Hidden Azure Some useful features to keep your







- Slides: 52
Hidden Azure Some useful features to keep your secrets safe Global Azure Bootcamp - Boston Azure - Boston 25 -April-2015 Bill Wilder, Finomial CTO @codingoutloud@gmail. com blog. codingoutloud. com linkedin. com/in/billwilder • Except where noted contents © 2014 Development Partners Software Corporation • http: //www. devpartners. com •
Hidden Azure Some useful features to keep your secrets safe Find this slide Global Azure Bootcamp - Boston Azure - Boston deck here 25 -April-2015 Bill Wilder, Finomial CTO @codingoutloud@gmail. com blog. codingoutloud. com linkedin. com/in/billwilder • Except where noted contents © 2014 Development Partners Software Corporation • http: //www. devpartners. com •
Questions during or after? @codingoutloud
www. cloudarchitecturepatterns. com Who is Bill Wilder? www. bostonazure. org www. devpartners. com
Goal: Alert you to the existence of a few Azure service features (awareness – not in-depth)
Automation Run. Books
Problem • Run a Nightly Job • Automatically • Securely – Deals with sensitive credentials • With auditing • All of it is in Power. Shell
demo
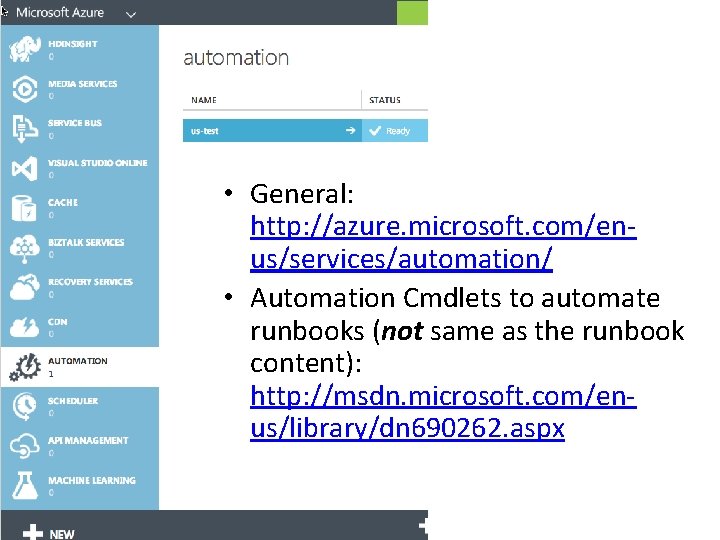
• General: http: //azure. microsoft. com/enus/services/automation/ • Automation Cmdlets to automate runbooks (not same as the runbook content): http: //msdn. microsoft. com/enus/library/dn 690262. aspx
Vulnerabilities (cool? ) (interesting? )

Ever hear of… • A 1 -Injection • A 2 -Broken Authentication and Session Management • A 3 -Cross-Site Scripting (XSS) • A 4 -Insecure Direct Object References • A 5 -Security Misconfiguration • A 6 -Sensitive Data Exposure • A 7 -Missing Function Level Access Control • A 8 -Cross-Site Request Forgery (CSRF) • A 9 -Using Components with Known Vulnerabilities • A 10 -Unvalidated Redirects and Forwards

unicorn cloud security for apps SESSION HIJACKING X SS SQL N O I T C E J IN CSRF Copyright © 2013 Elizabeth B. O’Connor • used with permission • www. elizabethboconnor. com
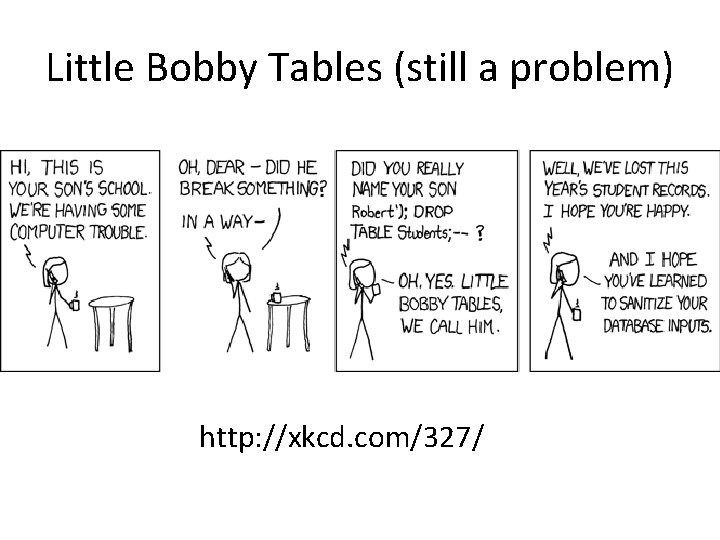
Little Bobby Tables (still a problem) http: //xkcd. com/327/
fun security challenges
Logging in securely with AAD (yawn? )

Boring?
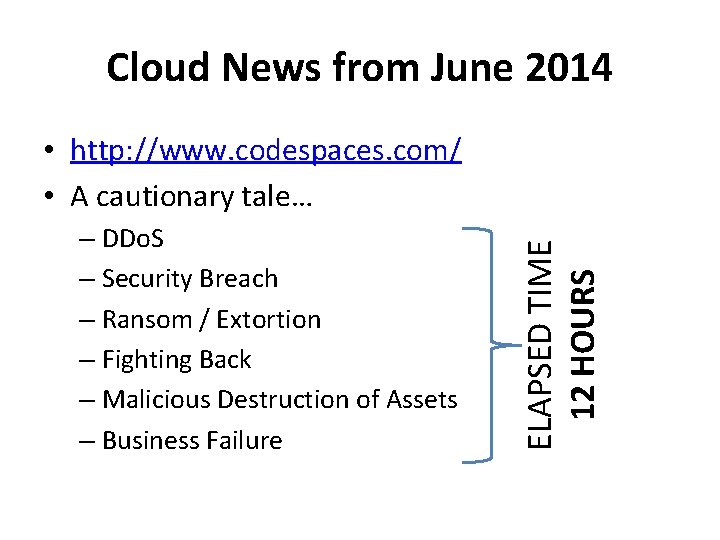
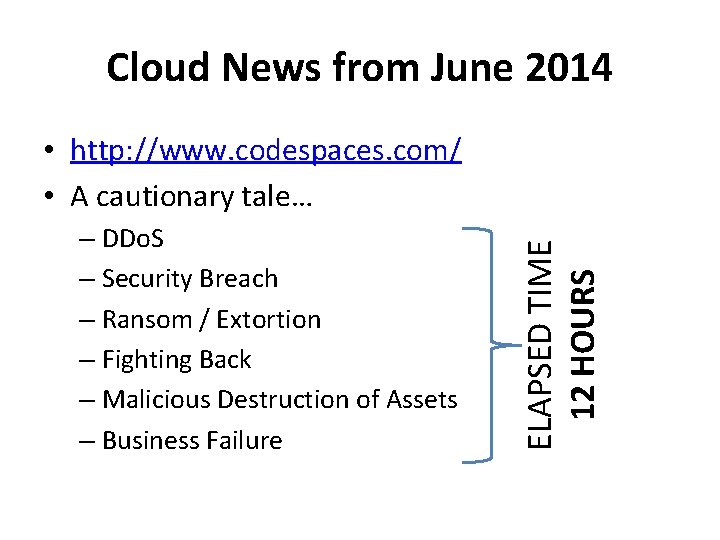
Cloud News from June 2014 – DDo. S – Security Breach – Ransom / Extortion – Fighting Back – Malicious Destruction of Assets – Business Failure ELAPSED TIME 12 HOURS • http: //www. codespaces. com/ • A cautionary tale…
n r e t t a P Anti 1 FA single-factor auth (2 FA/MFA is widely available – e. g. , AAD)
demo
Azure Key Vault
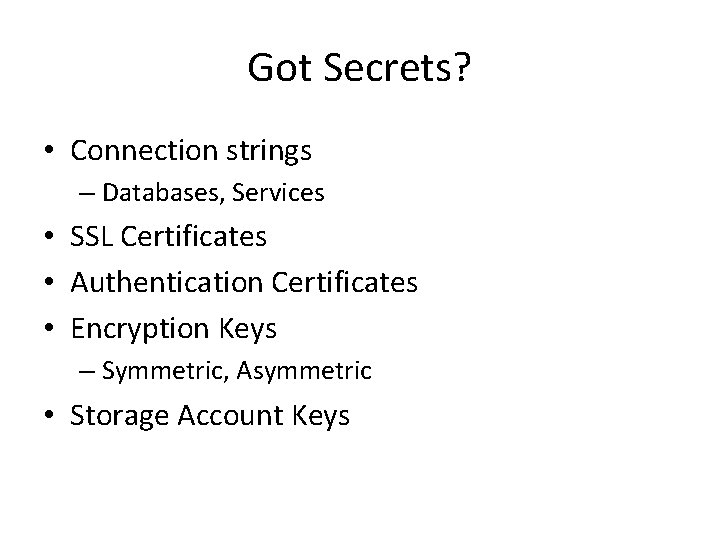
Got Secrets? • Connection strings – Databases, Services • SSL Certificates • Authentication Certificates • Encryption Keys – Symmetric, Asymmetric • Storage Account Keys
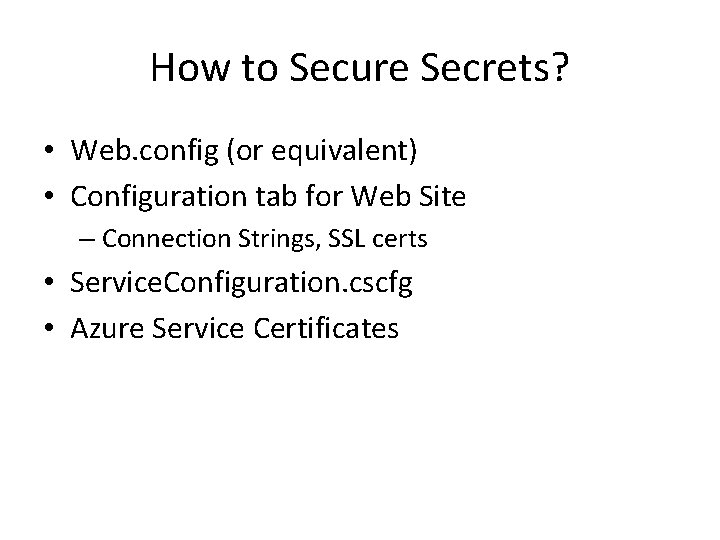
How to Secure Secrets? • Web. config (or equivalent) • Configuration tab for Web Site – Connection Strings, SSL certs • Service. Configuration. cscfg • Azure Service Certificates
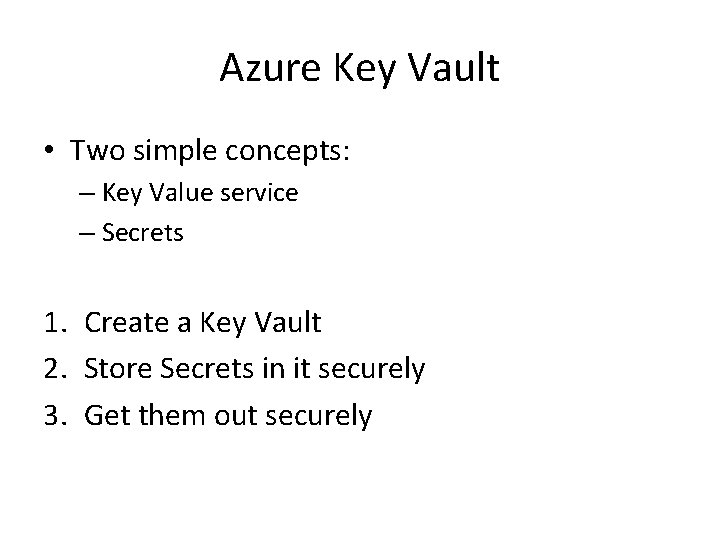
Azure Key Vault • Two simple concepts: – Key Value service – Secrets 1. Create a Key Vault 2. Store Secrets in it securely 3. Get them out securely
demo
More Azure Key Vault Concepts • Key Vault • Secret • Key – Wrap – Unwrap • HSM • Security Principal
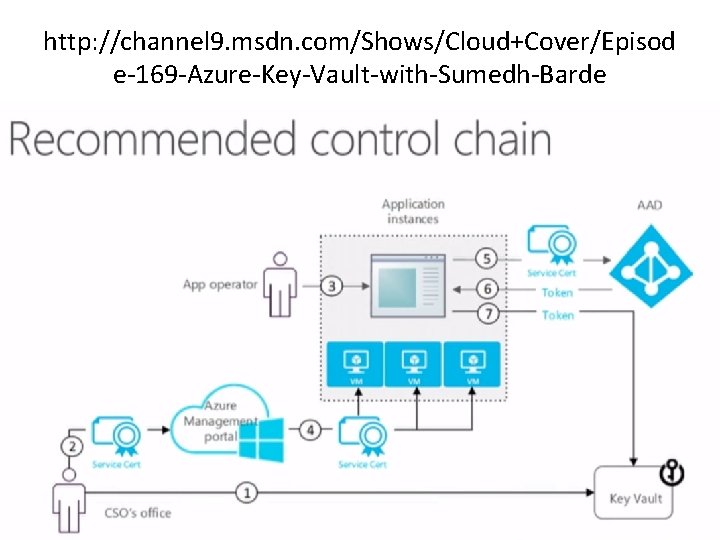
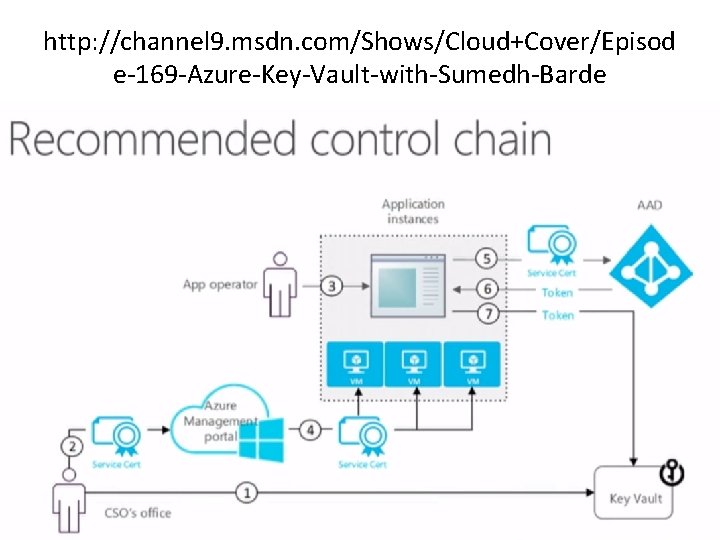
http: //channel 9. msdn. com/Shows/Cloud+Cover/Episod e-169 -Azure-Key-Vault-with-Sumedh-Barde
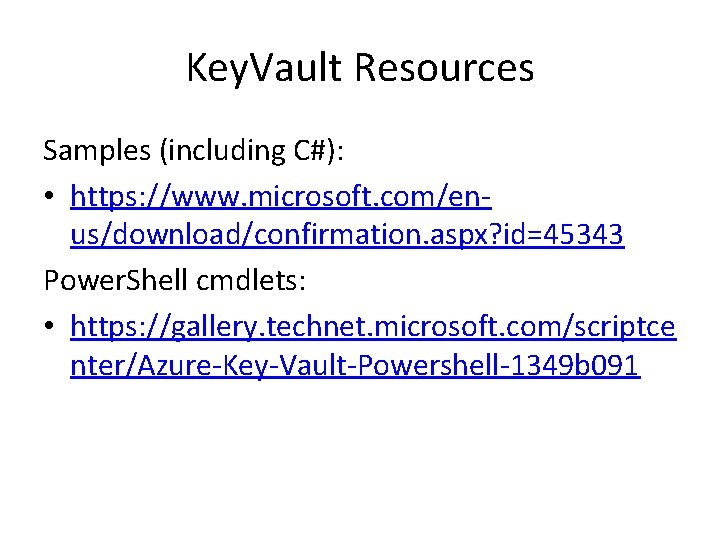
Key. Vault Resources Samples (including C#): • https: //www. microsoft. com/enus/download/confirmation. aspx? id=45343 Power. Shell cmdlets: • https: //gallery. technet. microsoft. com/scriptce nter/Azure-Key-Vault-Powershell-1349 b 091
Valet Key Pattern
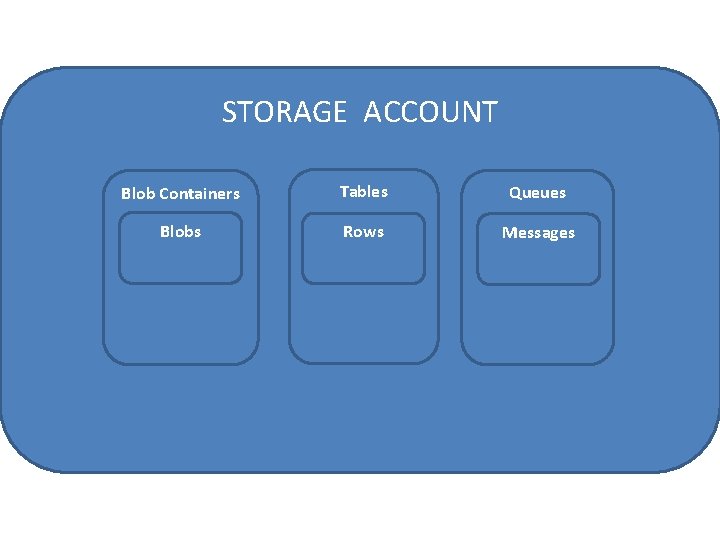
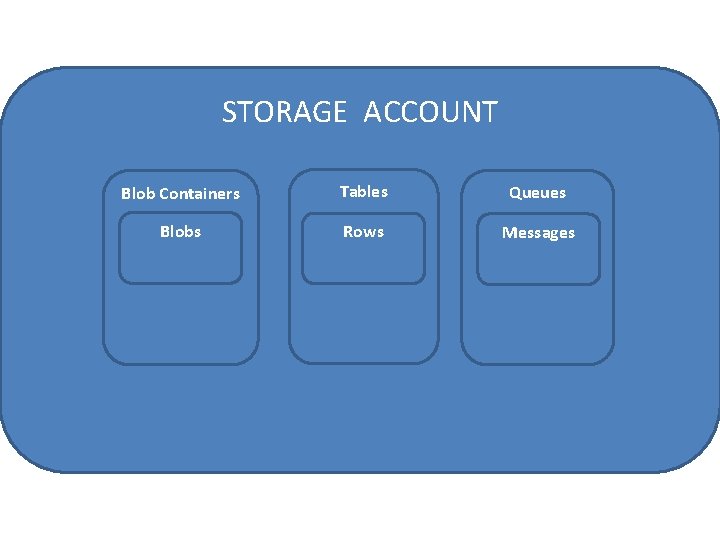
STORAGE ACCOUNT Blob Containers Tables Queues Blobs Rows Messages
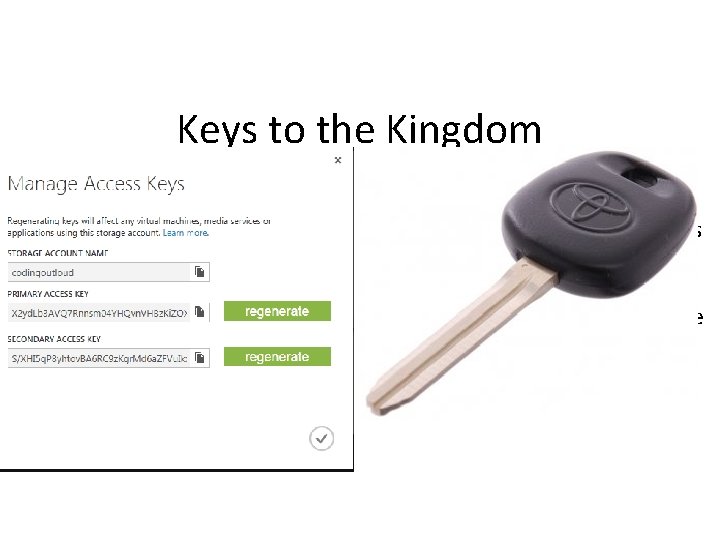
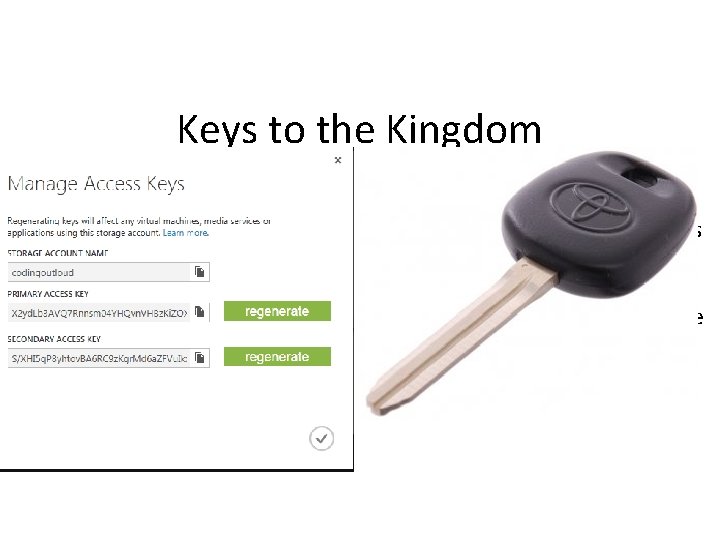
Keys to the Kingdom Account Scope Fine for internal, trusted systems Not safe for untrusted clients Similar to DB connection string For DB, we gate access with code (ever afraid of Tenant Leakage) • With Azure Storage, we can do better • • •
e l a V K t y e
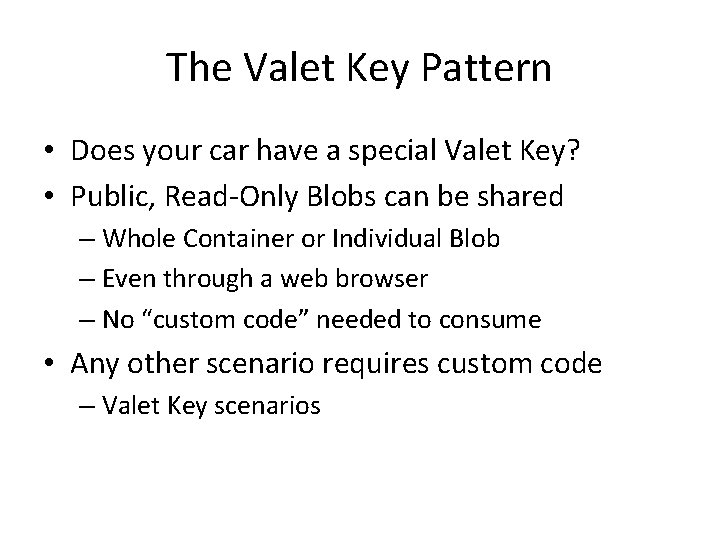
The Valet Key Pattern • Does your car have a special Valet Key? • Public, Read-Only Blobs can be shared – Whole Container or Individual Blob – Even through a web browser – No “custom code” needed to consume • Any other scenario requires custom code – Valet Key scenarios
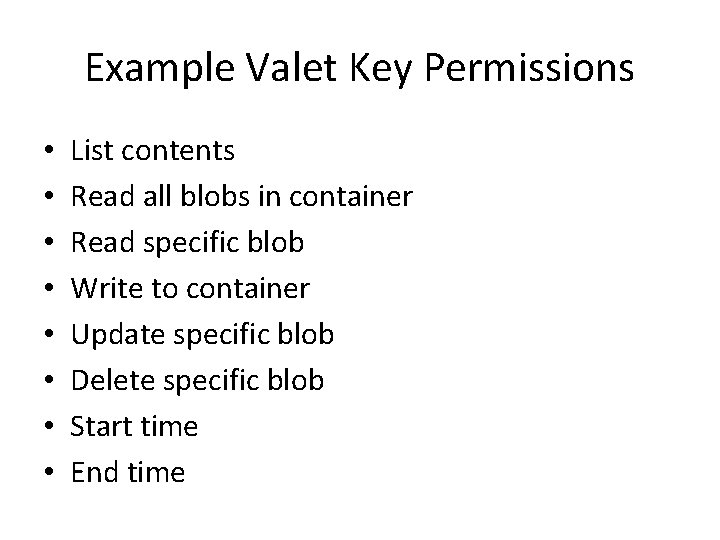
Example Valet Key Permissions • • List contents Read all blobs in container Read specific blob Write to container Update specific blob Delete specific blob Start time End time
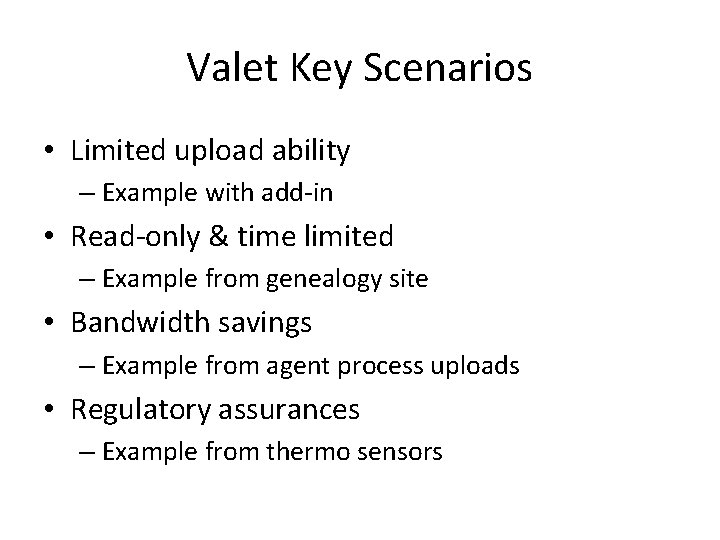
Valet Key Scenarios • Limited upload ability – Example with add-in • Read-only & time limited – Example from genealogy site • Bandwidth savings – Example from agent process uploads • Regulatory assurances – Example from thermo sensors
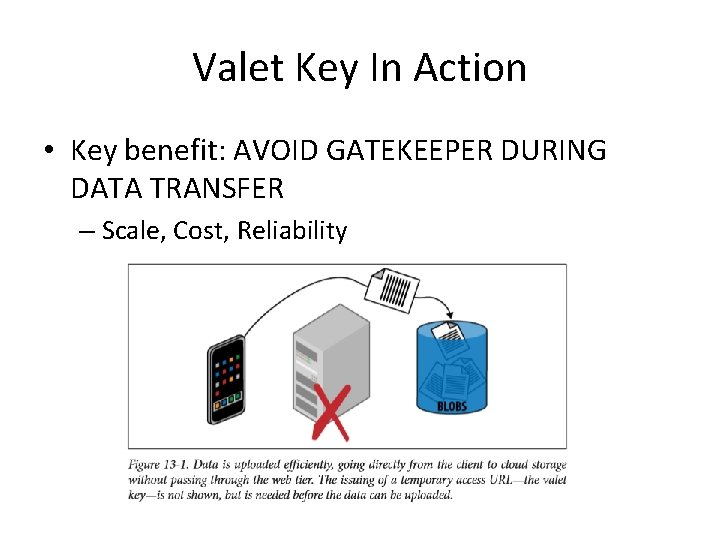
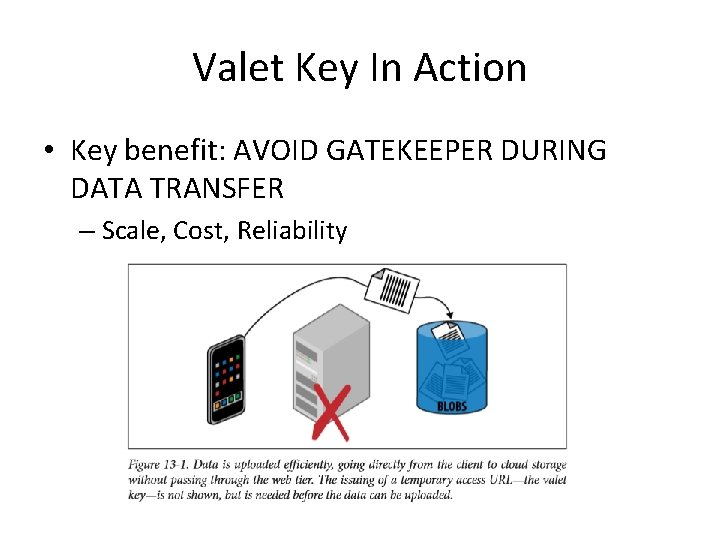
Valet Key In Action • Key benefit: AVOID GATEKEEPER DURING DATA TRANSFER – Scale, Cost, Reliability
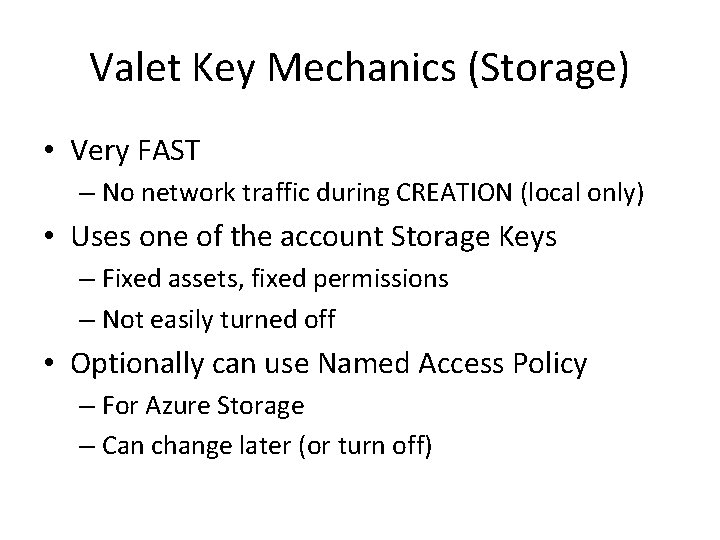
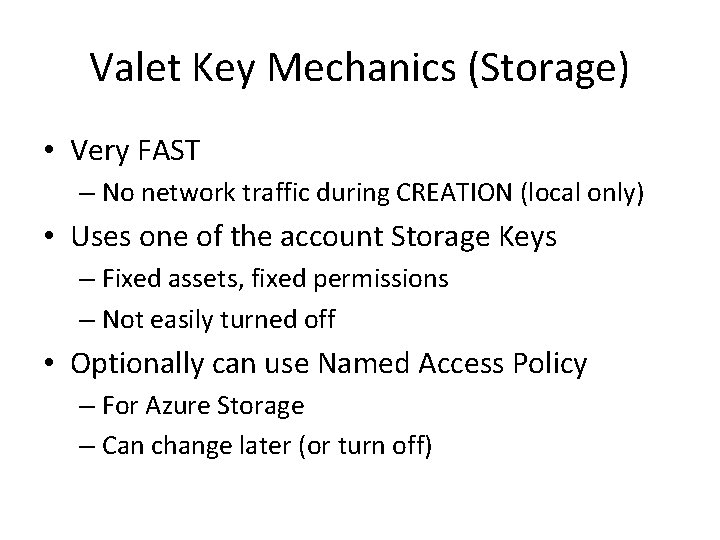
Valet Key Mechanics (Storage) • Very FAST – No network traffic during CREATION (local only) • Uses one of the account Storage Keys – Fixed assets, fixed permissions – Not easily turned off • Optionally can use Named Access Policy – For Azure Storage – Can change later (or turn off)
3. Temporary Lock

https: //gist. github. com/ codingoutloud/ 9403 c 39 c 1985 ec 15 b 733 code
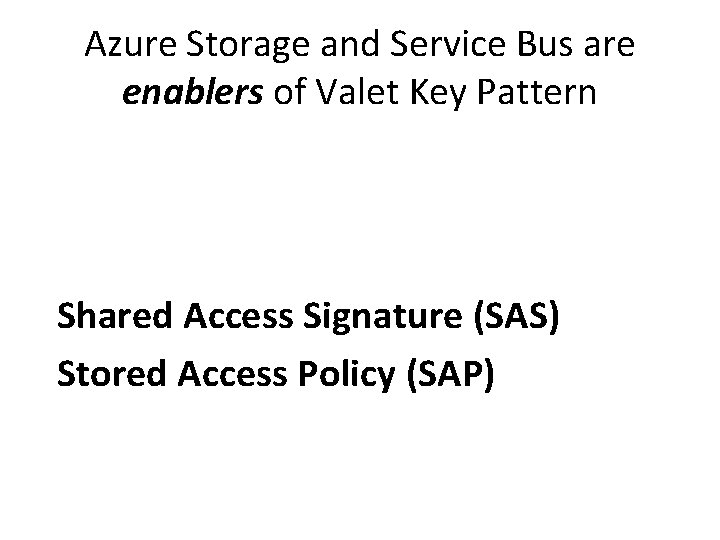
Azure Storage and Service Bus are enablers of Valet Key Pattern Shared Access Signature (SAS) Stored Access Policy (SAP)
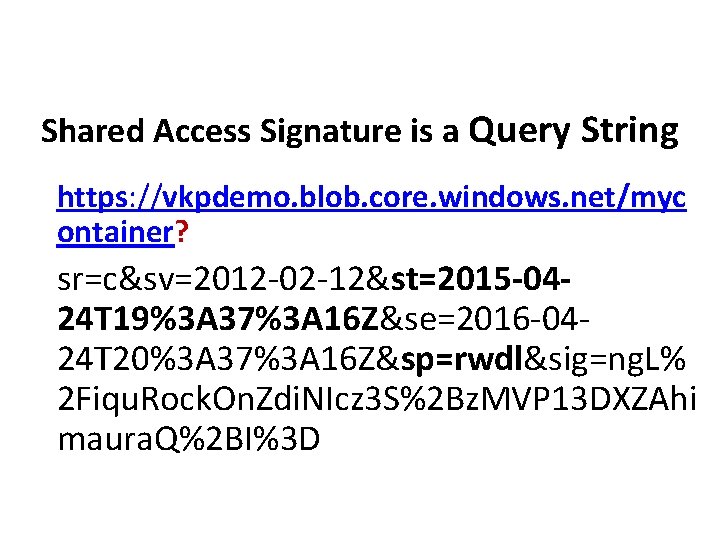
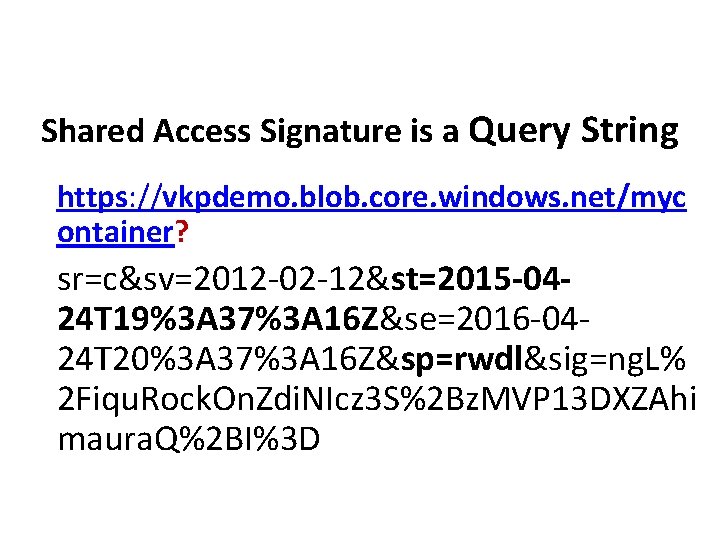
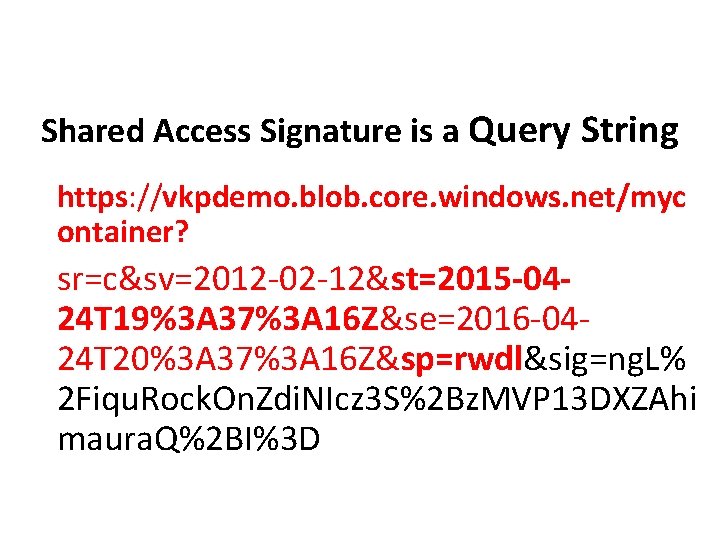
Shared Access Signature is a Query String https: //vkpdemo. blob. core. windows. net/myc ontainer? sr=c&sv=2012 -02 -12&st=2015 -0424 T 19%3 A 37%3 A 16 Z&se=2016 -0424 T 20%3 A 37%3 A 16 Z&sp=rwdl&sig=ng. L% 2 Fiqu. Rock. On. Zdi. NIcz 3 S%2 Bz. MVP 13 DXZAhi maura. Q%2 BI%3 D
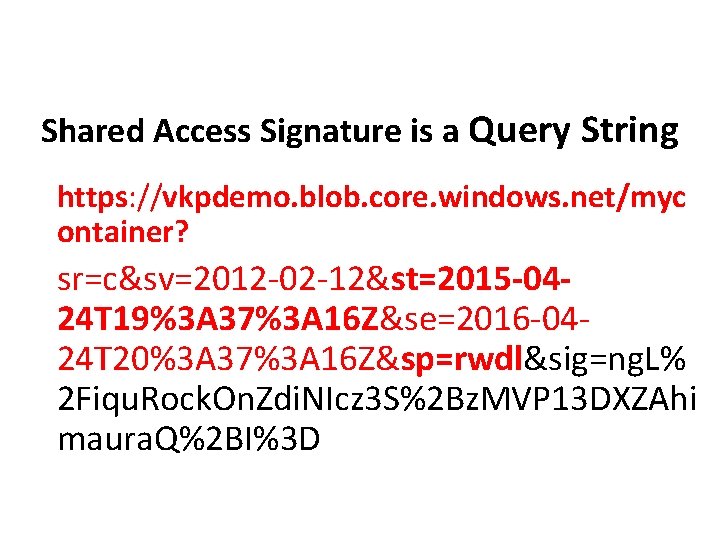
Shared Access Signature is a Query String https: //vkpdemo. blob. core. windows. net/myc ontainer? sr=c&sv=2012 -02 -12&st=2015 -0424 T 19%3 A 37%3 A 16 Z&se=2016 -0424 T 20%3 A 37%3 A 16 Z&sp=rwdl&sig=ng. L% 2 Fiqu. Rock. On. Zdi. NIcz 3 S%2 Bz. MVP 13 DXZAhi maura. Q%2 BI%3 D
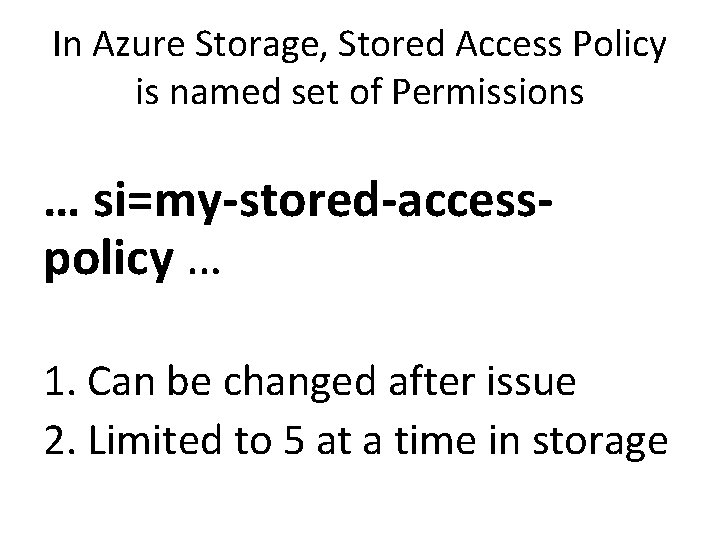
In Azure Storage, Stored Access Policy is named set of Permissions … si=my-stored-accesspolicy … 1. Can be changed after issue 2. Limited to 5 at a time in storage
Actually Useful Valet Key Pattern Scenarios
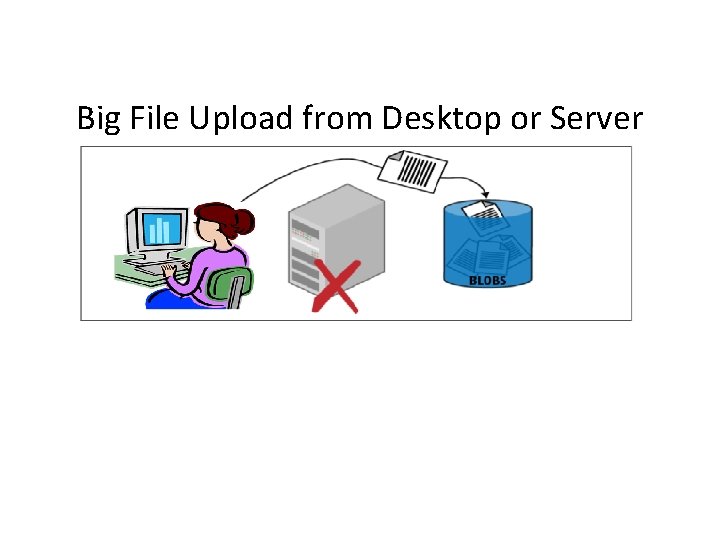
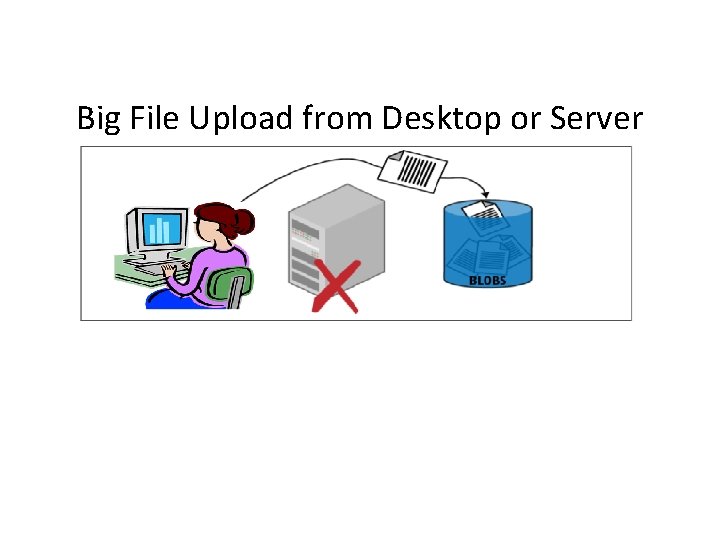
Big File Upload from Desktop or Server
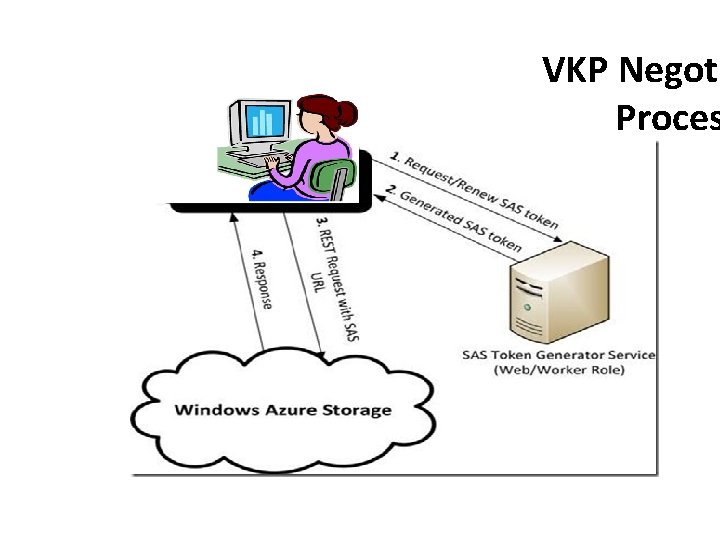
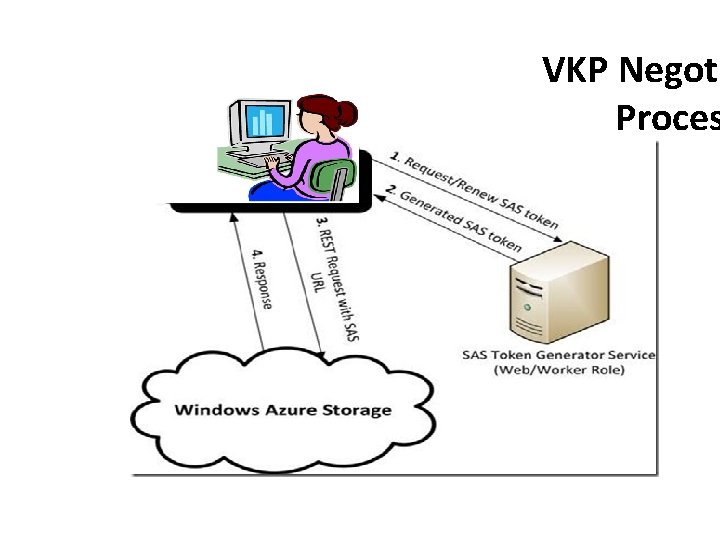
VKP Negoti Proces
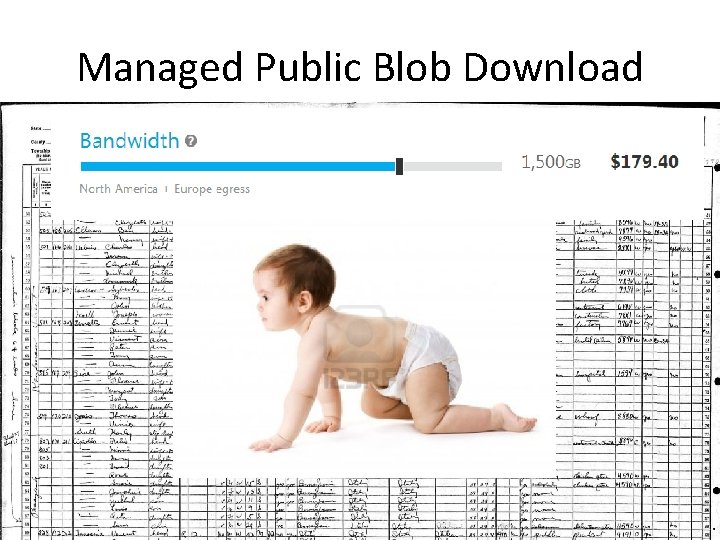
Managed Public Blob Download
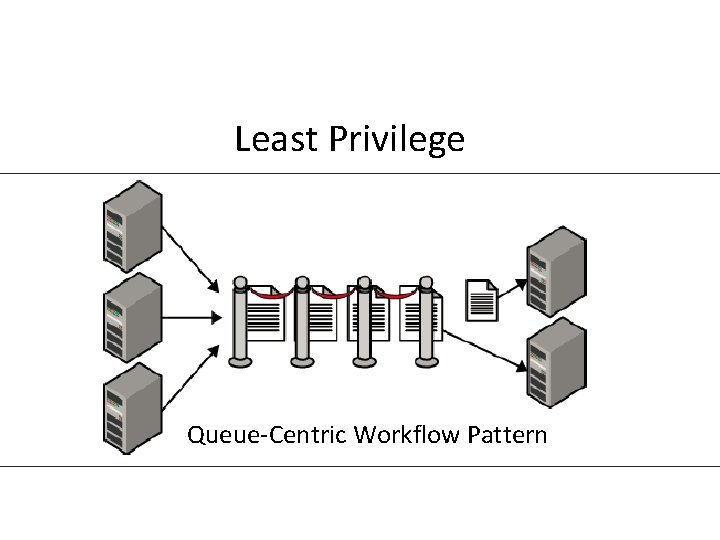
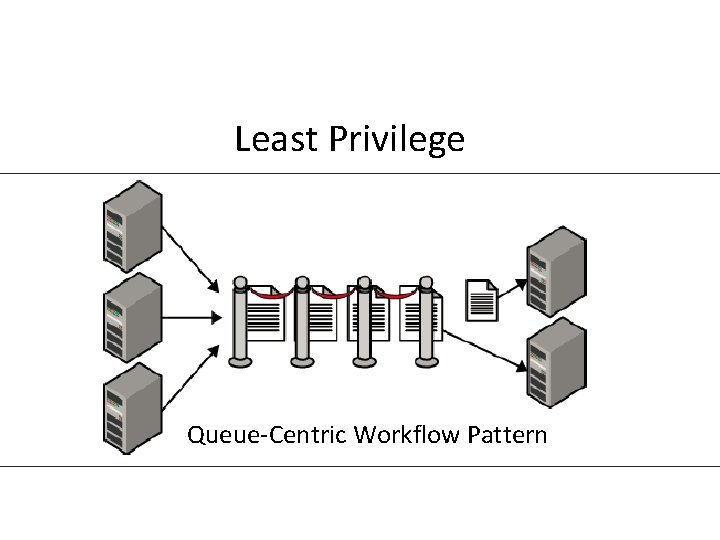
Least Privilege Queue-Centric Workflow Pattern
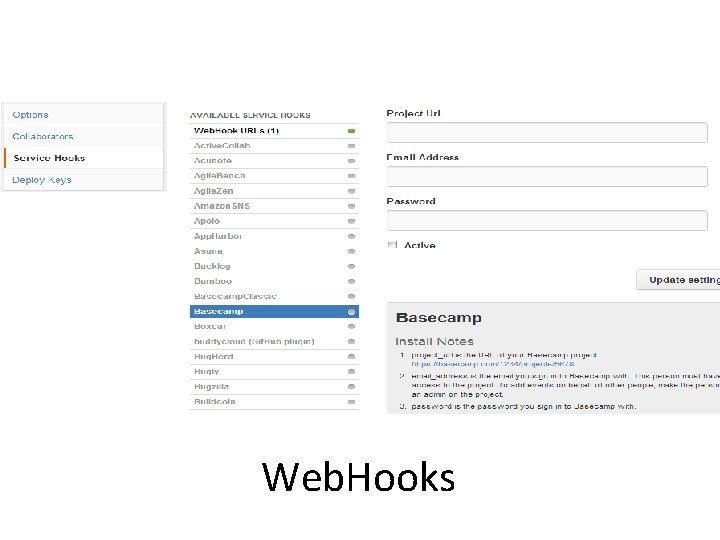
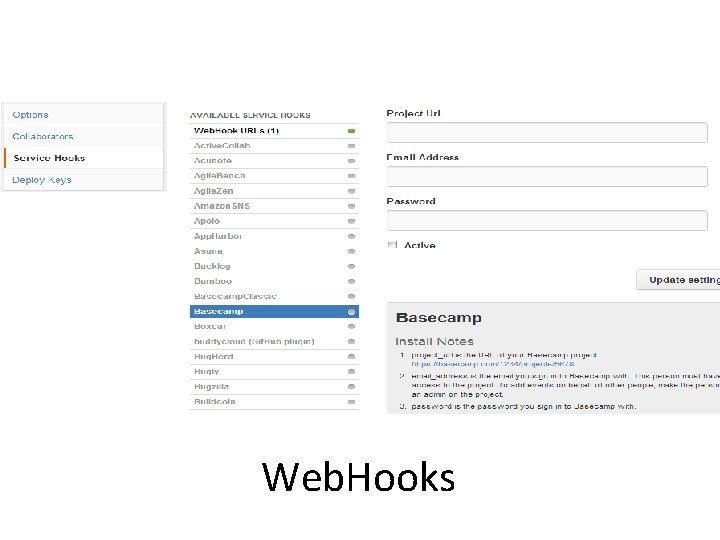
Web. Hooks

Keep it safe, kids! And stay in school.
And…. Find this slide deck here See you at Boston Azure bostonazure. org Bill Wilder @codingoutloud@gmail. com blog. codingoutloud. com linkedin. com/in/billwilder • Except where noted, slide deck is © 2014 Development Partners Software Corporation • http: //www. devpartners. com •


des questions?