HUMAN RIGHTS IN CYBERSPACE The Hague Process Courses
HUMAN RIGHTS IN CYBERSPACE The Hague Process: Courses on the International Law Applicable to Cyber Operations Santiago, Chile 8– 12 May 2017
State Pronouncements on IHRL in Cyberspace • UN GGE 2013 report • “State efforts to address the security of ICTs must go hand-inhand with respect for human rights and fundamental freedoms set forth in the Universal Declaration of Human Rights and other international instruments. ” • UN GGE 2015 report • “[T]he Group identified as of central importance the commitments of States to. . . respect for human rights and fundamental freedoms; . . . ” “States must comply with their obligations under international law to respect and protect human rights and fundamental freedoms” • Human Rights Council, 2016 • “[T]he same rights that people have offline must also be protected online” 2

Key Sources of IHRL Relevant for Cyber • Global treaties • International Covenant on Civil and Political Rights • International Covenant on Economic, Social and Cultural Rights • Regional treaties • American Convention on Human Rights • European Convention for the Protection of Human Rights and Fundamental Freedoms • Charter of Fundamental Rights of the European Union • African Charter on Human and Peoples’ Rights • Customary IHRL 3
Applicability of IHRL • Treaties: Bind only Parties • Customary: Binds all States • Issues • Ascertaining customary nature • Which sources reflect customary law? • E. g. , ICCPR, ICESR, UDHR? • Extraterritorial applicability? 4
Types of IHRL obligations • Respect • State must not violate • Negative obligation • Example: State must not monitor the communications of an ethnic minority for the purpose of persecuting them • Example: State must not direct a hosting service provider to stop offering services to an individual who manages a website that reports on the government’s corruption 5
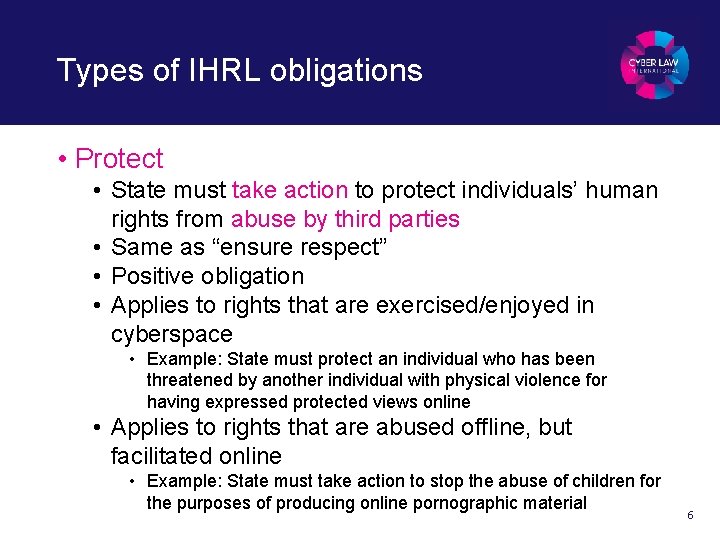
Types of IHRL obligations • Protect • State must take action to protect individuals’ human rights from abuse by third parties • Same as “ensure respect” • Positive obligation • Applies to rights that are exercised/enjoyed in cyberspace • Example: State must protect an individual who has been threatened by another individual with physical violence for having expressed protected views online • Applies to rights that are abused offline, but facilitated online • Example: State must take action to stop the abuse of children for the purposes of producing online pornographic material 6
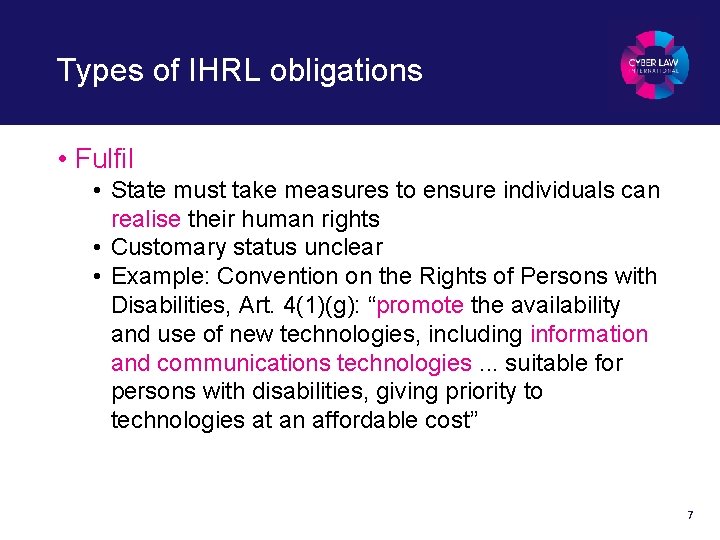
Types of IHRL obligations • Fulfil • State must take measures to ensure individuals can realise their human rights • Customary status unclear • Example: Convention on the Rights of Persons with Disabilities, Art. 4(1)(g): “promote the availability and use of new technologies, including information and communications technologies. . . suitable for persons with disabilities, giving priority to technologies at an affordable cost” 7
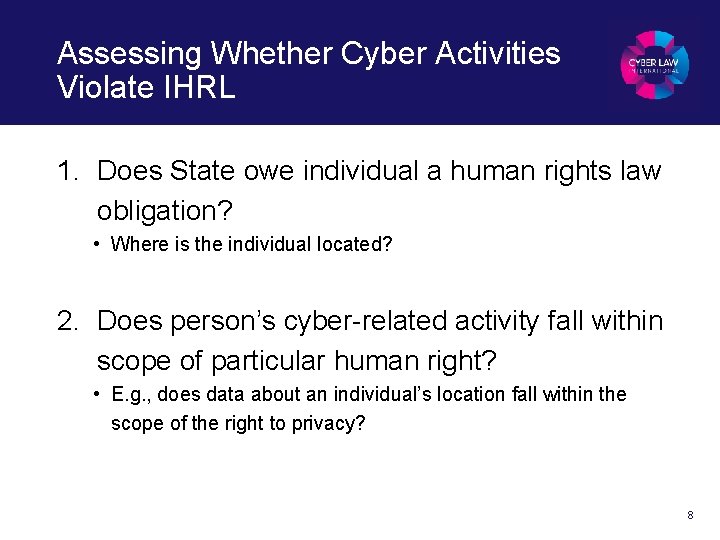
Assessing Whether Cyber Activities Violate IHRL 1. Does State owe individual a human rights law obligation? • Where is the individual located? 2. Does person’s cyber-related activity fall within scope of particular human right? • E. g. , does data about an individual’s location fall within the scope of the right to privacy? 8
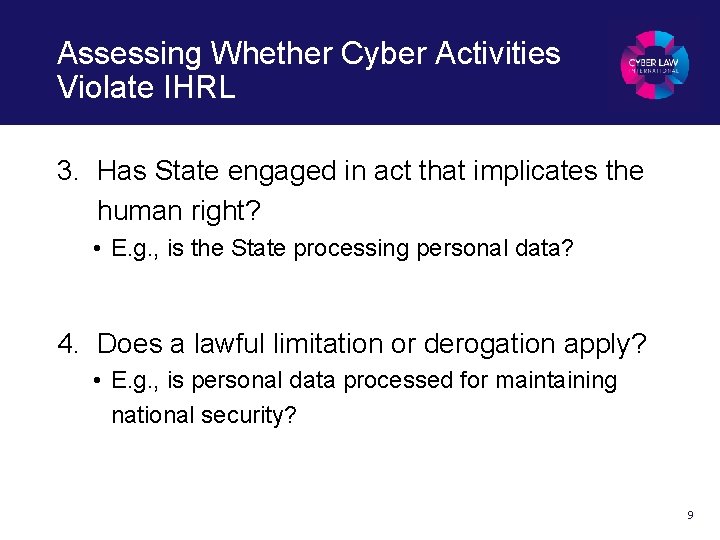
Assessing Whether Cyber Activities Violate IHRL 3. Has State engaged in act that implicates the human right? • E. g. , is the State processing personal data? 4. Does a lawful limitation or derogation apply? • E. g. , is personal data processed for maintaining national security? 9
Applicability of IHRL to Cyber Activities • Within State’s territory • Extraterritorially: “Power or effective control” • Over territory (spacial model) • Example: Occupied territory • Over individual (personal model) • Example: Detained person • States that reject extraterritorial application? 10
Cyber-Specific Scenarios • Security services capture a person abroad and read her emails on her phone versus • Security services hack into the person’s phone remotely and read her emails • A State captures the communications of an individual who lives in that State while the individual is at home versus • The State captures the individual’s communications while he is on holiday abroad 11
Extraterritoriality in Cyberspace • Cyber challenges traditional approach to extraterritoriality • Is approach sustainable? • Example: Tallinn Manual 2. 0 “a few Experts’” approach: if the exercise or enjoyment of a right by an individual is within State’s power or effective control, State owes IHRL obligation • Majority view: Not lex lata 12
Cyber-Relevant Human Rights • Examples: • Freedom of expression • Privacy • Freedom of opinion • Due process • Association and peaceful assembly • Protection from defamation 13
Freedom of Cyber Expression • Recognised in various treaties • Separate from the freedom of opinion • ICCPR definition: “Everyone shall have the right to freedom of expression; this right shall include freedom to seek, receive and impart information and ideas of all kinds, regardless of frontiers, either orally, in writing or in print, in the form of art, or through any other media of his choice. ” 14
Freedom of Cyber Expression • Examples: • • Websites Blogs Online forums Social media posts Skype, Viber, Whatsapp calls Text messages Etc. 15
Privacy in Cyberspace • Recognised in various treaties • ICCPR definition: “No one shall be subjected to arbitrary or unlawful interference with his privacy, family, home or correspondence, nor to unlawful attacks on his honour and reputation. ” 16
Privacy in Cyberspace • Scope • Confidentiality of communications • Personal data • Confidentiality: communications must be “delivered to the addressee without being opened or otherwise read” • General Comment No. 16, para. 8 • Is email metadata part of a communication? • Personal data: no generally accepted definition • Health-related data clearly qualifies 17
Privacy In Cyberspace • Machine inspection based on algorithms of communications / personal data without human access? • Mere collection of communications / personal data for potential future examination? • Is the enjoyment of the right dependent on a reasonable expectation of privacy? 18
Cyber-Specific Human Rights • Human right to anonymity? • Human right to access the internet? • Human right to be forgotten? 19
Limitations • No limitations on absolute rights • Examples: freedom from torture, freedom from slavery, right to hold an opinion • Limitations are distinct from derogation • Requirements for limitations: • • • Legitimate purpose Necessary Proportionate Authorised by law Non-discriminatory • Requirements apply to both the obligation to respect and to protect 20
Requirements for Limitations • Legitimate purpose • • • Protection of rights and reputations of others National security Public order Public health or morals Example: monitoring certain online communications in order to counter terrorism • Necessary • Example: Blocking / sinkholing online communications that incite to genocide 21
![Requirements for Limitations • Proportionate • “[R]estrictive measures. . . the least intrusive instrument Requirements for Limitations • Proportionate • “[R]estrictive measures. . . the least intrusive instrument](http://slidetodoc.com/presentation_image/3a0154bb0763128f435c6ca28679c4ce/image-22.jpg)
Requirements for Limitations • Proportionate • “[R]estrictive measures. . . the least intrusive instrument amongst those which might achieve their protective function; they must be proportionate to the interest to be protected. . . ” – General Comment No. 27, para. 14. • Example: Is it proportionate to engage in mass collection of online communications? 22
Requirements for Limitations • Authorised by law • Precise and clear to put affected individuals on notice • Does the authorisation need to be set forth in domestic law or does international law suffice? • Example: A law that sets forth the legal basis for online surveillance must outline the conditions under which the State may engage in such surveillance 23
Requirements for Limitations • Non-discriminatory • Distinctions, exclusions, restrictions, or preferences for the purpose or effect of nullifying or impairing the recognition, enjoyment, or exercise, on an equal footing, of rights and freedoms. Can be based on, e. g. : • • • Race Colour Sex Language Religion Political or other opinion National or social origin Property Birth • Example: Disrupting internet services in a region populated by a particular ethnic group 24

QUESTIONS?
- Slides: 25