IBM Security Systems IBM Security Strategy Intelligence Integration
IBM Security Systems IBM Security Strategy Intelligence, Integration and Expertise Marc van Zadelhoff VP, WW Strategy and Product Management Joe Ruthven IBM MEA Security Leader IBM Security Systems April 2013 © 2012 IBM Corporation 1 © 2013 IBM Corporation
IBM Security Systems Innovative technology changes everything 1 trillion connected objects 1 billion mobile workers Social business Bring your own IT Cloud and virtualization 2 © 2013 IBM Corporation
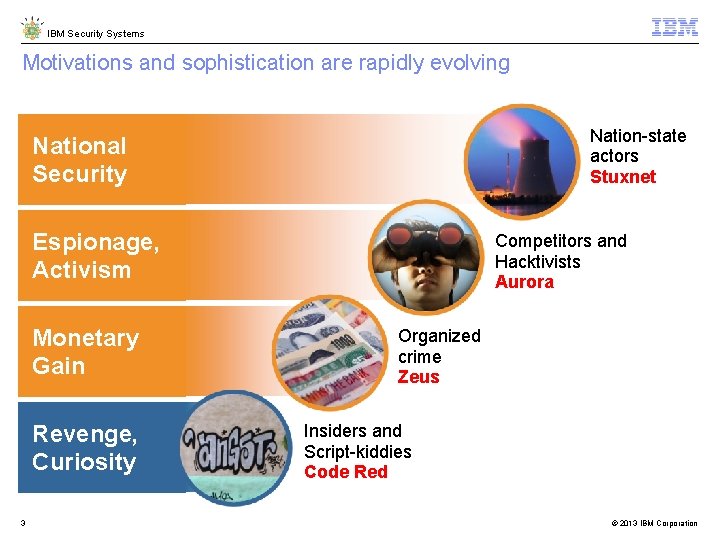
IBM Security Systems Motivations and sophistication are rapidly evolving Nation-state actors Stuxnet National Security Espionage, Activism Monetary Gain Revenge, Curiosity 3 Competitors and Hacktivists Aurora Organized crime Zeus Insiders and Script-kiddies Code Red © 2013 IBM Corporation
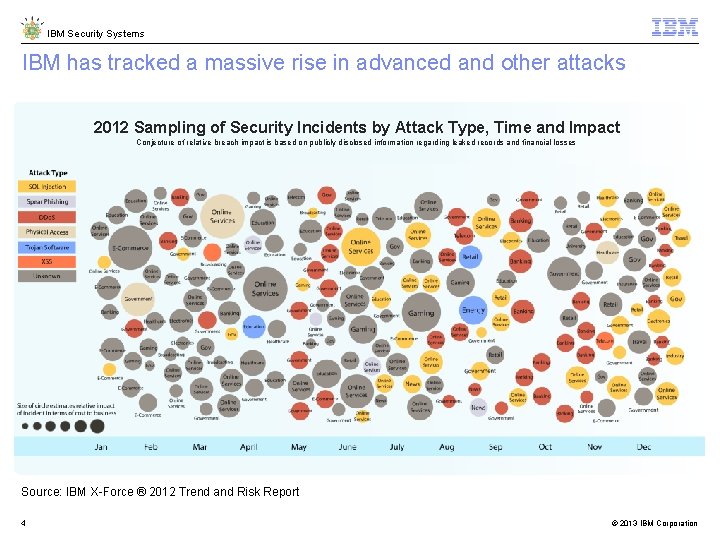
IBM Security Systems IBM has tracked a massive rise in advanced and other attacks 2012 Sampling of Security Incidents by Attack Type, Time and Impact Conjecture of relative breach impact is based on publicly disclosed information regarding leaked records and financial losses Source: IBM X-Force ® 2012 Trend and Risk Report 4 © 2013 IBM Corporation
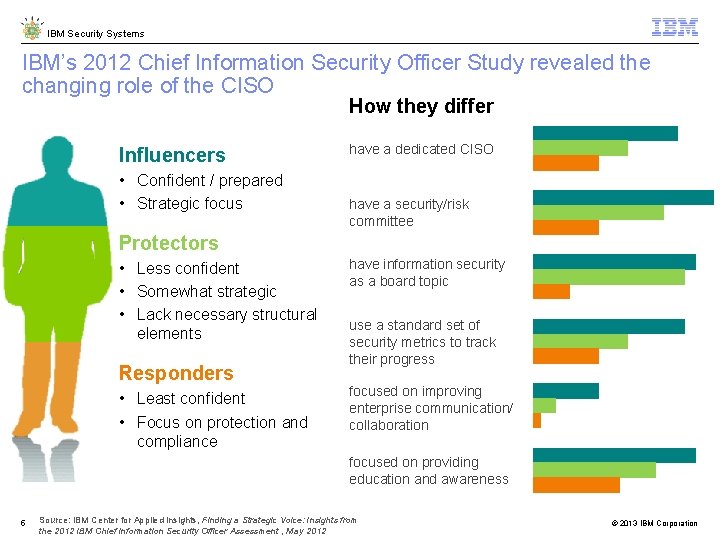
IBM Security Systems IBM’s 2012 Chief Information Security Officer Study revealed the changing role of the CISO How they differ Influencers • Confident / prepared • Strategic focus have a dedicated CISO have a security/risk committee Protectors • Less confident • Somewhat strategic • Lack necessary structural elements Responders • Least confident • Focus on protection and compliance have information security as a board topic use a standard set of security metrics to track their progress focused on improving enterprise communication/ collaboration focused on providing education and awareness 5 Source: IBM Center for Applied Insights, Finding a Strategic Voice: Insights from the 2012 IBM Chief Information Security Officer Assessment , May 2012 © 2013 IBM Corporation
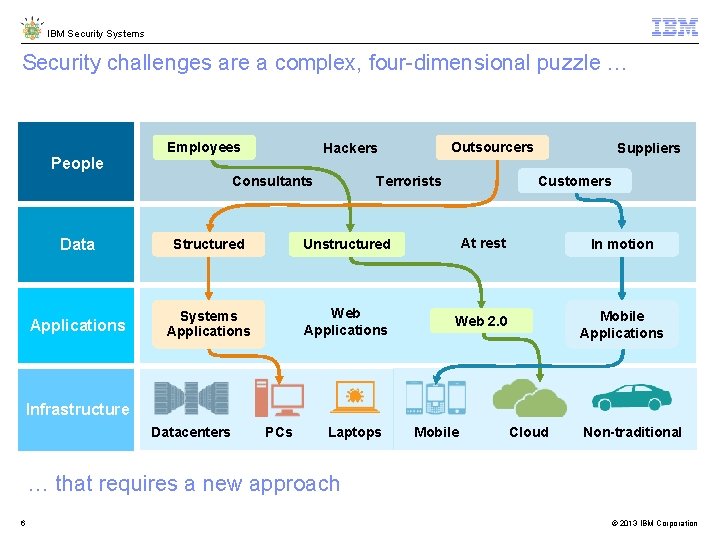
IBM Security Systems Security challenges are a complex, four-dimensional puzzle … People Employees Outsourcers Hackers Consultants Suppliers Customers Terrorists Data Structured Unstructured At rest In motion Applications Systems Applications Web 2. 0 Mobile Applications Infrastructure Datacenters PCs Laptops Mobile Cloud Non-traditional … that requires a new approach 6 © 2013 IBM Corporation

IBM Security Systems 7 © 2013 IBM Corporation
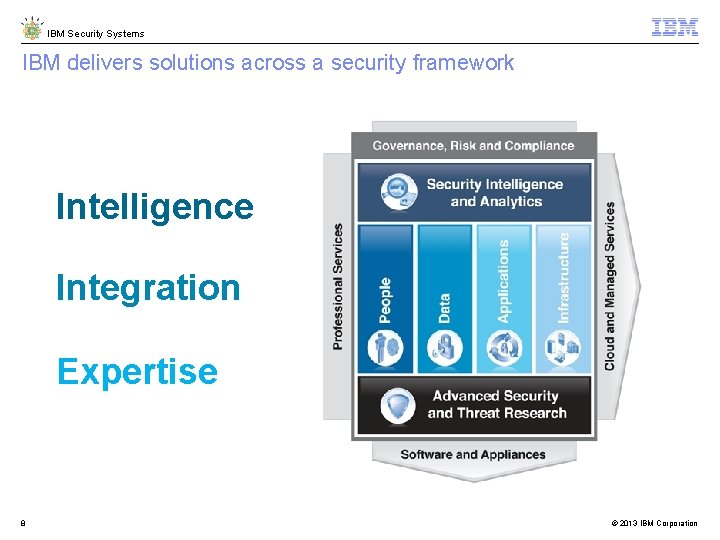
IBM Security Systems IBM delivers solutions across a security framework Intelligence Integration Expertise 8 © 2013 IBM Corporation
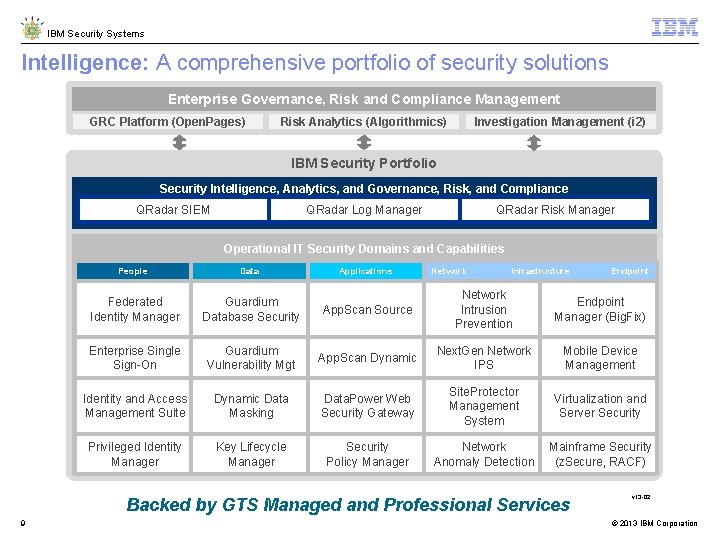
IBM Security Systems Intelligence: A comprehensive portfolio of security solutions Enterprise Governance, Risk and Compliance Management GRC Platform (Open. Pages) Risk Analytics (Algorithmics) Investigation Management (i 2) IBM Security Portfolio Security Intelligence, Analytics, and Governance, Risk, and Compliance QRadar SIEM QRadar Log Manager QRadar Risk Manager Operational IT Security Domains and Capabilities People Data Federated Identity Manager Guardium Database Security Enterprise Single Sign-On Applications Network Infrastructure App. Scan Source Network Intrusion Prevention Endpoint Manager (Big. Fix) Guardium Vulnerability Mgt App. Scan Dynamic Next. Gen Network IPS Mobile Device Management Identity and Access Management Suite Dynamic Data Masking Data. Power Web Security Gateway Site. Protector Management System Virtualization and Server Security Privileged Identity Manager Key Lifecycle Manager Security Policy Manager Network Anomaly Detection Mainframe Security (z. Secure, RACF) Backed by GTS Managed and Professional Services 9 Endpoint v 13 -02 © 2013 IBM Corporation
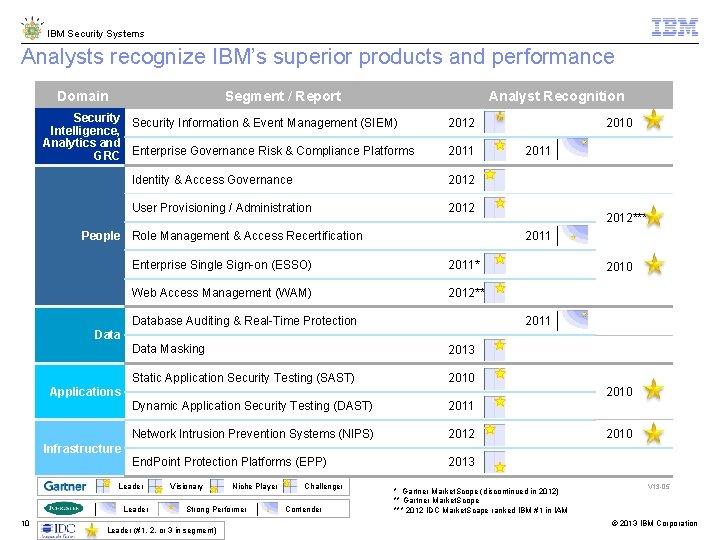
IBM Security Systems Analysts recognize IBM’s superior products and performance Domain Segment / Report Analyst Recognition Security Information & Event Management (SIEM) Intelligence, Analytics and GRC Enterprise Governance Risk & Compliance Platforms 2012 2011 Identity & Access Governance 2012 User Provisioning / Administration 2012 People Role Management & Access Recertification 2010 2011 2012*** 2011 Enterprise Single Sign-on (ESSO) 2011* Web Access Management (WAM) 2012** Database Auditing & Real-Time Protection 2010 2011 Data Masking 2013 Static Application Security Testing (SAST) 2010 Dynamic Application Security Testing (DAST) 2011 Network Intrusion Prevention Systems (NIPS) 2012 End. Point Protection Platforms (EPP) 2013 2010 Applications 2010 Infrastructure Leader 10 Visionary Niche Player Strong Performer Leader (#1, 2, or 3 in segment) Challenger Contender * Gartner Market. Scope (discontinued in 2012) ** Gartner Market. Scope *** 2012 IDC Market. Scape ranked IBM #1 in IAM V 13 -05 © 2013 IBM Corporation
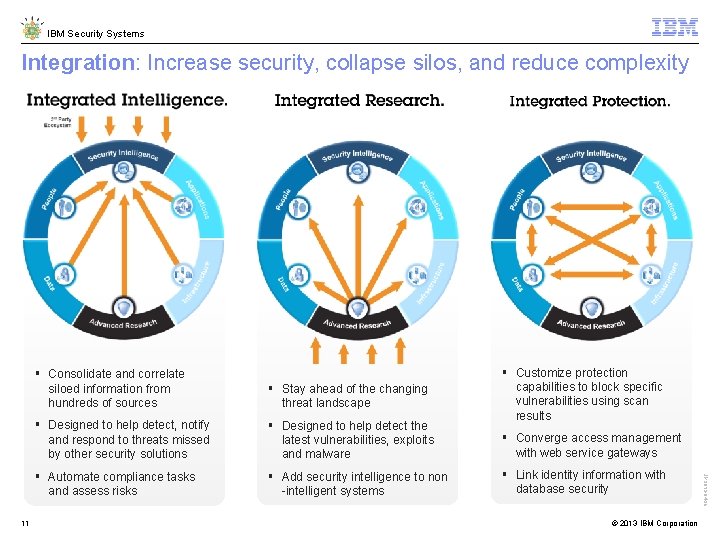
IBM Security Systems Integration: Increase security, collapse silos, and reduce complexity § Stay ahead of the changing threat landscape § Designed to help detect, notify and respond to threats missed by other security solutions § Designed to help detect the latest vulnerabilities, exploits and malware § Automate compliance tasks and assess risks § Add security intelligence to non -intelligent systems § Customize protection capabilities to block specific vulnerabilities using scan results § Converge access management with web service gateways § Link identity information with database security © 2013 IBM Corporation JK 2012 -04 -26 11 § Consolidate and correlate siloed information from hundreds of sources
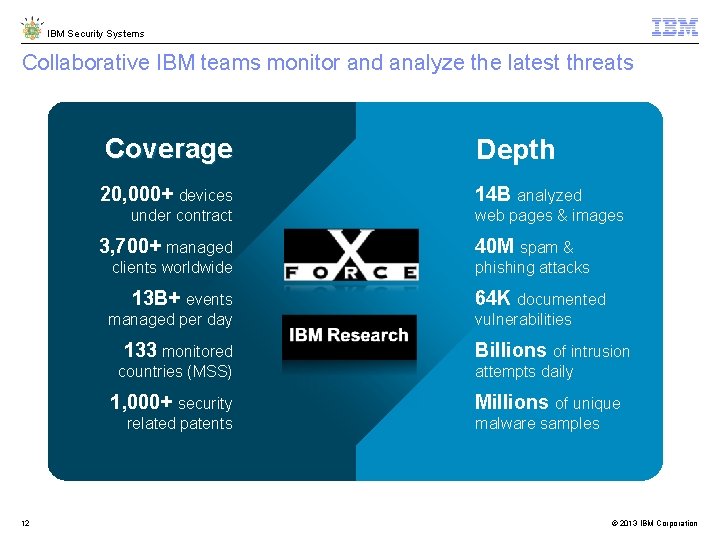
IBM Security Systems Collaborative IBM teams monitor and analyze the latest threats Coverage Depth 20, 000+ devices 14 B analyzed under contract 3, 700+ managed clients worldwide 13 B+ events managed per day 133 monitored countries (MSS) 1, 000+ security related patents 12 web pages & images 40 M spam & phishing attacks 64 K documented vulnerabilities Billions of intrusion attempts daily Millions of unique malware samples © 2013 IBM Corporation
IBM Security Systems 13 © 2013 IBM Corporation
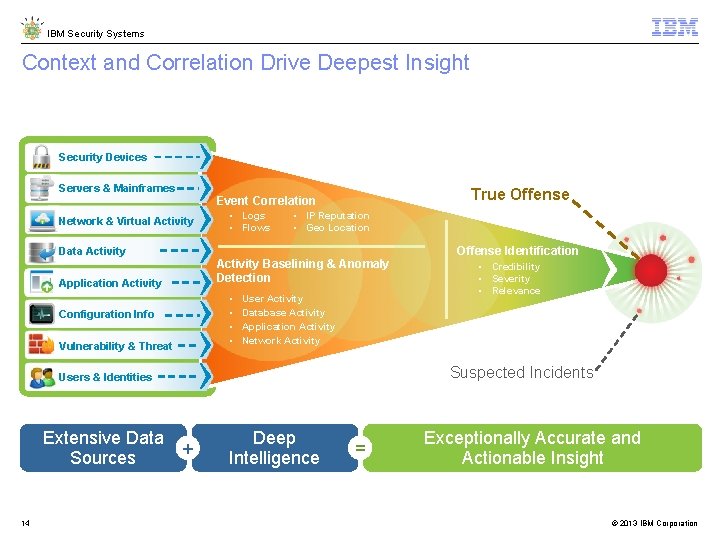
IBM Security Systems Context and Correlation Drive Deepest Insight Security Devices Servers & Mainframes True Offense Event Correlation Network & Virtual Activity Data Activity • Logs • Flows • IP Reputation • Geo Location Activity Baselining & Anomaly Detection Application Activity • • Configuration Info Vulnerability & Threat User Activity Database Activity Application Activity Network Activity 14 • Credibility • Severity • Relevance Suspected Incidents Users & Identities Extensive Data Sources Offense Identification + Deep Intelligence = Exceptionally Accurate and Actionable Insight © 2013 IBM Corporation
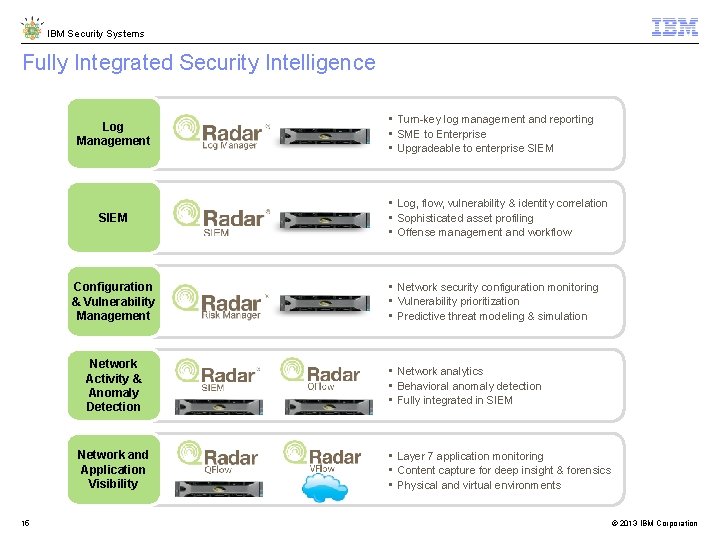
IBM Security Systems Fully Integrated Security Intelligence Log Management SIEM Configuration & Vulnerability Management Network Activity & Anomaly Detection Network and Application Visibility 15 • Turn-key log management and reporting • SME to Enterprise • Upgradeable to enterprise SIEM • Log, flow, vulnerability & identity correlation • Sophisticated asset profiling • Offense management and workflow • Network security configuration monitoring • Vulnerability prioritization • Predictive threat modeling & simulation • Network analytics • Behavioral anomaly detection • Fully integrated in SIEM • Layer 7 application monitoring • Content capture for deep insight & forensics • Physical and virtual environments © 2013 IBM Corporation
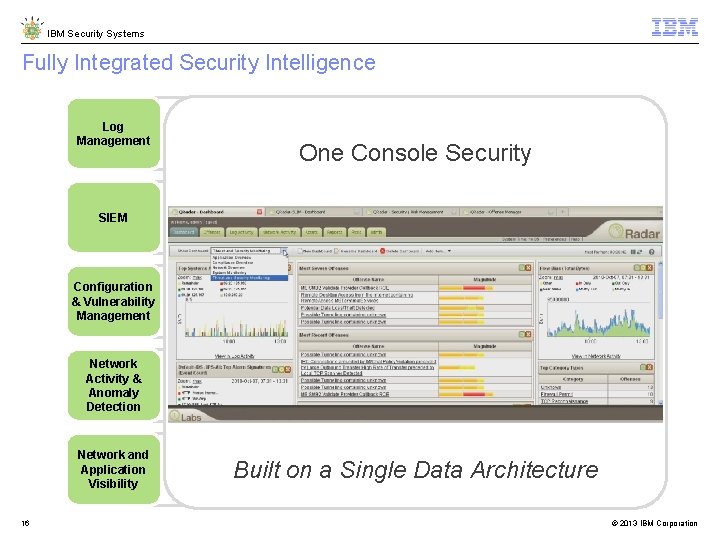
IBM Security Systems Fully Integrated Security Intelligence Log Management SIEM Configuration & Vulnerability Management Network Activity & Anomaly Detection Network and Application Visibility 16 • Turn-key log management and reporting • SME to Enterprise • Upgradeable to enterprise SIEM One Console Security • Log, flow, vulnerability & identity correlation • Sophisticated asset profiling • Offense management and workflow • Network security configuration monitoring • Vulnerability prioritization • Predictive threat modeling & simulation • Network analytics • Behavioral anomaly detection • Fully integrated in SIEM • Layer 7 application monitoring • Content capture for deep insight & forensics • Physical and virtual environments Built on a Single Data Architecture © 2013 IBM Corporation
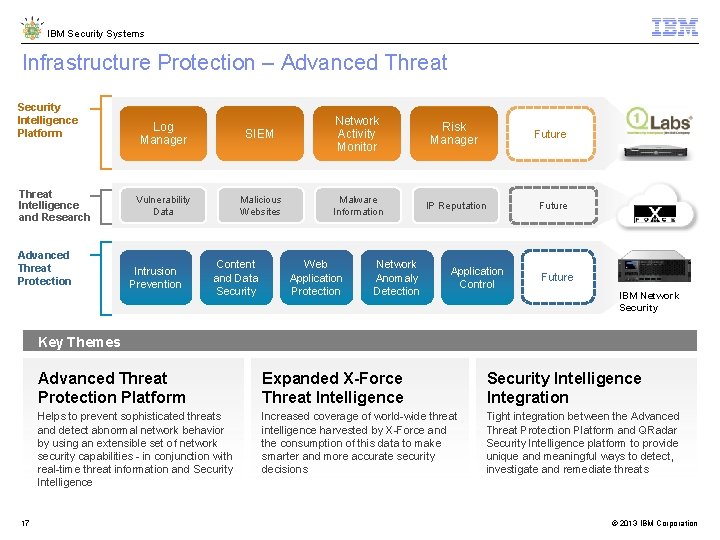
IBM Security Systems Infrastructure Protection – Advanced Threat Security Intelligence Platform Threat Intelligence and Research Advanced Threat Protection Log Manager SIEM Network Activity Monitor Risk Manager Future Vulnerability Data Malicious Websites Malware Information IP Reputation Future Intrusion Prevention Content and Data Security Web Application Protection Network Anomaly Detection Application Control Future IBM Network Security Key Themes 17 Advanced Threat Protection Platform Expanded X-Force Threat Intelligence Security Intelligence Integration Helps to prevent sophisticated threats and detect abnormal network behavior by using an extensible set of network security capabilities - in conjunction with real-time threat information and Security Intelligence Increased coverage of world-wide threat intelligence harvested by X-Force and the consumption of this data to make smarter and more accurate security decisions Tight integration between the Advanced Threat Protection Platform and QRadar Security Intelligence platform to provide unique and meaningful ways to detect, investigate and remediate threats © 2013 IBM Corporation
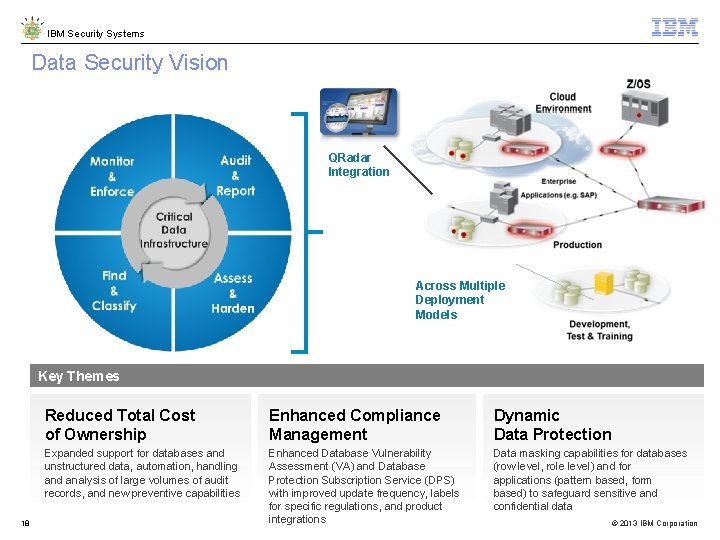
IBM Security Systems Data Security Vision QRadar Integration Across Multiple Deployment Models Key Themes 18 Reduced Total Cost of Ownership Enhanced Compliance Management Dynamic Data Protection Expanded support for databases and unstructured data, automation, handling and analysis of large volumes of audit records, and new preventive capabilities Enhanced Database Vulnerability Assessment (VA) and Database Protection Subscription Service (DPS) with improved update frequency, labels for specific regulations, and product integrations Data masking capabilities for databases (row level, role level) and for applications (pattern based, form based) to safeguard sensitive and confidential data © 2013 IBM Corporation
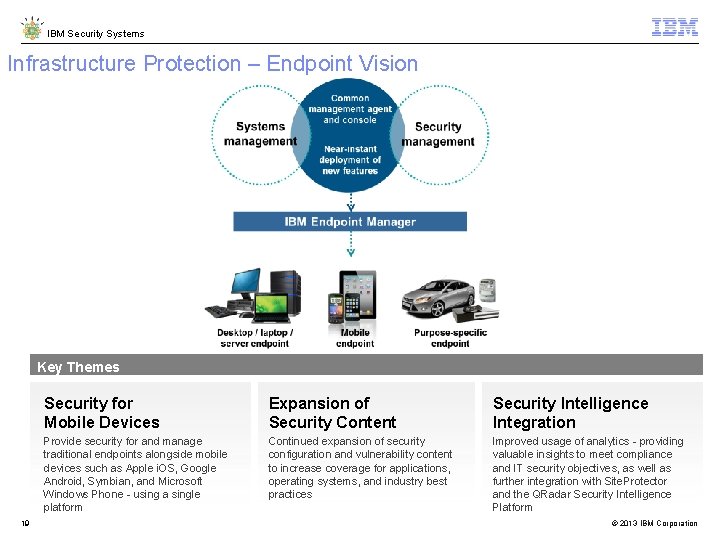
IBM Security Systems Infrastructure Protection – Endpoint Vision Key Themes 19 Security for Mobile Devices Expansion of Security Content Security Intelligence Integration Provide security for and manage traditional endpoints alongside mobile devices such as Apple i. OS, Google Android, Symbian, and Microsoft Windows Phone - using a single platform Continued expansion of security configuration and vulnerability content to increase coverage for applications, operating systems, and industry best practices Improved usage of analytics - providing valuable insights to meet compliance and IT security objectives, as well as further integration with Site. Protector and the QRadar Security Intelligence Platform © 2013 IBM Corporation
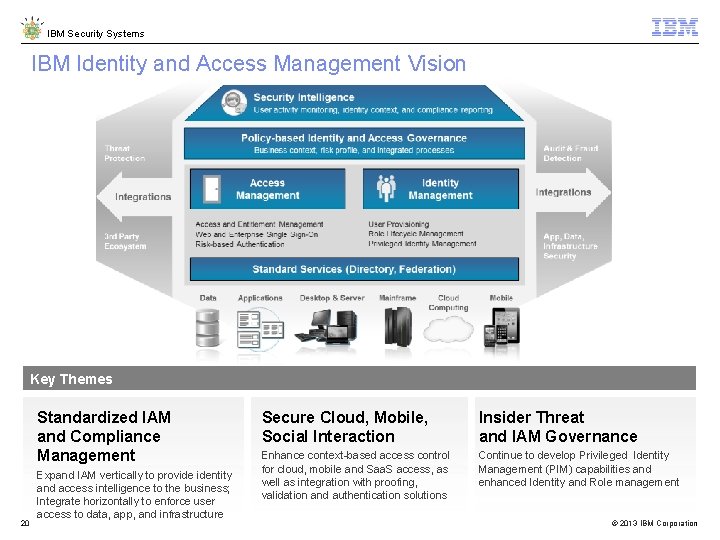
IBM Security Systems IBM Identity and Access Management Vision Key Themes Standardized IAM and Compliance Management 20 Expand IAM vertically to provide identity and access intelligence to the business; Integrate horizontally to enforce user access to data, app, and infrastructure Secure Cloud, Mobile, Social Interaction Insider Threat and IAM Governance Enhance context-based access control for cloud, mobile and Saa. S access, as well as integration with proofing, validation and authentication solutions Continue to develop Privileged Identity Management (PIM) capabilities and enhanced Identity and Role management © 2013 IBM Corporation
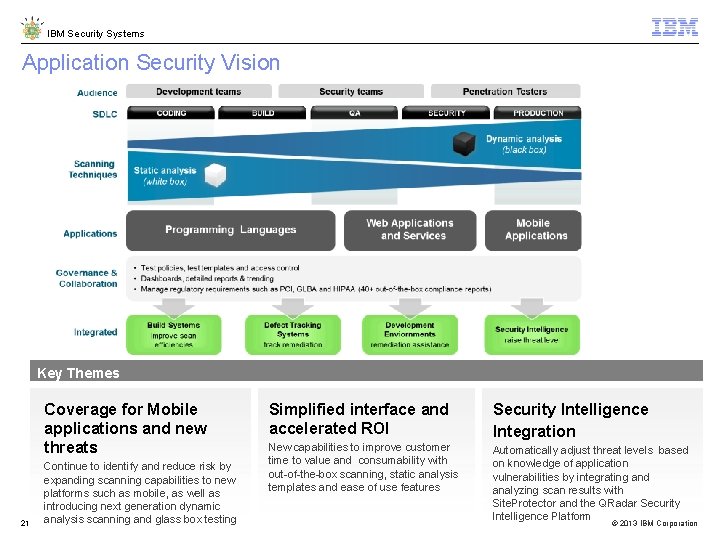
IBM Security Systems Application Security Vision Key Themes Coverage for Mobile applications and new threats 21 Continue to identify and reduce risk by expanding scanning capabilities to new platforms such as mobile, as well as introducing next generation dynamic analysis scanning and glass box testing Simplified interface and accelerated ROI Security Intelligence Integration New capabilities to improve customer time to value and consumability with out-of-the-box scanning, static analysis templates and ease of use features Automatically adjust threat levels based on knowledge of application vulnerabilities by integrating and analyzing scan results with Site. Protector and the QRadar Security Intelligence Platform © 2013 IBM Corporation
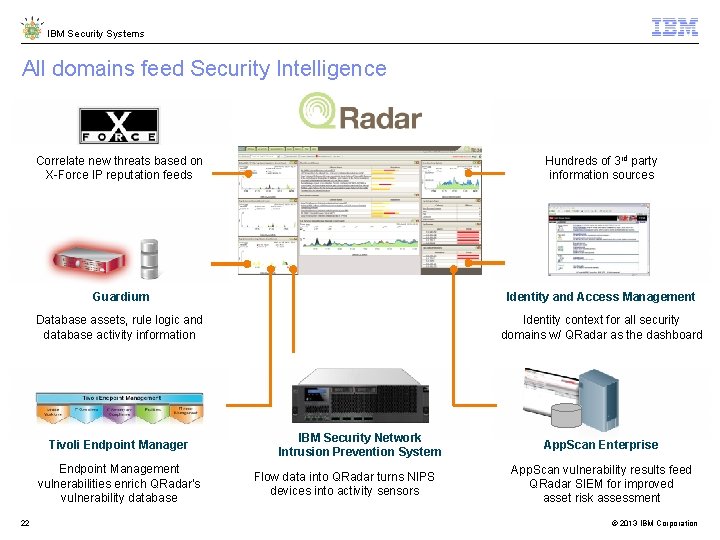
IBM Security Systems All domains feed Security Intelligence Correlate new threats based on X-Force IP reputation feeds Hundreds of 3 rd party information sources Guardium Identity and Access Management Database assets, rule logic and database activity information Identity context for all security domains w/ QRadar as the dashboard Tivoli Endpoint Manager Endpoint Management vulnerabilities enrich QRadar’s vulnerability database 22 IBM Security Network Intrusion Prevention System Flow data into QRadar turns NIPS devices into activity sensors App. Scan Enterprise App. Scan vulnerability results feed QRadar SIEM for improved asset risk assessment © 2013 IBM Corporation
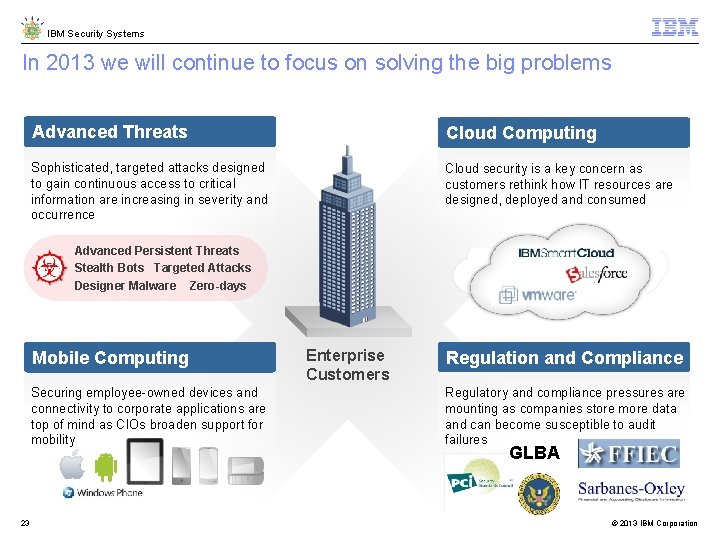
IBM Security Systems In 2013 we will continue to focus on solving the big problems Advanced Threats Cloud Computing Sophisticated, targeted attacks designed to gain continuous access to critical information are increasing in severity and occurrence Cloud security is a key concern as customers rethink how IT resources are designed, deployed and consumed Advanced Persistent Threats Stealth Bots Targeted Attacks Designer Malware Zero-days Mobile Computing Securing employee-owned devices and connectivity to corporate applications are top of mind as CIOs broaden support for mobility 23 Enterprise Customers Regulation and Compliance Regulatory and compliance pressures are mounting as companies store more data and can become susceptible to audit failures GLBA © 2013 IBM Corporation
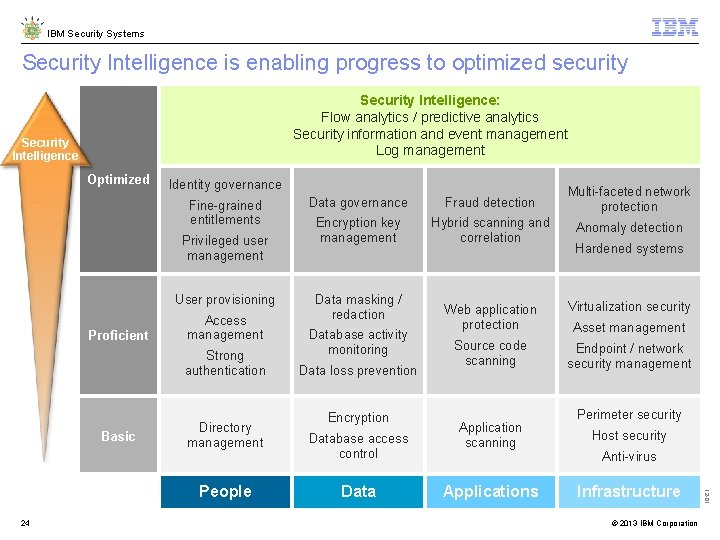
IBM Security Systems Security Intelligence is enabling progress to optimized security Security Intelligence: Flow analytics / predictive analytics Security information and event management Log management Security Intelligence Optimized Identity governance Fine-grained entitlements Privileged user management User provisioning Proficient Access management Strong authentication Basic Directory management 24 Fraud detection Multi-faceted network protection Encryption key management Hybrid scanning and correlation Anomaly detection Data masking / redaction Database activity monitoring Data loss prevention Encryption Database access control Data Hardened systems Web application protection Virtualization security Source code scanning Endpoint / network security management Application scanning Applications Asset management Perimeter security Host security Anti-virus Infrastructure © 2013 IBM Corporation 12 -01 People Data governance
IBM Security Systems Intelligent solutions provide the DNA to secure a Smarter Planet Security Intelligence, Analytics & GRC People Data Applications Infrastructure 25 © 2013 IBM Corporation
IBM Security Systems Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to improper access from within and outside your enterprise. Improper access can result in information being altered, destroyed or misappropriated or can result in damage to or misuse of your systems, including to attack others. No IT system or product should be considered completely secure and no single product or security measure can be completely effective in preventing improper access. IBM systems and products are designed to be part of a comprehensive security approach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM DOES NOT WARRANT THAT SYSTEMS AND PRODUCTS ARE IMMUNE FROM THE MALICIOUS OR ILLEGAL CONDUCT OF ANY PARTY. ibm. com/security © Copyright IBM Corporation 2012. All rights reserved. The information contained in these materials is provided for informational purposes only, and is provided AS IS without warranty of any kind, express or implied. IBM shall not be responsible for any damages arising out of the use of, or otherwise related to, these materials. Nothing contained in these materials is intended to, nor shall have the effect of, creating any warranties or representations from IBM or its suppliers or licensors, or altering the terms and conditions of the applicable license agreement governing the use of IBM software. References in these materials to IBM products, programs, or services do not imply that they will be available in all countries in which IBM operates. Product release dates and/or capabilities referenced in these materials may change at any time at IBM’s sole discretion based on market opportunities or other factors, and are not intended to be a commitment to future product or feature availability in any way. IBM, the IBM logo, and other IBM products and services are trademarks of the International Business Machines Corporation, in the United States, other © 2013 IBM Corporation 26 countries or both. Other company, product, or service names may be trademarks or service marks of others.
- Slides: 26