HTTP Authentication Basic and Digest Access Authentication rfc
HTTP Authentication: Basic and Digest Access Authentication rfc 2617
Contents n n Access Authentication Framework Basic Access Authentication Digest Access Authentication Specification of Digest Headers WWW-Authentication header ¨ Authorization Request header ¨ Authentication-Info header ¨ n n Digest Operation Example
Access Authentication Framework Simple challenge-response authentication mechanism n Token – user identifying information n Realm directive – protection space n Credential n Checksum & Hash n
Basic Access Authentication n Authentication with user ID/password ¨ Cleartext based mechanism ¨ No encryption method
Digest Access Authentication n 목적 BAA의 취약점을 보완(flaws of cleartext) ¨ No message encryption ¨ n Overall Operation Simple challenge-response paradigm ¨ Challenge use nonce value ¨ Response contains a checksum ¨ n n Default, MD 5 Username, password, given nonce value, HTTP method, requested URI
Specification of Digest Headers n WWW-Authentication header ¨ n Authorization Request header ¨ n 서버가 access-protected object에 대한 request를 수신했을 때, acceptable Authorization header가 없을 경우, 전송 서버로부터 WWW-Authentication header를 수신한 후 다시 access를 요청하기 위해 전송 Authentication-Info header ¨ 성공적인 인증을 위해 서버에 의해 전송되는 정보
![WWW-Authentication header 1/3 challenge = "Digest" digest-challenge = 1#( realm | [ domain ] WWW-Authentication header 1/3 challenge = "Digest" digest-challenge = 1#( realm | [ domain ]](http://slidetodoc.com/presentation_image_h2/e78ccb3553e7938a08cd4c6d252f9988/image-7.jpg)
WWW-Authentication header 1/3 challenge = "Digest" digest-challenge = 1#( realm | [ domain ] | nonce | [ opaque ] |[ stale ] | [ algorithm ] | [ qop-options ] | [auth-param] ) domain URI nonce-value opaque stale algorithm = = = = qop-options qop-value "domain" "=" <"> URI ( 1*SP URI ) <"> absolute. URI | abs_path "nonce" "=" nonce-value quoted-string "opaque" "=" quoted-string "stale" "=" ( "true" | "false" ) "algorithm" "=" ( "MD 5" | "MD 5 -sess" | token ) = "qop" "=" <"> 1#qop-value <"> = "auth" | "auth-int" | token
WWW-Authentication header 2/3 n Realm ¨ n Nonce ¨ ¨ ¨ n Server-specified data string Uniquely generated at 401 response is made Base 64 or hexadecimal data recommended Implementation dependent Opaque to client Opaque ¨ ¨ ¨ n 인증될 사용자의 name, password 서버에서 생성된 값 클라이언트의 Authorization header에 그대로 포함되어 돌아옴 Base 64 or hexadecimal data recommended Stale ¨ ¨ ¨ Previous request의 nonce값이 잘못되어 있음을 나타냄 TRUE – nonce값이 잘못되었을 경우 (username/password는 정상이라 판단) FALSE, TRUE와 다른 값, stale directive가 없는 경우 – username/password가 비정상
WWW-Authentication header 3/3 n Algorithm ¨ ¨ ¨ Digest와 checksum에 쓰인 알고리즘 Default, MD 5 KD(secret, data) n ¨ H(data) n ¨ n H(data) = MD 5(data) KD(secret, data) = H(concat(secret, “: ”, data)) Qop-options ¨ ¨ Option 필드(back compatibility) Quoted string Quality of protection Example n n n Data에 checksum 알고리즘을 적용해 얻은 문장 Example (MD 5) n n Data를 secret을 이용해 digest한 문장 “Auth” – authentication “Auth-int” – authentication with integrity protection Auth-param ¨ For extension
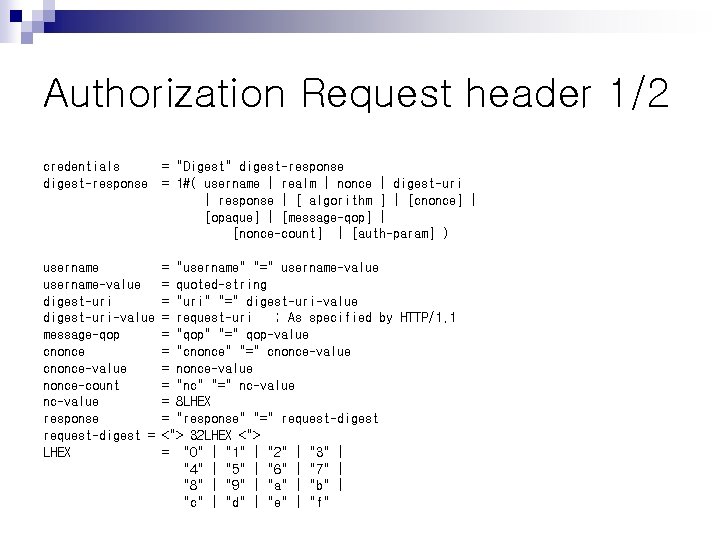
Authorization Request header 1/2 credentials digest-response = "Digest" digest-response = 1#( username | realm | nonce | digest-uri | response | [ algorithm ] | [cnonce] | [opaque] | [message-qop] | [nonce-count] | [auth-param] ) username-value digest-uri-value message-qop cnonce-value nonce-count nc-value response request-digest = LHEX = "username" "=" username-value = quoted-string = "uri" "=" digest-uri-value = request-uri ; As specified by HTTP/1. 1 = "qop" "=" qop-value = "cnonce" "=" cnonce-value = "nc" "=" nc-value = 8 LHEX = "response" "=" request-digest <"> 32 LHEX <"> = "0" | "1" | "2" | "3" | "4" | "5" | "6" | "7" | "8" | "9" | "a" | "b" | "c" | "d" | "e" | "f"
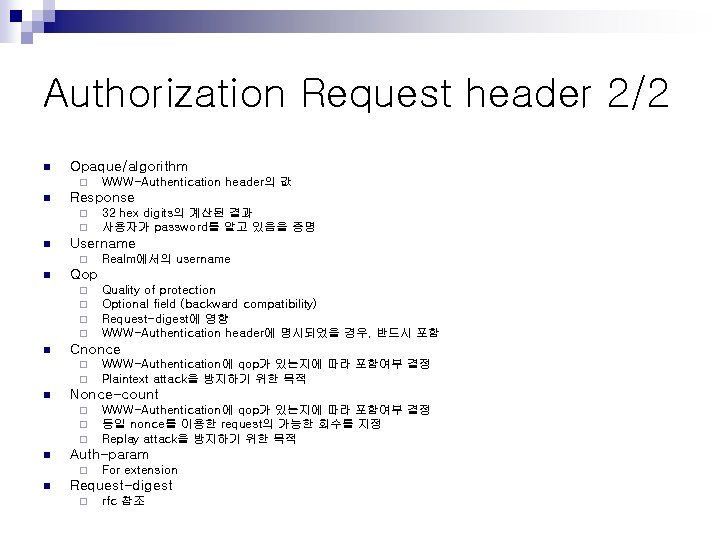
Authorization Request header 2/2 n Opaque/algorithm ¨ n Response ¨ ¨ n WWW-Authentication에 qop가 있는지에 따라 포함여부 결정 동일 nonce를 이용한 request의 가능한 회수를 지정 Replay attack을 방지하기 위한 목적 Auth-param ¨ n WWW-Authentication에 qop가 있는지에 따라 포함여부 결정 Plaintext attack을 방지하기 위한 목적 Nonce-count ¨ ¨ ¨ n Quality of protection Optional field (backward compatibility) Request-digest에 영향 WWW-Authentication header에 명시되었을 경우, 반드시 포함 Cnonce ¨ ¨ n Realm에서의 username Qop ¨ ¨ n 32 hex digits의 계산된 결과 사용자가 password를 알고 있음을 증명 Username ¨ n WWW-Authentication header의 값 For extension Request-digest ¨ rfc 참조
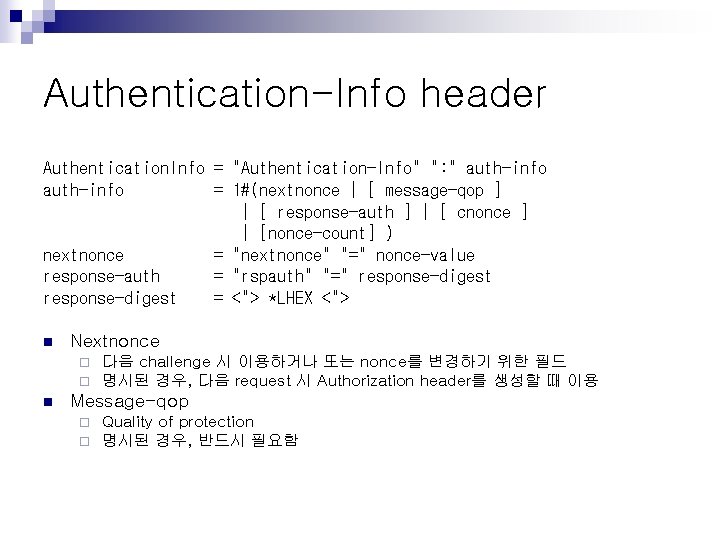
Authentication-Info header Authentication. Info = "Authentication-Info" ": " auth-info = 1#(nextnonce | [ message-qop ] | [ response-auth ] | [ cnonce ] | [nonce-count] ) nextnonce = "nextnonce" "=" nonce-value response-auth = "rspauth" "=" response-digest = <"> *LHEX <"> n Nextnonce ¨ ¨ n 다음 challenge 시 이용하거나 또는 nonce를 변경하기 위한 필드 명시된 경우, 다음 request 시 Authorization header를 생성할 때 이용 Message-qop ¨ ¨ Quality of protection 명시된 경우, 반드시 필요함
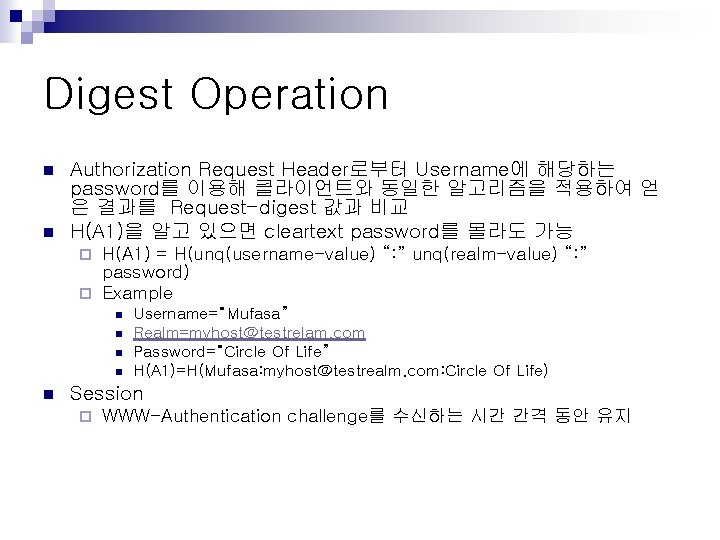
Digest Operation n n Authorization Request Header로부터 Username에 해당하는 password를 이용해 클라이언트와 동일한 알고리즘을 적용하여 얻 은 결과를 Request-digest 값과 비교 H(A 1)을 알고 있으면 cleartext password를 몰라도 가능 H(A 1) = H(unq(username-value) “: ” unq(realm-value) “: ” password) ¨ Example ¨ n n n Username=“Mufasa” Realm=myhost@testrelam. com Password=“Circle Of Life” H(A 1)=H(Mufasa: myhost@testrealm. com: Circle Of Life) Session ¨ WWW-Authentication challenge를 수신하는 시간 간격 동안 유지
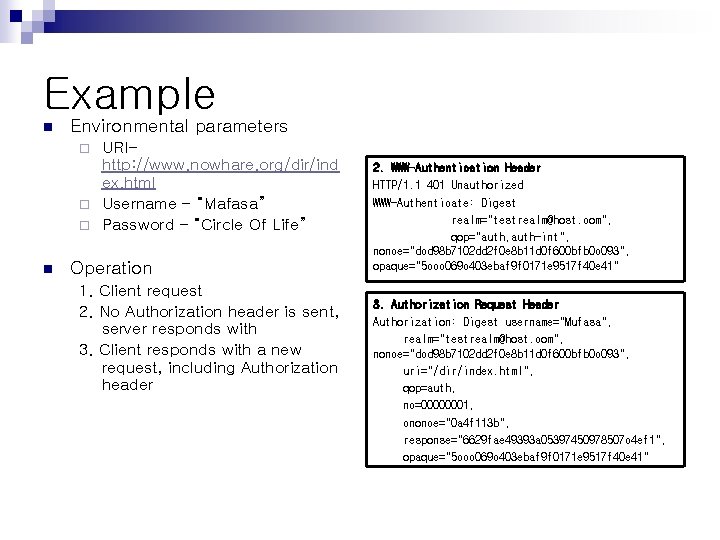
Example n Environmental parameters URIhttp: //www. nowhare. org/dir/ind ex. html ¨ Username – “Mafasa” ¨ Password – “Circle Of Life” ¨ n Operation 1. Client request 2. No Authorization header is sent, server responds with 3. Client responds with a new request, including Authorization header 2. WWW-Authentication Header HTTP/1. 1 401 Unauthorized WWW-Authenticate: Digest realm="testrealm@host. com", qop="auth, auth-int", nonce="dcd 98 b 7102 dd 2 f 0 e 8 b 11 d 0 f 600 bfb 0 c 093", opaque="5 ccc 069 c 403 ebaf 9 f 0171 e 9517 f 40 e 41" 3. Authorization Request Header Authorization: Digest username="Mufasa", realm="testrealm@host. com", nonce="dcd 98 b 7102 dd 2 f 0 e 8 b 11 d 0 f 600 bfb 0 c 093", uri="/dir/index. html", qop=auth, nc=00000001, cnonce="0 a 4 f 113 b", response="6629 fae 49393 a 05397450978507 c 4 ef 1", opaque="5 ccc 069 c 403 ebaf 9 f 0171 e 9517 f 40 e 41"
- Slides: 14