Identity Management a Key eBusiness Enabler Marco Casassa
Identity Management: a Key e-Business Enabler Marco Casassa Mont Pete Bramhall Mickey Gittler Joe Pato Owen Rees Trust, Security and Privacy Hewlett-Packard Laboratories Bristol, UK SSGRR 2002 s

Outline • Background: Identity & Identity Management • Current and Future Trends • Important Issues • Our Research on Identity Management • Conclusions
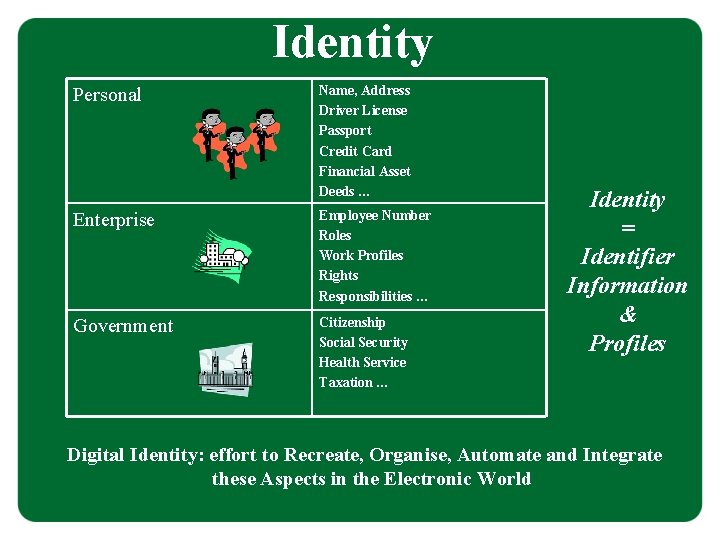
Identity Personal Name, Address Driver License Passport Credit Card Financial Asset Deeds … Enterprise Employee Number Roles Work Profiles Rights Responsibilities … Government Citizenship Social Security Health Service Taxation … Identity = Identifier Information & Profiles Digital Identity: effort to Recreate, Organise, Automate and Integrate these Aspects in the Electronic World
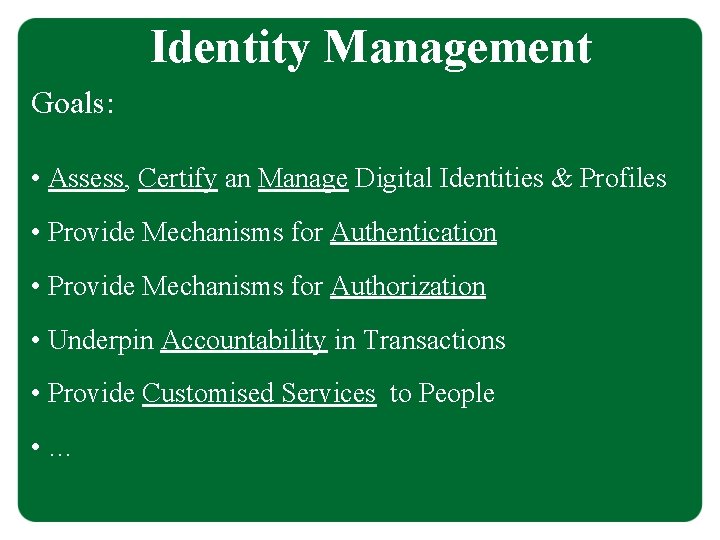
Identity Management Goals: • Assess, Certify an Manage Digital Identities & Profiles • Provide Mechanisms for Authentication • Provide Mechanisms for Authorization • Underpin Accountability in Transactions • Provide Customised Services to People • …
Identity Management Relevance in Multiple Contexts: • Personal • Social • E-Commerce • Enterprise, B 2 B • Government • …
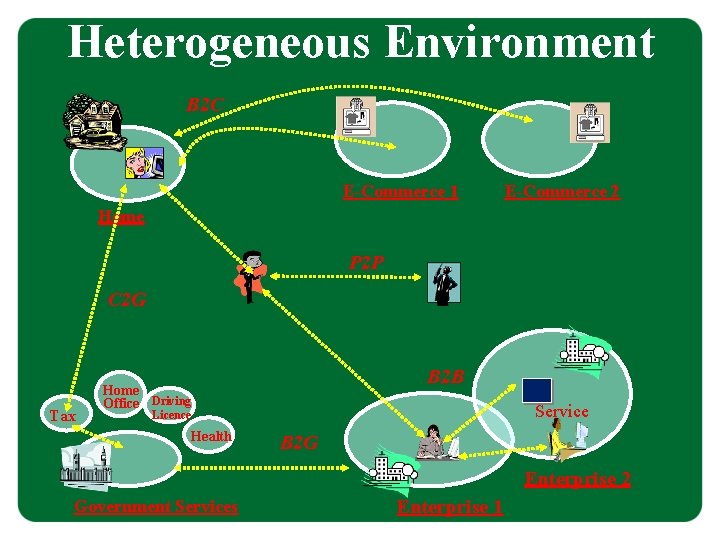
Heterogeneous Environment B 2 C E-Commerce 1 E-Commerce 2 Home P 2 P C 2 G Tax B 2 B Home Office Driving Service Licence Health B 2 G Enterprise 2 Government Services Enterprise 1
Identity Management Current Trends 1. Consumer and E-Commerce Space 2. Enterprise and B 2 B Space 3. Government Space
Current Trends Consumer and E-Commerce Space Federated Identity Management: • Simplification of Authentication and Profile Management Processes for Consumers • Authentication and Single-Sign-On across multiple e-Commerce Sites • Mediations by Identity Providers (Trusted Third Parties) • Major Players: - Microsoft (Passport, . My. Services), - Liberty Alliance Project (Consortium) [HP is a Core Member of Liberty Alliance]
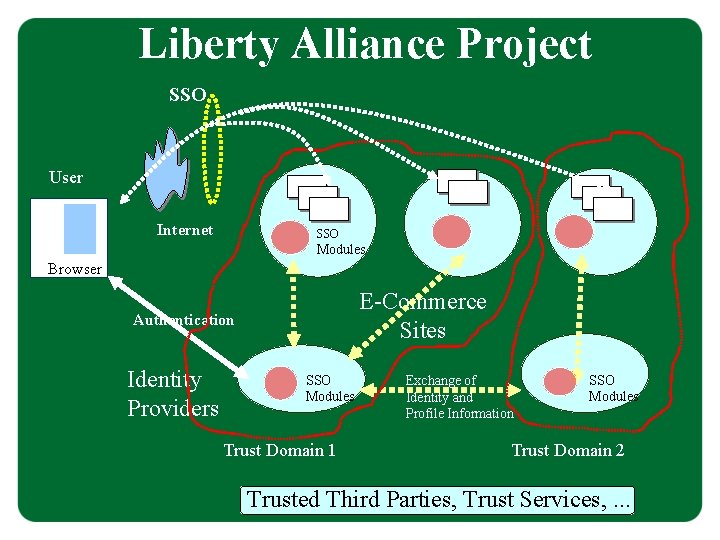
Liberty Alliance Project SSO User Internet SSO Modules Browser E-Commerce Sites Authentication Identity Providers SSO Modules Trust Domain 1 Exchange of Identity and Profile Information SSO Modules Trust Domain 2 Trusted Third Parties, Trust Services, . . .
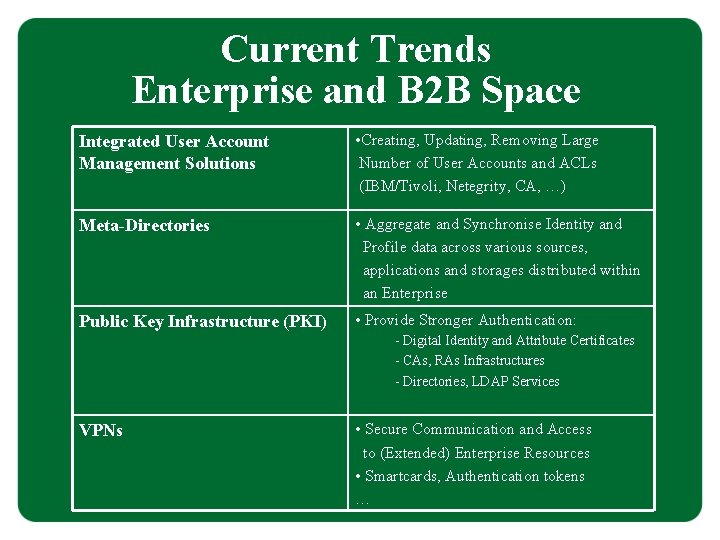
Current Trends Enterprise and B 2 B Space Integrated User Account Management Solutions • Creating, Updating, Removing Large Number of User Accounts and ACLs (IBM/Tivoli, Netegrity, CA, …) Meta-Directories • Aggregate and Synchronise Identity and Profile data across various sources, applications and storages distributed within an Enterprise Public Key Infrastructure (PKI) • Provide Stronger Authentication: - Digital Identity and Attribute Certificates - CAs, RAs Infrastructures - Directories, LDAP Services VPNs • Secure Communication and Access to (Extended) Enterprise Resources • Smartcards, Authentication tokens …
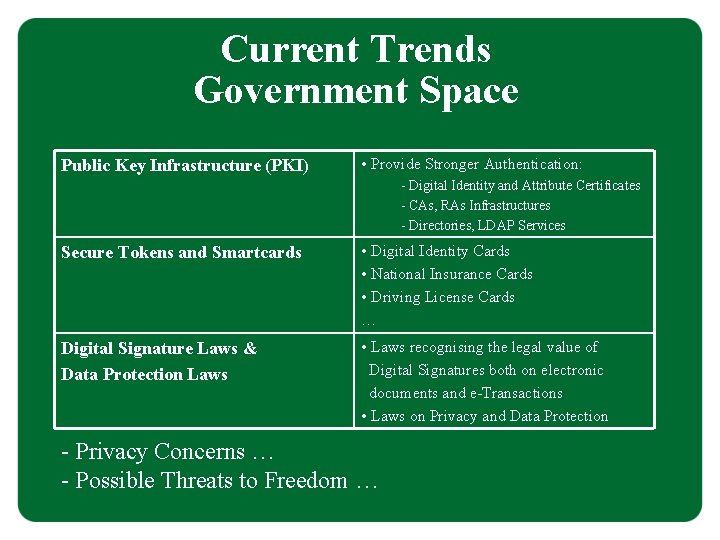
Current Trends Government Space Public Key Infrastructure (PKI) • Provide Stronger Authentication: - Digital Identity and Attribute Certificates - CAs, RAs Infrastructures - Directories, LDAP Services Secure Tokens and Smartcards • Digital Identity Cards • National Insurance Cards • Driving License Cards … Digital Signature Laws & Data Protection Laws • Laws recognising the legal value of Digital Signatures both on electronic documents and e-Transactions • Laws on Privacy and Data Protection - Privacy Concerns … - Possible Threats to Freedom …
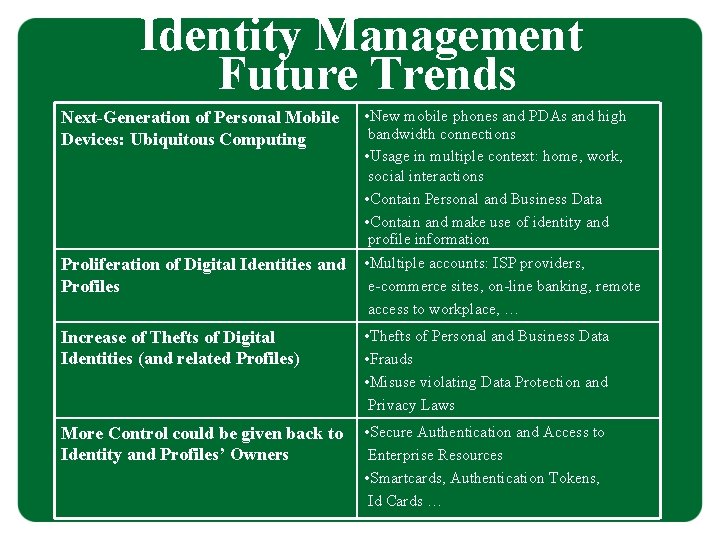
Identity Management Future Trends Next-Generation of Personal Mobile Devices: Ubiquitous Computing • New mobile phones and PDAs and high bandwidth connections • Usage in multiple context: home, work, social interactions • Contain Personal and Business Data • Contain and make use of identity and profile information Proliferation of Digital Identities and Profiles • Multiple accounts: ISP providers, e-commerce sites, on-line banking, remote access to workplace, … Increase of Thefts of Digital Identities (and related Profiles) • Thefts of Personal and Business Data • Frauds • Misuse violating Data Protection and Privacy Laws More Control could be given back to Identity and Profiles’ Owners • Secure Authentication and Access to Enterprise Resources • Smartcards, Authentication Tokens, Id Cards …
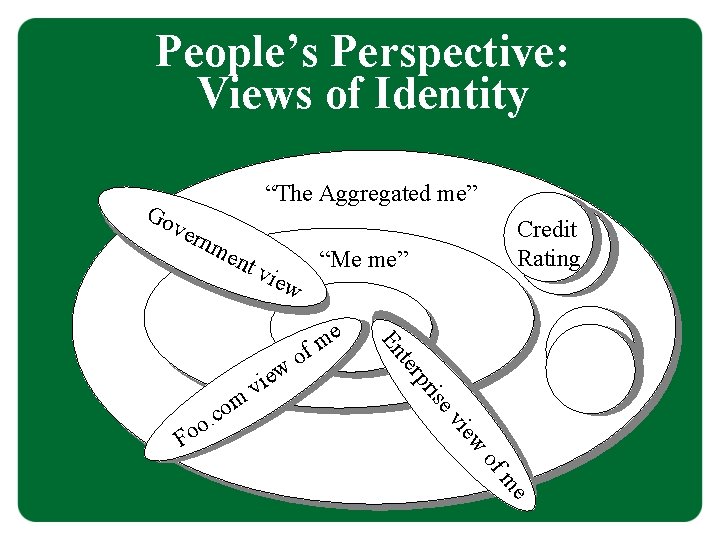
People’s Perspective: Views of Identity Go “The Aggregated me” ver nm ent “Me me” vie w o ise pr v iew e m f ter En w vie . c o Fo om Credit Rating of me
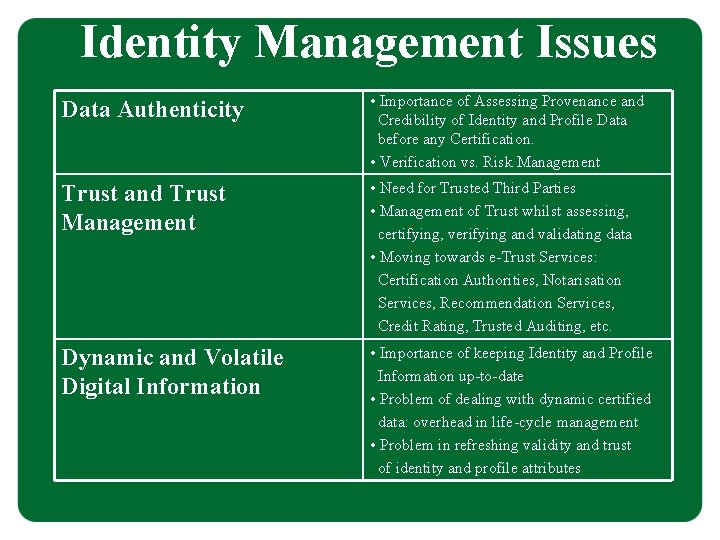
Identity Management Issues Data Authenticity • Importance of Assessing Provenance and Credibility of Identity and Profile Data before any Certification. • Verification vs. Risk Management Trust and Trust Management • Need for Trusted Third Parties • Management of Trust whilst assessing, certifying, verifying and validating data • Moving towards e-Trust Services: Certification Authorities, Notarisation Services, Recommendation Services, Credit Rating, Trusted Auditing, etc. Dynamic and Volatile Digital Information • Importance of keeping Identity and Profile Information up-to-date • Problem of dealing with dynamic certified data: overhead in life-cycle management • Problem in refreshing validity and trust of identity and profile attributes
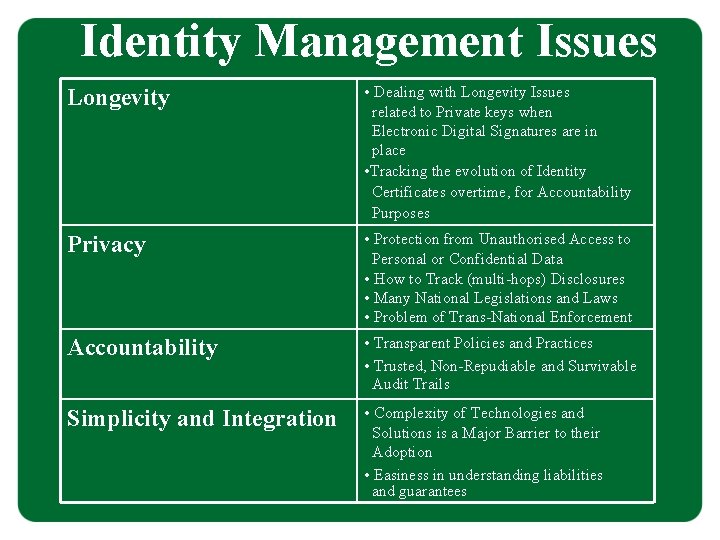
Identity Management Issues Longevity • Dealing with Longevity Issues related to Private keys when Electronic Digital Signatures are in place • Tracking the evolution of Identity Certificates overtime, for Accountability Purposes Privacy • Protection from Unauthorised Access to Personal or Confidential Data • How to Track (multi-hops) Disclosures • Many National Legislations and Laws • Problem of Trans-National Enforcement Accountability • Transparent Policies and Practices • Trusted, Non-Repudiable and Survivable Audit Trails Simplicity and Integration • Complexity of Technologies and Solutions is a Major Barrier to their Adoption • Easiness in understanding liabilities and guarantees
Identity Management: Our Reference Model
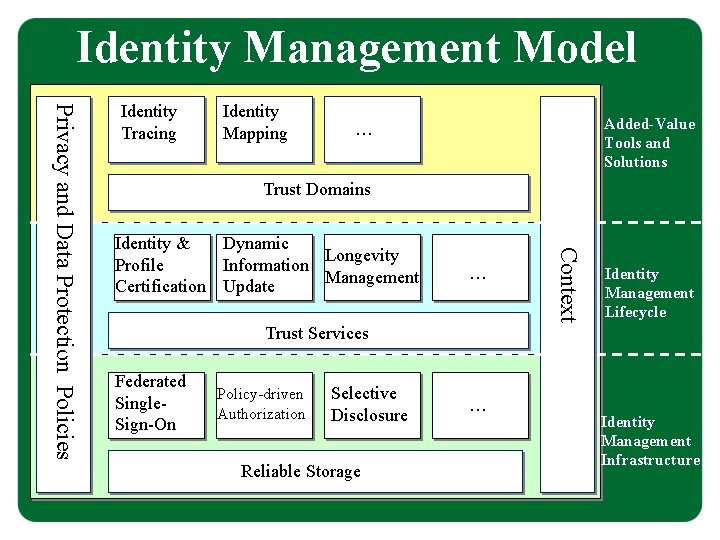
Identity Management Model Identity Mapping Added-Value Tools and Solutions … Trust Domains Identity & Dynamic Longevity Profile Information Management Certification Update … Trust Services Federated Single. Sign-On Policy-driven Authorization Selective Disclosure Reliable Storage … Context Privacy and Data Protection Policies Identity Tracing Identity Management Lifecycle Identity Management Infrastructure
Identity Management: Our Past Research PASTELS project: - Trust Management for Identities and Profiles in Dynamic B 2 B Environments - Flexible and Dynamic Authorization at the Service Level
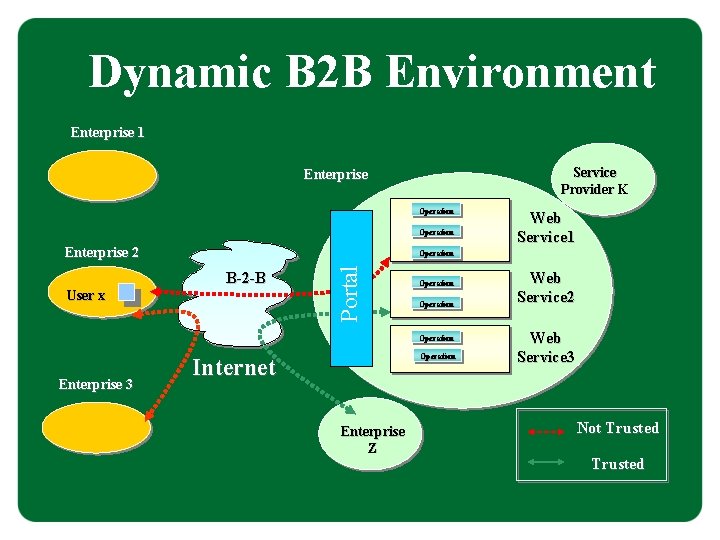
Dynamic B 2 B Environment Enterprise 1 Service Provider K Enterprise Operation Enterprise 2 User x Portal Operation B-2 -B Operation Enterprise 3 Web Service 1 Operation Internet Enterprise Z Web Service 2 Web Service 3 Not Trusted
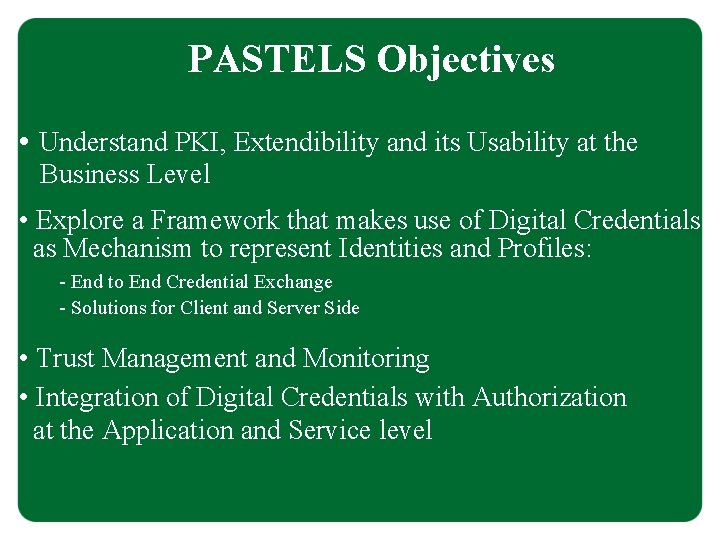
PASTELS Objectives • Understand PKI, Extendibility and its Usability at the Business Level • Explore a Framework that makes use of Digital Credentials as Mechanism to represent Identities and Profiles: - End to End Credential Exchange - Solutions for Client and Server Side • Trust Management and Monitoring • Integration of Digital Credentials with Authorization at the Application and Service level
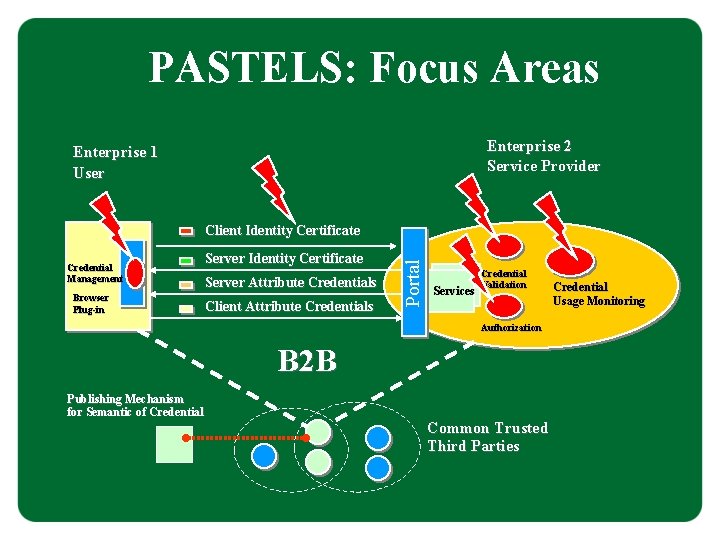
PASTELS: Focus Areas Enterprise 2 Service Provider Enterprise 1 User Credential Management Browser Plug-in Server Identity Certificate Server Attribute Credentials Client Attribute Credentials Portal Client Identity Certificate Services Credential Validation Authorization B 2 B Publishing Mechanism for Semantic of Credential Common Trusted Third Parties Credential Usage Monitoring
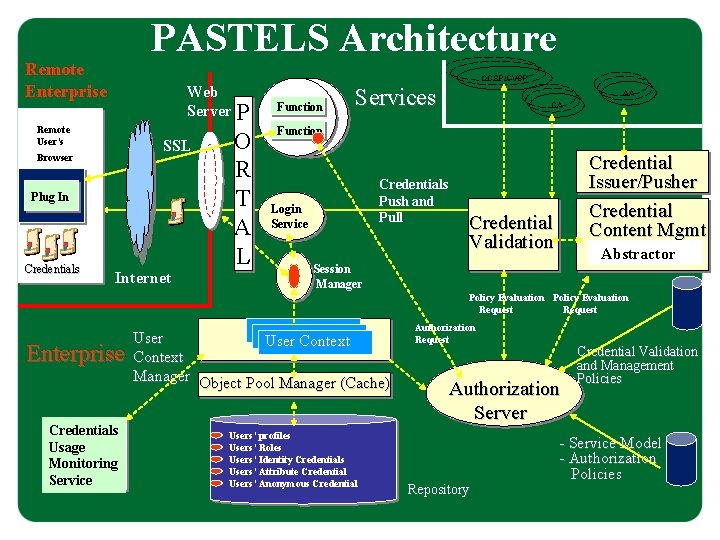
PASTELS Architecture Remote Enterprise Web Server P Remote User’s SSL Browser Plug In Credentials Internet O R T A L OCSP/CVSP Function Services AA CA Function Credentials Push and Pull Login Service Credential Issuer/Pusher Credential Content Mgmt Credential Validation Abstractor Session Manager Policy Evaluation Request Enterprise Credentials Usage Monitoring Service User Context Manager Object Pool Manager (Cache) Users’ profiles Users’ Roles Users’ Identity Credentials Users’ Attribute Credential Users’ Anonymous Credential Authorization Request Authorization Server Repository Credential Validation and Management Policies - Service Model - Authorization Policies
PASTELS Lessons Learnt • Systems driven by Polices (at the Business, Trust and Security levels) introduce Flexibility in coping with Dynamic Enterprise Requirement. • Complexity of PKI in term of Trust Management: CAs Hierarchies do not Scale and Introduce Complexity during Credential Verification • Need to Simplify PKI at the User site: Dealing with multiple Digital Credentials is Not Trivial • Dynamic Data is a Problem for Digital Credentials. Overhead in Lifecycle Management and Communication.
Identity Management: Our Current Research Areas Work In Progress: 1. Active Digital Credentials 2. Accountable Management of Identities 3. Identity Management in Dynamic Mobile 4. Environment
1. Active Digital Credentials Problems • Cope with Dynamic Identity and Profile Information (financial, trust, rating, etc. ) • Provision of Up-to-Date Certified Information • Complexity of Current Lifecycle Management when dealing with Dynamic Information
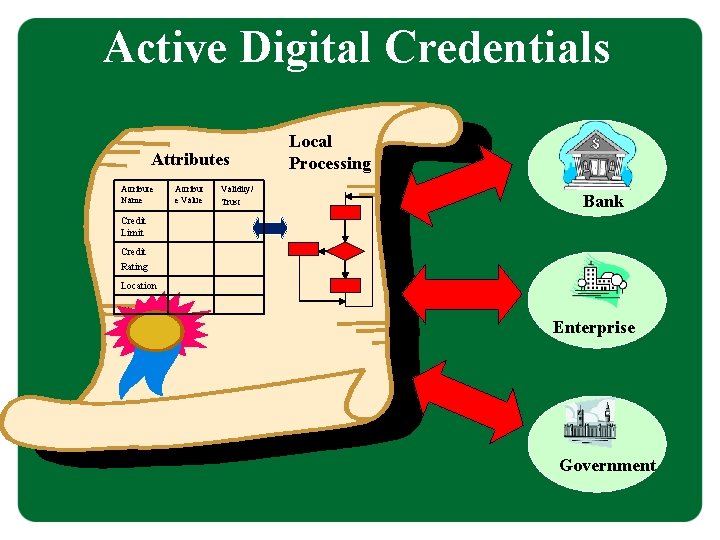
Active Digital Credentials Attribute Name Attribut e Value Validity/ Trust Local Processing Bank Credit Limit Credit Rating Location … Enterprise Government
Active Digital Credentials
Active Digital Credentials
Active Digital Credentials Scenario 1
Active Digital Credentials Scenario 2
2. Accountable Management of Identities Problems • “Who Knows What about Me”? • How to Trace Disclosures of my Identities/Profiles? • How to Enforce Privacy when Disclosing Personal/Business Identities and Profiles? • How to Prevent Abuses? Context • Federated Identity Management (Liberty Alliance) • Dynamic B 2 B environment • Personal or Group Interactions with PDAs
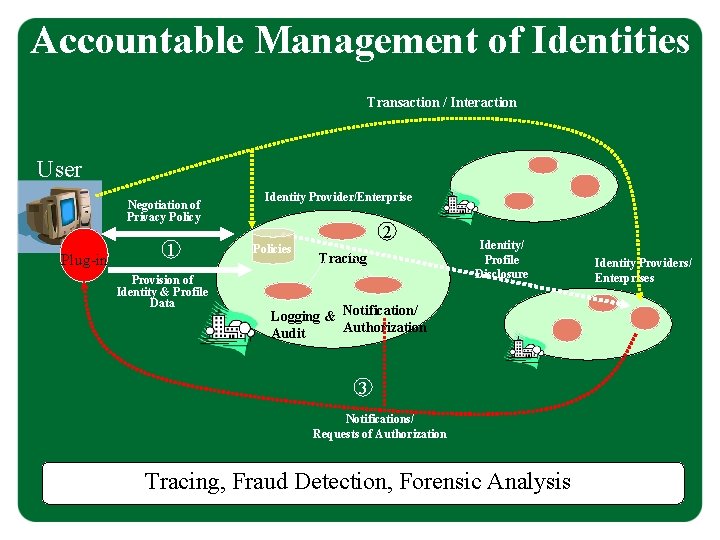
Accountable Management of Identities Transaction / Interaction User Negotiation of Privacy Policy Plug-in 1 Provision of Identity & Profile Data Identity Provider/Enterprise 2 Policies Tracing Identity/ Profile Disclosure Logging & Notification/ Authorization Audit 3 Notifications/ Requests of Authorization Tracing, Fraud Detection, Forensic Analysis Identity Providers/ Enterprises
3. Identity Management in Dynamic Mobile Environment Problems • People are Sociable but also Paranoid … • Protection of Identity and Profile Information contained in Mobile Devices and PDAs • Selective Disclosure of Information • Trust Measurement and Management Context • Ad-hoc Group Interactions • Usage of Personal Appliances (PDAs, Mobiles, …)
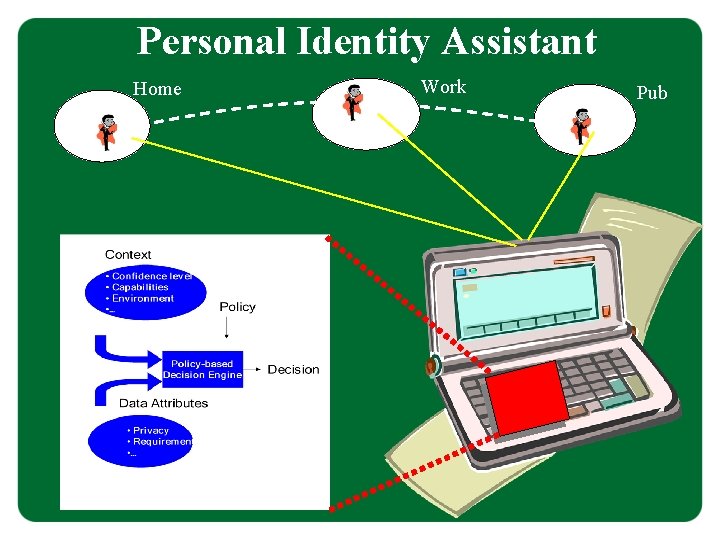
Personal Identity Assistant Home Work Pub
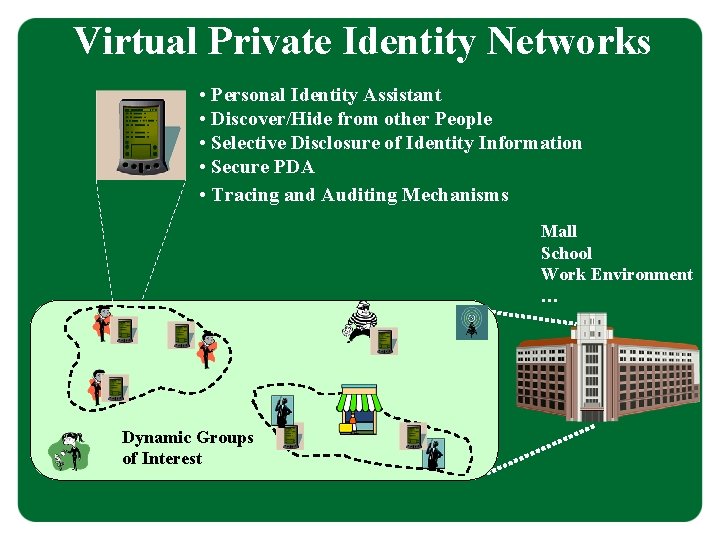
Virtual Private Identity Networks • Personal Identity Assistant • Discover/Hide from other People • Selective Disclosure of Identity Information • Secure PDA • Tracing and Auditing Mechanisms Mall School Work Environment … Dynamic Groups of Interest
Important Aspects • Importance of Security for Identity Management: at the System, Application, Service and Communication levels • Need for Survivable Data Storages to Store Sensitive Identity and Profile Data and related Logging/Auditing Information • Enforcement of Accountability: non-Repudiable Event Logging and Auditing Mechanisms • Research Challenges in Open and Dynamic Contexts, involving Dynamic Relationships and Interactions between People and Organisations.
Conclusions • Identity Management is about the Electronic Management of Digital Identities and Profiles. • Added Value: Underpins Accountability. It enables Interactions and Transactions in the Personal, Social, E-Commerce Business and Government Context. • Simplification of Identity Management is Important for Ubiquitous Computing. • Dilemmas: on one hand Identity Management helps to Bridge Digital and Physical Worlds. On the Other Hand it could be a Threat to Privacy and Freedom • It is not only a Technological Play. Legislation is Needed to Mitigate Risks

- Slides: 38