IBM XForce Exchange COLLABORATIVE THREAT INTELLIGENCE AND ACTIONABLE
IBM X-Force Exchange COLLABORATIVE THREAT INTELLIGENCE AND ACTIONABLE INTEGRATION Adrian Aldea IBM Security Senior Consultant CEE Nov 2017, Chisinau
65% of enterprise firms use external threat intelligence to enhance their security decision making 1 Security teams often lack critical support to make the most of these resources. Analysts can’t separate the signal from the noise 1 Source: ESG Global 2 IBM Security Data is gathered from untrusted sources It takes too long to make information actionable
IBM X-Force Exchange is a threat intelligence sharing platform designed to help your security teams research, collaborate, and act. xforce. ibmcloud. com 3 IBM Security
3 use cases: collaborative threat intelligence 4 IBM Security Research: Enhance security insights with curated content Collaborate: Engage with peers to validate threats and develop response plans Act: Strengthen security solutions with threat intelligence delivered through open standards
RESEARCH Investigate security incidents with curated content COLLABORATE Validate threats and develop response plans with peers ACT Integrate threat intelligence with security solutions through open standards 5 IBM Security
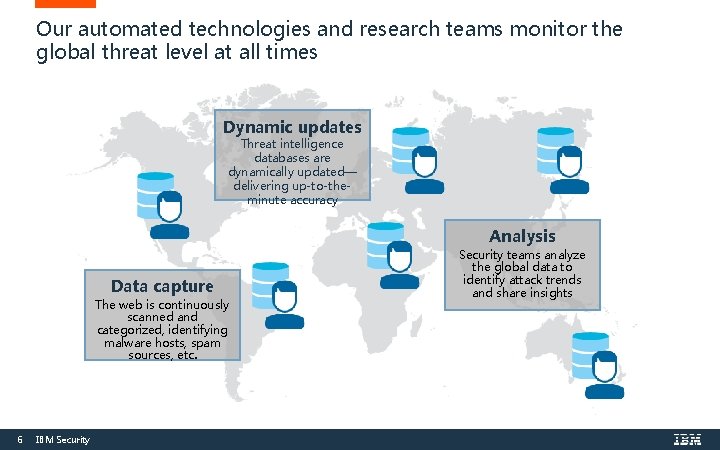
Our automated technologies and research teams monitor the global threat level at all times Dynamic updates Threat intelligence databases are dynamically updated— delivering up-to-theminute accuracy Analysis Data capture The web is continuously scanned and categorized, identifying malware hosts, spam sources, etc. 6 IBM Security teams analyze the global data to identify attack trends and share insights
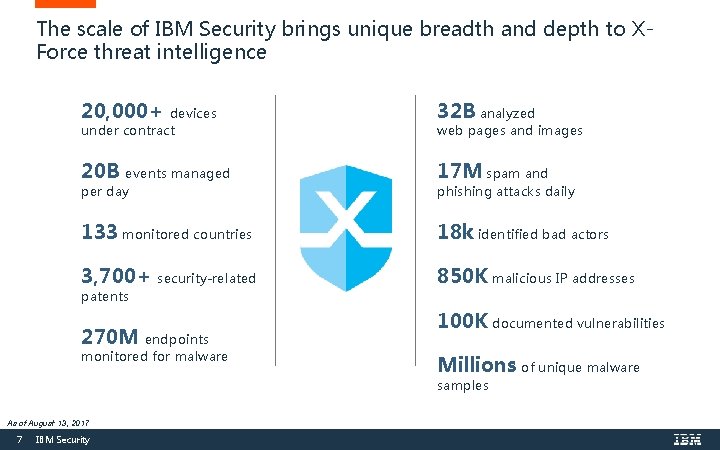
The scale of IBM Security brings unique breadth and depth to XForce threat intelligence 20, 000+ 32 B analyzed 20 B events managed 17 M spam and 133 monitored countries 18 k identified bad actors 3, 700+ 850 K malicious IP addresses devices under contract per day security-related patents 270 M endpoints monitored for malware web pages and images phishing attacks daily 100 K documented vulnerabilities Millions of unique malware samples As of August 13, 2017 7 IBM Security
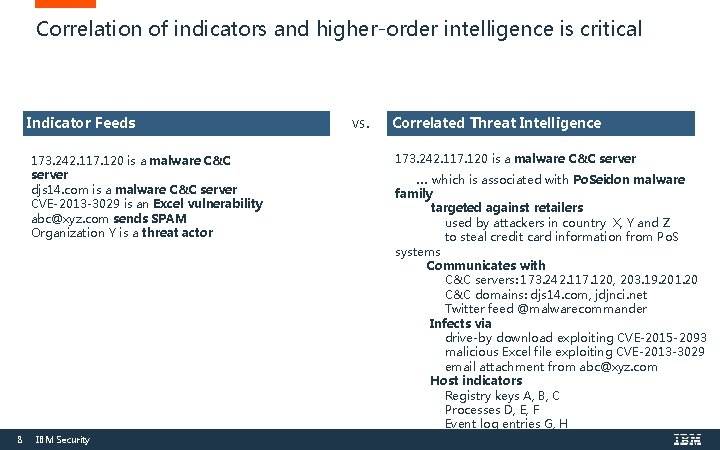
Correlation of indicators and higher-order intelligence is critical Indicator Feeds 173. 242. 117. 120 is a malware C&C server djs 14. com is a malware C&C server CVE-2013 -3029 is an Excel vulnerability abc@xyz. com sends SPAM Organization Y is a threat actor 8 IBM Security vs. Correlated Threat Intelligence 173. 242. 117. 120 is a malware C&C server … which is associated with Po. Seidon malware family targeted against retailers used by attackers in country X, Y and Z to steal credit card information from Po. S systems Communicates with C&C servers: 173. 242. 117. 120, 203. 19. 201. 20 C&C domains: djs 14. com, jdjnci. net Twitter feed @malwarecommander Infects via drive-by download exploiting CVE-2015 -2093 malicious Excel file exploiting CVE-2013 -3029 email attachment from abc@xyz. com Host indicators Registry keys A, B, C Processes D, E, F Event log entries G, H Memory fingerprint J, K
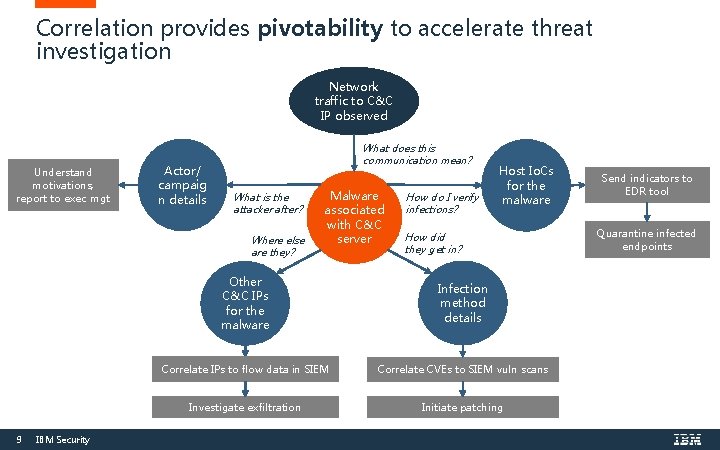
Correlation provides pivotability to accelerate threat investigation Network traffic to C&C IP observed Understand motivations, report to exec mgt Actor/ campaig n details What does this communication mean? What is the attacker after? Where else are they? 9 IBM Security Malware associated with C&C server How do I verify infections? Host Io. Cs for the malware How did they get in? Other C&C IPs for the malware Infection method details Correlate IPs to flow data in SIEM Correlate CVEs to SIEM vuln scans Investigate exfiltration Initiate patching Send indicators to EDR tool Quarantine infected endpoints
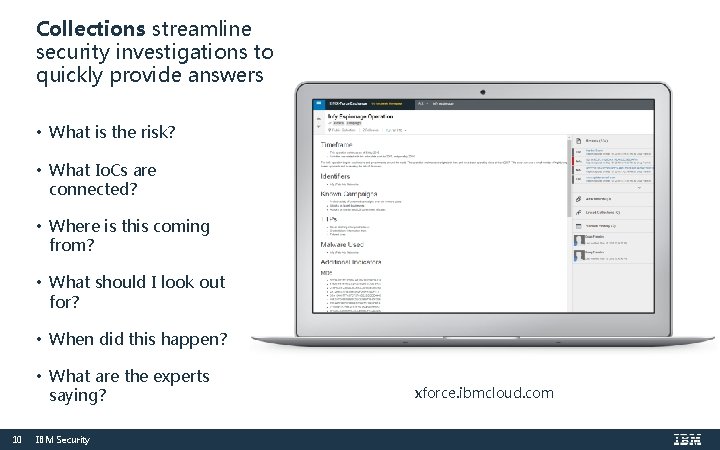
Collections streamline security investigations to quickly provide answers • What is the risk? • What Io. Cs are connected? • Where is this coming from? • What should I look out for? • When did this happen? • What are the experts saying? 10 IBM Security xforce. ibmcloud. com
RESEARCH Investigate security incidents with curated content COLLABORATE Validate threats and develop response plans with peers ACT Integrate threat intelligence with security solutions through open standards 11 IBM Security
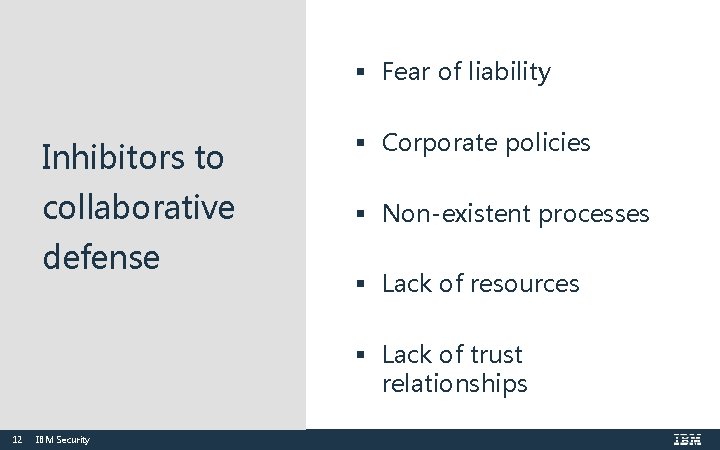
§ Fear of liability Inhibitors to § Corporate policies collaborative § Non-existent processes defense § Lack of resources § Lack of trust relationships 12 IBM Security
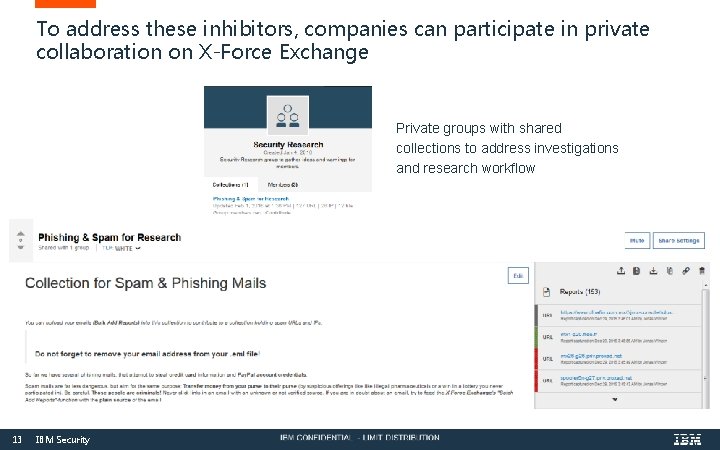
To address these inhibitors, companies can participate in private collaboration on X-Force Exchange Private groups with shared collections to address investigations and research workflow 13 IBM Security
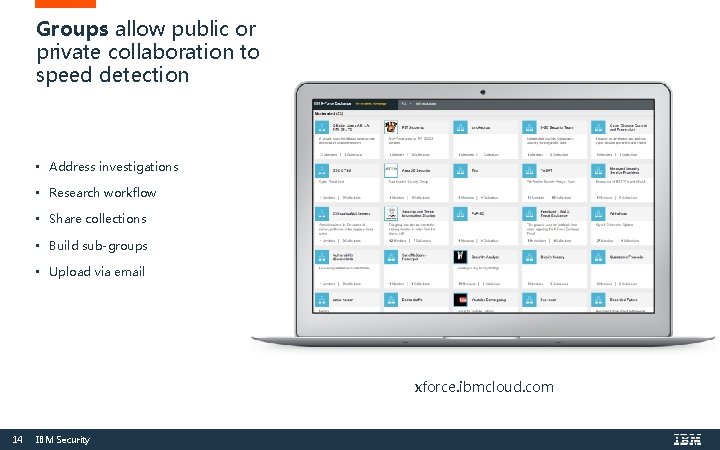
Groups allow public or private collaboration to speed detection • Address investigations • Research workflow • Share collections • Build sub-groups • Upload via email xforce. ibmcloud. com 14 IBM Security
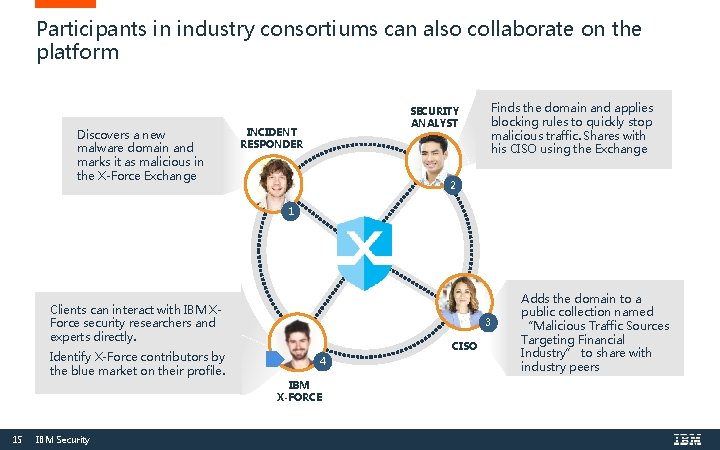
Participants in industry consortiums can also collaborate on the platform Discovers a new malware domain and marks it as malicious in the X-Force Exchange SECURITY ANALYST INCIDENT RESPONDER Finds the domain and applies blocking rules to quickly stop malicious traffic. Shares with his CISO using the Exchange 2 1 Clients can interact with IBM XForce security researchers and experts directly. Identify X-Force contributors by the blue market on their profile. 3 CISO 4 IBM X-FORCE 15 IBM Security Adds the domain to a public collection named “Malicious Traffic Sources Targeting Financial Industry” to share with industry peers
RESEARCH Investigate security incidents with curated content COLLABORATE Validate threats and develop response plans with peers ACT Integrate threat intelligence with security solutions through open standards 16 IBM Security
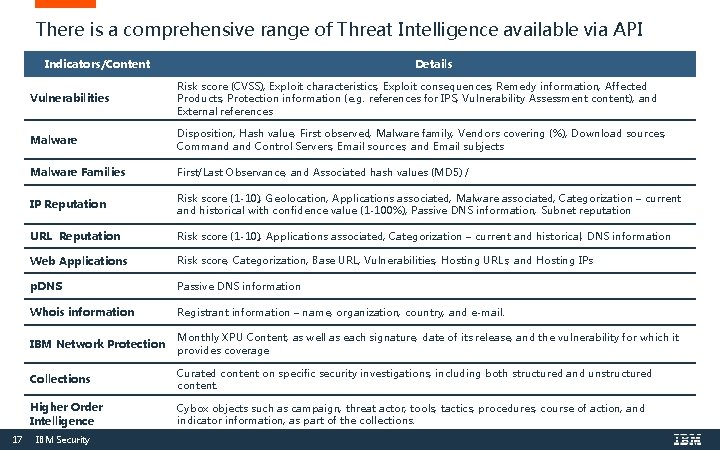
There is a comprehensive range of Threat Intelligence available via API Indicators/Content 17 Details Vulnerabilities Risk score (CVSS), Exploit characteristics, Exploit consequences, Remedy information, Affected Products, Protection information (e. g. references for IPS, Vulnerability Assessment content), and External references Malware Disposition, Hash value, First observed, Malware family, Vendors covering (%), Download sources, Command Control Servers, Email sources, and Email subjects Malware Families First/Last Observance, and Associated hash values (MD 5) / IP Reputation Risk score (1 -10), Geolocation, Applications associated, Malware associated, Categorization – current and historical with confidence value (1 -100%), Passive DNS information, Subnet reputation URL Reputation Risk score (1 -10), Applications associated, Categorization – current and historical, DNS information Web Applications Risk score, Categorization, Base URL, Vulnerabilities, Hosting URLs, and Hosting IPs p. DNS Passive DNS information Whois information Registrant information – name, organization, country, and e-mail. IBM Network Protection Monthly XPU Content, as well as each signature, date of its release, and the vulnerability for which it provides coverage Collections Curated content on specific security investigations, including both structured and unstructured content. Higher Order Intelligence Cybox objects such as campaign, threat actor, tools, tactics, procedures, course of action, and indicator information, as part of the collections. IBM Security
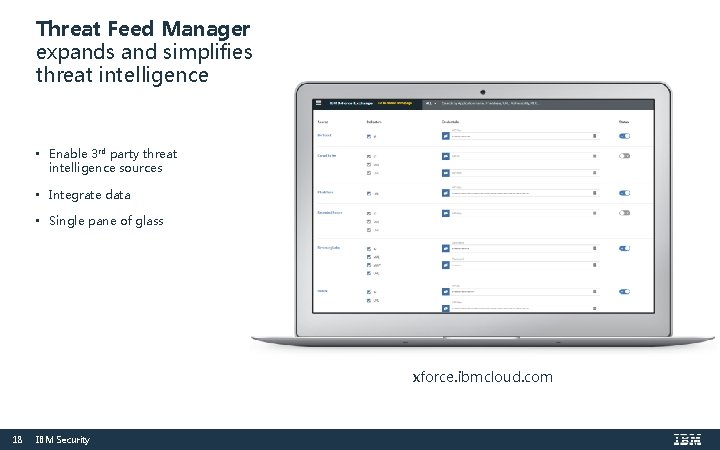
Threat Feed Manager expands and simplifies threat intelligence • Enable 3 rd party threat intelligence sources • Integrate data • Single pane of glass xforce. ibmcloud. com 18 IBM Security
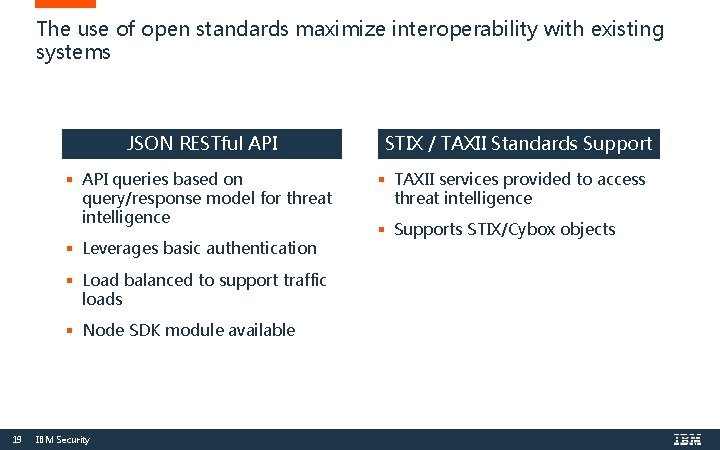
The use of open standards maximize interoperability with existing systems JSON RESTful API § API queries based on query/response model for threat intelligence § Leverages basic authentication § Load balanced to support traffic loads § Node SDK module available 19 IBM Security STIX / TAXII Standards Support § TAXII services provided to access threat intelligence § Supports STIX/Cybox objects
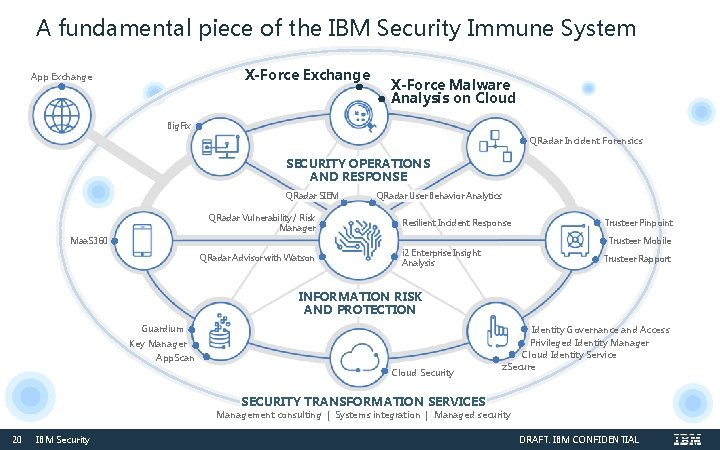
A fundamental piece of the IBM Security Immune System X-Force Exchange App Exchange X-Force Malware Analysis on Cloud Big. Fix QRadar Incident Forensics SECURITY OPERATIONS AND RESPONSE QRadar SIEM QRadar Vulnerability / Risk Manager QRadar User Behavior Analytics Resilient Incident Response Trusteer Pinpoint Trusteer Mobile Maa. S 360 QRadar Advisor with Watson i 2 Enterprise Insight Analysis Trusteer Rapport INFORMATION RISK AND PROTECTION Guardium Key Manager App. Scan Cloud Security Identity Governance and Access Privileged Identity Manager Cloud Identity Service z. Secure SECURITY TRANSFORMATION SERVICES Management consulting | Systems integration | Managed security 20 IBM Security DRAFT: IBM CONFIDENTIAL
THANK YOU FOLLOW US ON: ibm. com/securityintelligence. com xforce. ibmcloud. com @ibmsecurity youtube/user/ibmsecuritysolution s © Copyright IBM Corporation 2017. All rights reserved. The information contained in these materials is provided for informational purposes only, and is provided AS IS without warranty of any kind, express or implied. IBM shall not be responsible for any damages arising out of the use of, or otherwise related to, these materials. Nothing contained in these materials is intended to, nor shall have the effect of, creating any warranties or representations from IBM or its suppliers or licensors, or altering the terms and conditions of the applicable license agreement governing the use of IBM software. References in these materials to IBM products, programs, or services do not imply that they will be available in all countries in which IBM operates. Product release dates and / or capabilities referenced in these materials may change at any time at IBM’s sole discretion based on market opportunities or other factors, and are not intended to be a commitment to future product or feature availability in any way. IBM, the IBM logo, and other IBM products and services are trademarks of the International Business Machines Corporation, in the United States, other countries or both. Other company, product, or service names may be trademarks or service marks of others. Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to improper access from within and outside your enterprise. Improper access can result in information being altered, destroyed, misappropriated or misused or can result in damage to or misuse of your systems, including for use in attacks on others. No IT system or product should be considered completely secure and no single product, service or security measure can be completely effective in preventing improper use or access. IBM systems, products and services are designed to be part of a lawful, comprehensive security approach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM DOES NOT WARRANT THAT ANYSYSTEMS, PRODUCTS OR SERVICES ARE IMMUNE FROM, OR WILL MAKE YOUR ENTERPRISE IMMUNE FROM, THE MALICIOUS OR ILLEGAL CONDUCT OF ANY PARTY.
- Slides: 21