ICT Security Issues in Europe Tony Brett Oxford

ICT Security Issues in Europe Tony Brett Oxford University Computing Services http: //users. ox. ac. uk/~tony
Agenda u Brief Security Update u Identity Theft u Standards and Governments u The Future of Spam u Vulnerabilities u Biometrics u Some Stories u Questions & URLs
A Brief Security Update “Even in 2003, security is the least understood of all computer system components. ”
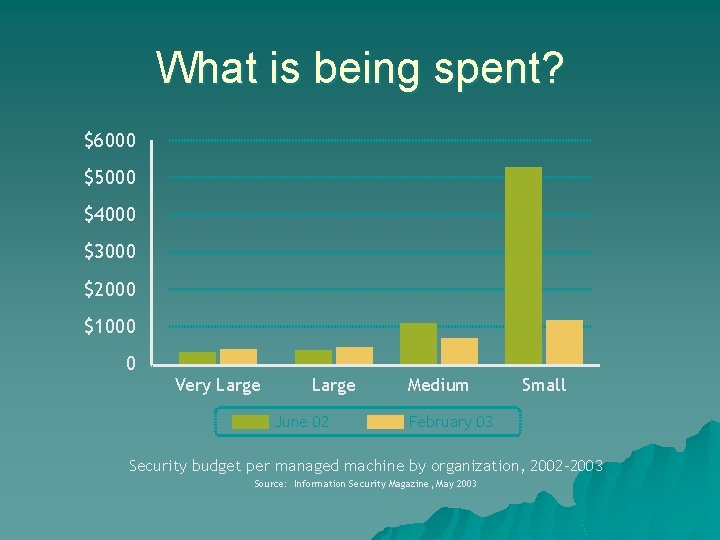
What is being spent? $6000 $5000 $4000 $3000 $2000 $1000 0 Very Large June 02 Medium Small February 03 Security budget per managed machine by organization, 2002 -2003 Source: Information Security Magazine, May 2003
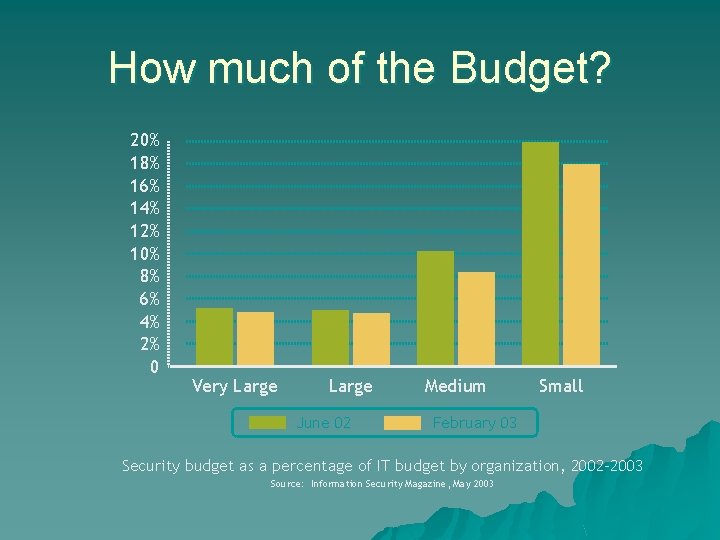
How much of the Budget? 20% 18% 16% 14% 12% 10% 8% 6% 4% 2% 0 Very Large June 02 Medium Small February 03 Security budget as a percentage of IT budget by organization, 2002 -2003 Source: Information Security Magazine, May 2003
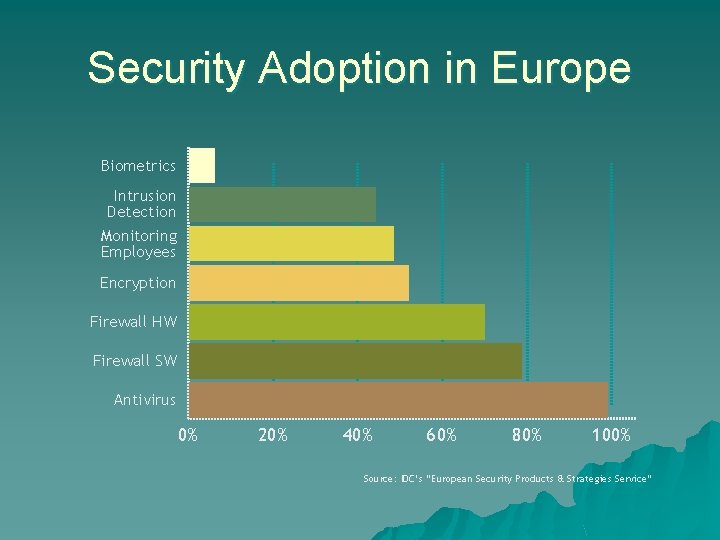
Security Adoption in Europe Biometrics Intrusion Detection Monitoring Employees Encryption Firewall HW Firewall SW Antivirus 0% 20% 40% 60% 80% 100% Source: IDC’s “European Security Products & Strategies Service”
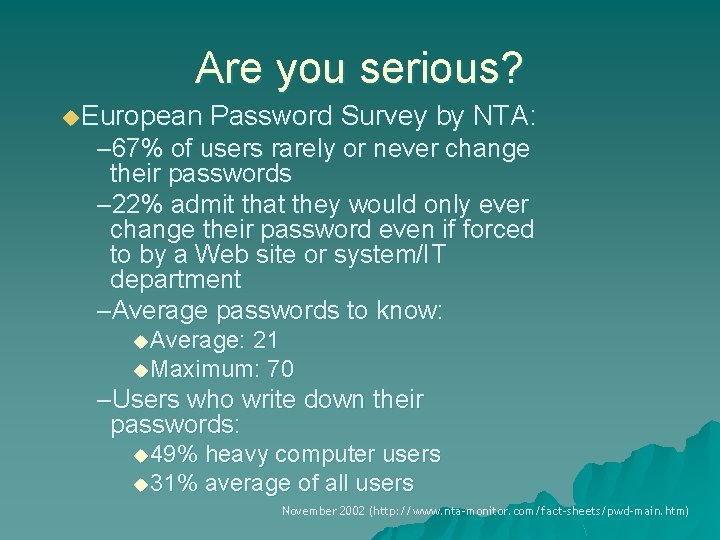
Are you serious? u. European Password Survey by NTA: – 67% of users rarely or never change their passwords – 22% admit that they would only ever change their password even if forced to by a Web site or system/IT department –Average passwords to know: u. Average: 21 u. Maximum: 70 –Users who write down their passwords: u 49% heavy computer users u 31% average of all users November 2002 (http: //www. nta-monitor. com/fact-sheets/pwd-main. htm)

63% …of security breaches are caused by human error Source: Computing Technology Industry Assn. , 2003
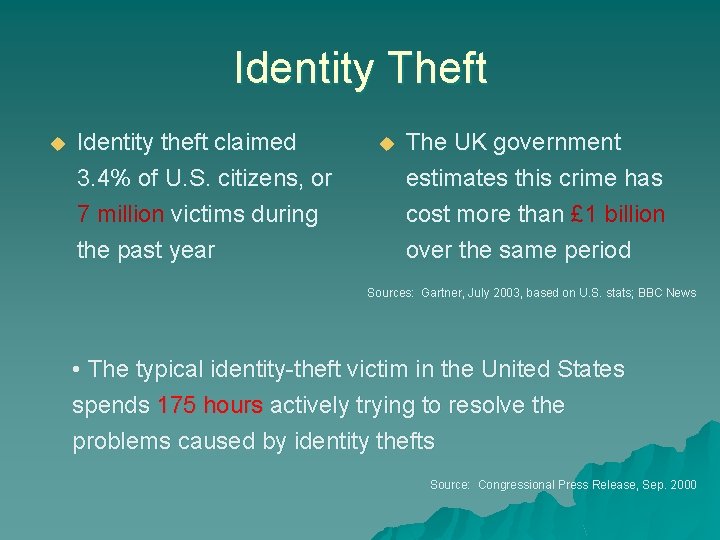
Identity Theft u Identity theft claimed 3. 4% of U. S. citizens, or 7 million victims during the past year u The UK government estimates this crime has cost more than £ 1 billion over the same period Sources: Gartner, July 2003, based on U. S. stats; BBC News • The typical identity-theft victim in the United States spends 175 hours actively trying to resolve the problems caused by identity thefts Source: Source Congressional Press Release, Sep. 2000
Identity theft …is Britain's fastest-growing white-collar crime, increasing at nearly 500% a year. “The number of consumers who have fallen prey to identity thieves is severely underreported. ” Moreover, arrests in identity theft cases are extremely rare, catching the perpetrator in only one out of every 700 cases.
![“The current [Internet] identity-theft hot spots are Eastern Europe and Southeast Asia where the “The current [Internet] identity-theft hot spots are Eastern Europe and Southeast Asia where the](http://slidetodoc.com/presentation_image/16d16ecd51efce6d2ff0a230464dbbea/image-11.jpg)
“The current [Internet] identity-theft hot spots are Eastern Europe and Southeast Asia where the level of education and technical sophistication is high, and where tracking down and prosecuting criminals can be very tricky. ” Bruce Townsend Special Agent, Financial Crimes Division US Secret Service Source: Unesco Observatory on the Information Society
A true story u Tri. West Healthcare Alliance in Arizona provided healthcare services for members of the U. S. military. u Thieves stole computers containing confidential records. u Losses were $2. 7 million. u Cost to victims: $30 million to repair damage to credit ratings
The worst case scenario u. Stolen acts identities used for criminal –First day of work for a woman in San Diego –Employer did a background check –She arrived, and then departed in handcuffs u. Her ID was used when another woman was arrested for drug possession.
Phishing u E-mail purporting to be from Bank etc u Invites submission of personal details u The recent Russian phishing scams load the real Barclays/Halifax/Nationwide etc. pages in one browser window along with a pop-up site from the fake site requesting account details. u Fake URLS: http: //www. barclays. co. uk@3468664375/verify. htm
Pop Quiz 1 u. Since 1976, more than 2. 5 million U. S. patents have been issued. How many reference the word “security”? –A. 16, 475 –B. 123, 210 –C. 64, 689 D. –D. 493, 298

Standards & Governments u The United States has taken an industryby-industry approach to privacy protection in its laws and regulations, in contrast to European countries. u Privacy measures are contained in specific laws on credit reporting, cable television regulation, video rental data, banking information, telecommunications, etc…
Variation by Country u The United States relies on citizen initiative and judicial enforcement u Britain uses a registration system u Germany uses an ombudsman u Sweden employs a licensing system Info on comparative laws: Colin J. Bennett, Regulating Privacy: Data Protection and Public Policy in Europe and the United States (Ithaca: Cornell University Press, 1992)

Standards to Watch u XML is basis for many new protocols Security Assertion Markup Language u Web Services Description Language u – Tells apps what web services are available and how to ask for them u Simple Object Access Protocol – Defines the conversation between service provider requestor u Universal Description, Discovery, and Integration – Provides repositories for service definitions and
European Standards u British Standard 7799 Part 1 – High-level security advice – Just a checklist and not a process? u British Standard 7799 Part 2 – Similar to part 1, but with fewer suggestions for implementation (“shall” instead of “should”) u ISO 17799 – Based on BS 7799, passed in 2000
Other Security Works u ISO Guidelines for the Management of IT Security – Five-part technical report u NIST Special Publication 800 -14 – Best practices based on BS 7799 but more detailed – Security handbook: 800 -12 – Security self-assessment: 800 -26
The Midas Touch… u U. S. requires the 27 visa-waved countries to install biometric codes onto passports by October 2004 u Singapore may be first country to implement u U. K. to use fingerprint info u New EU passports will be embedded with a radio frequency ID chip that contains biometric data

European Digital Rights u European Digital Rights (EDRi), was formed by 10 separate bodies in seven EU member states u In the UK, the Foundation for Information Policy Research (FIPR) and Privacy International will work with EDRi. u They oppose EU and Council of Europe incursions into personal data – Data retention requirements – Telecommunications interception – Council of Europe cybercrime treaty – Internet rating and filtering – Restrictions on Web-based freedom of speech.
Viva la Air France! u Air France won the right to take over a Web site that uses a garbled version of its name apparently to steer business toward other travel firms and some finance companies. u Known as "typosquatting'' u Ruling by United Nations' World Intellectual Property Organisation (Wipo), which runs an arbitration service for Internet name disputes u The arbitrator said that the "typographical misspelling'' of the Air France trademark showed that the site was registered in bad faith u http: //www. 0 xford-university. org/ u http: //www. yaju. com
The Future of SPAM u Message. Labs scanned (Oct. 2003) – 252 million e-mail messages for spam – 325. 8 milion e-mails for viruses u Results – Spam was 50. 5% (15% in oct 2002) of overall messages; increasing at 15% per month – 1% Viruses

5 th March 2003 u. AOL announced it had blocked one billion spam emails from reaching its members in one day
US Laws u Many new laws being created by states, feds, international u Lawsuits being filed against “legitimate” spammers (AOL is a big plaintiff) u California court upheld a law requiring unsolicited commercial email to have “ADV: ” or “ADV: ADLT” in the subject u False headers in Minnesota are subject to $25 per email or $35, 000 per day max

Euro-SPAM u Opt-in and opt-out laws for EC (Directive 2002/58/EC u Entry into official journal 31 st July 2002 u 31 st October 2003, Implementation by member states u Prohibits unsolicited email, SMS, mail, etc. u Requires that prior explicit consent of the recipients (OK The pictures are Euro-Trash!)
Euro. CAUCE u The European Coalition Against Unsolicited Commercial Email u Internet users who are fed up with spam and have formed a coalition to promote legislation which would outlaw UCE u Volunteers, don’t take money http: //www. euro. cauce. org/en/index. html

The Goal u Make spamming cost prohibitive u Spammers will send out millions of messages to reach a few stupid users u We all suffer
How they do it u Number/symbol substitution – “Get Low Mortgage” or “Get Low M 0 rtgage” – Holy Sh!t u Misspell key words – Creditcard u Innocuous words – Come see me u Use your name in the subject or message
Filter technologies u Statistical Filters – Looks for words in email over period of time – Calculates the likelihood of spam – Reliable 95 -99% of the time – Generate few false positives u Open source spam filters u Bayesian Filters - http: //spamconference. org
Vulnerabilities u They can be anywhere – Is MP 3 or WMF modified? Will it take over your machine?
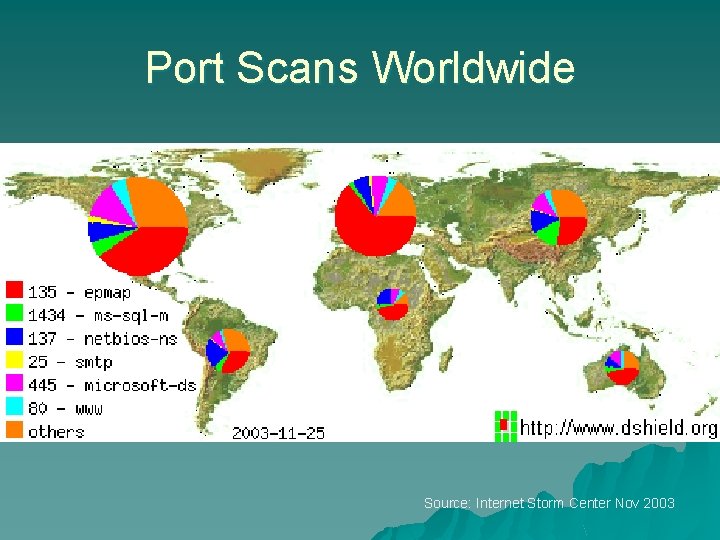
Port Scans Worldwide Source: Internet Storm Center Nov 2003
Top 10 Ports Scanned 80 World Wide Web HTTP u 1433 Microsoft-SQL-Server u 1434 Microsoft-SQL-Monitor u 135 DCE endpoint resolution u 137 NETBIOS Name Service u 445 Win 2 k+ Server Message Block u 25 Simple Mail Transfer u 901 Real. Secure sensor u 53 Domain Name Server u 554 Real Time Stream Control Protocol u Source: Internet Storm Center Nov 2003
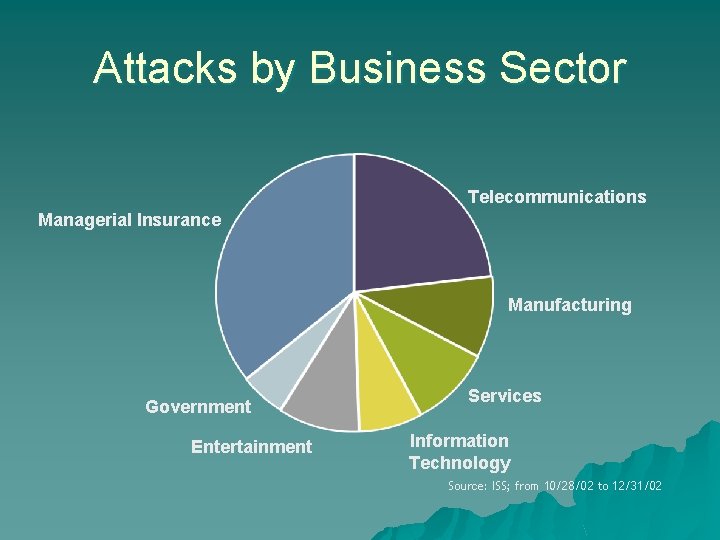
Attacks by Business Sector Telecommunications Managerial Insurance Manufacturing Government Entertainment Services Information Technology Source: ISS; from 10/28/02 to 12/31/02
Virus Control u Trying to improve upon heuristics to prevent viruses u Still not used by all users u Stupid users still are enticed – Can bypass email when users jump to a web site – Click here and see big thingies…
Pop Quiz #2 u What was the first patent that used the term “biometrics”? A. A fingerprint ID machine B. A basal body temperature monitor C. A method for tranquilizing warm-blooded animals A treadmill that tracks D. AD. treadmill that tracks heart rate
Biometrics: Free lunch through eyes u Western England High School u Problem: – Poor kids showed voucher while “rich” kids used money u Solution: – Uses retina scan to verify student – Pull money from account or redeem electronic voucher
You smell! u Each mouse has a unique urine smell u Similar link may exist between genes that control a human’s immune system and their body odor u Funding to determine if human smells are unique
Walk the walk u Nationwide Building Society (UK) is using biometric signatures to combat fraudulent transactions and cut the use of paper u Requires employees to verify fingerprints every several transactions
Vacation messages “Sorry I can’t reply to your email. I’m on a holiday until …” With a simple crossreference, a bad guy can get your home address Use “out of the office today” or use the auto-reply on internal email
Young hacker! u 11 u At year old boy in Florida lunch, went to classroom u Teacher hadn’t logged off u Changed his grades u Facing felony charges (doubtful he’ll see any jail time)
u Trippin Smurfs Jail time… – Broke into 10 JPL servers on day of Columbia tragedy (Feb. 1) – Expected to receive long prison term u Brian Ferguson – Hacked AOL account of NY judge Kim Eaton – 3 years u William Grace & Brandon Wilson – Hacked California Court – 9 years behind bars u Douglas Boudreqeau – – – Broke into Boston College network Charged $2000 to other BC students Suspended, and school will pay for his defence to “ensure he is adequately represented”
Nigerian Bank Scan – 419 u People receive email claiming that they’ve won $10 million u All they need to do is cash cheque and have $1 million transferred to account in Nigeria u User makes $9 million for effort u After money is transferred, bank account is closed; cheque bounces; user out $1 million u $90, 000 average loss to 150 U. K. residents who fell for it
As principal Vernon said in The Breakfast Club… “Don’t mess with a bull… …you’ll get the horns. ”
Resources and Questions u Thanks to Alan Mark of Novell for permission to use some of his slides from Brainshare Europe 2003 in this presentation u Questions? u http: //users. ox. ac. uk/~tony
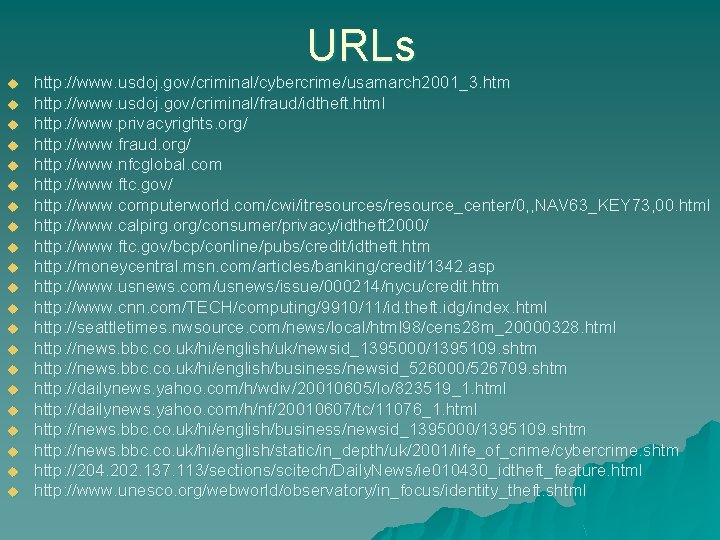
URLs u u u u u u http: //www. usdoj. gov/criminal/cybercrime/usamarch 2001_3. htm http: //www. usdoj. gov/criminal/fraud/idtheft. html http: //www. privacyrights. org/ http: //www. fraud. org/ http: //www. nfcglobal. com http: //www. ftc. gov/ http: //www. computerworld. com/cwi/itresources/resource_center/0, , NAV 63_KEY 73, 00. html http: //www. calpirg. org/consumer/privacy/idtheft 2000/ http: //www. ftc. gov/bcp/conline/pubs/credit/idtheft. htm http: //moneycentral. msn. com/articles/banking/credit/1342. asp http: //www. usnews. com/usnews/issue/000214/nycu/credit. htm http: //www. cnn. com/TECH/computing/9910/11/id. theft. idg/index. html http: //seattletimes. nwsource. com/news/local/html 98/cens 28 m_20000328. html http: //news. bbc. co. uk/hi/english/uk/newsid_1395000/1395109. shtm http: //news. bbc. co. uk/hi/english/business/newsid_526000/526709. shtm http: //dailynews. yahoo. com/h/wdiv/20010605/lo/823519_1. html http: //dailynews. yahoo. com/h/nf/20010607/tc/11076_1. html http: //news. bbc. co. uk/hi/english/business/newsid_1395000/1395109. shtm http: //news. bbc. co. uk/hi/english/static/in_depth/uk/2001/life_of_crime/cybercrime. shtm http: //204. 202. 137. 113/sections/scitech/Daily. News/ie 010430_idtheft_feature. html http: //www. unesco. org/webworld/observatory/in_focus/identity_theft. shtml
- Slides: 48