HostSponsor Exercise Name 2015 Tabletop Exercise Host Logo
Host/Sponsor Exercise Name 2015 Tabletop Exercise Host Logo / Seal Month DD, YYYY
Welcome and Opening Remarks Host/Sponsor POC Name Position Organization Host Logo / Seal 2
Exercise Overview and Facilitator Name Organization / Department / Office Division Sub Office Host Logo / Seal 3
Exercise Structure § This exercise will be a multimedia, facilitated tabletop exercise § Players will participate in the following three modules: – <Module, Phase, or Other> <1>: < Insert Name > – <Module, Phase, or Other> <2>: < Insert Name > – <Module, Phase, or Other> <3>: < Insert Name > § Scenario updates will be provided at the beginning of each Module § Exercise will conclude with a brief Hot Wash Host Logo / Seal 4
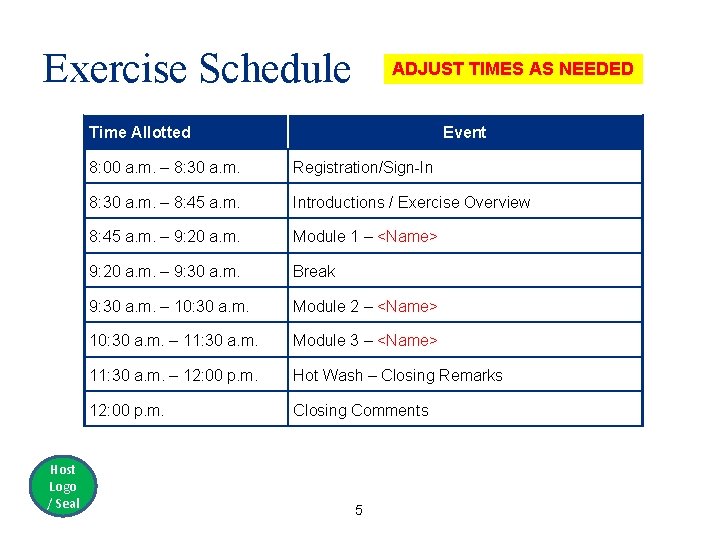
Exercise Schedule ADJUST TIMES AS NEEDED Time Allotted Host Logo / Seal Event 8: 00 a. m. – 8: 30 a. m. Registration/Sign-In 8: 30 a. m. – 8: 45 a. m. Introductions / Exercise Overview 8: 45 a. m. – 9: 20 a. m. Module 1 – <Name> 9: 20 a. m. – 9: 30 a. m. Break 9: 30 a. m. – 10: 30 a. m. Module 2 – <Name> 10: 30 a. m. – 11: 30 a. m. Module 3 – <Name> 11: 30 a. m. – 12: 00 p. m. Hot Wash – Closing Remarks 12: 00 p. m. Closing Comments 5
Exercise Objectives § Create an opportunity for stakeholders to explore and address cybersecurity challenges and increase cybersecurity awareness. § Assess the integration of cybersecurity into <Organization’s> all-hazards preparedness. § Examine cybersecurity management structures, incident information sharing, escalation criteria, and related courses of action. § Identify cascading impacts of a cyber-attack to critical systems § <Insert additional/other organization specific objectives> Host Logo / Seal 6
Participant Roles and Responsibilities § Players: Respond to situation presented based on current plans, policies, and procedures § Observers: Support players in developing responses, but do not directly participate § Facilitators provide situation updates and moderate discussions. They also provide additional information or resolve questions as required § Evaluators are assigned to observe and document key findings during the exercise Host Logo / Seal 7
Exercise Guidelines § This is an open, low-stress environment. Varying viewpoints, even disagreements, are expected § Respond to the scenario using your knowledge of current plans and capabilities (i. e. , you may use only existing assets) and insights derived from your experience and training § Decisions are not precedent setting and may not reflect your organization’s final position on a given issue. This exercise is an opportunity to discuss and present multiple options and possible solutions § Be an active participant! Host Logo / Seal 8
Assumptions and Artificialities § The exercise is conducted in a no-fault learning environment wherein capabilities, plans, systems, and processes will not be evaluated § There is no “hidden agenda” nor are there any trick questions § The exercise scenario is plausible, and events occur as they are presented § All players receive information at the same time § The scenario is not derived from current intelligence Host Logo / Seal 9
Module 1: <Name> Host Logo / Seal 10
T – 2 Years: Initiation § According to an autopsy report, the sudden death of a 15 -year -old girl who was treated at [hospital name here], was ruled to be the result of a severe type of pneumonia § Patient’s family suspects improper care as the true leading cause of death and blames the [hospital name] § Soon after the release of the autopsy report, the family of the girl begins to demand the medical center be held accountable and files a wrongful death lawsuit against [hospital name] Host Logo / Seal 11
T – 6 Months: Motivation § Upon presentation and litigation of the wrongful death lawsuit, the court rules in favor of [hospital name] § The family remains unconvinced, distraught, and angry over the verdict Host Logo / Seal 12
T – 5 Months: Advisory § The Multi-State Information Sharing and Analysis Center (MS -ISAC) in partnership with the National Health Information Sharing and Analysis Center (NH-ISAC) releases a joint advisory § Highlights several recent attacks against state health information exchanges Host Logo / Seal 13
![T – 10 Days: Indication § The [hospital name] begins to notice an increase T – 10 Days: Indication § The [hospital name] begins to notice an increase](http://slidetodoc.com/presentation_image_h2/817f85117285c1a4691e83657b4407df/image-14.jpg)
T – 10 Days: Indication § The [hospital name] begins to notice an increase in scans and phishing campaigns, similar to those that were reported at other medical providers throughout the country, including a 25% increase in attempted attacks against their networks Host Logo / Seal 14
T – 2 Days: Slow Motion § Employees begin to report internal network latency § Members of the public report they cannot access [hospital name]’s website Host Logo / Seal 15
![T – 1 Day: Degradation § [hospital name] systems performance continues to degrade, exacerbated T – 1 Day: Degradation § [hospital name] systems performance continues to degrade, exacerbated](http://slidetodoc.com/presentation_image_h2/817f85117285c1a4691e83657b4407df/image-16.jpg)
T – 1 Day: Degradation § [hospital name] systems performance continues to degrade, exacerbated by suspected data loss § Several nurses begin to report records that were available only a short time earlier are now completely unavailable Host Logo / Seal 16
Module 1 Discussion Host Logo / Seal 17
Consider the following during discussion… § Information sharing by various constituents, to include government sources of indicators and warnings – Information sharing mechanism limitations and challenges within [hospital name] § Internal cyber threat information requirements and thresholds for reporting credible threats and incidents to organizational executive leadership § What types of security-related industry alerts does the [hospital name] receive? Those from NH-ISAC? US-CERT? Others? Host Logo / Seal 18
Module 2: <Name> Host Logo / Seal 19
T – Day: Investigation § In response to the extreme latency and unavailable medical records, [hospital name] begins to field an increase in help desk calls related to the EMR problems § During this period, technicians confirm that records are actually missing and notice unusual patterns in access logs, including unauthorized access to the EMR system Host Logo / Seal 20
![T – Day: Escalation § The “News and Info” section of the [hospital name]’s T – Day: Escalation § The “News and Info” section of the [hospital name]’s](http://slidetodoc.com/presentation_image_h2/817f85117285c1a4691e83657b4407df/image-21.jpg)
T – Day: Escalation § The “News and Info” section of the [hospital name]’s public web site, including one of its social media platforms, is defaced § Defacement contains threats and a warning to the public about the [hospital name]’s level of care Hospital Host Logo / Seal THIS HOSPITAL WILL DECEIVE YOU – THEY CANNOT BE TRUSTED WITH YOUR INFORMATION, OR YOUR LIFE!!! 21
T + 1 Day: Communication § A local media affiliate of Global Network News and other local media outlets start reporting on the defacement of the [hospital name] homepage Host Logo / Seal 22
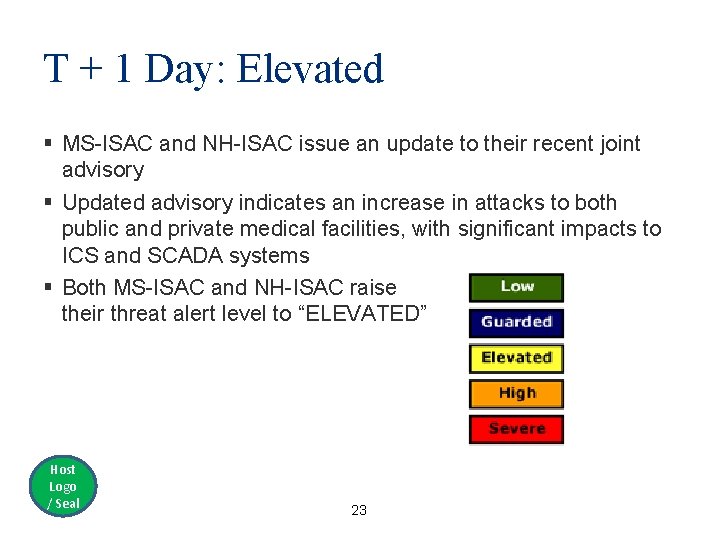
T + 1 Day: Elevated § MS-ISAC and NH-ISAC issue an update to their recent joint advisory § Updated advisory indicates an increase in attacks to both public and private medical facilities, with significant impacts to ICS and SCADA systems § Both MS-ISAC and NH-ISAC raise their threat alert level to “ELEVATED” Host Logo / Seal 23
Module 2 Discussion Host Logo / Seal 24
Consider the following during discussion… § Initial response measures and triggers for external incident response coordination § Existing incident response coordination, investigation, and mitigation efforts, and identification of impediments to timely response § Cyber incident escalation criteria and planned notifications § What is your planned cyber incident management structure? § How would external resources be requested and integrated? § Would legal department(s) be involved to address potential liability issues? How are they brought in appropriately? Host Logo / Seal 25
Module 3: <Name> Host Logo / Seal 26
![T + 1 Day: Explanation § Further investigation indicates that malware infected [hospital name] T + 1 Day: Explanation § Further investigation indicates that malware infected [hospital name]](http://slidetodoc.com/presentation_image_h2/817f85117285c1a4691e83657b4407df/image-27.jpg)
T + 1 Day: Explanation § Further investigation indicates that malware infected [hospital name] via a spearphishing e-mail opened by a [hospital name] employee with privileged access / administrator rights several weeks ago § This malware was used to alter supply inventory records and exfiltrate more than 50, 000 personally identifiable information (PII) and electronic protected health information (e. PHI) records Host Logo / Seal 27
T + 1 Day: Intensification § Patients and staff report an extreme change in temperature in the medical facility, complaining it is too hot § As a result of the complaints, [hospital name] suspects a potential malfunction to SCADA-enabled devices within HVAC and building management systems Host Logo / Seal 28
T + 1 Day: Expansion § Building Operations reports that a facilities technician tasked to inspect the HVAC and BMS is unable to login to the server that controls the HVAC system § The technician entered his credentials as usual, but received an “access denied” message Host Logo / Seal 29
![T + 1 Day: Exhaustion § [hospital name] has quickly exhausted all available resources T + 1 Day: Exhaustion § [hospital name] has quickly exhausted all available resources](http://slidetodoc.com/presentation_image_h2/817f85117285c1a4691e83657b4407df/image-30.jpg)
T + 1 Day: Exhaustion § [hospital name] has quickly exhausted all available resources to investigate the extent of the problem and restore affected systems, resulting in significant impacts to patient care and life safety concerns Host Logo / Seal 30
T + 2 Day: Attention § National media outlets begin reporting on the situation at [hospital name] § In particular, the media outlets are covering the messages posted on the [hospital name] website and social media platform Host Logo / Seal 31
![T + 4 Day: Ramifications § During an in-depth log review, the [hospital name] T + 4 Day: Ramifications § During an in-depth log review, the [hospital name]](http://slidetodoc.com/presentation_image_h2/817f85117285c1a4691e83657b4407df/image-32.jpg)
T + 4 Day: Ramifications § During an in-depth log review, the [hospital name] discovers that 65 days ago, “[insert exercise malware name]” was implanted on the medical facility’s network, resulting in the creation of a “super user” with admin rights § Investigators strongly suspect that the infection vector is linked to the spearphishing and network scanning, which eventually exploited a vulnerability in the [hospital name]’s network § Both the [hospital name] and the investigation team continue the systematic process of malware remediation, removal, and patch updates Host Logo / Seal 32
Module 3 Discussion Host Logo / Seal 33
Consider the following during discussion… § Identification of available response, investigation, and mitigation resources and capabilities § Identification of resource request coordination pathways § Cyber incident management structure § Role of public information during a cyber incident – Challenges when coordinating public communications – Public affairs playbook or pre-scripted statements § Processes or protocols when contacting and/or working with law enforcement § Processes and resources in place for evidence preservation and collection Host Logo / Seal 34
Exercise Hot Wash Host Logo / Seal 35
Hot Wash § Strengths – – – § Areas for Improvement – – – Host Logo / Seal 36
Points of Contact For questions about this exercise or recommendations for improvement, contact: Name of Facilitator Dept / Div / Office email Host Logo / Seal 37
- Slides: 37