IBM Security Solutions for MSSPs IBM Security 2019

IBM Security Solutions for MSSPs IBM Security / © 2019 IBM Corporation

“Build it and customers will come” is not a sustainable strategy Leading MSSPs must juggle multiple business objectives to differentiate against the competition Innovate to stay ahead of the technology curve Offer well defined and cutting edge services IBM Security / © 2019 IBM Corporation Acquire and retain customers Manage enterprise products across multiple customers Achieve operational efficiency to drive margin 2
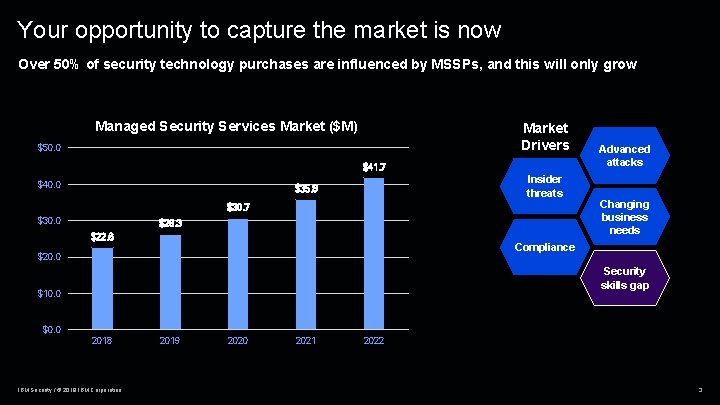
Your opportunity to capture the market is now Over 50% of security technology purchases are influenced by MSSPs, and this will only grow Managed Security Services Market ($M) Market Drivers $50. 0 $41. 7 $40. 0 Insider threats $35. 8 $30. 7 $30. 0 $26. 3 $22. 6 Advanced attacks Changing business needs Compliance $20. 0 Security skills gap $10. 0 $0. 0 2018 IBM Security / © 2019 IBM Corporation 2019 2020 2021 2022 3

Challenges facing your SOC Threats 93 Alerts Available analysts % SOC managers are not able 44 to triage all potential threats 3. 5 M Knowledge required Available time unfilled cybersecurity jobs by 2021 % of alerts go uninvestigated because analysts can’t keep up with volume IBM Security / © 2019 IBM Corporation 4
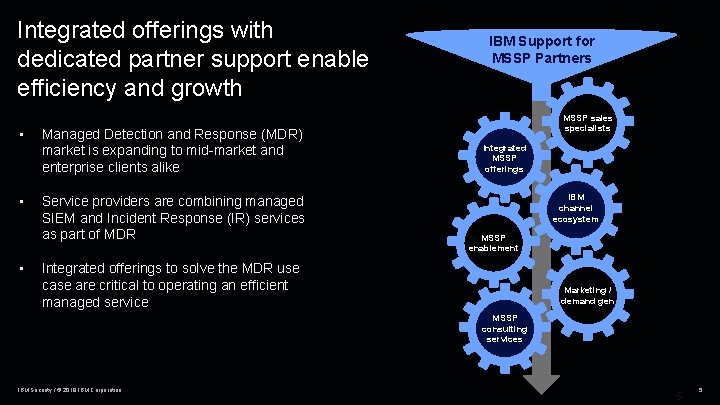
Integrated offerings with dedicated partner support enable efficiency and growth • • • Managed Detection and Response (MDR) market is expanding to mid-market and enterprise clients alike Service providers are combining managed SIEM and Incident Response (IR) services as part of MDR IBM Support for MSSP Partners MSSP sales specialists Integrated MSSP offerings IBM channel ecosystem MSSP enablement Integrated offerings to solve the MDR use case are critical to operating an efficient managed service Marketing / demand gen MSSP consulting services IBM Security / © 2019 IBM Corporation 5 5
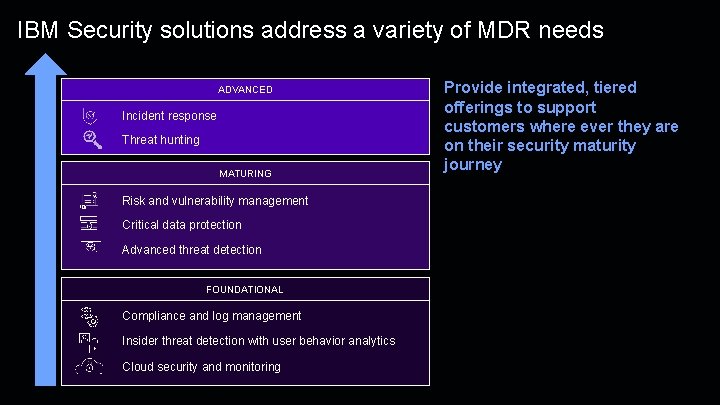
IBM Security solutions address a variety of MDR needs ADVANCED Incident response Threat hunting MATURING Risk and vulnerability management Critical data protection Advanced threat detection FOUNDATIONAL Compliance and log management Insider threat detection with user behavior analytics Cloud security and monitoring Provide integrated, tiered offerings to support customers where ever they are on their security maturity journey

Plan, build and run an effective SOC
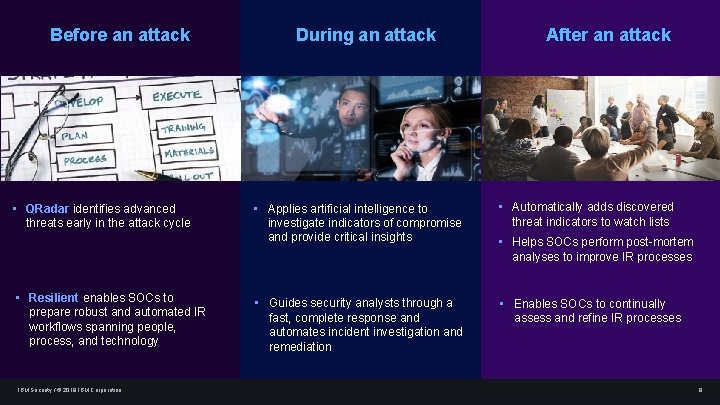
Before an attack • QRadar identifies advanced threats early in the attack cycle • Resilient enables SOCs to prepare robust and automated IR workflows spanning people, process, and technology IBM Security / © 2019 IBM Corporation During an attack After an attack • Applies artificial intelligence to investigate indicators of compromise and provide critical insights • Automatically adds discovered threat indicators to watch lists • Guides security analysts through a fast, complete response and automates incident investigation and remediation • Enables SOCs to continually assess and refine IR processes • Helps SOCs perform post-mortem analyses to improve IR processes 8

IBM QRadar helps address critical security challenges Complete visibility Endpoints Network activity Data activity Prioritized threats Automated investigations Proactive hunting Insider threats External threats Users and identities Threat intelligence Configuration information Cloud risks Vulnerabilities and threats Application activity Critical data Cloud platforms IBM Security / © 2019 IBM Corporation 9
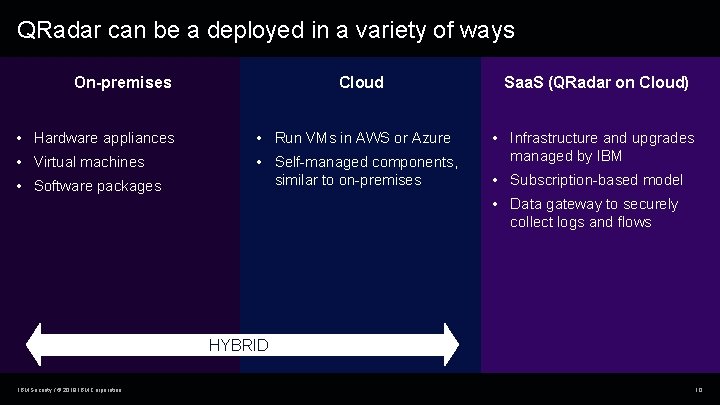
QRadar can be a deployed in a variety of ways Cloud On-premises • Hardware appliances • Run VMs in AWS or Azure • Virtual machines • Self-managed components, similar to on-premises • Software packages Saa. S (QRadar on Cloud) • Infrastructure and upgrades managed by IBM • Subscription-based model • Data gateway to securely collect logs and flows HYBRID IBM Security / © 2019 IBM Corporation 10
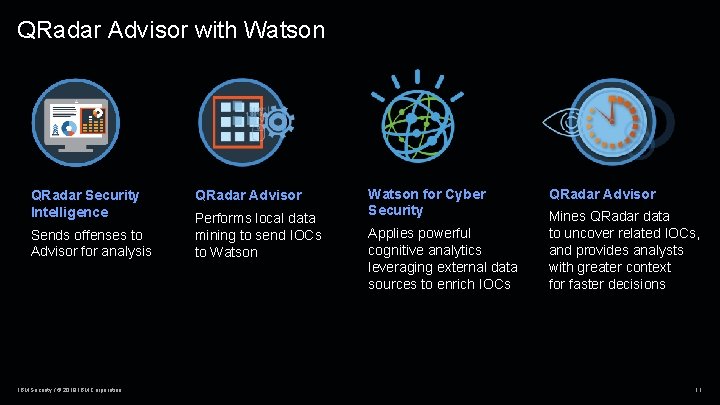
QRadar Advisor with Watson QRadar Security Intelligence Sends offenses to Advisor for analysis IBM Security / © 2019 IBM Corporation QRadar Advisor Performs local data mining to send IOCs to Watson for Cyber Security Applies powerful cognitive analytics leveraging external data sources to enrich IOCs QRadar Advisor Mines QRadar data to uncover related IOCs, and provides analysts with greater context for faster decisions 11
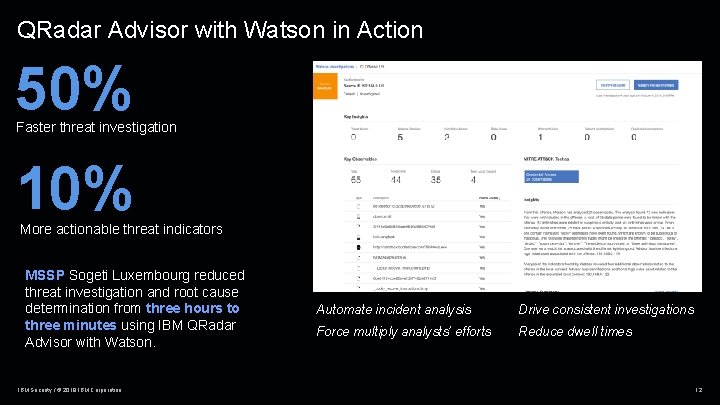
QRadar Advisor with Watson in Action 50% Faster threat investigation 10% More actionable threat indicators MSSP Sogeti Luxembourg reduced threat investigation and root cause determination from three hours to three minutes using IBM QRadar Advisor with Watson. IBM Security / © 2019 IBM Corporation Automate incident analysis Drive consistent investigations Force multiply analysts’ efforts Reduce dwell times 12
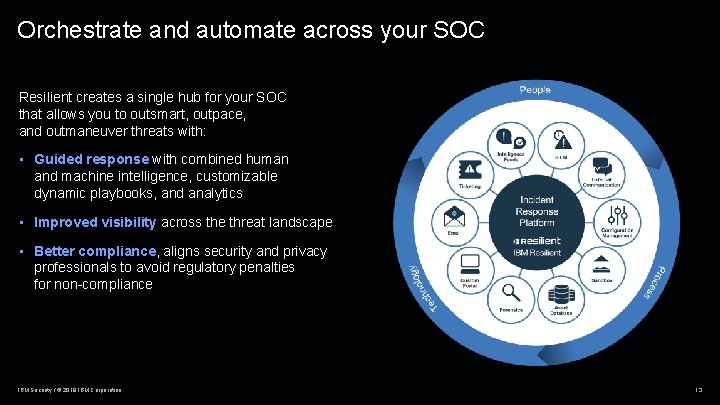
Orchestrate and automate across your SOC Resilient creates a single hub for your SOC that allows you to outsmart, outpace, and outmaneuver threats with: • Guided response with combined human and machine intelligence, customizable dynamic playbooks, and analytics • Improved visibility across the threat landscape • Better compliance, aligns security and privacy professionals to avoid regulatory penalties for non-compliance IBM Security / © 2019 IBM Corporation 13
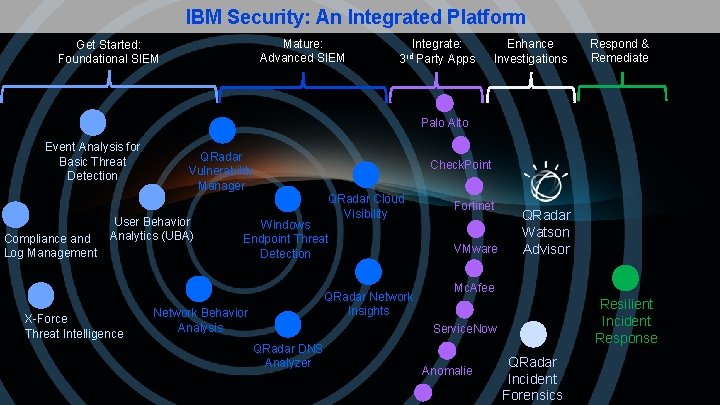
IBM Security: An Integrated Platform Mature: Advanced SIEM Get Started: Foundational SIEM Integrate: Party Apps 3 rd Enhance Investigations Respond & Remediate Palo Alto Event Analysis for Basic Threat Detection Compliance and Log Management QRadar Vulnerability Manager User Behavior Analytics (UBA) X-Force Threat Intelligence Check. Point QRadar Cloud Visibility Windows Endpoint Threat Detection QRadar Network Insights Network Behavior Analysis Fortinet VMware QRadar Watson Advisor Mc. Afee Resilient Incident Response Service. Now QRadar DNS Analyzer Anomalie QRadar Incident Forensics

THANK YOU FOLLOW US ON: ibm. com/securityintelligence. com ibm. com/security/community xforce. ibmcloud. com @ibmsecurity youtube/user/ibmsecuritysolutions © Copyright IBM Corporation 2019. All rights reserved. The information contained in these materials is provided for informational purposes only, and is provided AS IS without warranty of any kind, express or implied. Any statement of direction represents IBM's current intent, is subject to change or withdrawal, and represent only goals and objectives. IBM, the IBM logo, and other IBM products and services are trademarks of the International Business Machines Corporation, in the United States, other countries or both. Other company, product, or service names may be trademarks or service marks of others. Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to improper access from within and outside your enterprise. Improper access can result in information being altered, destroyed, misappropriated or misused or can result in damage to or misuse of your systems, including for use in attacks on others. No IT system or product should be considered completely secure and no single product, service or security measure can be completely effective in preventing improper use or access. IBM systems, products and services are designed to be part of a lawful, comprehensive security approach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM does not warrant that any systems, products or services are immune from, or will make your enterprise immune from, the malicious or illegal conduct of any party. IBM Security / © 2019 IBM Corporation 15
- Slides: 15