IBM QRadar on Cloud IBM security intelligence and
IBM QRadar on Cloud — IBM security intelligence and analytics delivered as a service September 2019
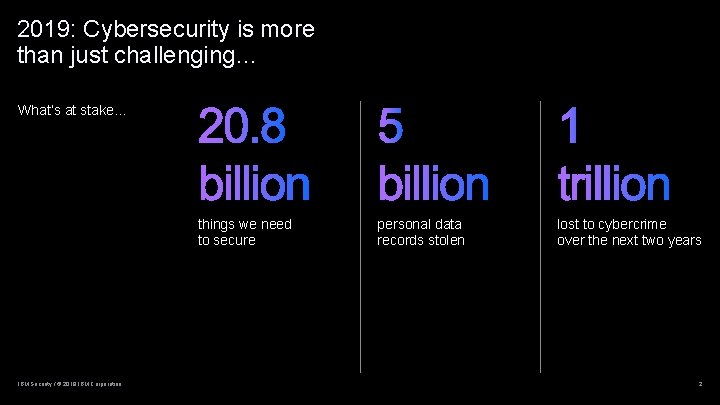
2019: Cybersecurity is more than just challenging… What’s at stake… things we need to secure IBM Security / © 2019 IBM Corporation personal data records stolen lost to cybercrime over the next two years 2
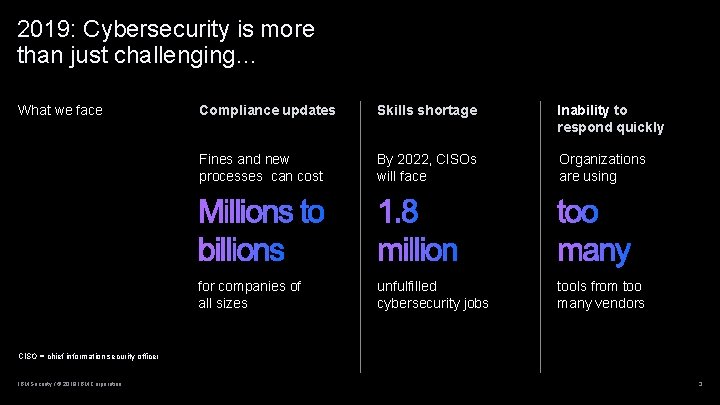
2019: Cybersecurity is more than just challenging… What we face Compliance updates Skills shortage Inability to respond quickly Fines and new processes can cost By 2022, CISOs will face Organizations are using for companies of all sizes unfulfilled cybersecurity jobs tools from too many vendors CISO = chief information security officer IBM Security / © 2019 IBM Corporation 3
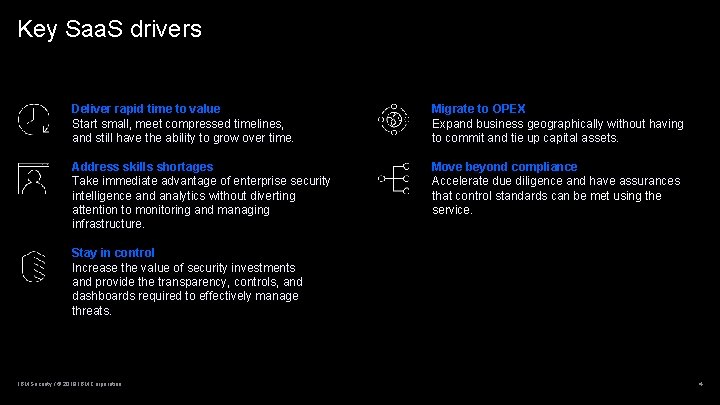
Key Saa. S drivers Deliver rapid time to value Start small, meet compressed timelines, and still have the ability to grow over time. Migrate to OPEX Expand business geographically without having to commit and tie up capital assets. Address skills shortages Take immediate advantage of enterprise security intelligence and analytics without diverting attention to monitoring and managing infrastructure. Move beyond compliance Accelerate due diligence and have assurances that control standards can be met using the service. Stay in control Increase the value of security investments and provide the transparency, controls, and dashboards required to effectively manage threats. IBM Security / © 2019 IBM Corporation 4
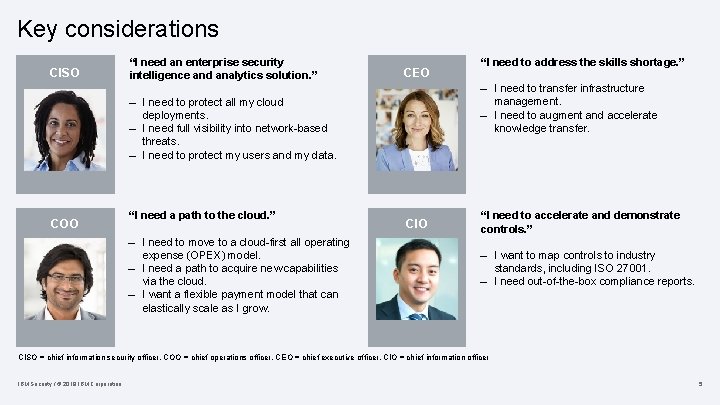
Key considerations CISO “I need an enterprise security intelligence and analytics solution. ” CEO – I need to transfer infrastructure management. – I need to augment and accelerate knowledge transfer. – I need to protect all my cloud deployments. – I need full visibility into network-based threats. – I need to protect my users and my data. COO “I need a path to the cloud. ” – I need to move to a cloud-first all operating expense (OPEX) model. – I need a path to acquire new capabilities via the cloud. – I want a flexible payment model that can elastically scale as I grow. “I need to address the skills shortage. ” CIO “I need to accelerate and demonstrate controls. ” – I want to map controls to industry standards, including ISO 27001. – I need out-of-the-box compliance reports. CISO = chief information security officer, COO = chief operations officer. CEO = chief executive officer, CIO = chief information officer IBM Security / © 2019 IBM Corporation 5
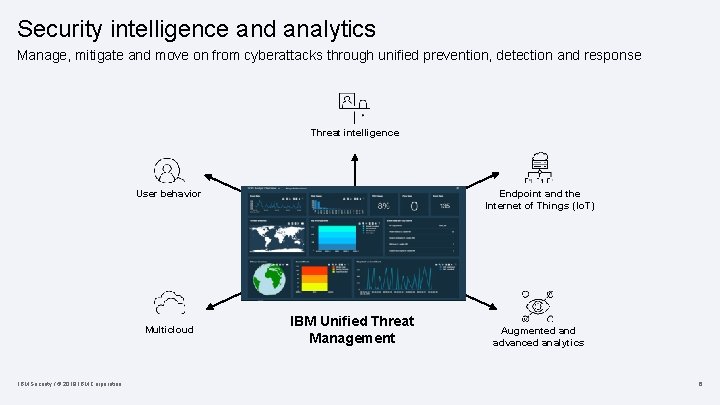
Security intelligence and analytics Manage, mitigate and move on from cyberattacks through unified prevention, detection and response Threat intelligence User behavior Multicloud IBM Security / © 2019 IBM Corporation Endpoint and the Internet of Things (Io. T) IBM Unified Threat Management Augmented and advanced analytics 6
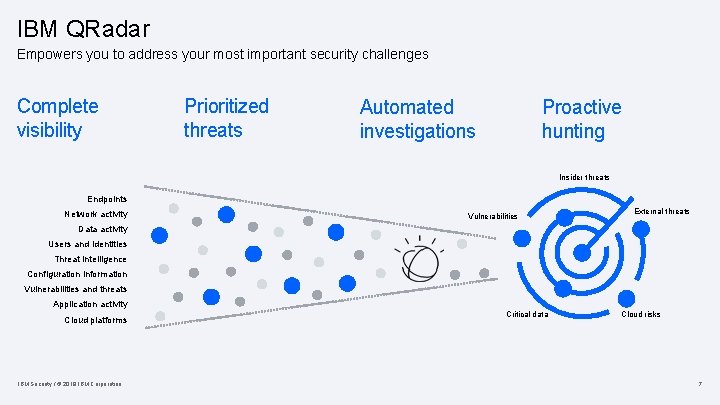
IBM QRadar Empowers you to address your most important security challenges Complete visibility Prioritized threats Automated investigations Proactive hunting Insider threats Endpoints Network activity Vulnerabilities External threats Data activity Users and identities Threat intelligence Configuration information Vulnerabilities and threats Application activity Cloud platforms IBM Security / © 2019 IBM Corporation Critical data Cloud risks 7
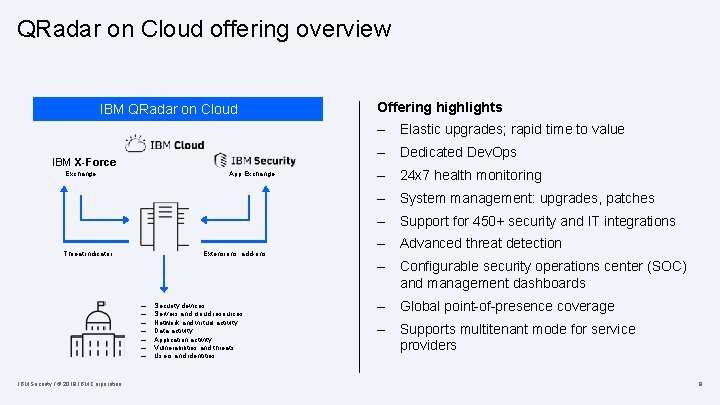
QRadar on Cloud offering overview IBM QRadar on Cloud Offering highlights – Elastic upgrades; rapid time to value – Dedicated Dev. Ops IBM X-Force App Exchange – 24 x 7 health monitoring – System management: upgrades, patches – Support for 450+ security and IT integrations Threat indicator Extensions, add-ons – Advanced threat detection – Configurable security operations center (SOC) and management dashboards – – – – IBM Security / © 2019 IBM Corporation Security devices Servers and cloud resources Network and virtual activity Data activity Application activity Vulnerabilities and threats Users and identities – Global point-of-presence coverage – Supports multitenant mode for service providers 8

QRadar on Cloud: A global footprint – Globally-distributed – Resiliency and redundancy by default – Built on securityrich IBM Cloud™ infrastructure San Jose London Toronto Frankfurt Dallas São Paulo IBM Security / © 2019 IBM Corporation Sydney 9
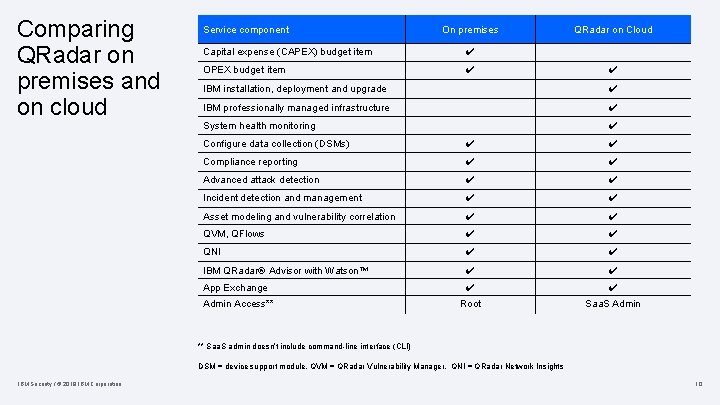
Comparing QRadar on premises and on cloud Service component On premises Capital expense (CAPEX) budget item ✔ OPEX budget item ✔ QRadar on Cloud ✔ IBM installation, deployment and upgrade ✔ IBM professionally managed infrastructure ✔ System health monitoring ✔ Configure data collection (DSMs) ✔ ✔ Compliance reporting ✔ ✔ Advanced attack detection ✔ ✔ Incident detection and management ✔ ✔ Asset modeling and vulnerability correlation ✔ ✔ QVM, QFlows ✔ ✔ QNI ✔ ✔ IBM QRadar® Advisor with Watson™ ✔ ✔ App Exchange ✔ ✔ Root Saa. S Admin Access** ** Saa. S admin doesn’t include command-line interface (CLI) DSM = device support module, QVM = QRadar Vulnerability Manager, QNI = QRadar Network Insights IBM Security / © 2019 IBM Corporation 10

Business model IBM Security / © 2019 IBM Corporation 11
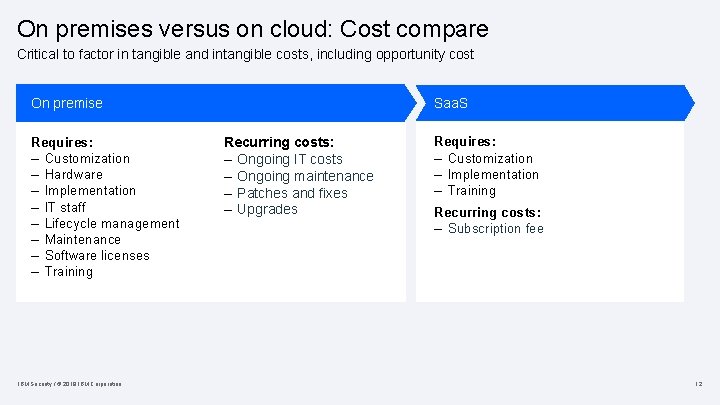
On premises versus on cloud: Cost compare Critical to factor in tangible and intangible costs, including opportunity cost On premise Requires: – Customization – Hardware – Implementation – IT staff – Lifecycle management – Maintenance – Software licenses – Training IBM Security / © 2019 IBM Corporation Saa. S Recurring costs: – Ongoing IT costs – Ongoing maintenance – Patches and fixes – Upgrades Requires: – Customization – Implementation – Training Recurring costs: – Subscription fee 12

On cloud: An expandedbenefit view Future extensibility Platform and use case scalability Resource reallocation Contracting simplicity Accelerated time to value IBM Security / © 2019 IBM Corporation Elastic use Lowered deployment costs Cost transparency Lowered maintenance costs Expand & burst from on premises 13

Address the skills gap IBM Security / © 2019 IBM Corporation 14
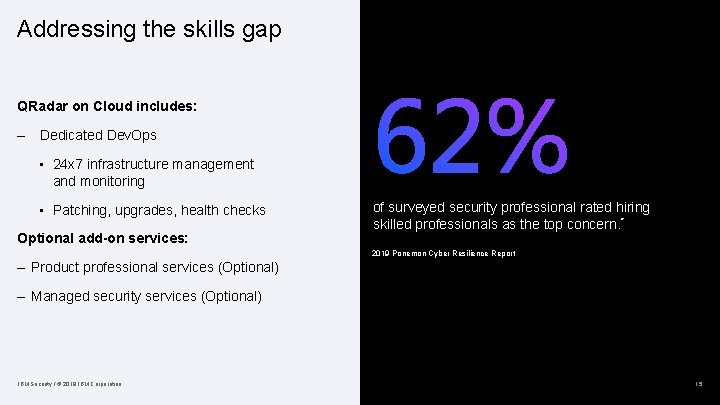
Addressing the skills gap QRadar on Cloud includes: – Dedicated Dev. Ops • 24 x 7 infrastructure management and monitoring • Patching, upgrades, health checks Optional add-on services: of surveyed security professional rated hiring skilled professionals as the top concern. * 2019 Ponemon Cyber Resilience Report – Product professional services (Optional) – Managed security services (Optional) IBM Security / © 2019 IBM Corporation 15

Integrating QRadar on Cloud with managed security services (MSS) – QRadar on Cloud powers a growing number of enterprise SOCs – MSSPs can extend the platform with fully managed and comanaged services providing 24 x 7 eyes-on-glass security threat monitoring and response – Domain-aware infrastructure supports management of multiple customers in a single QRadar on Cloud deployment MSSPs = managed security service providers IBM Security / © 2019 IBM Corporation 16

Stay in control IBM Security / © 2019 IBM Corporation 17
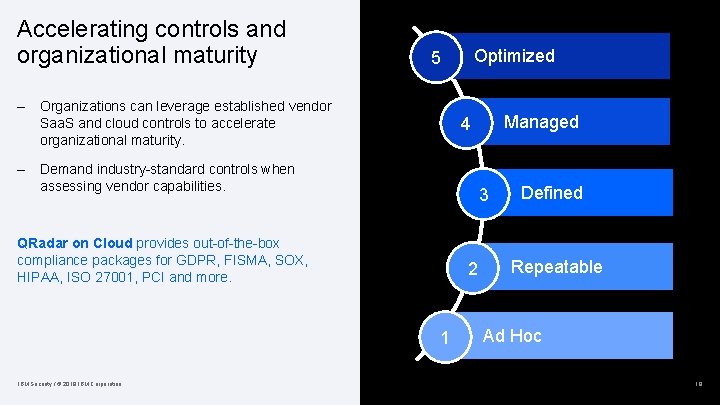
Accelerating controls and organizational maturity Optimized 5 – Organizations can leverage established vendor Saa. S and cloud controls to accelerate organizational maturity. – Demand industry-standard controls when assessing vendor capabilities. 3 QRadar on Cloud provides out-of-the-box compliance packages for GDPR, FISMA, SOX, HIPAA, ISO 27001, PCI and more. 2 1 IBM Security / © 2019 IBM Corporation Managed 4 Defined Repeatable Ad Hoc 18

Optional add-ons IBM Security / © 2019 IBM Corporation 19
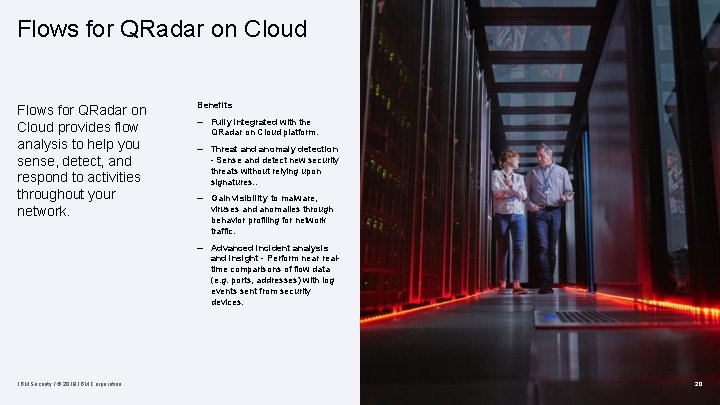
Flows for QRadar on Cloud provides flow analysis to help you sense, detect, and respond to activities throughout your network. Benefits – Fully integrated with the QRadar on Cloud platform. – Threat and anomaly detection - Sense and detect new security threats without relying upon signatures. . – Gain visibility to malware, viruses and anomalies through behavior profiling for network traffic. – Advanced incident analysis and insight - Perform near realtime comparisons of flow data (e. g. ports, addresses) with log events sent from security devices. IBM Security / © 2019 IBM Corporation 20
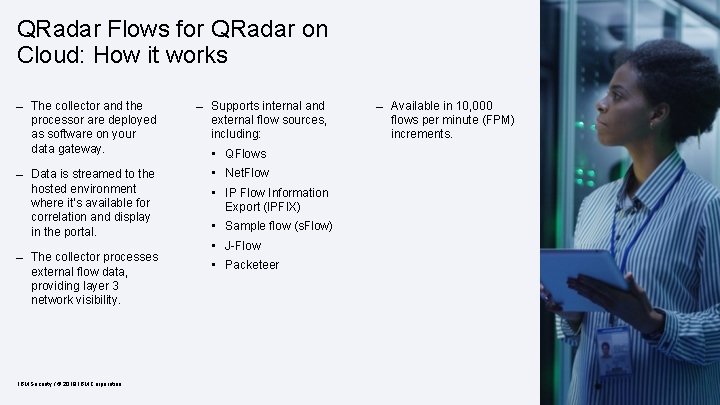
QRadar Flows for QRadar on Cloud: How it works – The collector and the processor are deployed as software on your data gateway. – Data is streamed to the hosted environment where it’s available for correlation and display in the portal. – The collector processes external flow data, providing layer 3 network visibility. IBM Security / © 2019 IBM Corporation – Supports internal and external flow sources, including: – Available in 10, 000 flows per minute (FPM) increments. • QFlows • Net. Flow • IP Flow Information Export (IPFIX) • Sample flow (s. Flow) • J-Flow • Packeteer 21
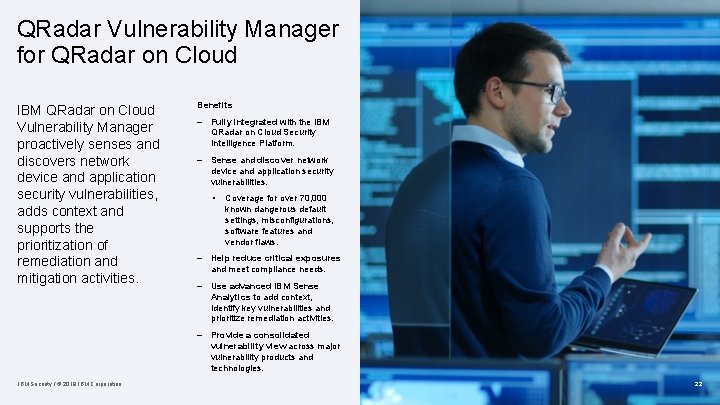
QRadar Vulnerability Manager for QRadar on Cloud IBM QRadar on Cloud Vulnerability Manager proactively senses and discovers network device and application security vulnerabilities, adds context and supports the prioritization of remediation and mitigation activities. IBM Security / © 2019 IBM Corporation Benefits – Fully integrated with the IBM QRadar on Cloud Security Intelligence Platform. – Sense and discover network device and application security vulnerabilities. • Coverage for over 70, 000 known dangerous default settings, misconfigurations, software features and vendor flaws. – Help reduce critical exposures and meet compliance needs. – Use advanced IBM Sense Analytics to add context, identify key vulnerabilities and prioritize remediation activities. – Provide a consolidated vulnerability view across major vulnerability products and technologies. 22
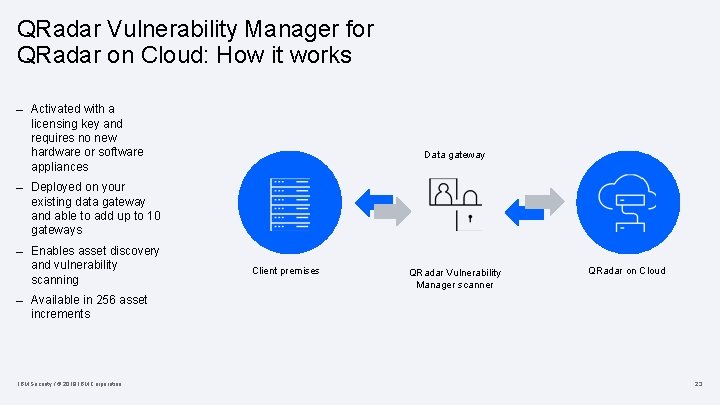
QRadar Vulnerability Manager for QRadar on Cloud: How it works – Activated with a licensing key and requires no new hardware or software appliances Data gateway – Deployed on your existing data gateway and able to add up to 10 gateways – Enables asset discovery and vulnerability scanning Client premises QRadar Vulnerability Manager scanner QRadar on Cloud – Available in 256 asset increments IBM Security / © 2019 IBM Corporation 23
IBM Security Product Professional Services IBM specialists remotely deliver product professional services. Deployment services – 40 hours per part; no SOW required – Includes an IBM Engagement Manager to schedule kick off calls Cloud optimization services – Eight days per year; two-day engagements Customer parser – Provides the development of custom parsers for supporting clients’ non-standard log source types to be sent to the cloud service IBM Security / © 2019 IBM Corporation 24

Summary IBM Security / © 2019 IBM Corporation 25
IBM Security Product Professional Services IBM specialists remotely deliver product professional services. – Cloud security product page: ibm. com/securityintelligence/qradar/securing-the-cloud – IBM Security Community: ibm. com/security/community – IBM Security App Exchange: exchange. xforce. ibmcloud. com/hub/ – IBM Knowledge Center: ibm. com/support/knowledgecenter/en – @ibmsecurity – securityintelligence. com Request a trial of IBM QRadar on Cloud Take a 14 day test drive of our detection capabilities and learn about QRadar ibm. com/us-en/marketplace/hosted-securityintelligence – youtube/user/ibmsecuritysolutions IBM Security / © 2019 IBM Corporation 26

Questions IBM Security / © 2019 IBM Corporation 27
Thank you Follow us on: ibm. com/securityintelligence. com ibm. com/security/community xforce. ibmcloud. com @ibmsecurity youtube/user/ibmsecuritysolutions © Copyright IBM Corporation 2019. All rights reserved. The information contained in these materials is provided for informational purposes only, and is provided AS IS without warranty of any kind, express or implied. Any statement of direction represents IBM’s current intent, is subject to change or withdrawal, and represent only goals and objectives. IBM, the IBM logo, and other IBM products and services are trademarks of the International Business Machines Corporation, in the United States, other countries or both. Other company, product, or service names may be trademarks or service marks of others. Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to improper access from within and outside your enterprise. Improper access can result in information being altered, destroyed, misappropriated or misused or can result in damage to or misuse of your systems, including for use in attacks on others. No IT system or product should be considered completely secure and no single product, service or security measure can be completely effective in preventing improper use or access. IBM systems, products and services are designed to be part of a lawful, comprehensive security approach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM does not warrant that any systems, products or services are immune from, or will make your enterprise immune from, the malicious or illegal conduct of any party.

- Slides: 29