I can be You Questioning the use of
I can be You: Questioning the use of Keystroke Dynamics as Biometrics Tey Chee Meng, Payas Gupta, Debin Gao Ke Chen
Outline • • • Introduction Keystroke biometrics Experimental Design Experimental Results Conclusion
Authentication using Biometrics • Physiological biometric: – – facial features hand geometry Fingerprints iris scans • Behavioral biometric: – Signatures – Handwriting – Typing patterns (i. e. keystroke dynamics)
Is Keystroke Biometrics Unique? • If imitation is possible, then keystroke dynamics would be unsuitable for use as a biometrics feature. • it is possible to imitate someone else’s keystroke typing if appropriate feedback is provided?
Keystroke Dynamics Keystroke dynamics refer to information about the typing pattern. pressing and releasing of a keystroke pair (ka, kb) results in 4 timings which are of interest to keystroke biometrics systems
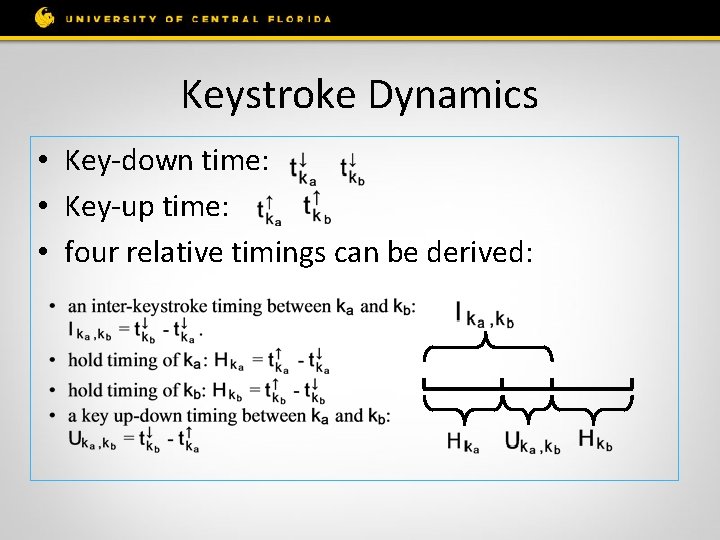
Keystroke Dynamics • Key-down time: • Key-up time: • four relative timings can be derived:
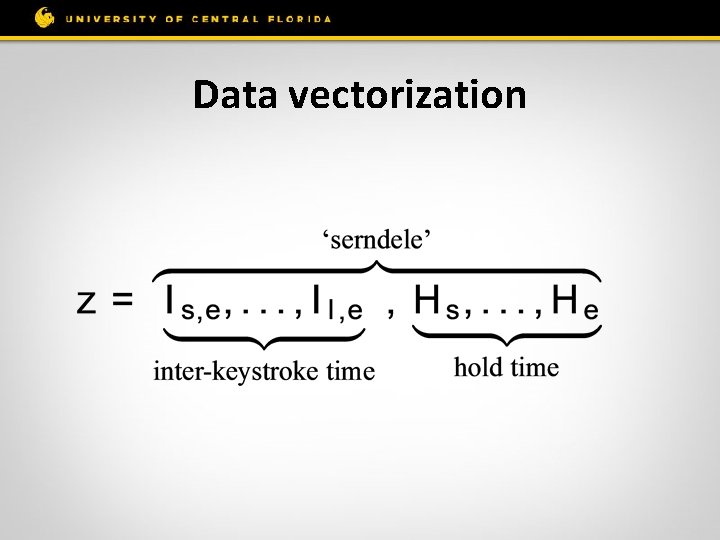
Data vectorization
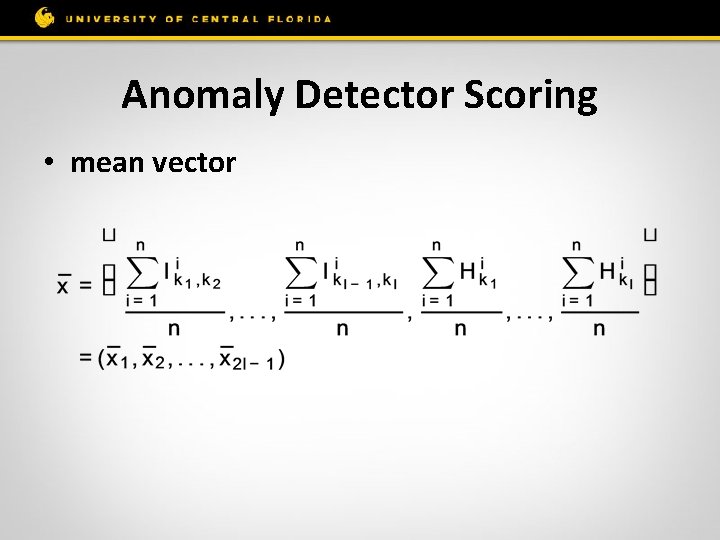
Anomaly Detector Scoring • mean vector
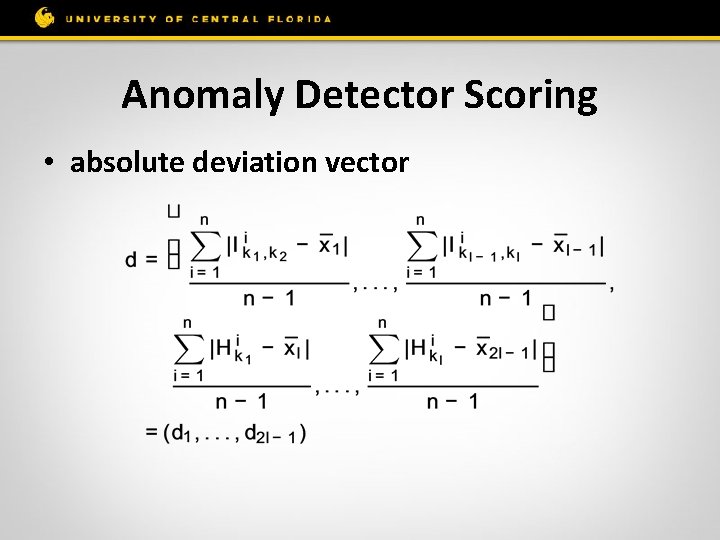
Anomaly Detector Scoring • absolute deviation vector
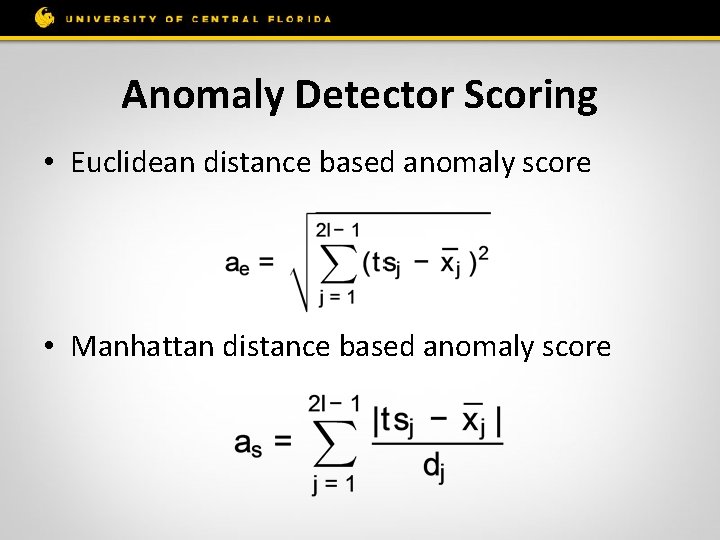
Anomaly Detector Scoring • Euclidean distance based anomaly score • Manhattan distance based anomaly score
Anomaly Detection Threshold • FRR: false rejection rate, decrease as threshold sets higher • FAR: false acceptance rate, increase as threshold sets higher • EER: equal error rate where FRR=FAR
Experiment Design • Attack scenarios – the attacker is able to extract the victim pattern from a compromised biometrics database. – the attacker may be able to capture samples of the victim’s keystrokes as she is authenticating (e. g. by installing a key- logger).
Choice of Password • “serndele” – minimize finger movements on a standard US keyboard. • “ths. ou. R 2” – chosen to maximize finger movements and therefore difficulty of typing.
Experiment 1 (e 1) • Training Data Collection 88 participants were asked to submit 200 samples for each of the two passwords using an existing keystroke dynamics based authentication system.
Experiment 2 (e 2) • Imitation using Euclidean distance 30 minutes imitation task: 84 participants played the role of attackers. 10 victims were randomly chosen from e 1. Each attacker was randomly assigned one of the 10 victims, and was given the victim’s mean vector for. Attackers gets real-time feedback of the Euclidean distance based anomaly score.
Experiment 3 (e 3 a) • Investigate the additional imitation session with Euclidean distance 14 best attackers were chosen from e 2 to perform the same imitation task in e 2 for only 20 minutes.
Experiment 4 (e 3 b) • Investigate the imitation performance of highly motivated attackers in optimal environment Feedback is based on full victim typing pattern Information (Manhattan distance and absolute deviation)
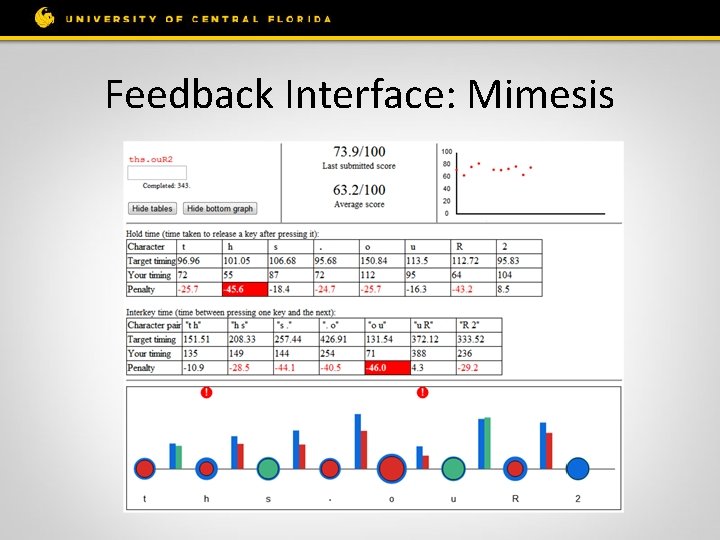
Feedback Interface: Mimesis
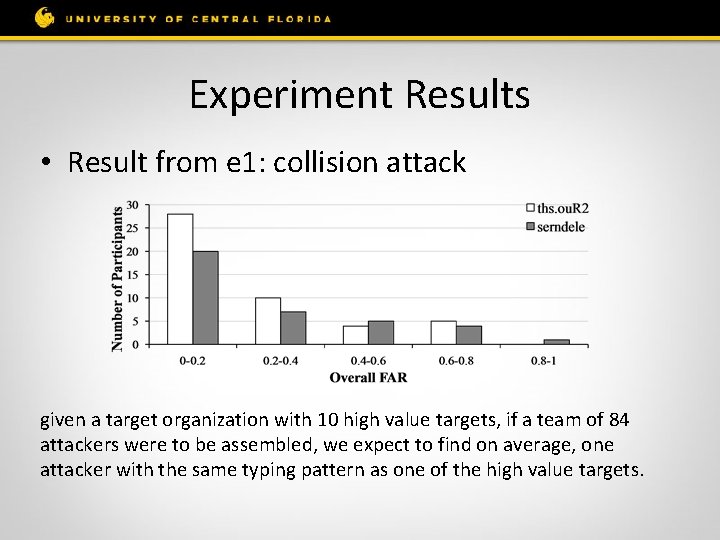
Experiment Results • Result from e 1: collision attack given a target organization with 10 high value targets, if a team of 84 attackers were to be assembled, we expect to find on average, one attacker with the same typing pattern as one of the high value targets.
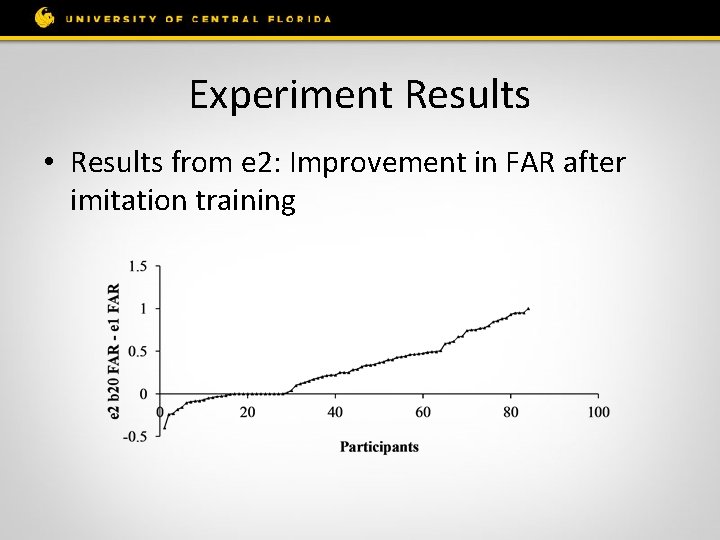
Experiment Results • Results from e 2: Improvement in FAR after imitation training
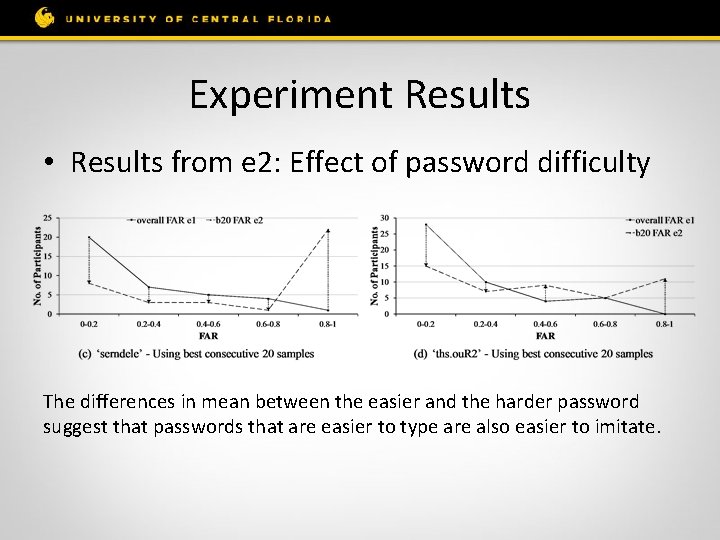
Experiment Results • Results from e 2: Effect of password difficulty The differences in mean between the easier and the harder password suggest that passwords that are easier to type are also easier to imitate.
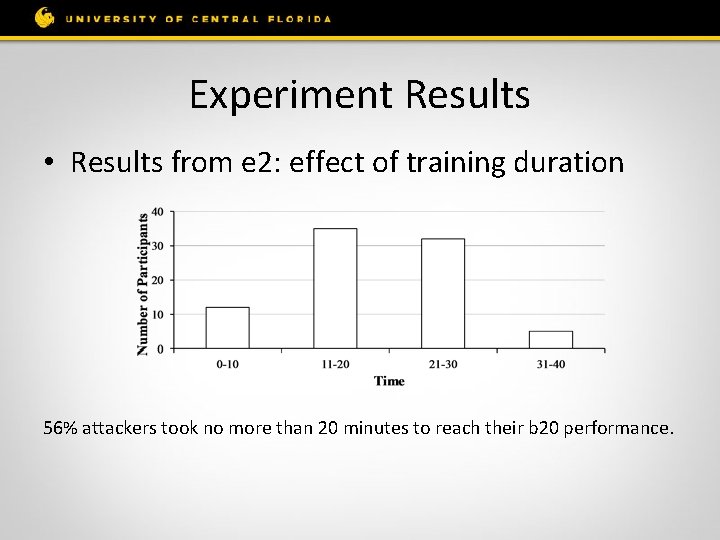
Experiment Results • Results from e 2: effect of training duration 56% attackers took no more than 20 minutes to reach their b 20 performance.
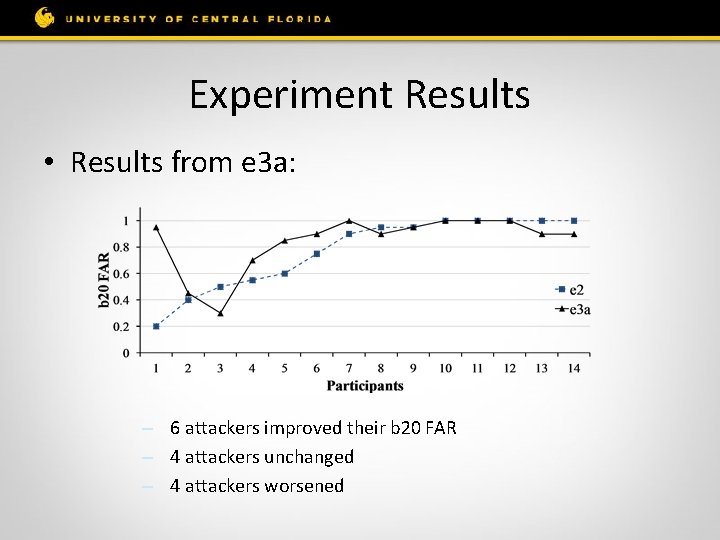
Experiment Results • Results from e 3 a: – 6 attackers improved their b 20 FAR – 4 attackers unchanged – 4 attackers worsened
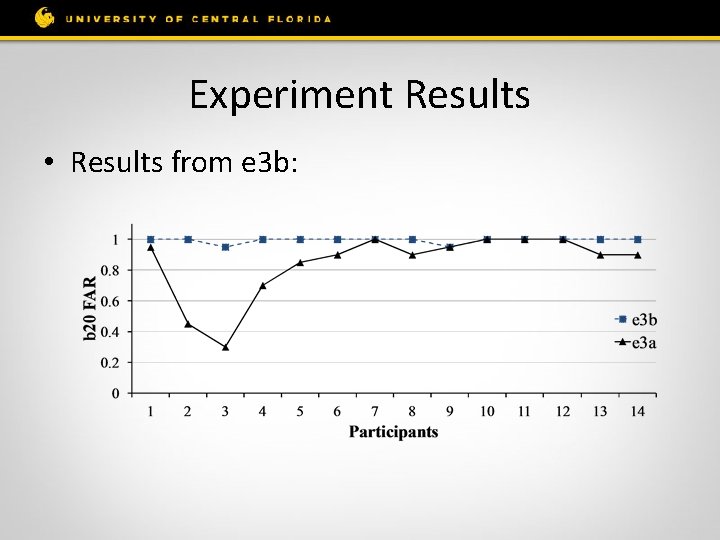
Experiment Results • Results from e 3 b:
Experiment Results • Factors affecting imitation outcome – Gender: male performs significantly better than females – Therefore there exists a weak correlation between the imitation outcome and the similarity between the attacker and victim’s typing pattern – Typing speed, keyboard, Number of trials per minute are not affecting factors
Conclusion • A user’s typing pattern can be imitated – Trained with incomplete model of the victim’s typing pattern, an attacker’s success rate is around 0. 52 – The best attacker increases FAR to 1 after training – When the number of attackers and victims are sizeable, chance of natural collision is significant

Conclusion • Easier passwords are easily imitated • Males are better imitators
Questions?
- Slides: 28