IBM XForce Insights from the 2016 IBM XForce
IBM X-Force Insights from the 2016 IBM X-Force Threat Intelligence Report Chris Poulin Research Strategist, X-Force IBM Security April 2016 © 2016 IBM Corporation
is the foundation for advanced security and threat research across the IBM Security Framework. © 2016 IBM Corporation 2
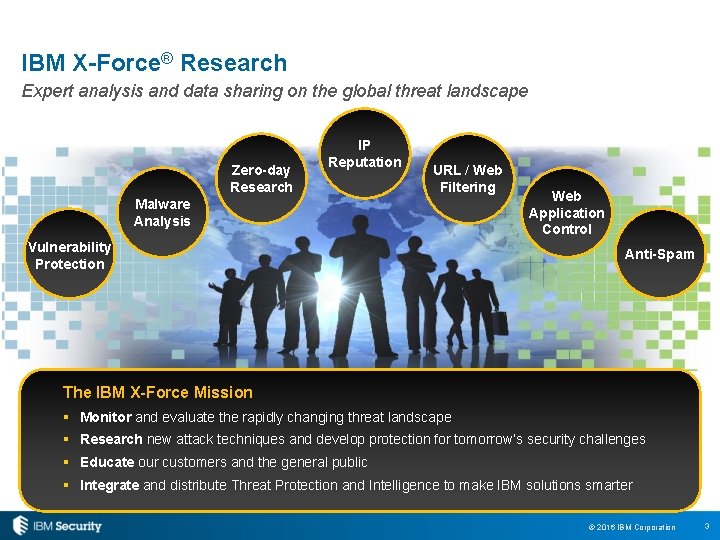
IBM X-Force® Research Expert analysis and data sharing on the global threat landscape Zero-day Research IP Reputation URL / Web Filtering Malware Analysis Vulnerability Protection Web Application Control Anti-Spam The IBM X-Force Mission § Monitor and evaluate the rapidly changing threat landscape § Research new attack techniques and develop protection for tomorrow’s security challenges § Educate our customers and the general public § Integrate and distribute Threat Protection and Intelligence to make IBM solutions smarter © 2016 IBM Corporation 3
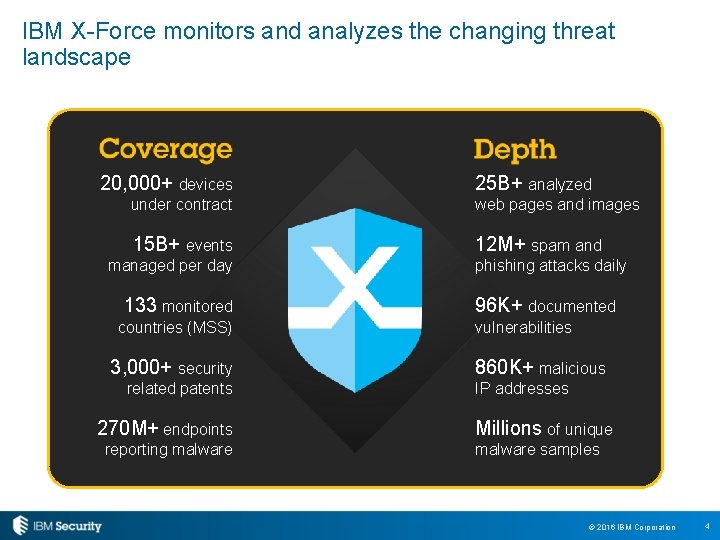
IBM X-Force monitors and analyzes the changing threat landscape 20, 000+ devices 25 B+ analyzed under contract web pages and images 15 B+ events 12 M+ spam and managed per day 133 monitored countries (MSS) 3, 000+ security related patents 270 M+ endpoints reporting malware phishing attacks daily 96 K+ documented vulnerabilities 860 K+ malicious IP addresses Millions of unique malware samples © 2016 IBM Corporation 4

Key Trends from 2015 5 © 2016 IBM Corporation 5
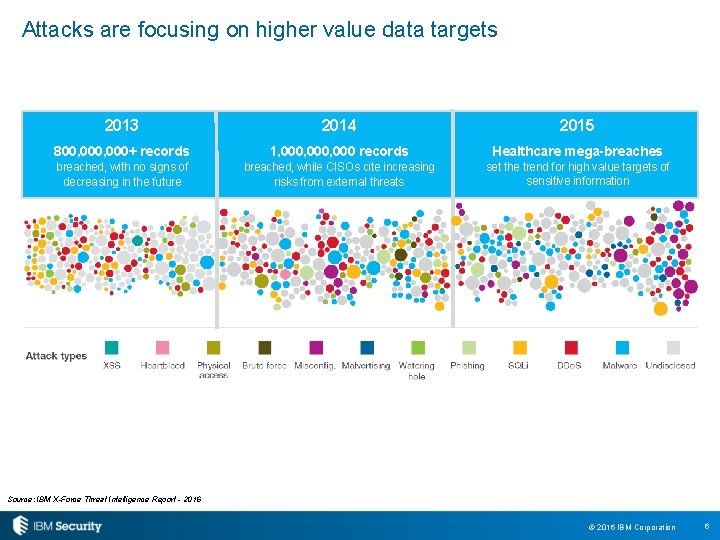
Attacks are focusing on higher value data targets 2013 2014 2015 800, 000+ records 1, 000, 000 records Healthcare mega-breaches breached, with no signs of decreasing in the future breached, while CISOs cite increasing risks from external threats set the trend for high value targets of sensitive information Source: IBM X-Force Threat Intelligence Report - 2016 © 2016 IBM Corporation 6
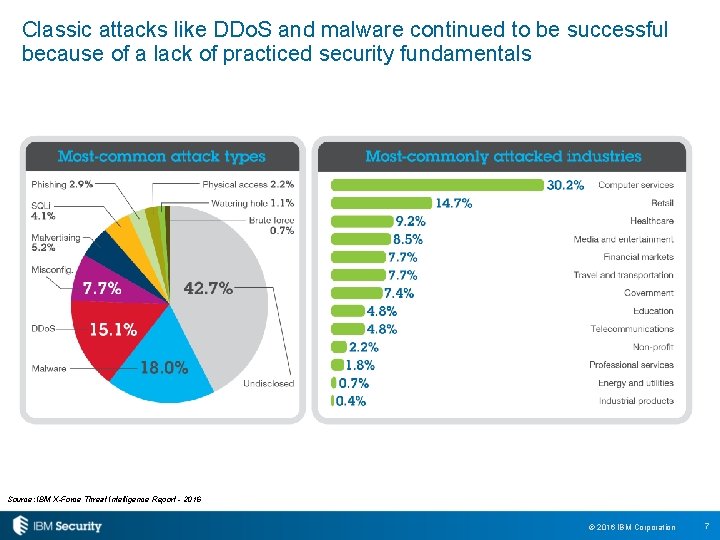
Classic attacks like DDo. S and malware continued to be successful because of a lack of practiced security fundamentals Source: IBM X-Force Threat Intelligence Report - 2016 © 2016 IBM Corporation 7
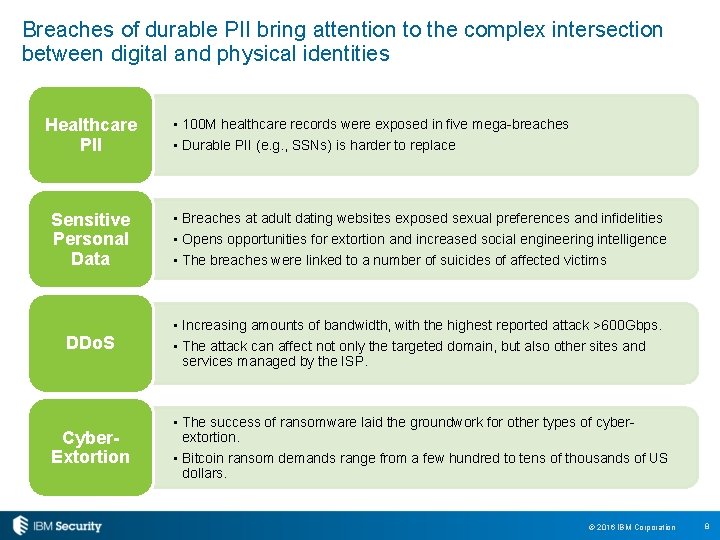
Breaches of durable PII bring attention to the complex intersection between digital and physical identities Healthcare PII • 100 M healthcare records were exposed in five mega-breaches • Durable PII (e. g. , SSNs) is harder to replace Sensitive Personal Data • Breaches at adult dating websites exposed sexual preferences and infidelities • Opens opportunities for extortion and increased social engineering intelligence • The breaches were linked to a number of suicides of affected victims DDo. S • Increasing amounts of bandwidth, with the highest reported attack >600 Gbps. • The attack can affect not only the targeted domain, but also other sites and services managed by the ISP. Cyber. Extortion • The success of ransomware laid the groundwork for other types of cyberextortion. • Bitcoin ransom demands range from a few hundred to tens of thousands of US dollars. © 2016 IBM Corporation 8

A little something we call OPSEC Accounts Identity Healthcare: many, many Tracking United & American Ashley Madison OPM, IRS Adult Friend Finder background info, fingerprints Starwood, Hyatt, Trump Io. T, Shodan © 2016 IBM Corporation 9
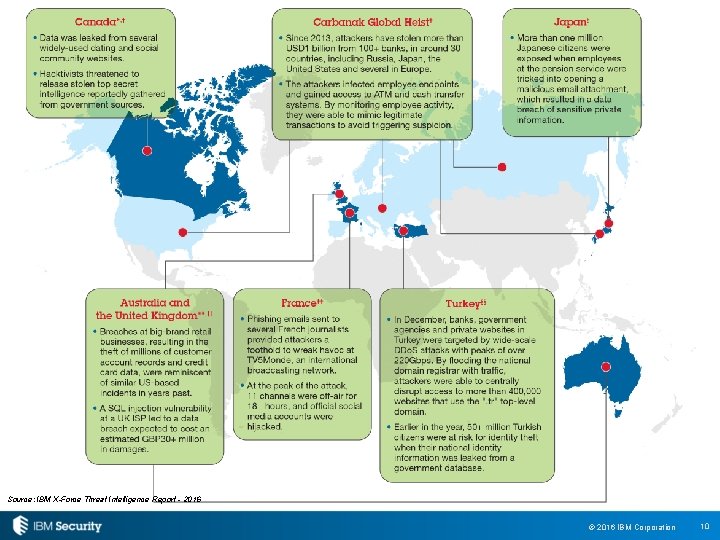
Source: IBM X-Force Threat Intelligence Report - 2016 © 2016 IBM Corporation 10
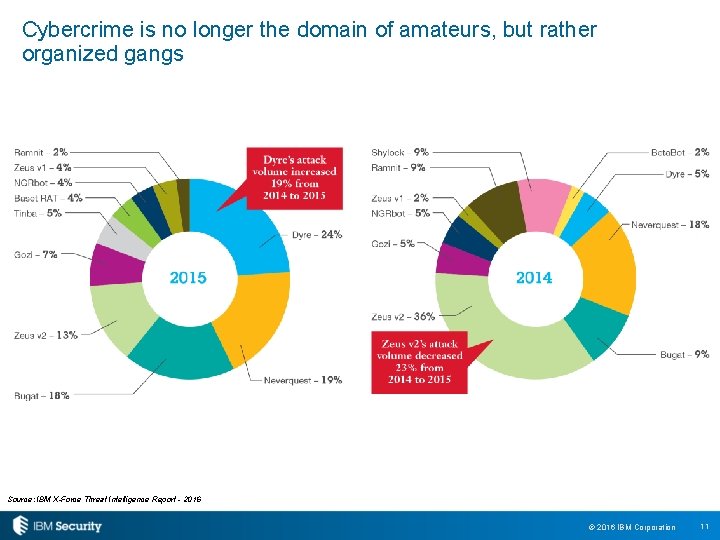
Cybercrime is no longer the domain of amateurs, but rather organized gangs Source: IBM X-Force Threat Intelligence Report - 2016 © 2016 IBM Corporation 11
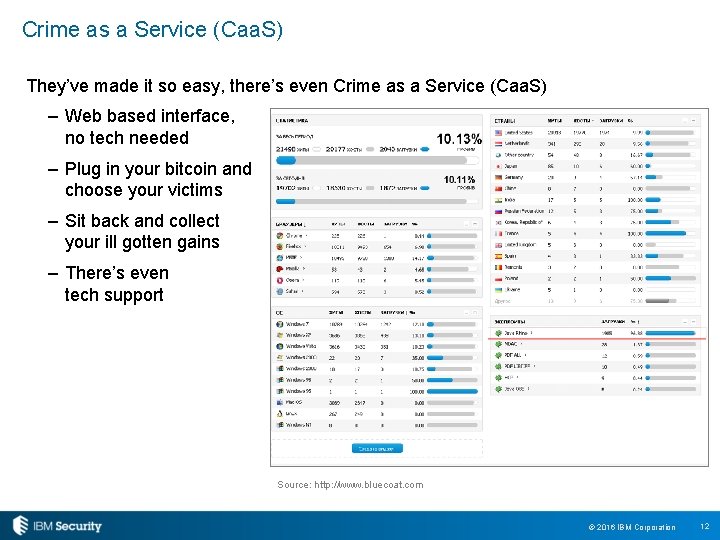
Crime as a Service (Caa. S) They’ve made it so easy, there’s even Crime as a Service (Caa. S) – Web based interface, no tech needed – Plug in your bitcoin and choose your victims – Sit back and collect your ill gotten gains – There’s even tech support Source: http: //www. bluecoat. com © 2016 IBM Corporation 12
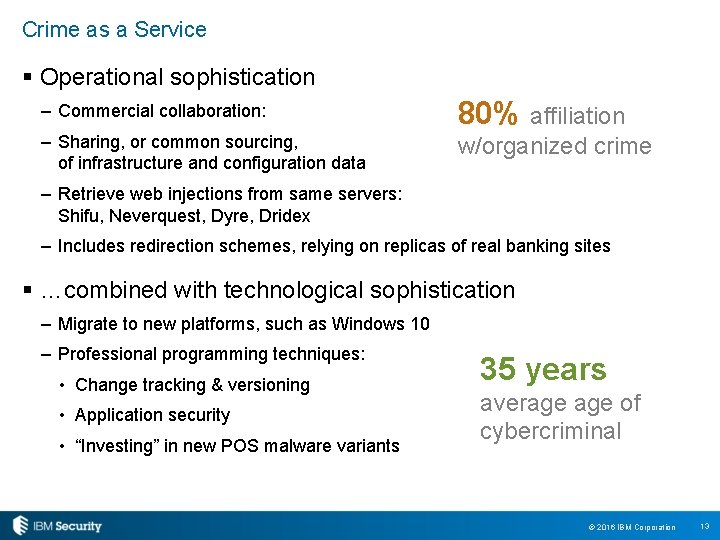
Crime as a Service § Operational sophistication – Commercial collaboration: 80% affiliation – Sharing, or common sourcing, of infrastructure and configuration data w/organized crime – Retrieve web injections from same servers: Shifu, Neverquest, Dyre, Dridex – Includes redirection schemes, relying on replicas of real banking sites § …combined with technological sophistication – Migrate to new platforms, such as Windows 10 – Professional programming techniques: • Change tracking & versioning • Application security • “Investing” in new POS malware variants 35 years average of cybercriminal © 2016 IBM Corporation 13
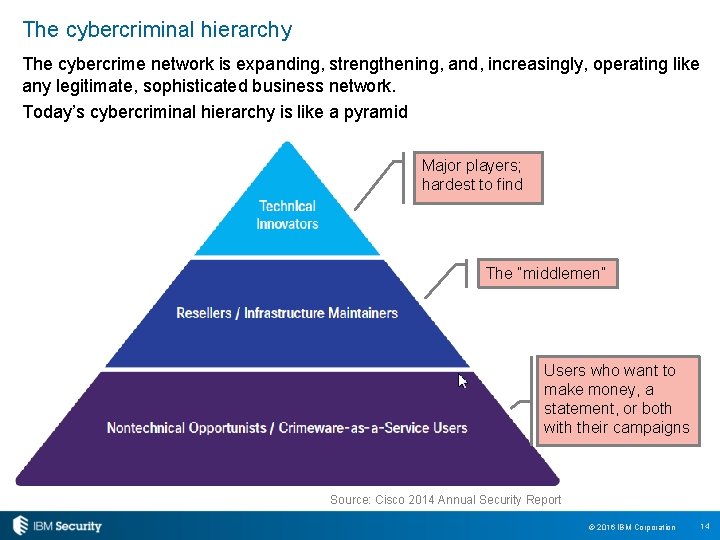
The cybercriminal hierarchy The cybercrime network is expanding, strengthening, and, increasingly, operating like any legitimate, sophisticated business network. Today’s cybercriminal hierarchy is like a pyramid Major players; hardest to find The “middlemen” Users who want to make money, a statement, or both with their campaigns Source: Cisco 2014 Annual Security Report © 2016 IBM Corporation 14
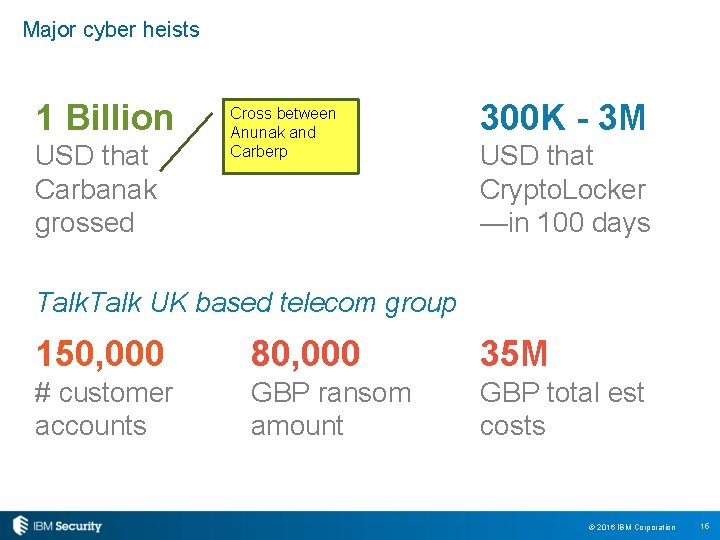
Major cyber heists 1 Billion USD that Carbanak grossed Cross between Anunak and Carberp 300 K - 3 M USD that Crypto. Locker —in 100 days Talk UK based telecom group 150, 000 80, 000 35 M # customer accounts GBP ransom amount GBP total est costs © 2016 IBM Corporation 15
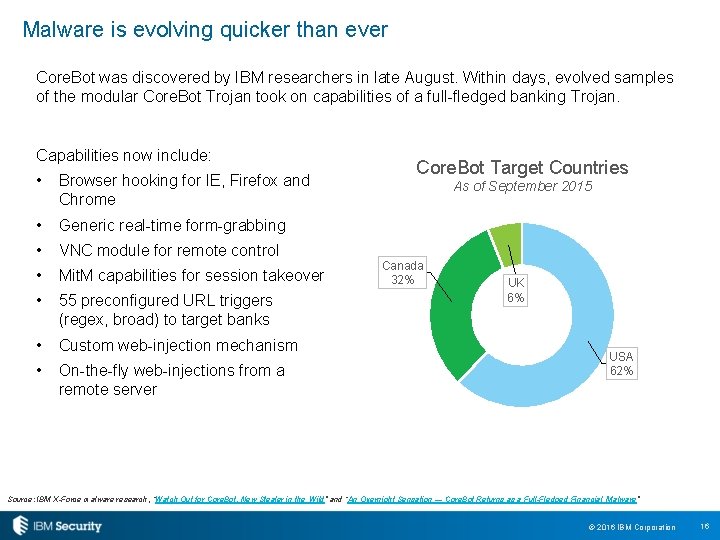
Malware is evolving quicker than ever Core. Bot was discovered by IBM researchers in late August. Within days, evolved samples of the modular Core. Bot Trojan took on capabilities of a full-fledged banking Trojan. Capabilities now include: • Browser hooking for IE, Firefox and Chrome • Generic real-time form-grabbing • VNC module for remote control • Mit. M capabilities for session takeover • 55 preconfigured URL triggers (regex, broad) to target banks • Custom web-injection mechanism • On-the-fly web-injections from a remote server Core. Bot Target Countries As of September 2015 Canada 32% UK 6% USA 62% Source: IBM X-Force malware research, “Watch Out for Core. Bot, New Stealer in the Wild” and “An Overnight Sensation — Core. Bot Returns as a Full-Fledged Financial Malware” © 2016 IBM Corporation 16
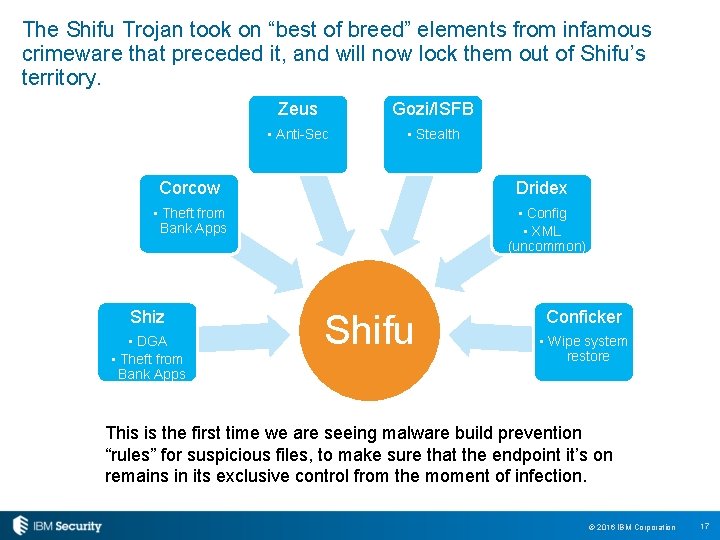
The Shifu Trojan took on “best of breed” elements from infamous crimeware that preceded it, and will now lock them out of Shifu’s territory. Zeus Gozi/ISFB • Anti-Sec • Stealth Corcow Dridex • Theft from Bank Apps Shiz • DGA • Theft from Bank Apps • Config • XML (uncommon) Shifu Conficker • Wipe system restore This is the first time we are seeing malware build prevention “rules” for suspicious files, to make sure that the endpoint it’s on remains in its exclusive control from the moment of infection. © 2016 IBM Corporation 17
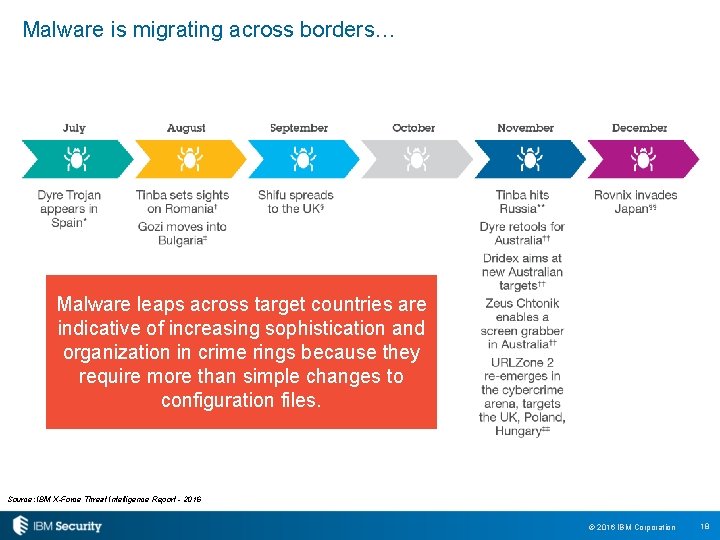
Malware is migrating across borders… Malware leaps across target countries are indicative of increasing sophistication and organization in crime rings because they require more than simple changes to configuration files. Source: IBM X-Force Threat Intelligence Report - 2016 © 2016 IBM Corporation 18
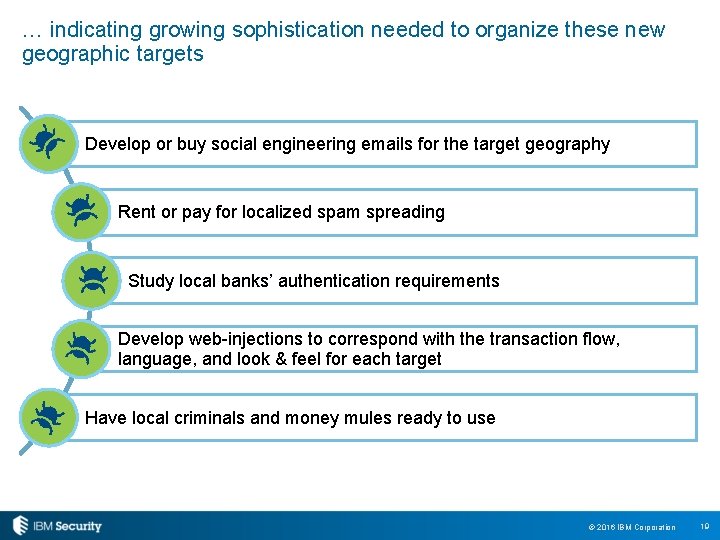
… indicating growing sophistication needed to organize these new geographic targets Develop or buy social engineering emails for the target geography Rent or pay for localized spam spreading Study local banks’ authentication requirements Develop web-injections to correspond with the transaction flow, language, and look & feel for each target Have local criminals and money mules ready to use © 2016 IBM Corporation 19
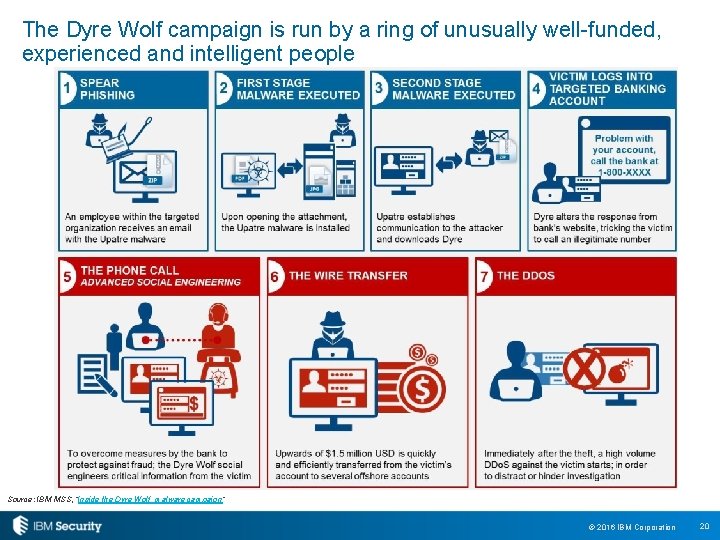
The Dyre Wolf campaign is run by a ring of unusually well-funded, experienced and intelligent people Source: IBM MSS, “Inside the Dyre Wolf malware campaign“ © 2016 IBM Corporation 20
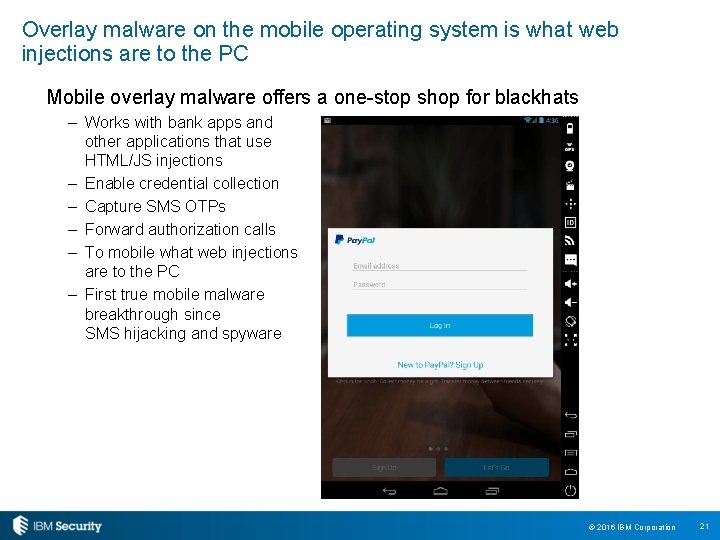
Overlay malware on the mobile operating system is what web injections are to the PC Mobile overlay malware offers a one-stop shop for blackhats – Works with bank apps and other applications that use HTML/JS injections – Enable credential collection – Capture SMS OTPs – Forward authorization calls – To mobile what web injections are to the PC – First true mobile malware breakthrough since SMS hijacking and spyware © 2016 IBM Corporation 21
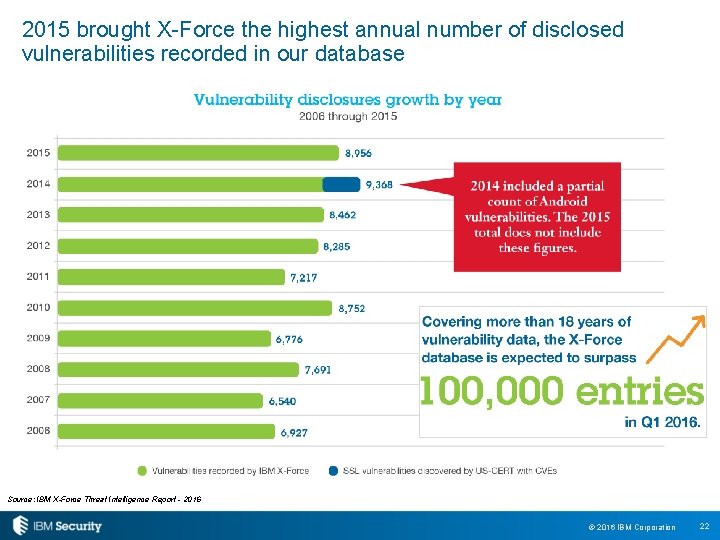
2015 brought X-Force the highest annual number of disclosed vulnerabilities recorded in our database Source: IBM X-Force Threat Intelligence Report - 2016 © 2016 IBM Corporation 22
Mobile and the Internet of Things is creating a Big Data risk ▶ Massive volumes, arriving at high velocity ▶ Hard to separate sensitive from not ▶ Hard to determine and maintain integrity ▶ M 2 M means access control is being challenged ▶ Dev. Ops with continuous delivery is exacerbating the problem © 2016 IBM Corporation 23
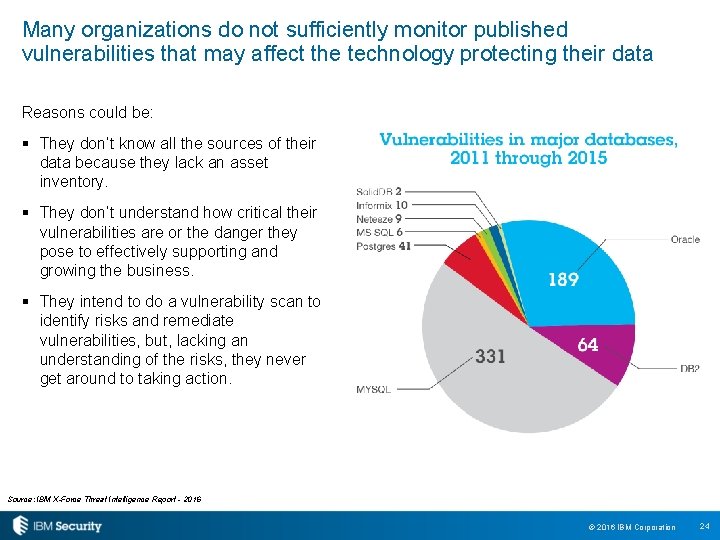
Many organizations do not sufficiently monitor published vulnerabilities that may affect the technology protecting their data Reasons could be: § They don’t know all the sources of their data because they lack an asset inventory. § They don’t understand how critical their vulnerabilities are or the danger they pose to effectively supporting and growing the business. § They intend to do a vulnerability scan to identify risks and remediate vulnerabilities, but, lacking an understanding of the risks, they never get around to taking action. Source: IBM X-Force Threat Intelligence Report - 2016 © 2016 IBM Corporation 24
Many of the incidents we’ve seen could be avoided with a focus on security basics Maintain a current and accurate asset inventory. Keep up with threat intelligence. Have a patching solution that covers your entire infrastructure. Maintain an identity governance practice to enforce and audit access control. Instrument your environment with effective detection. Create and practice a broad incident response plan. © 2016 IBM Corporation 25
Learn more about IBM X-Force No. 1 enterprise security software vendor in total revenue 25 industry analyst reports rank IBM Security as a LEADER 130+ 12 K+ 90% countries where IBM delivers managed security services clients protected including… of the Fortune 100 companies Join IBM X-Force Exchange xforce. ibmcloud. com Visit our web page ibm. com/security/xforce Watch our videos IBM Security You. Tube Channel View upcoming webinars & blogs Security. Intelligence. com Follow us on Twitter @ibmsecurity © 2016 IBM Corporation 26

Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to improper access from within and outside your enterprise. Improper access can result in information being altered, destroyed, misappropriated or misused or can result in damage to or misuse of your systems, including for use in attacks on others. No IT system or product should be considered completely secure and no single product, service or security measure can be completely effective in preventing improper use or access. IBM systems, products and services are designed to be part of a lawful, comprehensive security approach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM DOES NOT WARRANT THAT ANY SYSTEMS, PRODUCTS OR SERVICES ARE IMMUNE FROM, OR WILL MAKE YOUR ENTERPRISE IMMUNE FROM, THE MALICIOUS OR ILLEGAL CONDUCT OF ANY PARTY. THANK YOU www. ibm. com/security © Copyright IBM Corporation 2016. All rights reserved. The information contained in these materials is provided for informational purposes only, and is provided AS IS without warranty of any kind, express or implied. IBM shall not be responsible for any damages arising out of the use of, or otherwise related to, these materials. Nothing contained in these materials is intended to, nor shall have the effect of, creating any warranties or representations from IBM or its suppliers or licensors, or altering the terms and conditions of the applicable license agreement governing the use of IBM software. References in these materials to IBM products, programs, or services do not imply that they will be available in all countries in which IBM operates. Product release dates and / or capabilities referenced in these materials may change at any time at IBM’s sole discretion based on market opportunities or other factors, and are not intended to be a commitment to future product or feature availability in any way. IBM, the IBM logo, and other IBM products and services are trademarks of the International Business Machines Corporation, in the United States, other countries or both. Other company, product, or service names may be trademarks or service marks of others.
- Slides: 27