Identity Based Encrypted eMail Neil Costigan Dublin City
Identity Based Encrypted e-Mail Neil Costigan Dublin City University TM
Quick personal background… 1992. Graduate DCU (NIHE ). joined <<Telecom Ireland Software>>. 1994. Moved to Stockholm Sweden. joined consultancy firm : developed video conference software, firewalls, and ‘custom’ internet security software. 1997. Co-founded internet security company <<Celo Communications>>. 1998. Moved to San Francisco, California as CTO of Celo. 2000. Celo acquired by French smart card company <<Gemplus>>. 2001. Moved to Aix-en-Provence France to lead R&D for financial and security. 2002. Started MSc. @ DCU. Working with Dr. Mike Scott and Noel Mc. Cullough on an Enterprise Ireland funded project. 2 TM
The problem… • E-Mail is still one of the largest use of internet bandwidth. • E-Mail traffic, because of the underlying protocols, is exposed to unauthorised access (‘sniffing’) • Existing solutions, while technically functional, tend to impose prohibitive burden on the end user. 3 TM
4 TM
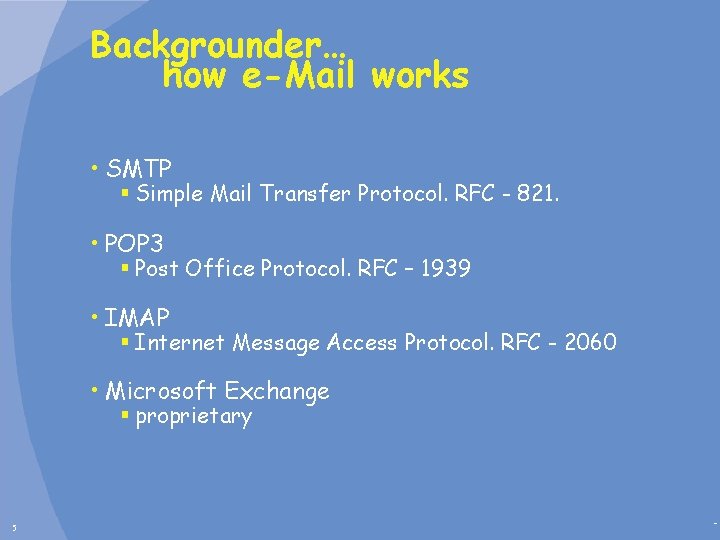
Backgrounder… how e-Mail works • SMTP § Simple Mail Transfer Protocol. RFC - 821. • POP 3 § Post Office Protocol. RFC – 1939 • IMAP § Internet Message Access Protocol. RFC - 2060 • Microsoft Exchange § proprietary 5 TM
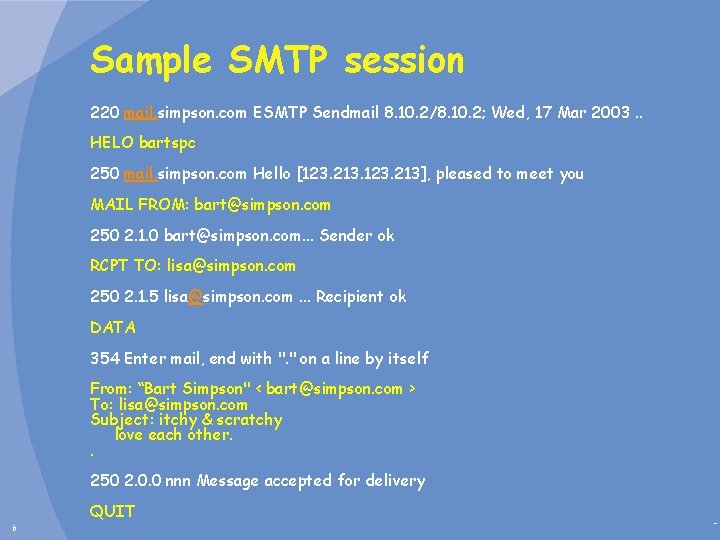
Sample SMTP session 220 mail. simpson. com ESMTP Sendmail 8. 10. 2/8. 10. 2; Wed, 17 Mar 2003. . HELO bartspc 250 mail. simpson. com Hello [123. 213], pleased to meet you MAIL FROM: bart@simpson. com 250 2. 1. 0 bart@simpson. com. . . Sender ok RCPT TO: lisa@simpson. com 250 2. 1. 5 lisa@simpson. com. . . Recipient ok DATA 354 Enter mail, end with ". " on a line by itself From: “Bart Simpson" < bart@simpson. com > To: lisa@simpson. com Subject: itchy & scratchy love each other. . 250 2. 0. 0 nnn Message accepted for delivery QUIT 6 TM
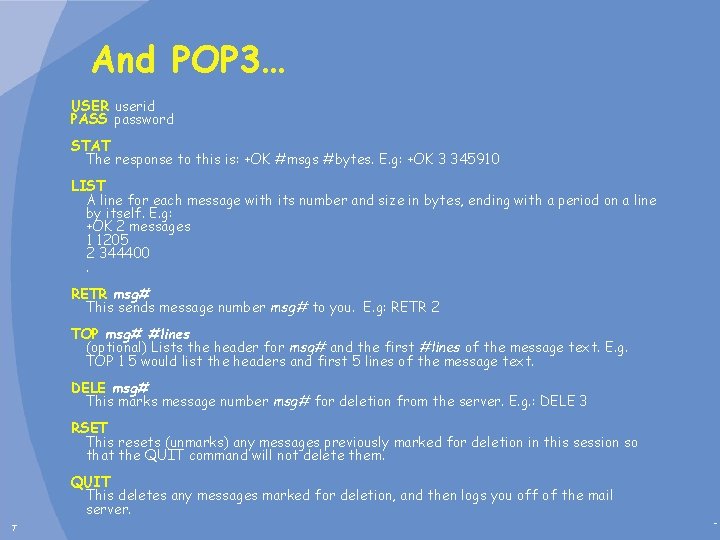
And POP 3… USER userid PASS password STAT The response to this is: +OK #msgs #bytes. E. g: +OK 3 345910 LIST A line for each message with its number and size in bytes, ending with a period on a line by itself. E. g: +OK 2 messages 1 1205 2 344400. RETR msg# This sends message number msg# to you. E. g: RETR 2 TOP msg# #lines (optional) Lists the header for msg# and the first #lines of the message text. E. g. TOP 1 5 would list the headers and first 5 lines of the message text. DELE msg# This marks message number msg# for deletion from the server. E. g. : DELE 3 RSET This resets (unmarks) any messages previously marked for deletion in this session so that the QUIT command will not delete them. QUIT This deletes any messages marked for deletion, and then logs you off of the mail server. 7 TM
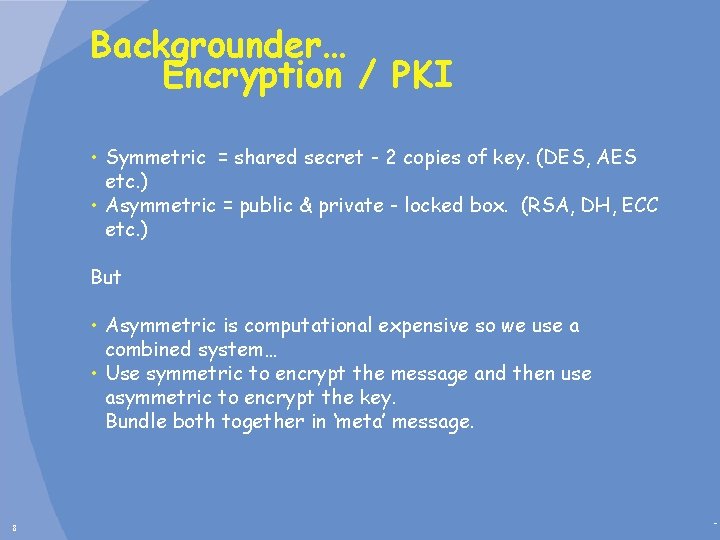
Backgrounder… Encryption / PKI • Symmetric = shared secret - 2 copies of key. (DES, AES etc. ) • Asymmetric = public & private - locked box. (RSA, DH, ECC etc. ) But • Asymmetric is computational expensive so we use a combined system… • Use symmetric to encrypt the message and then use asymmetric to encrypt the key. Bundle both together in ‘meta’ message. 8 TM
Backgrounder… existing email security S/MIME – RFC 2311 • Secure / Multipurpose Internet Mail Extensions. • Can be signed and/or encrypted. • DES encrypted with random key and this key is then encrypted by RSA public. (or DH ? ) • Keys embedded in X. 509 certificates swapped out of band. (prior or lookup. ) • Assumes trust of CA. • PGP performs similar but with ‘rings of trust’ Issues: • Losing keys ? • How to get the public key for a user? • How do I know the key I got is your key ? • User generated keys, getting signed etc. • Scalability • Revocation issues (CRLs, OCSP) 9 TM
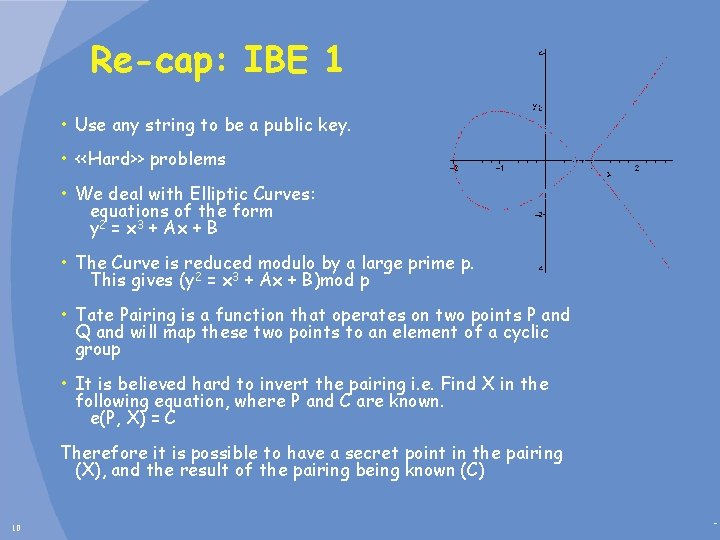
Re-cap: IBE 1 • Use any string to be a public key. • <<Hard>> problems • We deal with Elliptic Curves: equations of the form y 2 = x 3 + Ax + B • The Curve is reduced modulo by a large prime p. This gives (y 2 = x 3 + Ax + B)mod p • Tate Pairing is a function that operates on two points P and Q and will map these two points to an element of a cyclic group • It is believed hard to invert the pairing i. e. Find X in the following equation, where P and C are known. e(P, X) = C Therefore it is possible to have a secret point in the pairing (X), and the result of the pairing being known (C) 10 TM
Re-cap: IBE 2 • If you use the services of a Trusted Authority (with secret s), you have the following scheme to generate a shared secret: • A’s identity, as verified by TA, is mapped to the point A • B’s identity is mapped to the point B • A and B are given secret keys s. A and s. B respectively – remember, even they can’t calculate s on its own. shared secret = e(s. A, B) = e(A, s. B) = e(A, B)s 11 TM
Re-cap: IBE 3 • Again, the public key is a point ID and private key is s. ID, P and s. P are known to everyone. • Encryption is r. P, C = e(rs. P, ID) Message • Decryption is e(r. P, s. ID) C • Since e(r. P, s. ID) = e(s. P, ID)r = e(P, ID)sr • e(P, ID)sr Message = Message • So § You can use any email address or string or combo of both • Allows for ‘future’ sending. § There IS escrow… The TA can decrypt messages. 12 TM
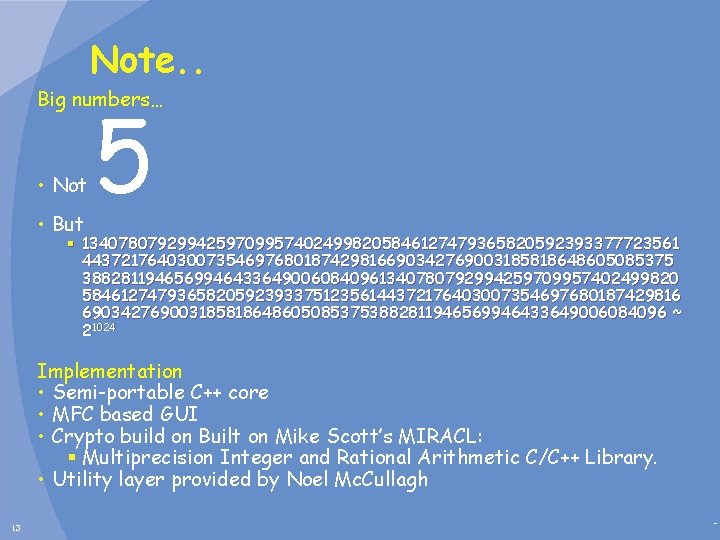
Note. . Big numbers… • Not • But 5 § 13407807929942597099574024998205846127479365820592393377723561 44372176403007354697680187429816690342769003185818648605085375 38828119465699464336490060840961340780792994259709957402499820 584612747936582059239337512356144372176403007354697680187429816 6903427690031858186486050853753882811946569946433649006084096 ~ 21024 Implementation • Semi-portable C++ core • MFC based GUI • Crypto build on Built on Mike Scott’s MIRACL: § Multiprecision Integer and Rational Arithmetic C/C++ Library. • Utility layer provided by Noel Mc. Cullagh 13 TM
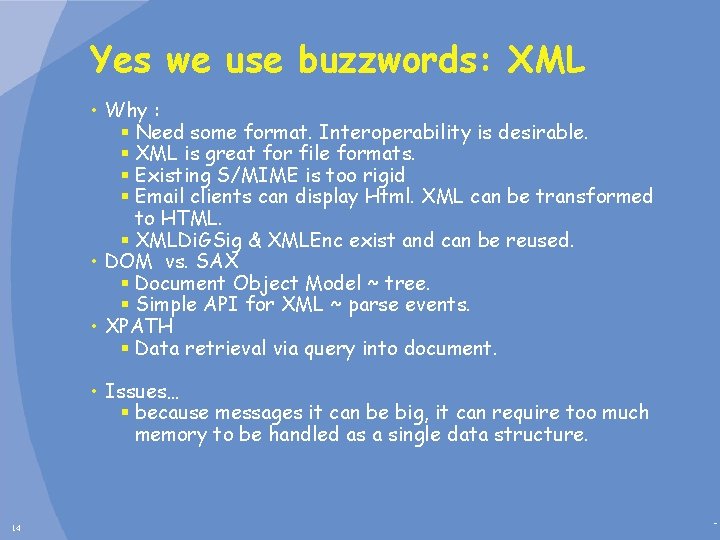
Yes we use buzzwords: XML • Why : § Need some format. Interoperability is desirable. § XML is great for file formats. § Existing S/MIME is too rigid § Email clients can display Html. XML can be transformed to HTML. § XMLDi. GSig & XMLEnc exist and can be reused. • DOM vs. SAX § Document Object Model ~ tree. § Simple API for XML ~ parse events. • XPATH § Data retrieval via query into document. • Issues… § because messages it can be big, it can require too much memory to be handled as a single data structure. 14 TM
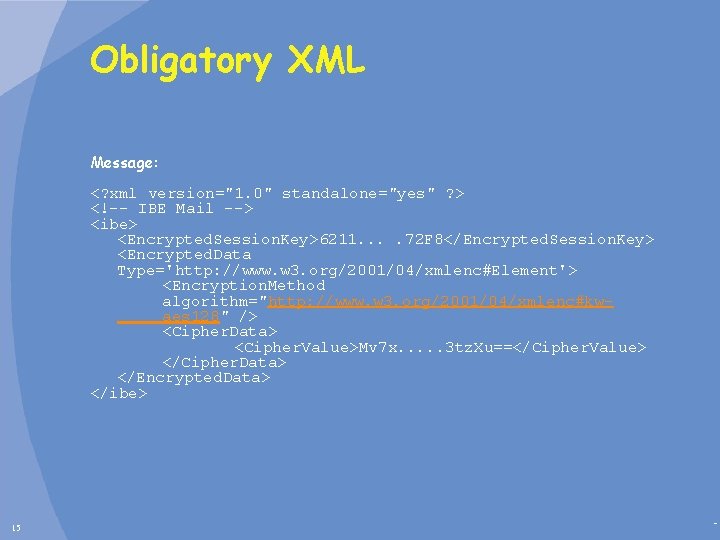
Obligatory XML Message: <? xml version="1. 0" standalone="yes" ? > <!-- IBE Mail --> <ibe> <Encrypted. Session. Key>6211. . 72 F 8</Encrypted. Session. Key> <Encrypted. Data Type='http: //www. w 3. org/2001/04/xmlenc#Element'> <Encryption. Method algorithm="http: //www. w 3. org/2001/04/xmlenc#kwaes 128" /> <Cipher. Data> <Cipher. Value>Mv 7 x. . . 3 tz. Xu==</Cipher. Value> </Cipher. Data> </Encrypted. Data> </ibe> 15 TM
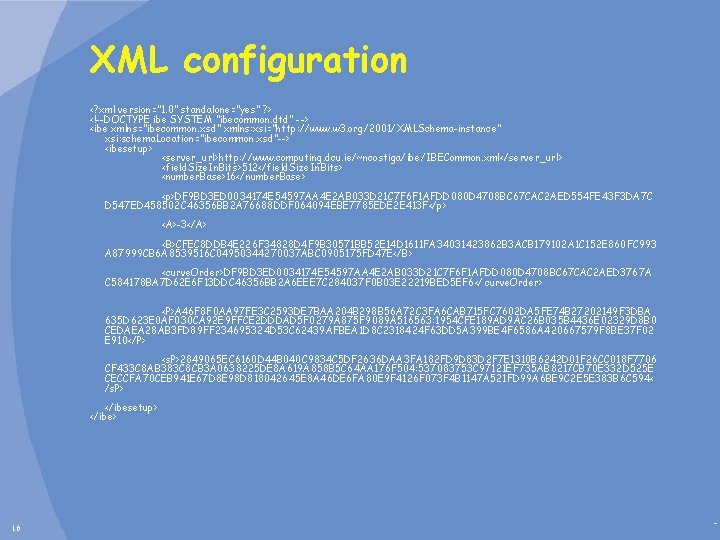
XML configuration <? xml version="1. 0" standalone="yes" ? > <!--DOCTYPE ibe SYSTEM "ibecommon. dtd" --> <ibe xmlns="ibecommon. xsd" xmlns: xsi="http: //www. w 3. org/2001/XMLSchema-instance" xsi: schema. Location="ibecommon. xsd"--> <ibesetup> <server_url>http: //www. computing. dcu. ie/~ncostiga/ibe/IBECommon. xml</server_url> <field. Size. In. Bits>512</field. Size. In. Bits> <number. Base>16</number. Base> <p>DF 9 BD 3 ED 0034174 E 54597 AA 4 E 2 AB 033 D 21 C 7 F 6 F 1 AFDD 080 D 4708 BC 67 CAC 2 AED 554 FE 43 F 3 DA 7 C D 547 ED 458502 C 46356 BB 2 A 76688 DDF 064094 EBE 7785 EDE 2 E 413 F</p> <A>-3</A> <B>CFEC 8 DDB 4 E 226 F 34828 D 4 F 9 B 30571 BB 52 E 14 D 1611 FA 34031423862 B 3 ACB 179102 A 1 C 152 E 860 FC 993 A 87999 CB 6 A 8539516 C 04950344270037 ABC 0905175 FD 47 E</B> <curve. Order>DF 9 BD 3 ED 0034174 E 54597 AA 4 E 2 AB 033 D 21 C 7 F 6 F 1 AFDD 080 D 4708 BC 67 CAC 2 AED 3767 A C 584178 BA 7 D 62 E 6 F 13 DDC 46356 BB 2 A 6 EEE 7 C 284037 F 0 B 03 E 22219 BED 5 EF 6</ curve. Order> <P>A 46 F 8 F 0 AA 97 FE 3 C 2593 DE 7 BAA 204 B 298 B 56 A 72 C 3 FA 6 CAB 715 FC 7602 DA 5 FE 74 B 27202149 F 3 DBA 635 D 623 E 0 AF 030 CA 92 E 9 FFCE 2 DDDAD 5 F 0279 A 875 F 9089 A 516563: 1954 CFE 189 AD 9 AC 26 B 035 B 4436 E 02329 D 8 B 0 CEDAEA 28 AB 3 FD 89 FF 234695324 D 53 C 62439 AFBEA 1 D 8 C 2318424 F 63 DD 5 A 399 BE 4 F 6586 A 420667579 F 8 BE 37 F 02 E 910</P> <s. P>2849065 EC 6160 D 44 B 040 C 9834 C 5 DF 2636 DAA 3 FA 182 FD 9 D 83 D 2 F 7 E 1310 B 6242 D 01 F 26 CC 018 F 7706 CF 433 C 8 AB 383 C 8 CB 3 A 0638225 DE 8 A 619 A 858 B 5 C 64 AA 176 F 504: 537083753 C 97121 EF 735 AB 8217 CB 70 E 332 D 525 E CECCFA 70 CEB 941 E 67 D 8 E 98 D 818042645 E 8 A 46 DE 6 FA 80 E 9 F 4126 F 073 F 4 B 1147 A 521 FD 99 A 6 BE 9 C 2 E 5 E 383 B 6 C 594< /s. P> </ibesetup> </ibe> 16 TM
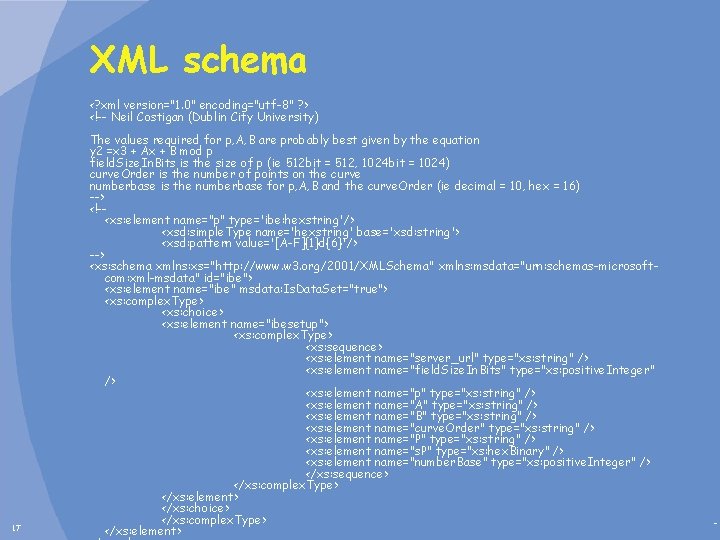
XML schema <? xml version="1. 0" encoding="utf-8" ? > <!-- Neil Costigan (Dublin City University) 17 The values required for p, A, B are probably best given by the equation y 2 =x 3 + Ax + B mod p field. Size. In. Bits is the size of p (ie 512 bit = 512, 1024 bit = 1024) curve. Order is the number of points on the curve numberbase is the numberbase for p, A, B and the curve. Order (ie decimal = 10, hex = 16) --> <!-<xs: element name="p" type='ibe: hexstring'/> <xsd: simple. Type name='hexstring' base='xsd: string'> <xsd: pattern value='[A-F]{1}d{6}'/> --> <xs: schema xmlns: xs="http: //www. w 3. org/2001/XMLSchema" xmlns: msdata="urn: schemas-microsoftcom: xml-msdata" id="ibe"> <xs: element name="ibe" msdata: Is. Data. Set="true"> <xs: complex. Type> <xs: choice> <xs: element name="ibesetup"> <xs: complex. Type> <xs: sequence> <xs: element name="server_url" type="xs: string" /> <xs: element name="field. Size. In. Bits" type="xs: positive. Integer" /> <xs: element name="p" type="xs: string" /> <xs: element name="A" type="xs: string" /> <xs: element name="B" type="xs: string" /> <xs: element name="curve. Order" type="xs: string" /> <xs: element name="P" type="xs: string" /> <xs: element name="s. P" type="xs: hex. Binary" /> <xs: element name="number. Base" type="xs: positive. Integer" /> </xs: sequence> </xs: complex. Type> </xs: element> </xs: choice> </xs: complex. Type> </xs: element> TM
Potential solutions • New secure email client. • ‘Add-on’ to existing systems. • ‘Catch all’ approach. 18 TM
New ‘Secure’ client • Exclusively an identity based encryption client • Commercially flawed. • Great as a test bed and to fine tune formats. 19 TM
Add-on: Outlook • Office allows automation via Scripting and COM add-ins • Reverse engineer VB scripting to find event ‘hooks’. • Pros § Use familiar interface, training, setup etc. § Can do proprietary MS Exchange • Cons § Version war § Limited in some respects… § Over featured in others. • Still most commercially viable (XX%? ) • Options include open source like Mozilla or Ximian 20 TM
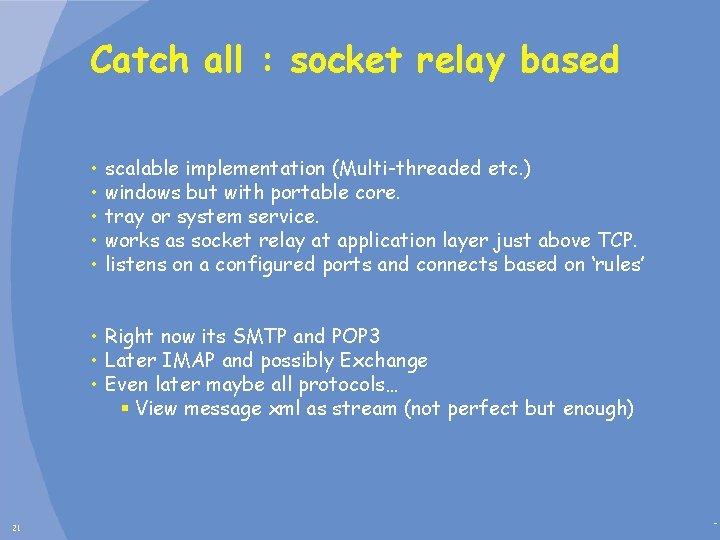
Catch all : socket relay based • • • scalable implementation (Multi-threaded etc. ) windows but with portable core. tray or system service. works as socket relay at application layer just above TCP. listens on a configured ports and connects based on ‘rules’ • Right now its SMTP and POP 3 • Later IMAP and possibly Exchange • Even later maybe all protocols… § View message xml as stream (not perfect but enough) 21 TM
22 TM
23 TM
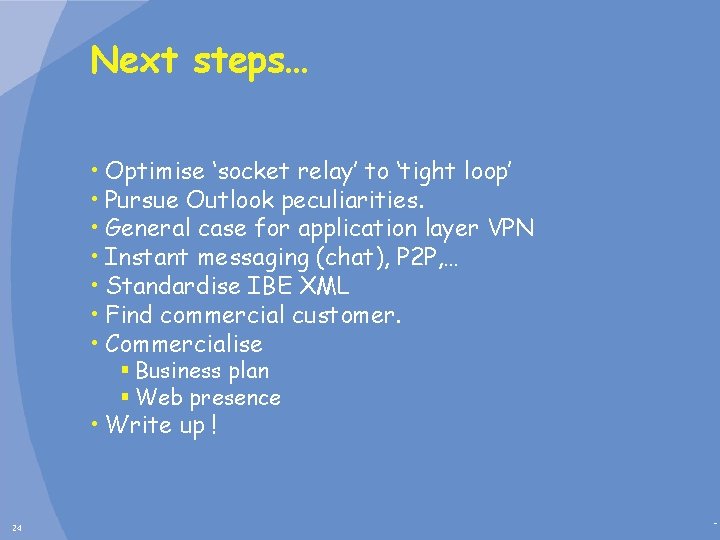
Next steps… • Optimise ‘socket relay’ to ‘tight loop’ • Pursue Outlook peculiarities. • General case for application layer VPN • Instant messaging (chat), P 2 P, … • Standardise IBE XML • Find commercial customer. • Commercialise § Business plan § Web presence • Write up ! 24 TM
- Slides: 24