IBM zVM Module 11 Networking 2004 IBM Corporation
IBM ^ z/VM Module 11: Networking © 2004 IBM Corporation
IBM ^ Objectives § Describe TCP/IP setup in conjunction with z/VM § Understand the fundamental concepts of computer networks § List and describe the four different protocols of the TCP/IP architecture and their purpose § Describe the purpose and function of routing © 2004 IBM Corporation
IBM ^ Objectives continued § List the reasons for using a routing table and the major differences between these dynamic routing table formats: RIP-1 4 RIP-2 4 OSPF 4 § List and describe the four different types of internet addressing: Network address format 4 Broadcast address format 4 Multicast address format 4 Subnetwork address format 4 © 2004 IBM Corporation
IBM ^ Objectives continued § Explain the major differences between the fiber connectors ESCON and FICON § Show and describe how a Parallel Sysplex is set up and the enhancements it can provide § Describe the devices and protocols that are available when configuring your network, including: 4 QDIO (can be configured into guest LANs with z/VM 4. 3) 4 OSA-Express and OSA-2 4 Hiper. Sockets (can be configured into guest LANs) © 2004 IBM Corporation
IBM ^ Objectives continued § Describe how VIPA is capable of adding another level of protection against network failures, along with recovery § Discuss the four major commands needed to monitor your TCP/IP network: 4 NETSTAT 4 RPCINFO 4 PING 4 TRACERTE © 2004 IBM Corporation
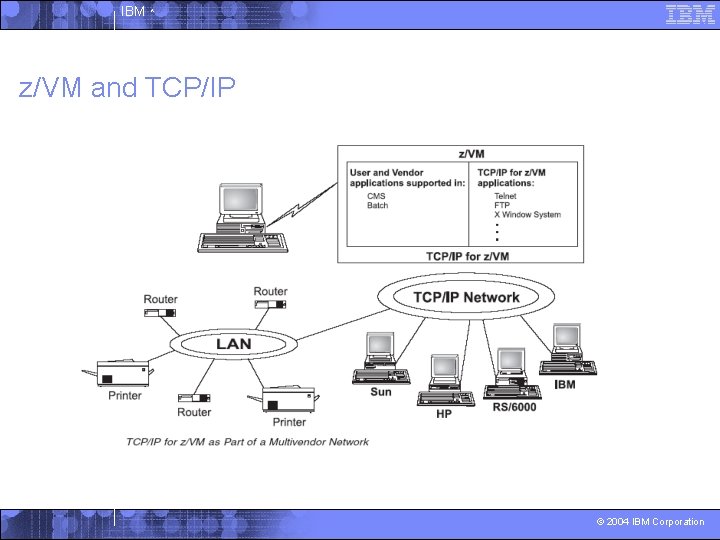
IBM ^ z/VM and TCP/IP © 2004 IBM Corporation
IBM ^ Computer Network § Is a group of connected nodes that are used for data communication § Its configuration consists of data processing devices, software, and transmission media that are linked for information interchange § Nodes are the functional units, located at the points of connection among the data circuits § Some of the more common network architectures, or protocols, used today are OSI, TCP/IP, SNA, and ISDN. © 2004 IBM Corporation
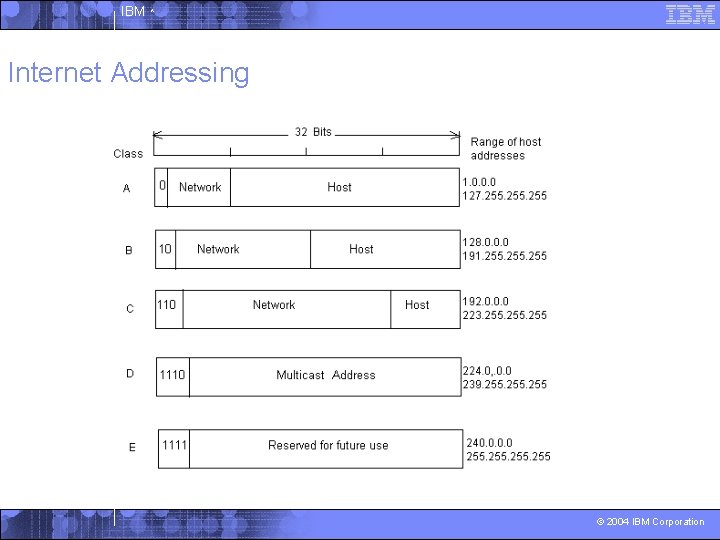
IBM ^ Internet Addressing © 2004 IBM Corporation
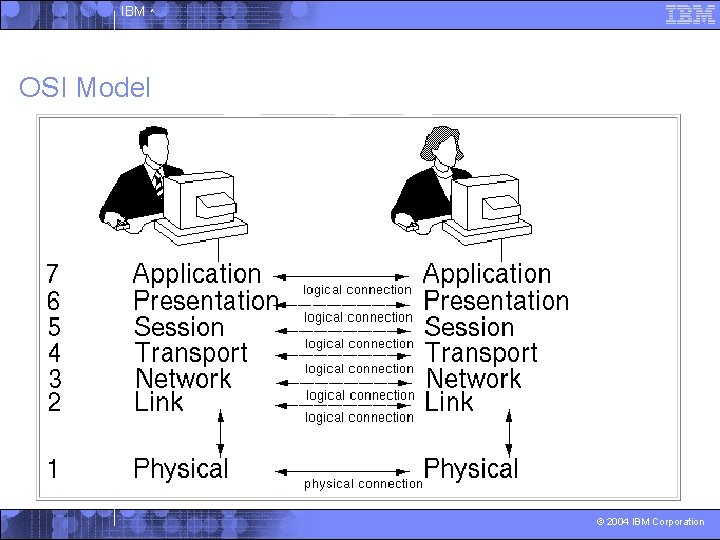
IBM ^ OSI Model © 2004 IBM Corporation
IBM ^ Internet Environment § The internet is a logical collection of networks supported by: 4 Gateways 4 Routers 4 Bridges 4 Hosts 4 Various layers of protocols § Protocols specify a set of rules and formats required to exchange and transfer packets of information. © 2004 IBM Corporation
IBM ^ Internet Environment continued § Internet – a worldwide network of computer networks § Intranet – a private network, usually used within a closed environment supporting one company § Extranet – a private network that uses the Internet protocols and the public telecommunication system to share part of a company’s business information with outside vendors © 2004 IBM Corporation
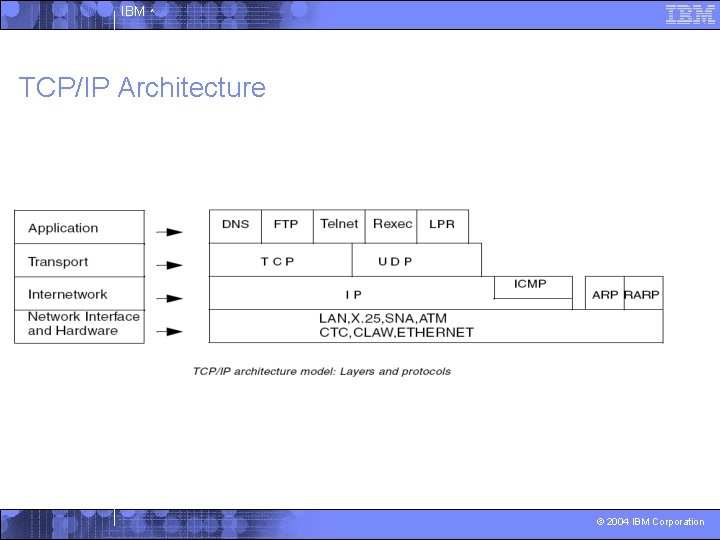
IBM ^ TCP/IP Architecture © 2004 IBM Corporation
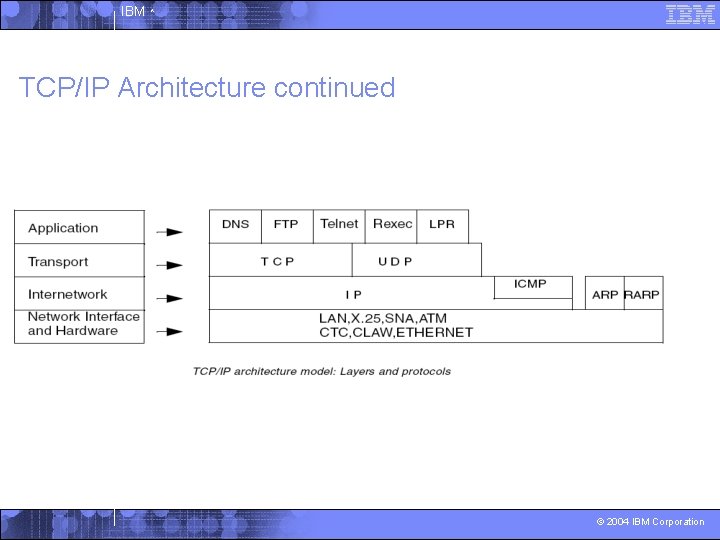
IBM ^ TCP/IP Architecture continued © 2004 IBM Corporation
IBM ^ Routing: Overview § It is the method by which a host or a gateway decides where to send a datagram. § There are two kinds of routing that are involved in communication within an internet: 4 Direct routing is used when the source and destination nodes are in the same logical network within an internet. 4 Indirect routing is used when the source and destination nodes are on different networks within an internet, where source nodes send packets to a gateway or router on the same network using direct routing and the packets are forwarded through intermediate gateways until the destination is reached © 2004 IBM Corporation
IBM ^ Routing: Overview - Terms § Important terms are: 4 Router 4 Gateway 4 Daemon 4 Network Interface 4 Network 4 Subnetwork 4 FTP 4 TELNET © 2004 IBM Corporation
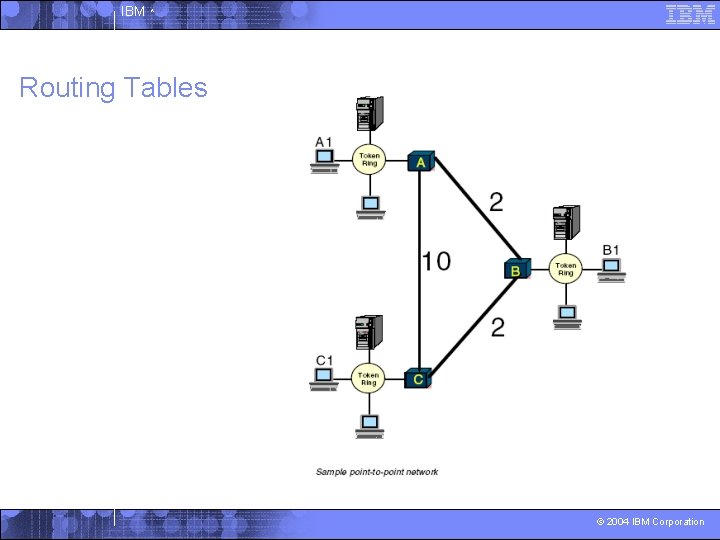
IBM ^ Routing Tables © 2004 IBM Corporation
IBM ^ Routing Table Management § The most complex task in configuring the TCP/IP network routing is establishing the routing tables. § Static routing requires you to manually configure the routing tables yourself. § With dynamic routing, information is automatically exchanged among various routers in your network, which allows IP address to be found when a new IP host come online. § The more common interior gateway protocols in dynamic routing are: RIP-1 4 RIP-2 4 © 2004 IBM Corporation
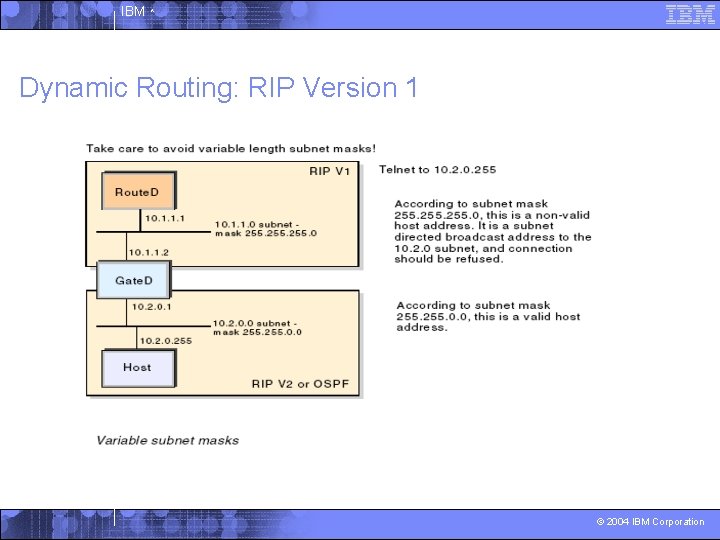
IBM ^ Dynamic Routing: RIP Version 1 © 2004 IBM Corporation
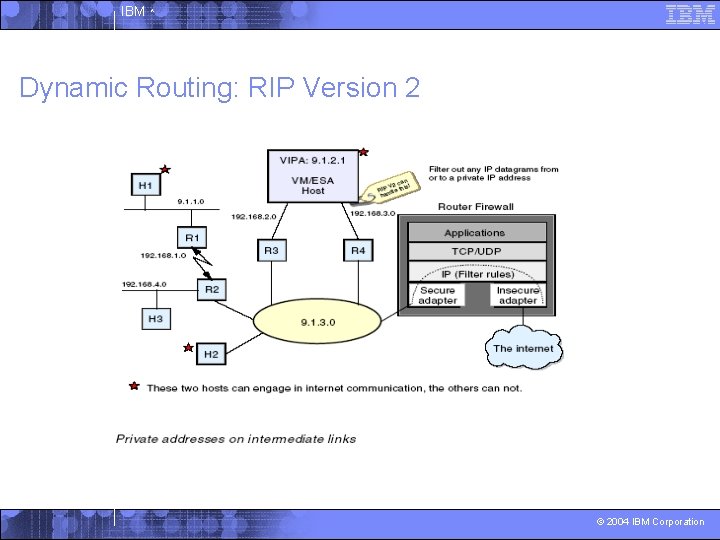
IBM ^ Dynamic Routing: RIP Version 2 © 2004 IBM Corporation
IBM ^ OSPF § Open Shortest Path First § OSPF differs from RIP in these ways: 4 No limitations on the hop count 4 Intelligent use of VLSM 4 Uses IP multicast to send link-state updates 4 Better convergence 4 Better load balancing 4 Allows for routing authentication © 2004 IBM Corporation
IBM ^ BGP § Border Gateway Protocol is an interautonomous system routing protocol. § The attributes that BGP uses in the route selection process include: 4 Weight 4 Local preference 4 Multi-exit discriminator 4 Origin 4 AS_Path 4 Next hop 4 Community © 2004 IBM Corporation
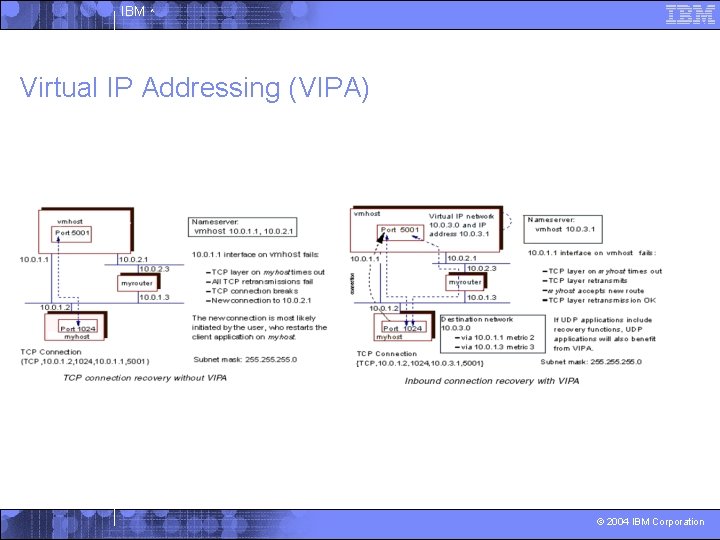
IBM ^ Virtual IP Addressing (VIPA) © 2004 IBM Corporation
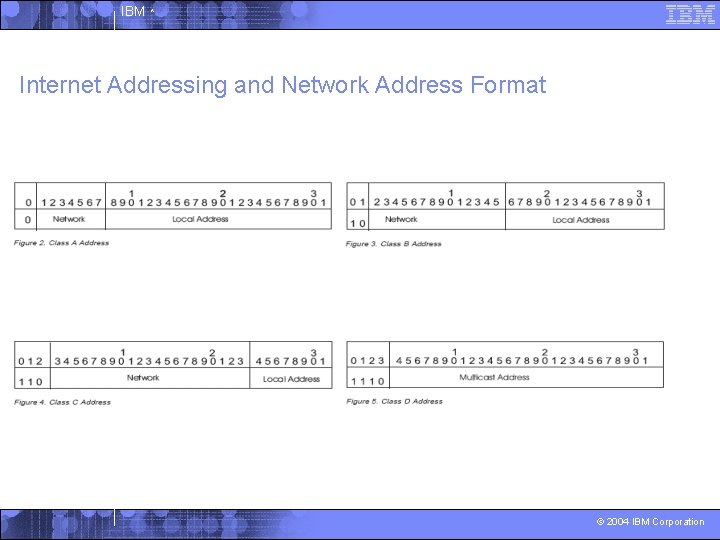
IBM ^ Internet Addressing and Network Address Format © 2004 IBM Corporation
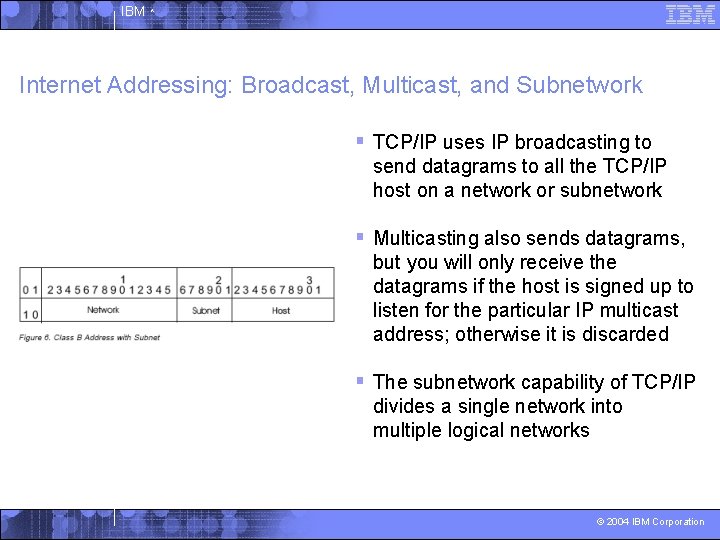
IBM ^ Internet Addressing: Broadcast, Multicast, and Subnetwork § TCP/IP uses IP broadcasting to send datagrams to all the TCP/IP host on a network or subnetwork § Multicasting also sends datagrams, but you will only receive the datagrams if the host is signed up to listen for the particular IP multicast address; otherwise it is discarded § The subnetwork capability of TCP/IP divides a single network into multiple logical networks © 2004 IBM Corporation
IBM ^ Networking Device Options © 2004 IBM Corporation
IBM ^ ESCON (Enterprise System Connectivity) § The high-speed fiber optic architecture first available on ES/9000 and many other peripherals § Originally used LEDs and worked at 10 MBps over 3 km stretches § A laser version announced in 1991 is capable of working at greater distances § Was replaced by FICON in 1998, though still available © 2004 IBM Corporation
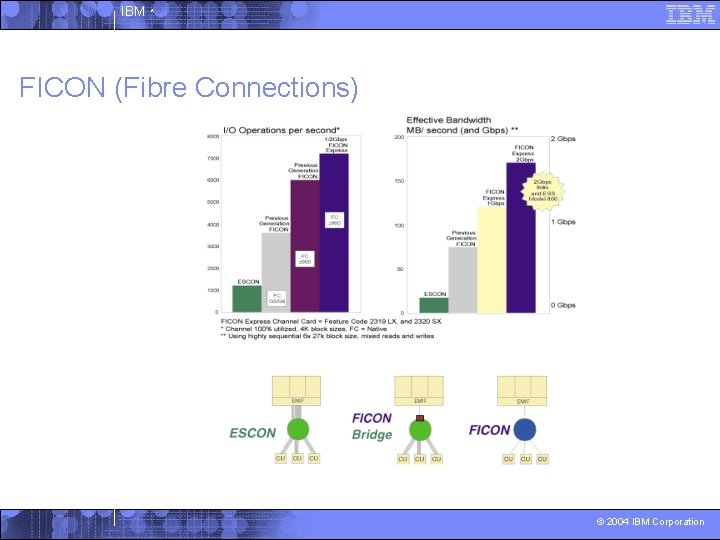
IBM ^ FICON (Fibre Connections) © 2004 IBM Corporation
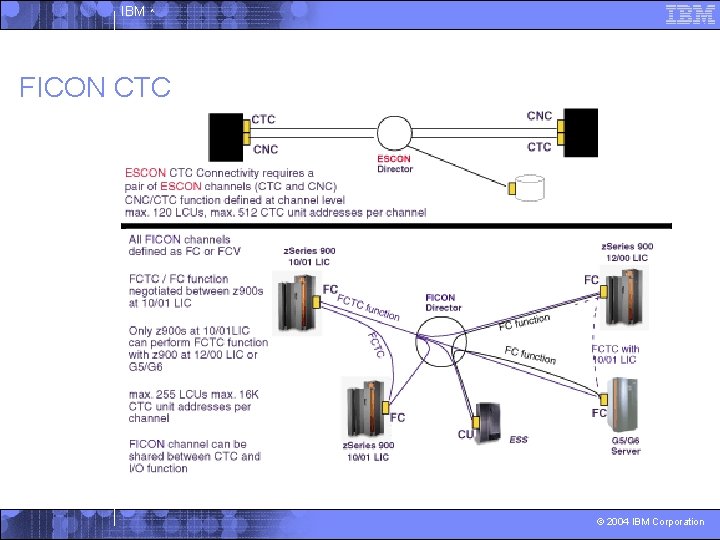
IBM ^ FICON CTC © 2004 IBM Corporation
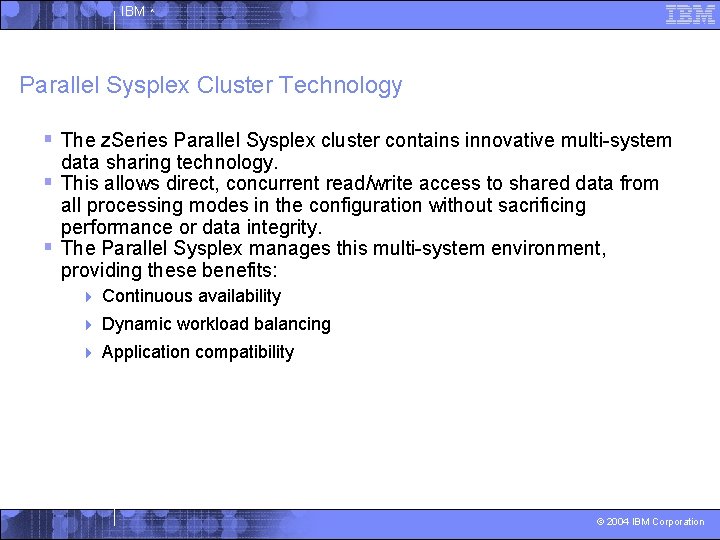
IBM ^ Parallel Sysplex Cluster Technology § The z. Series Parallel Sysplex cluster contains innovative multi-system data sharing technology. § This allows direct, concurrent read/write access to shared data from all processing modes in the configuration without sacrificing performance or data integrity. § The Parallel Sysplex manages this multi-system environment, providing these benefits: 4 Continuous availability 4 Dynamic workload balancing 4 Application compatibility © 2004 IBM Corporation
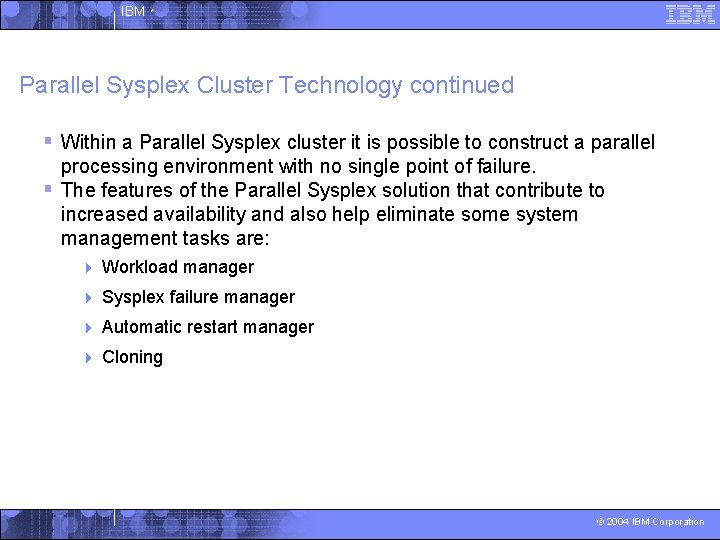
IBM ^ Parallel Sysplex Cluster Technology continued § Within a Parallel Sysplex cluster it is possible to construct a parallel processing environment with no single point of failure. § The features of the Parallel Sysplex solution that contribute to increased availability and also help eliminate some system management tasks are: 4 Workload manager 4 Sysplex failure manager 4 Automatic restart manager 4 Cloning © 2004 IBM Corporation
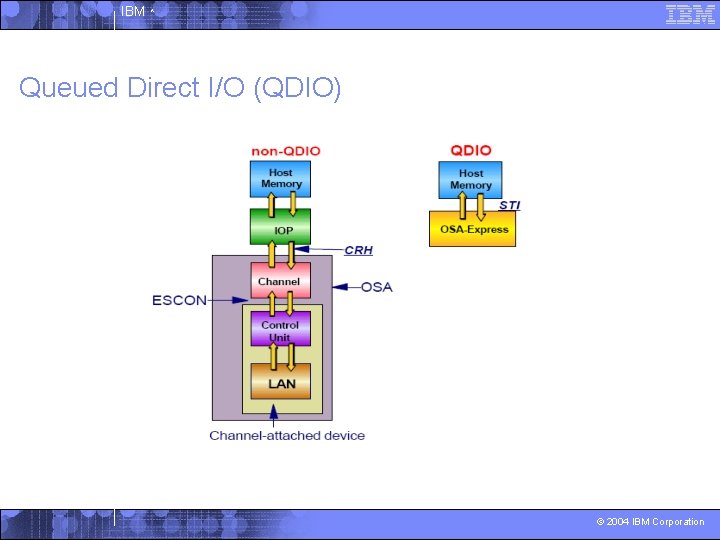
IBM ^ Queued Direct I/O (QDIO) © 2004 IBM Corporation
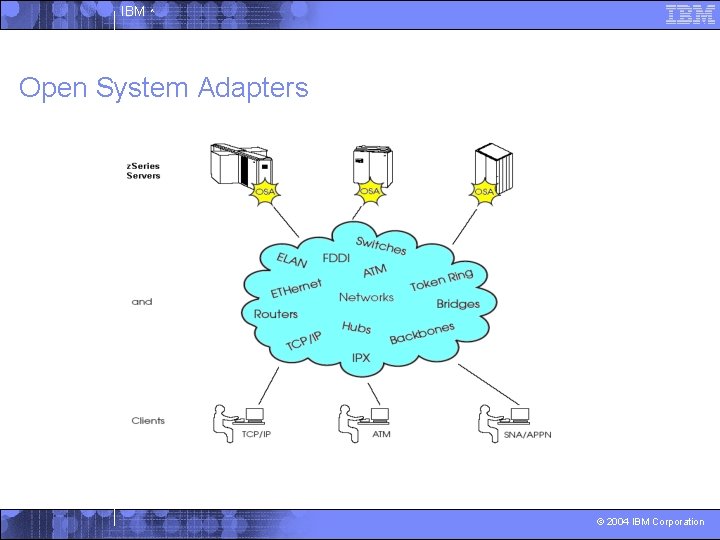
IBM ^ Open System Adapters © 2004 IBM Corporation
IBM ^ OSA-2 § An integrated hardware feature that allows a z. Series 900 to provide industry-standard connectivity directly to clients on local area networks. § The clients on the attached LAN can use the TCP/IP or the SNA/APPN protocol, or both. § Ethernet, Fast Ethernet, and ATM LAN attachment to the z 900 is supported by OSA-Express, but not by OSA-2. © 2004 IBM Corporation
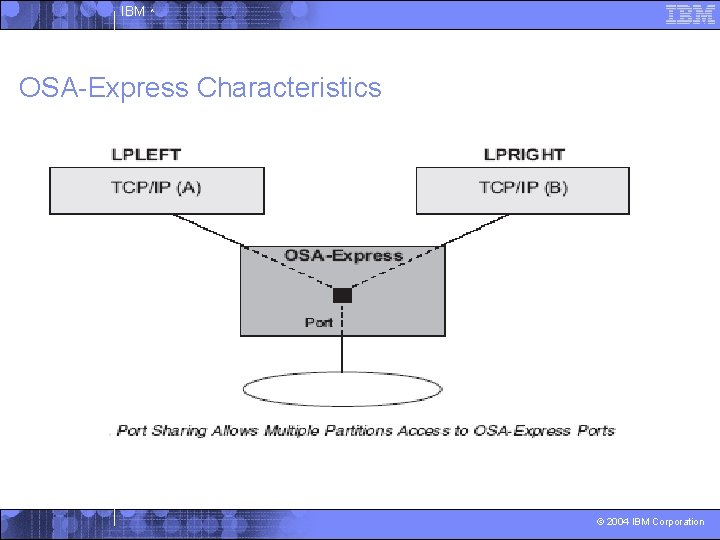
IBM ^ OSA-Express Characteristics © 2004 IBM Corporation
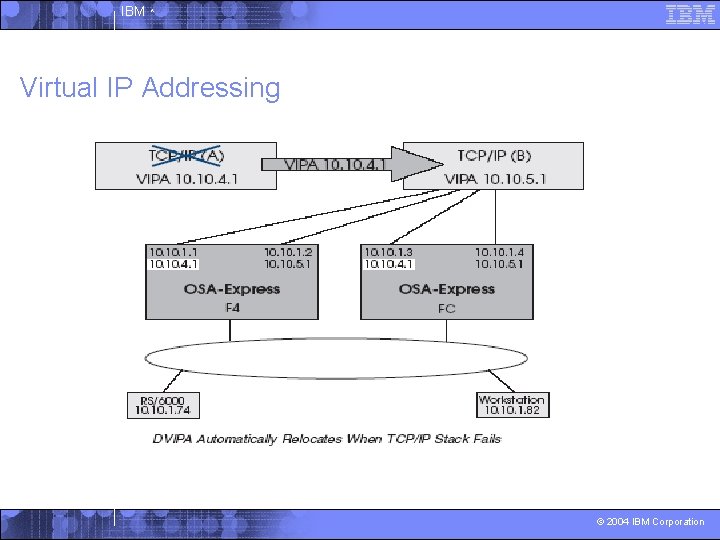
IBM ^ Virtual IP Addressing © 2004 IBM Corporation
IBM ^ What Are Hiper. Sockets and What Benefits Do They Provide? § They provide very fast TCP/IP communications between servers running in different LPARs on a z. Series CEC. § Hiper. Sockets uses internal Queued Input/Output (i. QDIO) at memory speeds to pass traffic between the virtual servers. § Important aspects of Hiper. Sockets include: 4 They can be used to communicate among consolidated servers in a single processor 4 They can be customized to accommodate varying traffic sizes 4 Since there is no server-to-service traffic outside the z. Series CEC, they provide a much higher level of network availability, security, simplicity, performance, and cost effectiveness © 2004 IBM Corporation
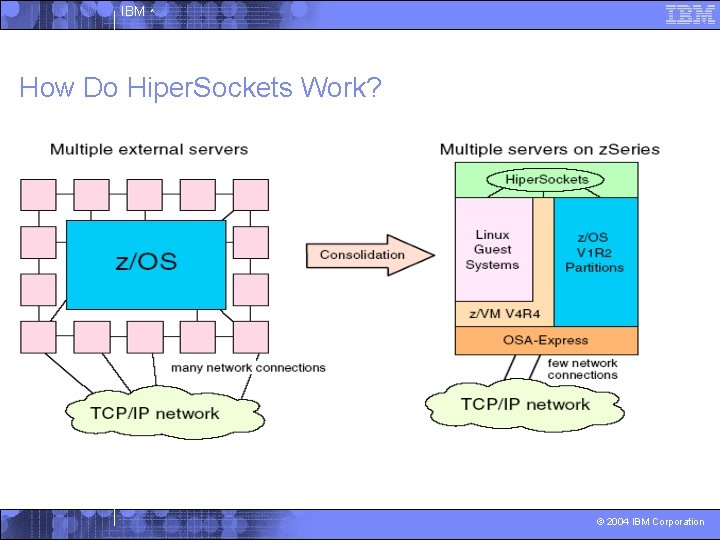
IBM ^ How Do Hiper. Sockets Work? © 2004 IBM Corporation
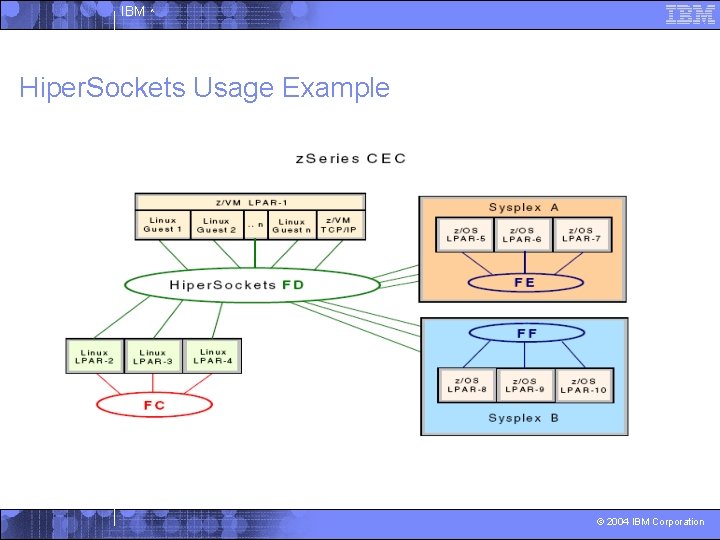
IBM ^ Hiper. Sockets Usage Example © 2004 IBM Corporation
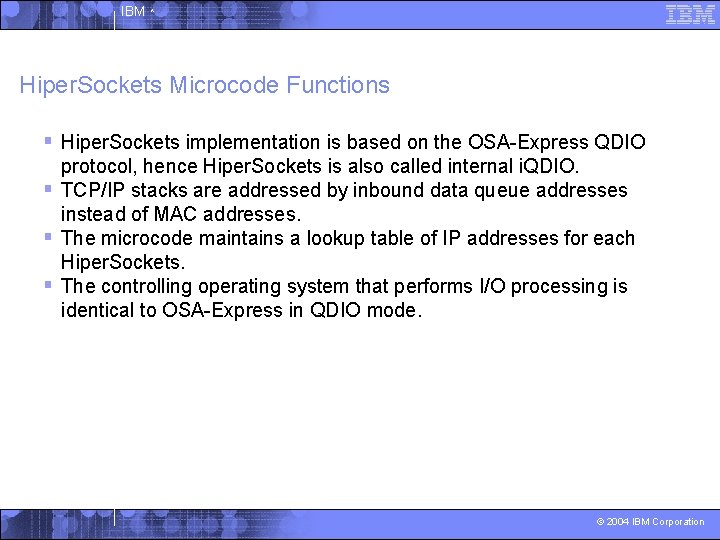
IBM ^ Hiper. Sockets Microcode Functions § Hiper. Sockets implementation is based on the OSA-Express QDIO protocol, hence Hiper. Sockets is also called internal i. QDIO. § TCP/IP stacks are addressed by inbound data queue addresses instead of MAC addresses. § The microcode maintains a lookup table of IP addresses for each Hiper. Sockets. § The controlling operating system that performs I/O processing is identical to OSA-Express in QDIO mode. © 2004 IBM Corporation
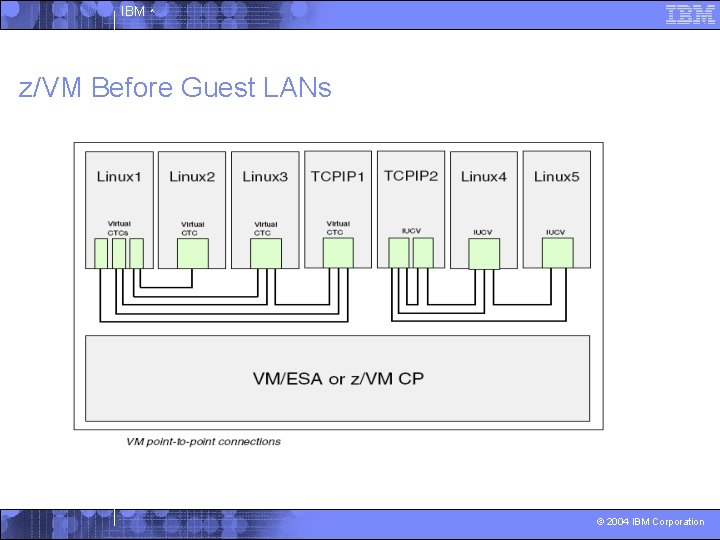
IBM ^ z/VM Before Guest LANs © 2004 IBM Corporation
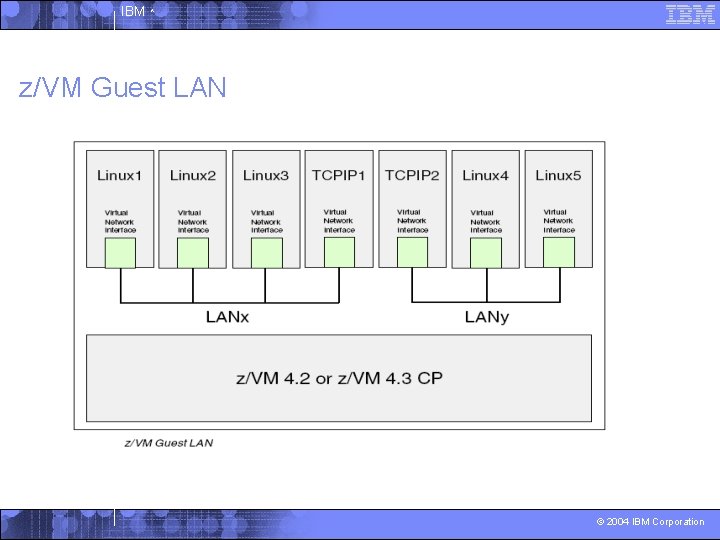
IBM ^ z/VM Guest LAN © 2004 IBM Corporation
IBM ^ z/VM’s Virtual Switch § z. /VM Virtual Switch is an extension of the Guest LAN simulated networking function. § VSWITCH operates almost exactly the same as a z/VM 4. 3 QDIO Guest LAN, with two important exceptions: 4 Direct external network access via OSA Express 4 IEEE 802. 1 Q VLAN Support © 2004 IBM Corporation
IBM ^ Network Consolidation Using the Virtual Switch § A Virtual Switch is capable of bridging a z/VM Guest LAN to an associated real LAN connected by an OSA-Express adapter. § Virtual Switch operates as part of the z/VM CP and is not a separate guest machine. § Virtual Switch support is also used to manage the z/VM VLAN environment. © 2004 IBM Corporation
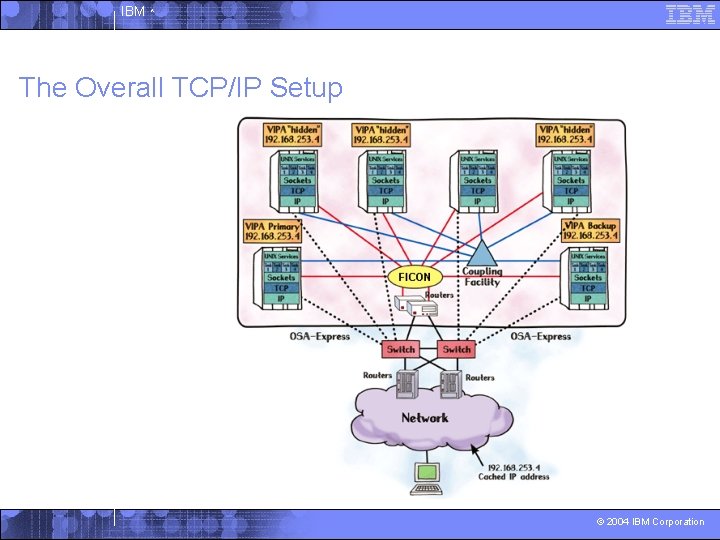
IBM ^ The Overall TCP/IP Setup © 2004 IBM Corporation
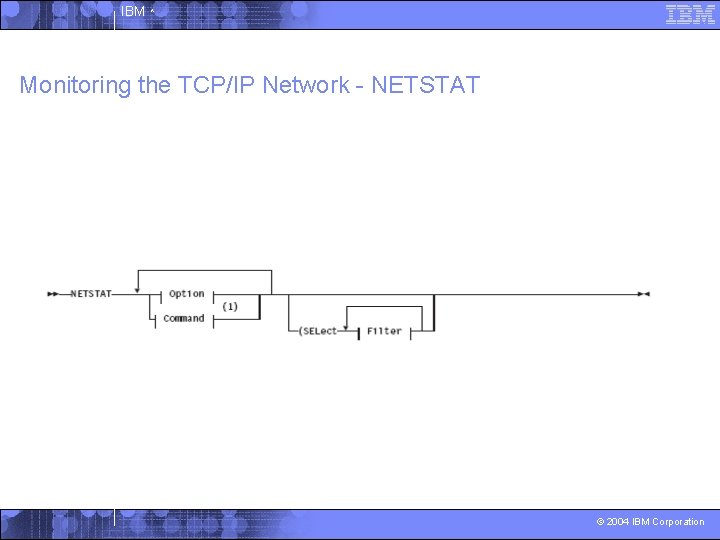
IBM ^ Monitoring the TCP/IP Network - NETSTAT © 2004 IBM Corporation
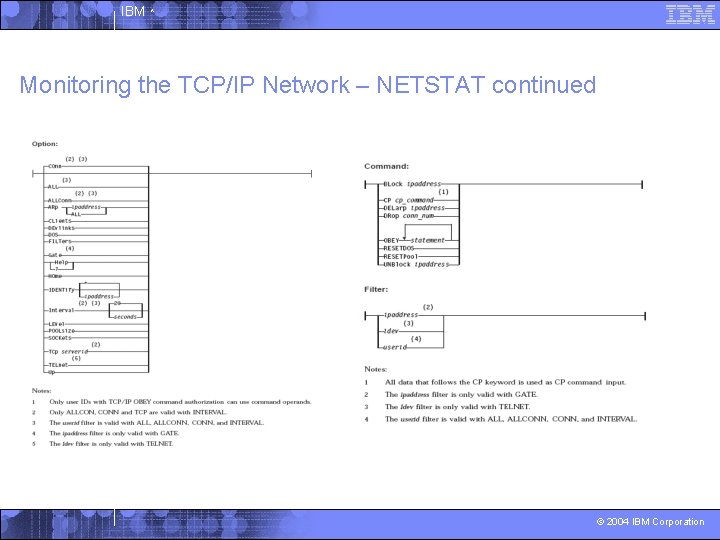
IBM ^ Monitoring the TCP/IP Network – NETSTAT continued © 2004 IBM Corporation
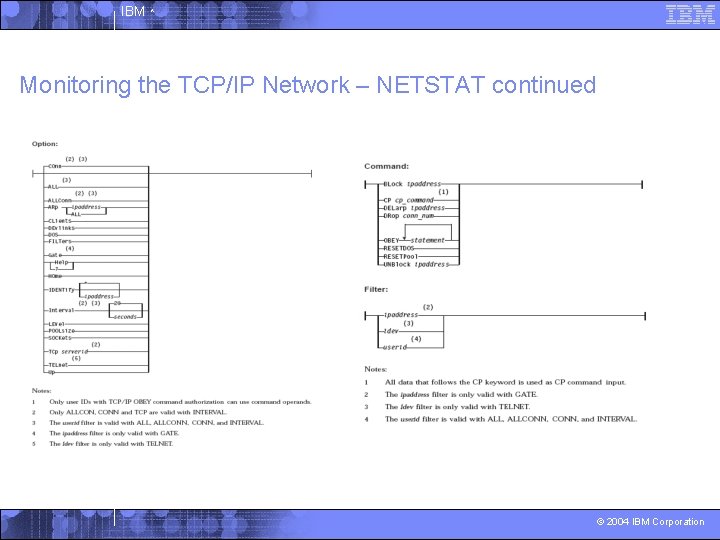
IBM ^ Monitoring the TCP/IP Network – NETSTAT continued © 2004 IBM Corporation
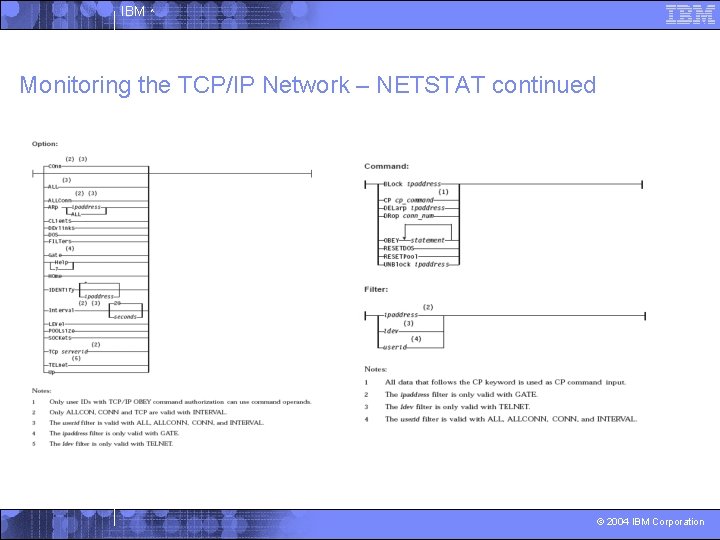
IBM ^ Monitoring the TCP/IP Network – NETSTAT continued © 2004 IBM Corporation
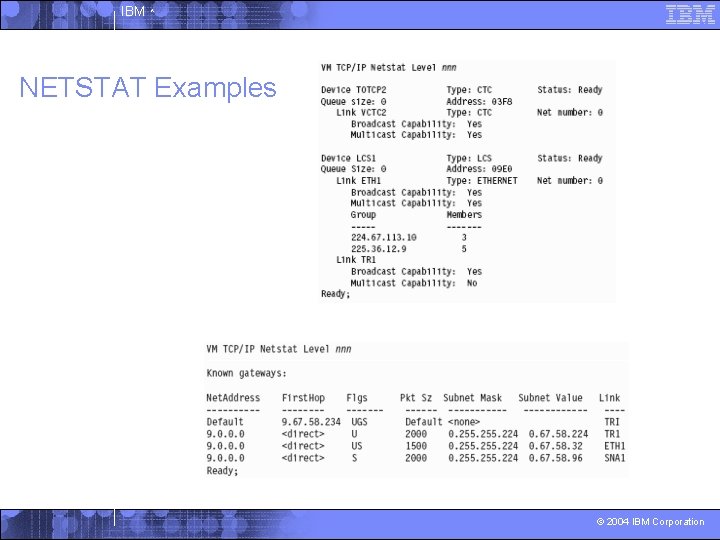
IBM ^ NETSTAT Examples © 2004 IBM Corporation
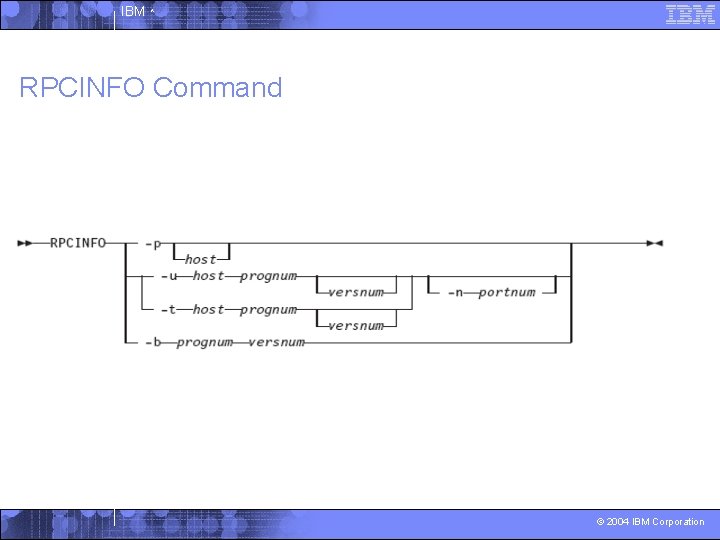
IBM ^ RPCINFO Command © 2004 IBM Corporation
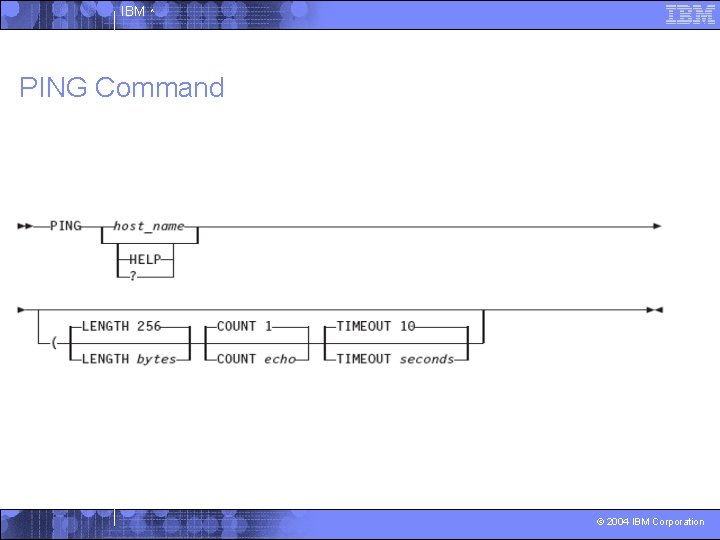
IBM ^ PING Command © 2004 IBM Corporation
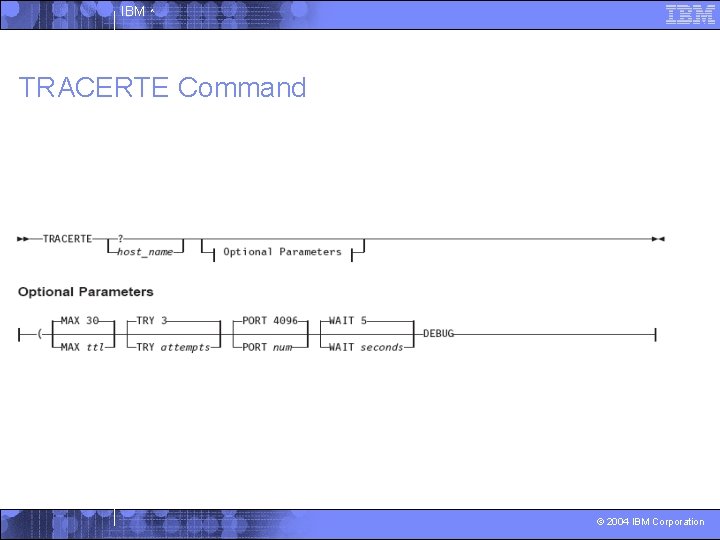
IBM ^ TRACERTE Command © 2004 IBM Corporation
IBM ^ TRACERTE Command Usage Notes § To use the TRACERTE command, you must be a privileged TCP/IP user. § The range of port numbers that the TRACERTE command uses is normally invalid; however you can change the starting port number for this range if the target host is using a nonstandard UPD port. § The TRACERTE function will give unpredictable results if the TCP/IP stack is configured to use equal-cost multi-path support. © 2004 IBM Corporation
IBM ^ Conclusion § Important topics discussed in this module: § Important devices discussed in this module: 4 TCP/IP Protocols and Functions 4 ESCON – Link Protocols – Networking Protocols – Transport Protocols – Application Protocols 4 Routing capabilities 4 Internet Addressing – Networking address format – Broadcast address format – Multicast address format – Subnetwork address format 4 FICON and FICON CTC 4 Parallel Sysplex 4 Queued Direct I/O 4 OSA-Express and OSA-2 4 Virtual IP Addressing 4 Hiper. Sockets 4 Guest LANs § Commands that are used to monitor the networking devices are: 4 NETSTAT 4 RPCINFO 4 PING 4 TRACERTE © 2004 IBM Corporation
IBM ^ Glossary Channel-to-channel Adapter (CTCA) – an adapter that cross-connect a pair of channels between systems to allow for point-to-point communications between two systems. Domain Name Server (DNS) -- the distributed data system (directory) used to map domain names to IP addresses. ESCON – Enterprise System Connection; a set of IBM products and services that provide a dynamically connected environment within an enterprise based upon fiber connections. FICON – Fiber Connectivity; a high-speed I/O interface for mainframe computer connections to storage devices. This new architecture is about eight times as efficient as ESCON. File Transfer Protocol (FTP): -- generally used for file transfers from TCP/IP systems, it originated on the internet. © 2004 IBM Corporation
IBM ^ Glossary Network File System (NFS): – a set of UNIX protocols for file sharing across a LAN; built on top of Ethernet and TCP/IP. Has became a standard in the UNIX environment. NFS Client – New to z/VM, NFS Client is integrated into both CMS and the priced, optional TCP/IP feature of z/VM. Socket – an end point provided by the transport service of a network for communications between processes or application programs. Secure Socket Layer (SSL): – a security protocol that provides communication privacy; SSL enables client/server applications to communicate in a way that is designed to prevent eavesdropping, tampering, and message forgery. Virtual Private Network (VPN): – a network comprised of one or more secure IP tunnels connecting two or more networks. © 2004 IBM Corporation
IBM ^ References § IBM eserver z. Series 900: OSA-Express Overview. October 2001. § TCP/IP Solutions for VM/ESA. 1999. § White, Bill, Rama Ayyar, and Velibor Uskokovic. IBM Redbook: z. Series Hiper. Sockets. May 2002 © 2004 IBM Corporation
- Slides: 57