IBM Security Solutions phkkr ibm com 2011 IBM

클라우드 환경에서의 보안 이슈와 대응 IBM Security Solutions 박형근 차장 (phk@kr. ibm. com) © 2011 IBM Corporation
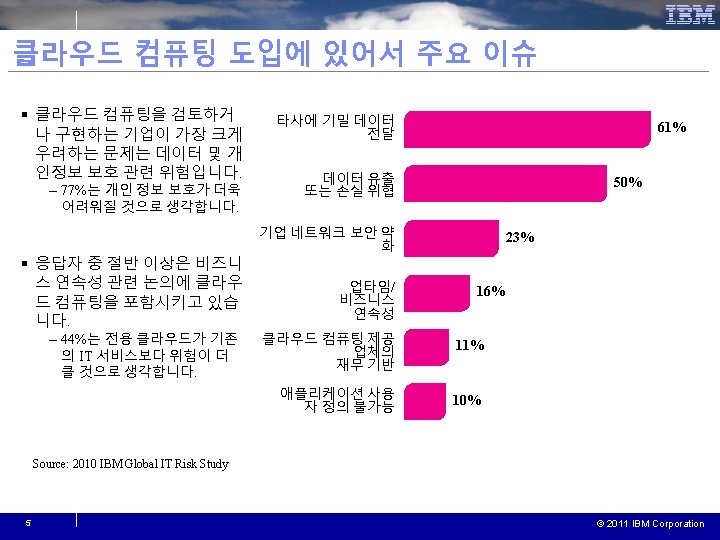
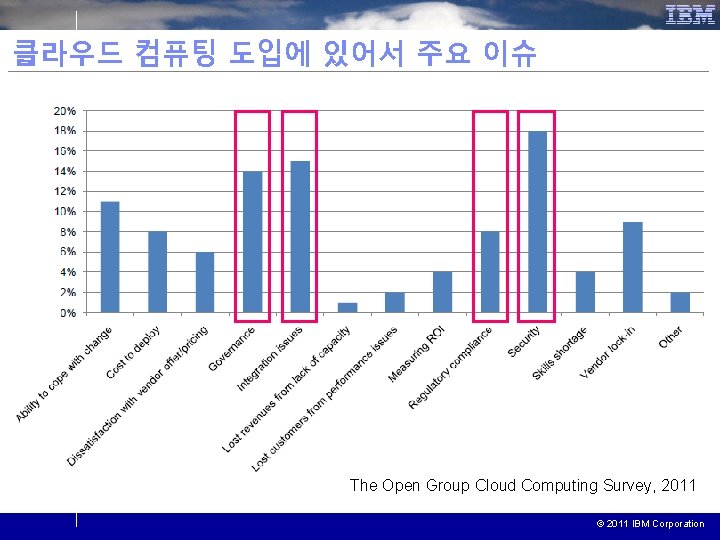
클라우드 컴퓨팅 도입에 있어서 주요 이슈 The Open Group Cloud Computing Survey, 2011 © 2011 IBM Corporation
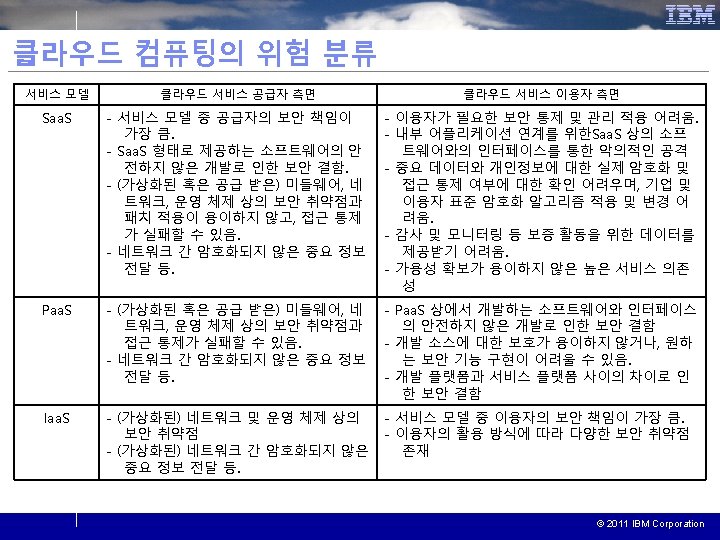
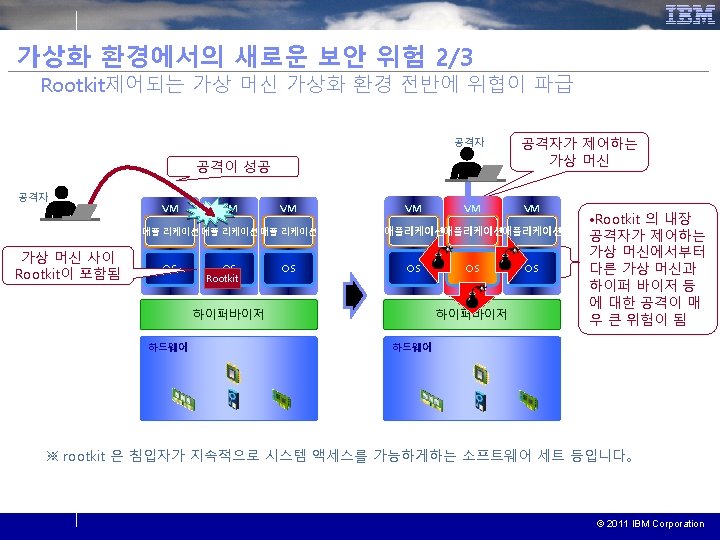
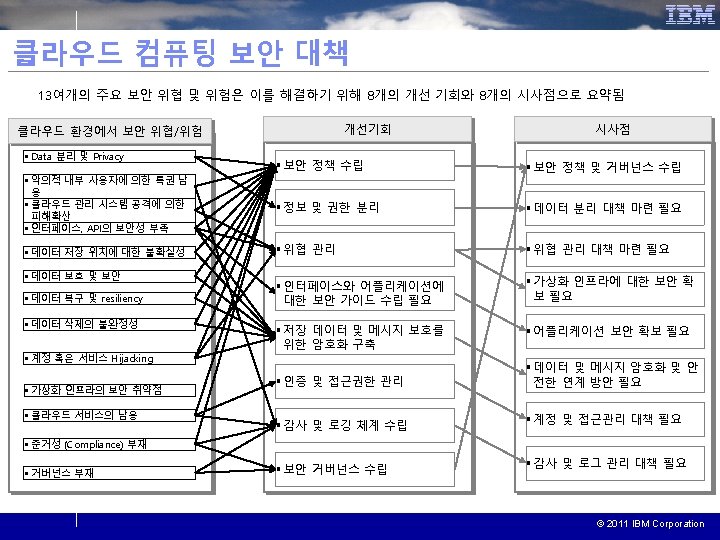
클라우드 보안 위협 목록 Gartner를 포함한 주요 기관들과 IBM은 클라우드 환경에서 발생할 수 있는 보안 위협들을 목록화였으며, 이들을 13여 개의 주요 목록으로 정리함 클라우드 환경에서 보안 위협 /위험 Gartner: Top Risks (2008) Privileged user access Regulatory compliance Data location Data segregation Recovery Investigative support Long-term viability [Heiser 09] Top Threats and Risks in Cloud Computing, IBM CSA: Top Threats (2010) Abuse and nefarious use of cloud Insecure interfaces and APIs Malicious insiders Shared technology issues Data loss or leakage Account or service hijacking Unknown risk profile ENISA: Top Security Risks (2009) Loss of governance Lock-in Isolation failure Compliance risks Management interface compromise Data protection Insecure or incomplete data deletion Malicious insider [ENISA 09/a] Process/VM Isolation, data segregation, multi -tenancy Malicious insiders (co-tenants, cloud provider) Management (incl. self-service) interface compromise Insecure interfaces and APIs Uncertainty over data location Data protection and security Data recovery, resiliency Insecure or incomplete data deletion Account or service hijacking Abuse of cloud services (extrusion) Compliance risks ※ ENISA : European Network and Information Security Agency, § Data 분리 및 Privacy § 악의적 내부 사용자에 의한 특권 남용 § 클라우드 관리 시스템 공격 에 의한 피해 확산 § 인터페이스, API의 보안성 부족 § 데이터 저장 위치에 대한 불확실성 § 데이터 보호 및 보안 § 데이터 복구 및 resiliency § 데이터 삭제의 불완정성 § 계정 혹은 서비스 Hijacking § 가상화 인프라의 보안 취약 점 § 클라우드 서비스의 남용 § 준거성 (Compliance) 부재 § 거버넌스 부재 CSA: Cloud Security Alliance © 2011 IBM Corporation
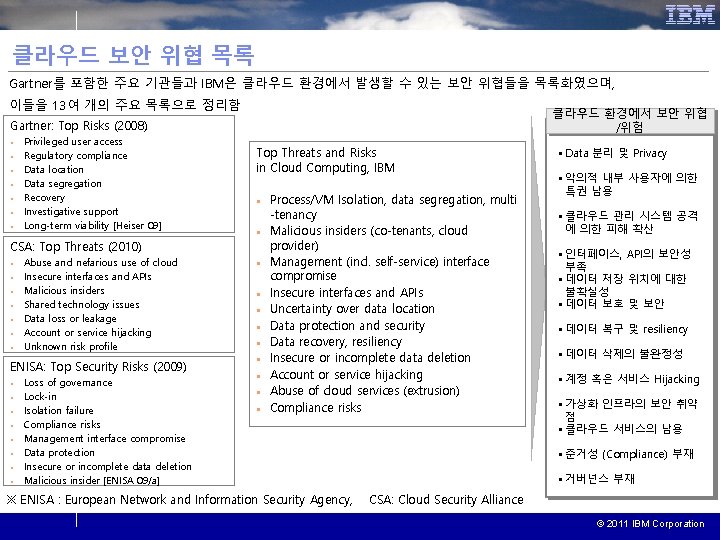
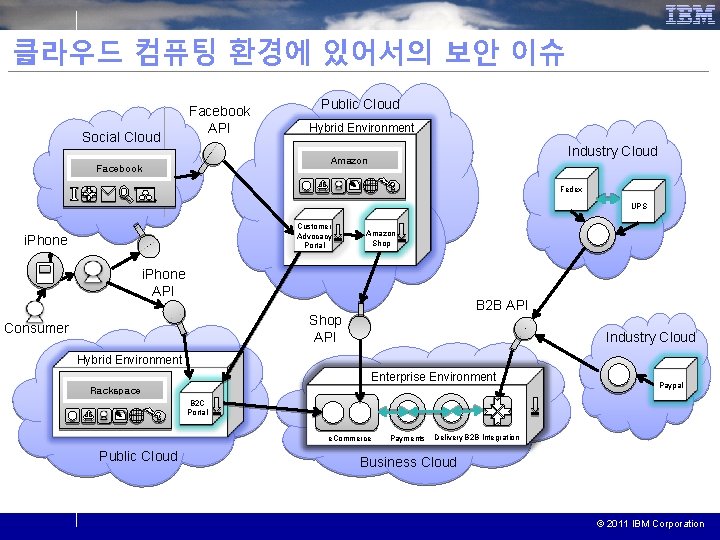
서비스 제공자와 이용자 간 책임 누가 어느 정도 수준으로 보안에 대한 책임을 갖는가? 데이터센터 Business Process-as-a-Service Application-as-a-Service Platform-as-a-Service Infrastructure-as-a-Service 12 인프라스트럭처 미들웨어 어플리케이션 프로세스 공급자 소비자 Page: -12 - © 2011 IBM Corporation 2020 -12 -
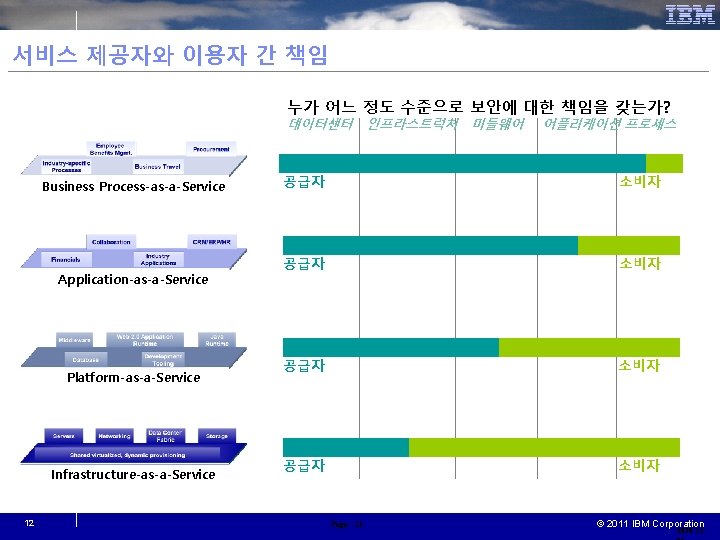
클라우드 컴퓨팅 환경에 있어서의 보안 이슈 Social Cloud Facebook API Public Cloud Hybrid Environment Industry Cloud Amazon Facebook I Fedex UPS Customer Advocacy Portal i. Phone Amazon Shop i. Phone API B 2 B API Shop API Consumer Industry Cloud Hybrid Environment Enterprise Environment Rackspace Paypal B 2 C Portal e. Commerce Public Cloud Payments Delivery B 2 B Integration Business Cloud © 2011 IBM Corporation
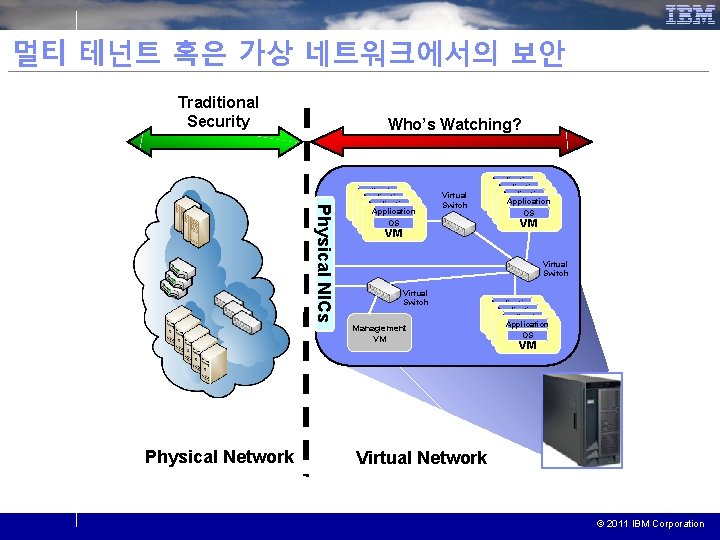
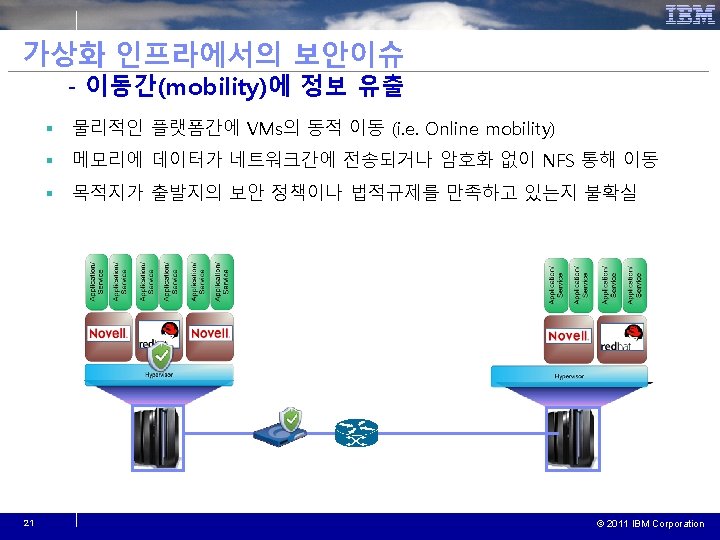
멀티 테넌트 혹은 가상 네트워크에서의 보안 Traditional Security Who’s Watching? Physical NICs Physical Network Application Process Service Application Process Process Service OS Application Process Service VM OS Process VM OS VM VM Virtual Switch Management VM Application Process Service Application Process Service OS Application Process Service VM OS Process VM OS VM VM Virtual Network © 2011 IBM Corporation
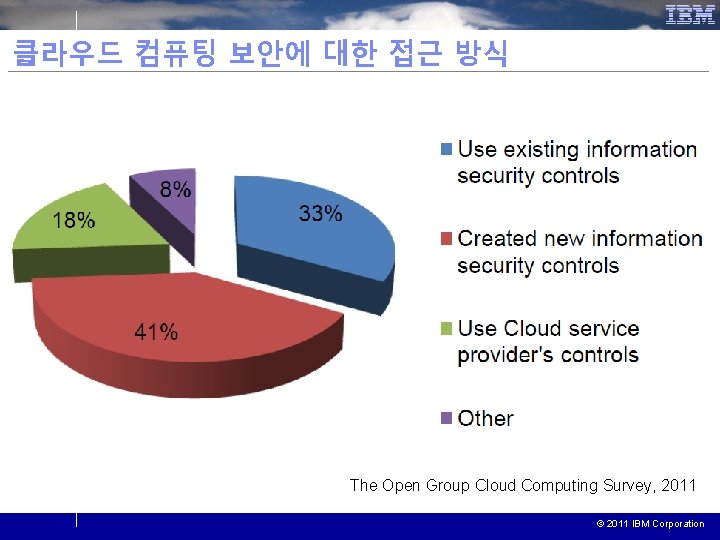
클라우드 컴퓨팅 보안에 대한 접근 방식 The Open Group Cloud Computing Survey, 2011 © 2011 IBM Corporation
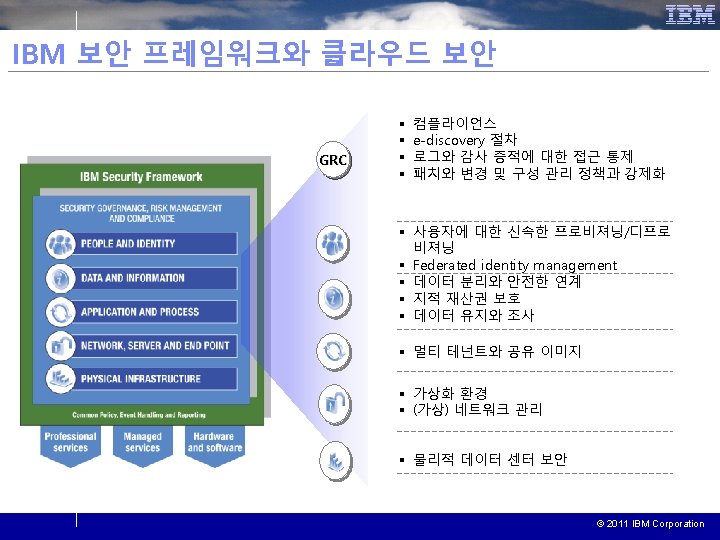
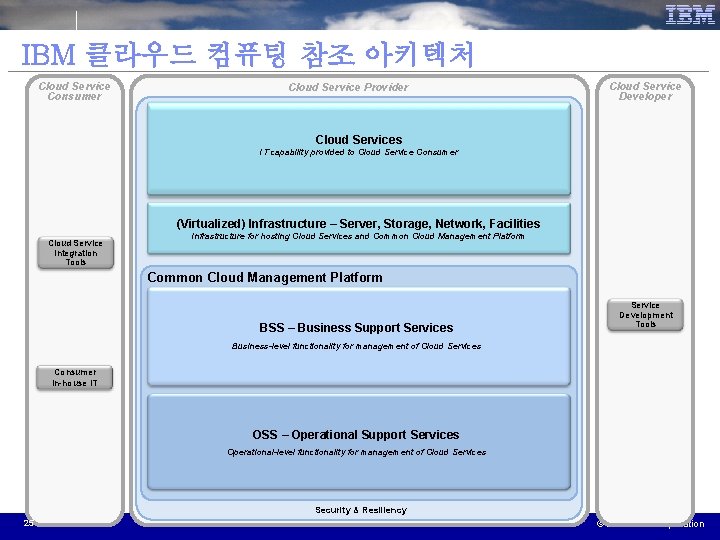
IBM 클라우드 컴퓨팅 참조 아키텍처 Cloud Service Consumer Cloud Service Provider Cloud Service Developer Cloud Services IT capability provided to Cloud Service Consumer (Virtualized) Infrastructure – Server, Storage, Network, Facilities Cloud Service Integration Tools Infrastructure for hosting Cloud Services and Common Cloud Management Platform BSS – Business Support Services Service Development Tools Business-level functionality for management of Cloud Services Consumer In-house IT OSS – Operational Support Services Operational-level functionality for management of Cloud Services Security & Resiliency 25 © 2011 IBM Corporation
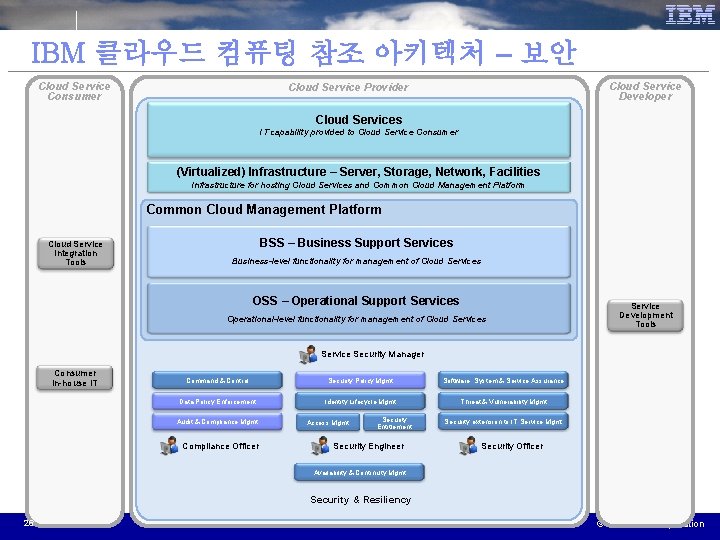
IBM 클라우드 컴퓨팅 참조 아키텍처 – 보안 Cloud Service Consumer Cloud Service Developer Cloud Service Provider Cloud Services IT capability provided to Cloud Service Consumer (Virtualized) Infrastructure – Server, Storage, Network, Facilities Infrastructure for hosting Cloud Services and Common Cloud Management Platform Cloud Service Integration Tools BSS – Business Support Services Business-level functionality for management of Cloud Services OSS – Operational Support Services Operational-level functionality for management of Cloud Services Service Development Tools Service Security Manager Consumer In-house IT Command & Control Security Policy Mgmt Software, System & Service Assurance Data Policy Enforcement Identity Lifecycle Mgmt Threat & Vulnerability Mgmt Audit & Compliance Mgmt Compliance Officer Access Mgmt Security Entitlement Security Engineer Security extension to IT Service Mgmt Security Officer Availability & Continuity Mgmt Security & Resiliency 26 © 2011 IBM Corporation
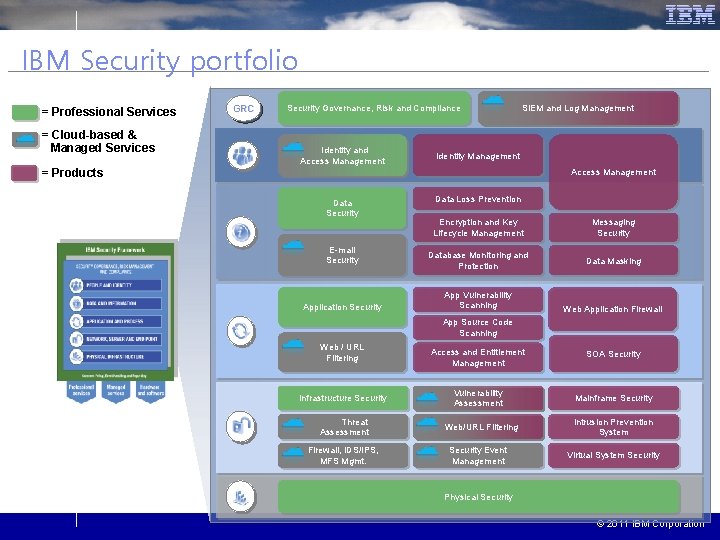
IBM Security portfolio = Professional Services = Cloud-based & Managed Services = Products GRC Security Governance, Risk and Compliance Identity and Access Management SIEM and Log Management Identity Management Access Management Data Security E-mail Security Application Security Data Loss Prevention Encryption and Key Lifecycle Management Messaging Security Database Monitoring and Protection Data Masking App Vulnerability Scanning Web Application Firewall App Source Code Scanning Web / URL Filtering Infrastructure Security Threat Assessment Firewall, IDS/IPS, MFS Mgmt. Access and Entitlement Management SOA Security Vulnerability Assessment Mainframe Security Web/URL Filtering Security Event Management Intrusion Prevention System Virtual System Security Physical Security © 2011 IBM Corporation
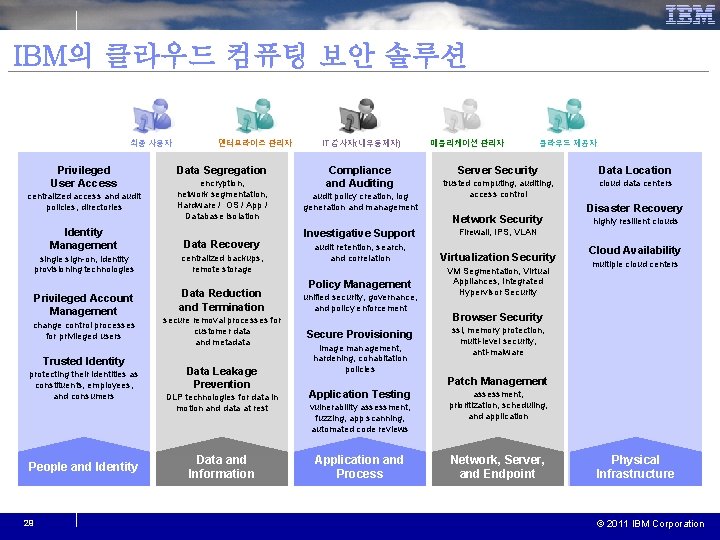
IBM의 클라우드 컴퓨팅 보안 솔루션 최종 사용자 Privileged User Access centralized access and audit policies, directories 엔터프라이즈 관리자 Data Segregation encryption, network segmentation, Hardware / OS / App / Database isolation Identity Management Data Recovery single sign-on, identity provisioning technologies centralized backups, remote storage Privileged Account Management change control processes for privileged users Trusted Identity protecting their identities as constituents, employees, and consumers People and Identity 29 Data Reduction and Termination secure removal processes for customer data and metadata Data Leakage Prevention IT 감사자(내부통제자) Compliance and Auditing audit policy creation, log generation and management 애플리케이션 관리자 클라우드 제공자 Server Security Data Location trusted computing, auditing, access control cloud data centers Network Security Investigative Support Firewall, IPS, VLAN audit retention, search, and correlation Virtualization Security Policy Management unified security, governance, and policy enforcement Secure Provisioning image management, hardening, cohabitation policies VM Segmentation, Virtual Appliances, Integrated Hypervisor Security Disaster Recovery highly resilient clouds Cloud Availability multiple cloud centers Browser Security ssl, memory protection, multi-level security, anti-malware Patch Management DLP technologies for data in motion and data at rest Application Testing Data and Information Application and Process vulnerability assessment, fuzzing, app scanning, automated code reviews assessment, prioritization, scheduling, and application Network, Server, and Endpoint Physical Infrastructure © 2011 IBM Corporation
Thank you! © 2011 IBM Corporation
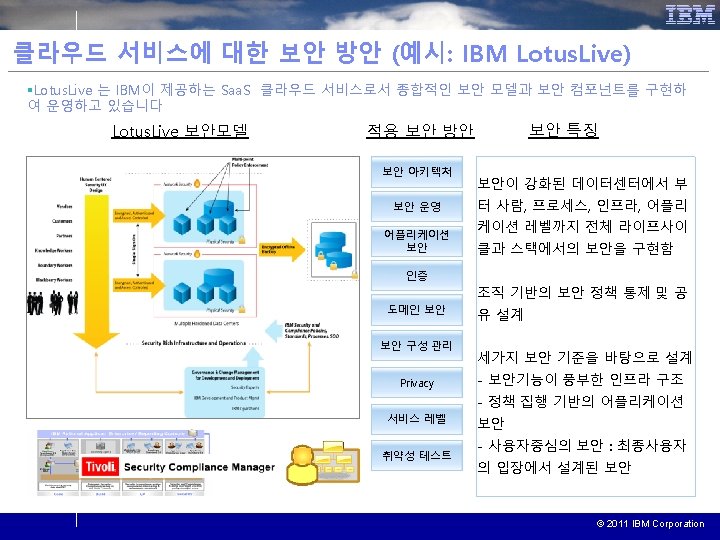
- Slides: 31