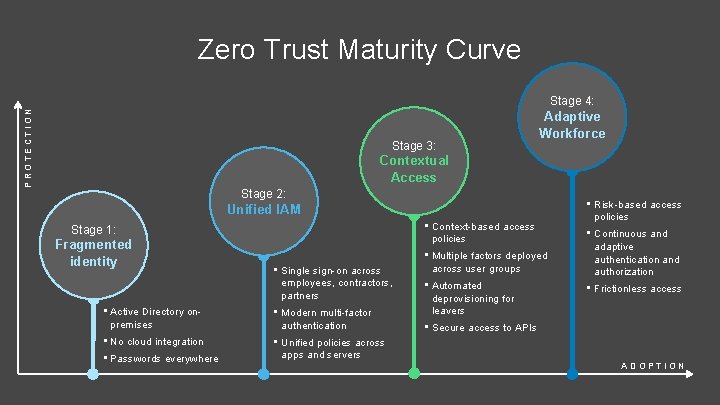
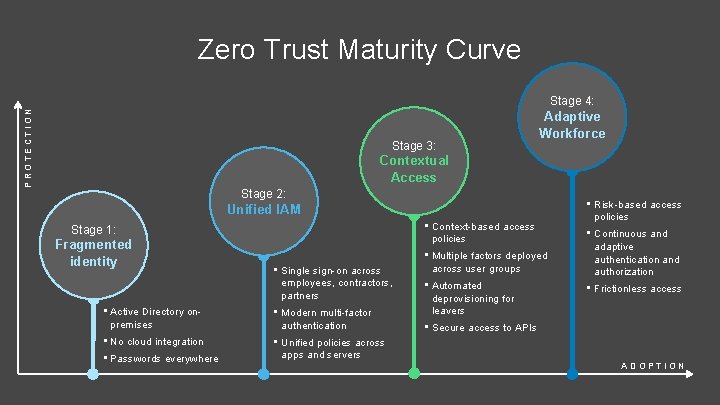
Zero Trust Maturity Curve PROTECTION Stage 4: Stage 3: Adaptive Workforce Contextual Access Stage 2: Unified IAM • Context-based access policies Stage 1: Fragmented identity • Single sign-on across employees, contractors, partners • Active Directory onpremises • Modern multi-factor authentication • No cloud integration • Unified policies across apps and servers • Passwords everywhere • Multiple factors deployed across user groups • Automated deprovisioning for leavers • Risk-based access policies • Continuous and adaptive authentication and authorization • Frictionless access • Secure access to APIs ADOPTION

There’s no silver bullet for Zero Trust © Okta and/or its affiliates. All rights reserved. Okta Confidential 9 The Zero Trust journey starts with Identity Okta is the modern Zero Trust Platform
“Okta was the foundation that could help us mature to a zero trust model. ” Fox is the There’s no-Melody silver Hildebrandt, The. Global Zero. CISO, Trust 21 st Century Okta bullet for Zero journey starts modern Zero Trust with Identity Trust Platform © Okta and/or its affiliates. All rights reserved. Okta Confidential 10