How Cyber Security Affects Facility Design Teams Speaker
How Cyber Security Affects Facility Design Teams Speaker: George Fragulis, Program Manager, Pond Moderator: Doug De. Fazio, Director of Corporate Strategy & Risk Management, KOMAN Holdings
WHY WAS UFC 4 -010 -06 CREATED? • The current state of building controls leaves buildings vulnerable to attack • Air gap not feasible; too many operating efficiencies are lost

EXAMPLES

WITH RESILIENCY COMES RISK • We need technology to make our buildings more robust • Technology allows our buildings to tell us what they need • That connectivity comes with risks
COMMON VULNERABILITIES • Connectivity • OT open protocols • Documentation • What systems do you have? • What protocols do you use? • Data flows • Virtual machines on servers
UFC 4 -010 -06 APPLICATION • All active and new projects must comply • Methods of security are based on NIST documents
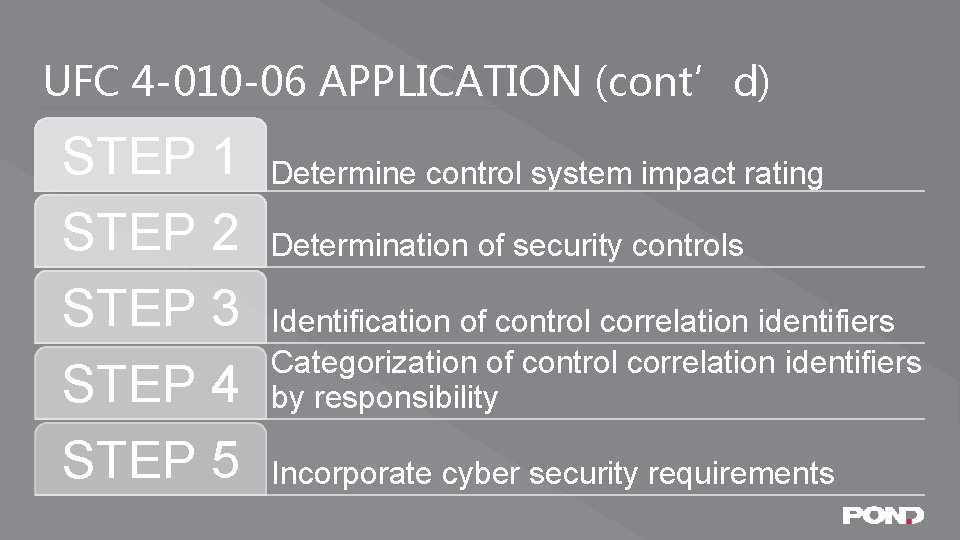
UFC 4 -010 -06 APPLICATION (cont’d) STEP 1 STEP 2 STEP 3 STEP 4 STEP 5 Determine control system impact rating Determination of security controls Identification of control correlation identifiers Categorization of control correlation identifiers by responsibility Incorporate cyber security requirements
UFC 4 -010 -06 APPLICATION (cont’d) • Security Officer determines the impact rating of the control system • Do. D Impact levels are determined based on the mission of the relevant Service • Do not proceed with out the impact rating
UFC 4 -010 -06 APPLICATION (cont’d) • Compile a list of all the controls
UFC 4 -010 -06 APPLICATION (cont’d) • With the list of controls, compile a list of the correlation identifiers
UFC 4 -010 -06 APPLICATION (cont’d) • Identifies who is responsible for implementing security protocols • As part of the operations • As part of the design • As part of the set up • Or it is not practical to secure

UFC 4 -010 -06 APPLICATION (cont’d) • Responsible parties implement the security requirements
PROJECT EXAMPLE
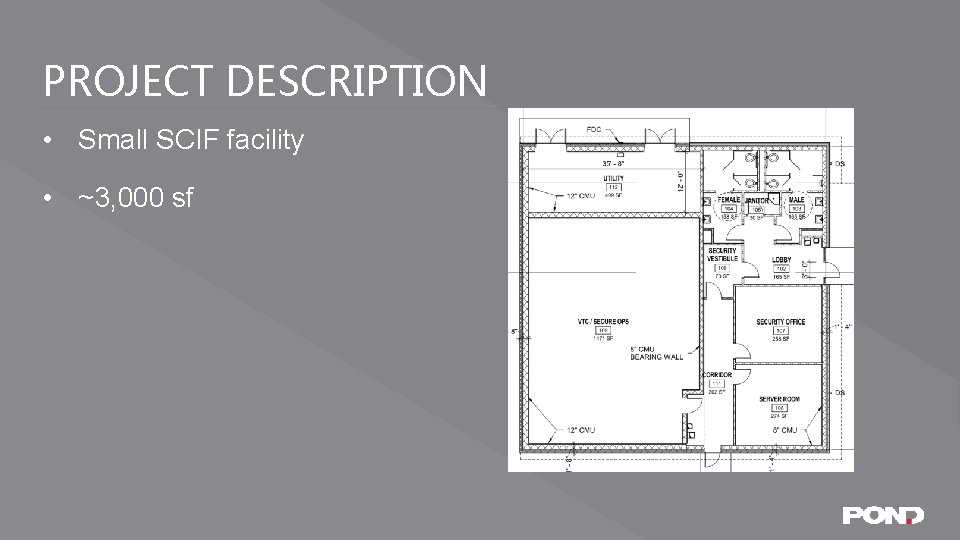
PROJECT DESCRIPTION • Small SCIF facility • ~3, 000 sf
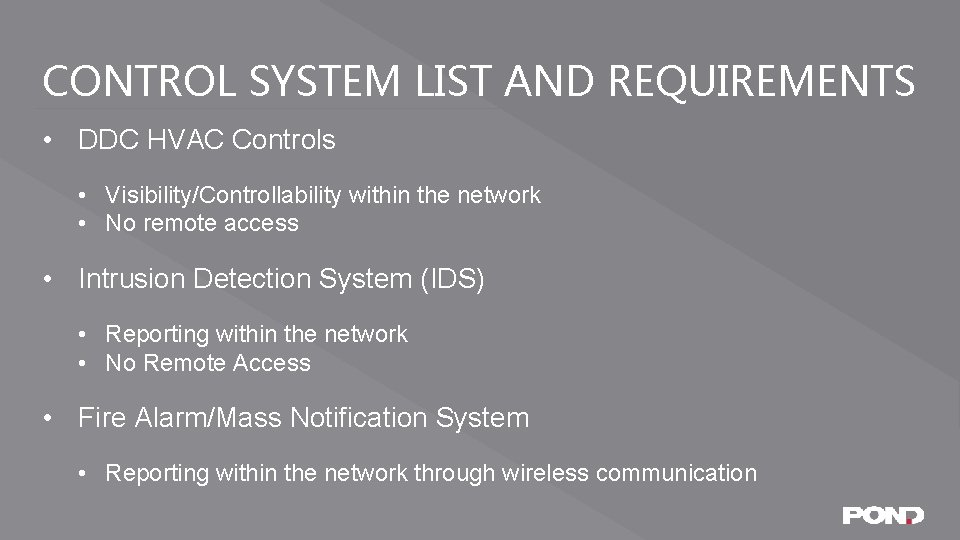
CONTROL SYSTEM LIST AND REQUIREMENTS • DDC HVAC Controls • Visibility/Controllability within the network • No remote access • Intrusion Detection System (IDS) • Reporting within the network • No Remote Access • Fire Alarm/Mass Notification System • Reporting within the network through wireless communication
DETERMINE IMPACT RATING • The System Owner (SO) with concurrence with the Authorizing Official determines Impact levels • Largely based on the Mission • This facility is a ‘Mission Support’ facility • (Versus: Mission Essential, Mission Critical) • Impact Rating (C-I-A) • Confidentiality = L • Integrity = L • Availability = L • UFC 4 -010 -06 Directs us to Appendix G and H
DETERMINE SECURITY CONTROLS • Appendix G • G-2. 3 Security Controls which are “Automatically Met” • IDS and Fire Alarm systems previously approved on the installation will have met security requirements at the 5 levels of the network architecture • Therefore, designer should focus on the DDC controls • Appendix H • Use table H-1 for L-L-L • See table H-2 and H-3 for recommend CCIs to be tailored out
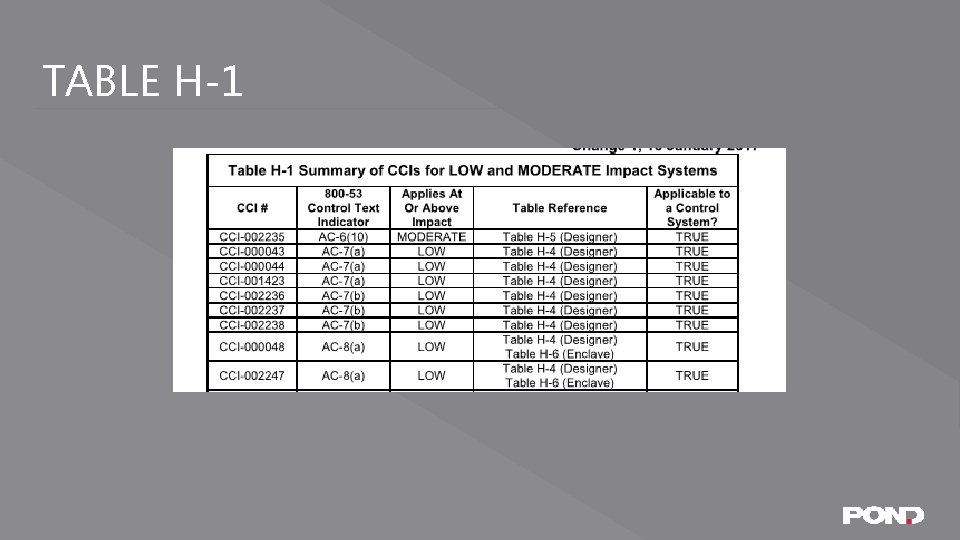
TABLE H-1
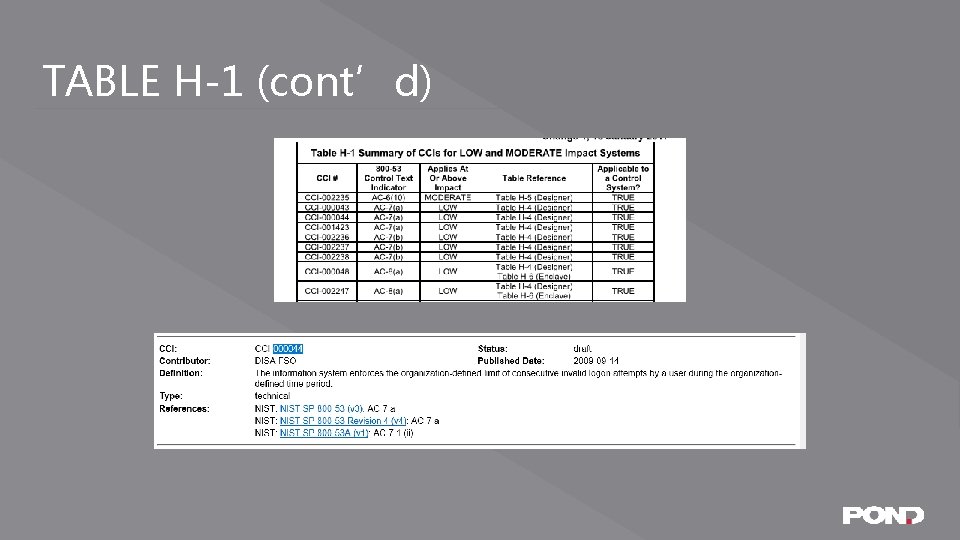
TABLE H-1 (cont’d)
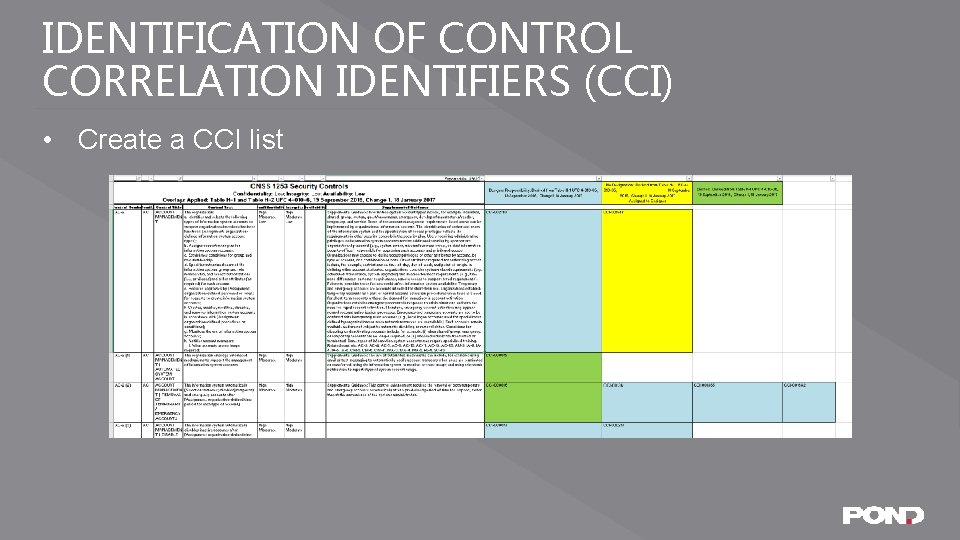
IDENTIFICATION OF CONTROL CORRELATION IDENTIFIERS (CCI) • Create a CCI list
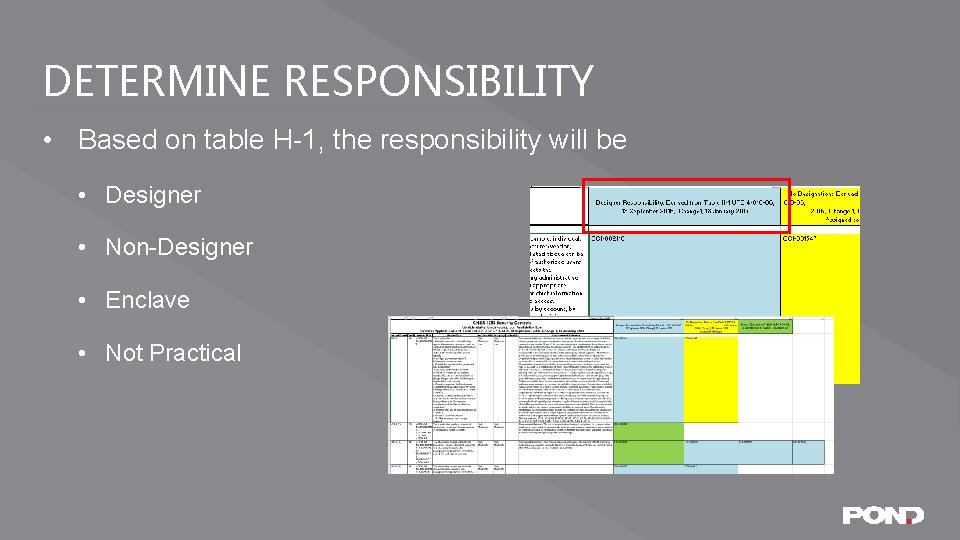
DETERMINE RESPONSIBILITY • Based on table H-1, the responsibility will be • Designer • Non-Designer • Enclave • Not Practical
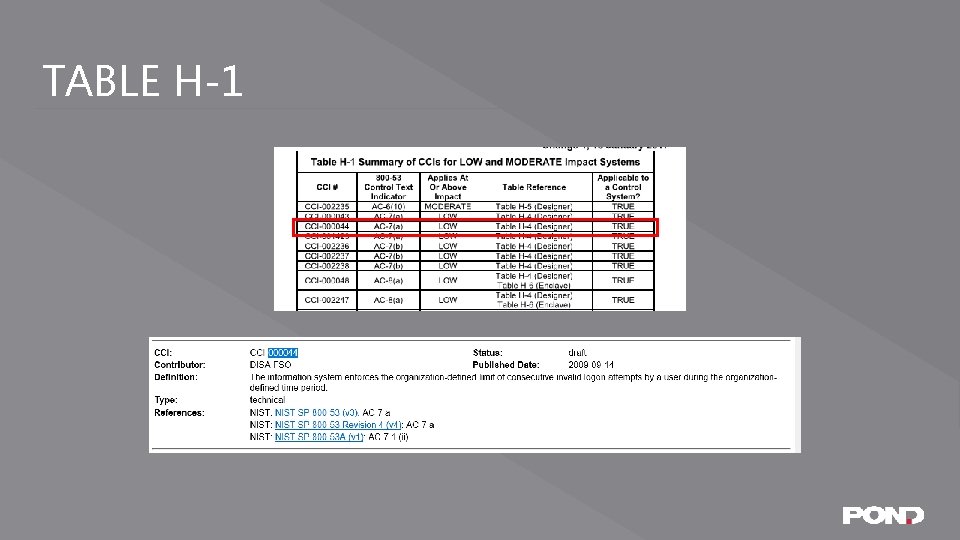
TABLE H-1
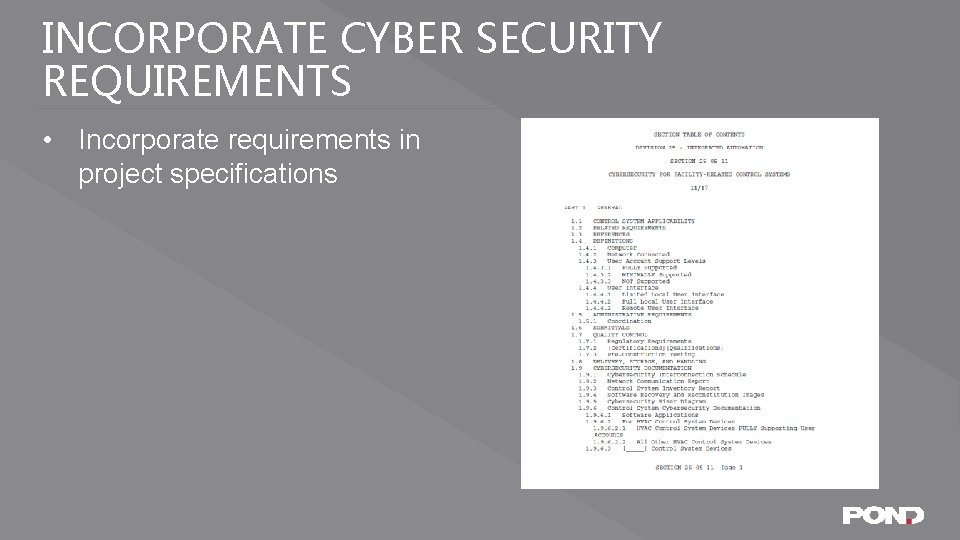
INCORPORATE CYBER SECURITY REQUIREMENTS • Incorporate requirements in project specifications

QUESTIONS?
THANK YOU George Fragulis, PE, PMP, CEM, BEMP, LEED AP BD+C T: (404) 748 -4846 E: fragulisg@pondco. com
- Slides: 25