HEXA Compact Data Structures for Faster Packet Processing
- Slides: 27
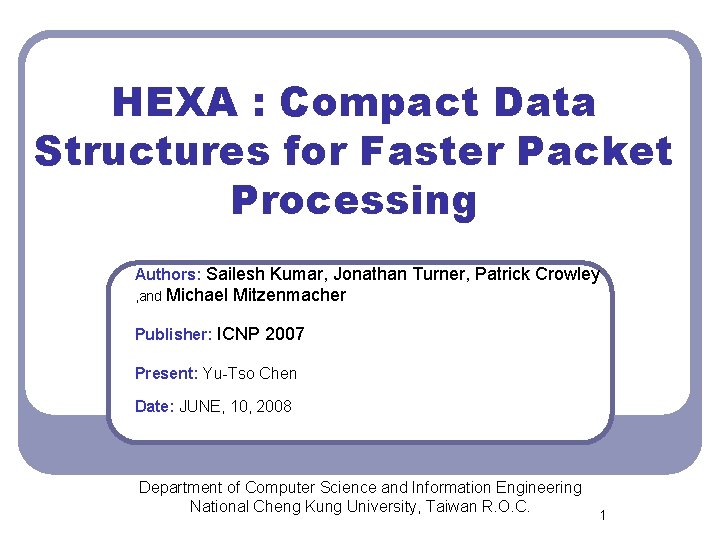
HEXA : Compact Data Structures for Faster Packet Processing Authors: Sailesh Kumar, Jonathan Turner, Patrick Crowley , and Michael Mitzenmacher Publisher: ICNP 2007 Present: Yu-Tso Chen Date: JUNE, 10, 2008 Department of Computer Science and Information Engineering National Cheng Kung University, Taiwan R. O. C. 1
Outline l l 1. Introduction 2. Proposed Approach 3. Architecture Description 4. Performance Evaluation 2
Introduction l l l HEXA (History-based Encoding, e. Xecution and addressing) Directed graphs are commonly used to implement various packet processing algorithms Used a fixed constant numbers of bits per node for structured graphs such as tries 3
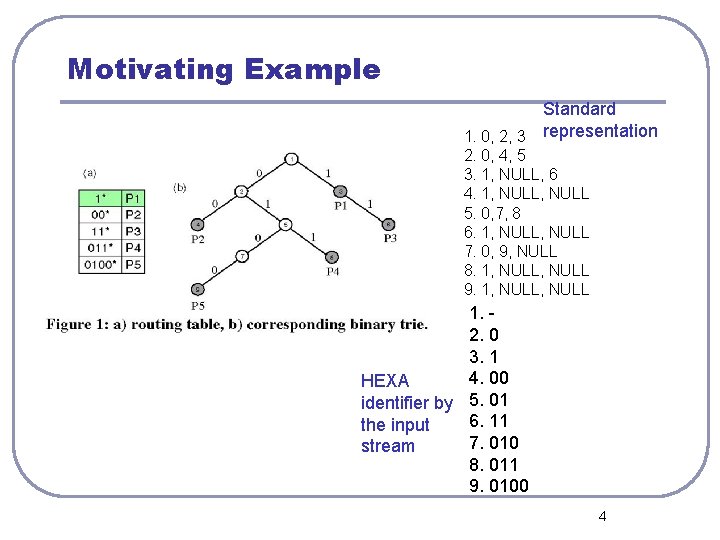
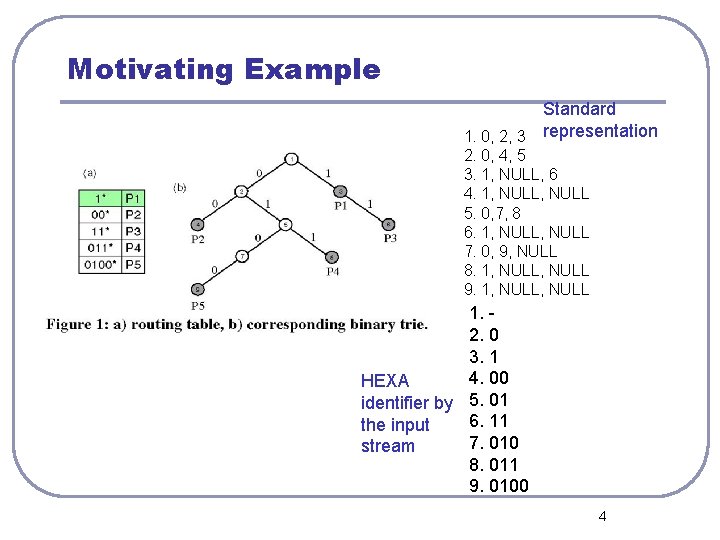
Motivating Example Standard 1. 0, 2, 3 representation 2. 0, 4, 5 3. 1, NULL, 6 4. 1, NULL 5. 0, 7, 8 6. 1, NULL 7. 0, 9, NULL 8. 1, NULL 9. 1, NULL 1. 2. 0 3. 1 4. 00 HEXA identifier by 5. 01 6. 11 the input 7. 010 stream 8. 011 9. 0100 4
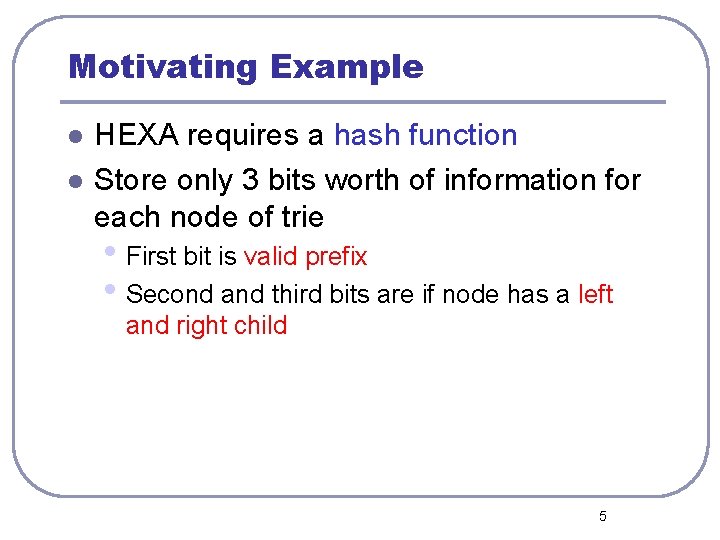
Motivating Example l l HEXA requires a hash function Store only 3 bits worth of information for each node of trie • First bit is valid prefix • Second and third bits are if node has a left and right child 5
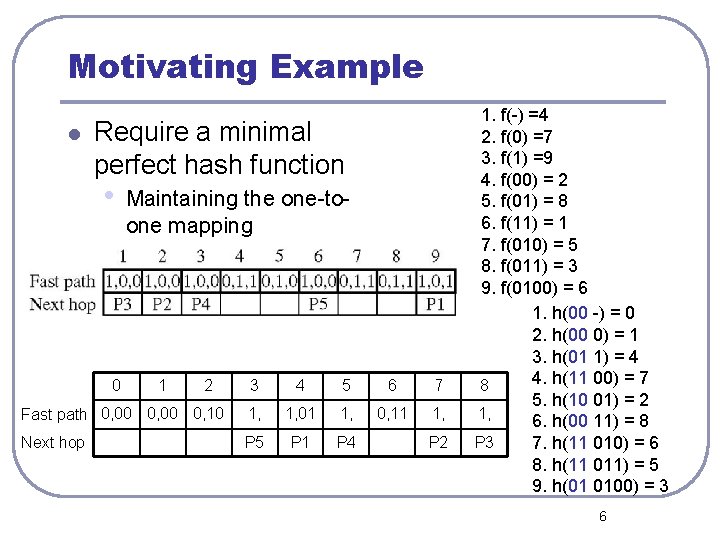
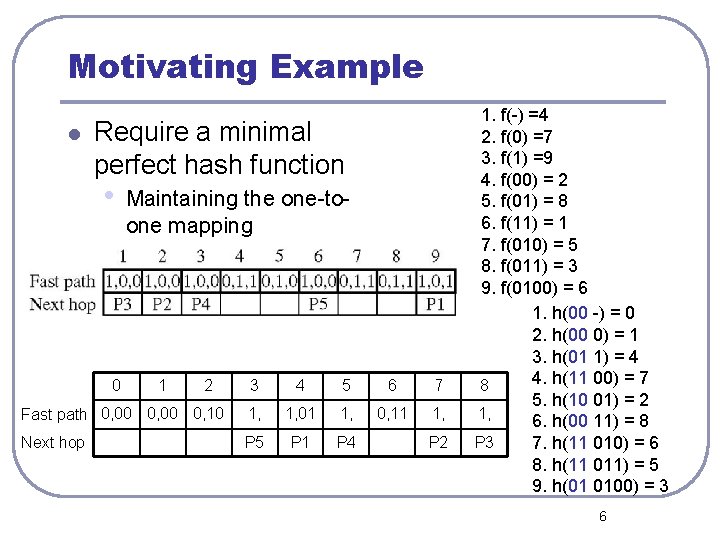
Motivating Example l Require a minimal perfect hash function • 0 Maintaining the one-toone mapping 1 2 3 4 5 6 7 Fast path 0, 00 0, 10 1, 01 1, 0, 11 1, Next hop P 5 P 1 P 4 P 2 1. f(-) =4 2. f(0) =7 3. f(1) =9 4. f(00) = 2 5. f(01) = 8 6. f(11) = 1 7. f(010) = 5 8. f(011) = 3 9. f(0100) = 6 1. h(00 -) = 0 2. h(00 0) = 1 3. h(01 1) = 4 4. h(11 00) = 7 8 5. h(10 01) = 2 1, 6. h(00 11) = 8 P 3 7. h(11 010) = 6 8. h(11 011) = 5 9. h(01 0100) = 3 6
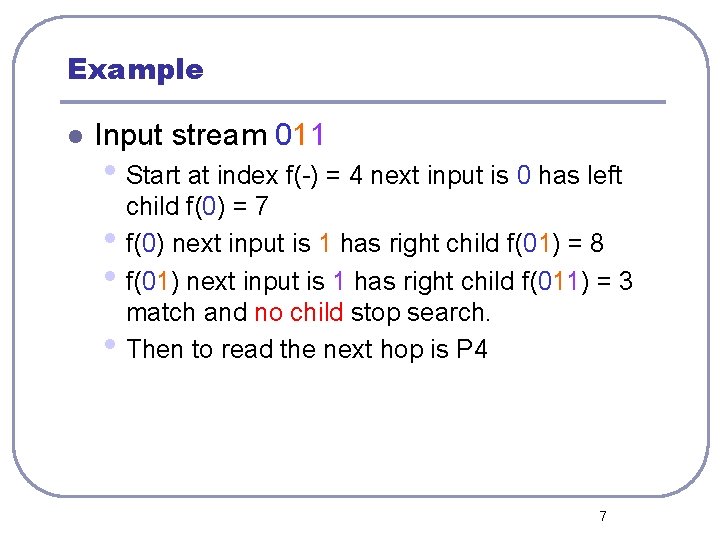
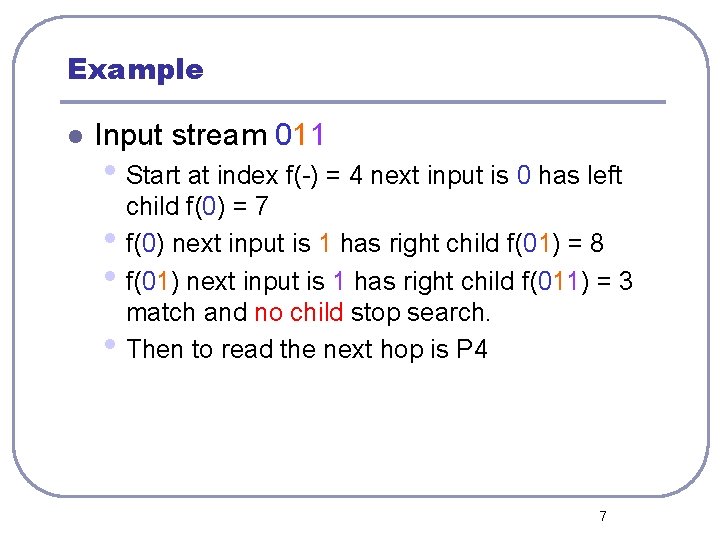
Example l Input stream 011 • Start at index f(-) = 4 next input is 0 has left • • • child f(0) = 7 f(0) next input is 1 has right child f(01) = 8 f(01) next input is 1 has right child f(011) = 3 match and no child stop search. Then to read the next hop is P 4 7
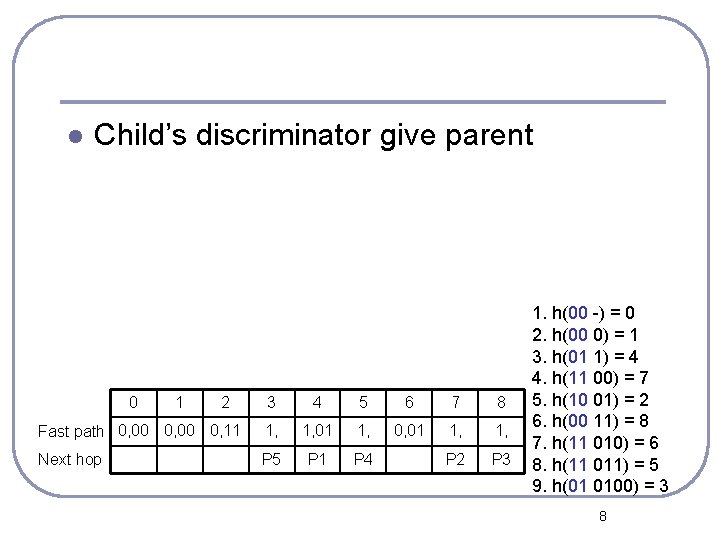
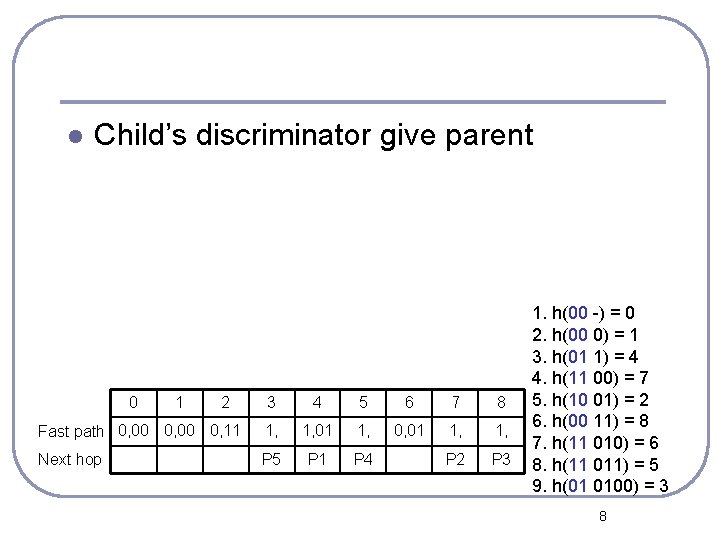
l Child’s discriminator give parent 0 1 2 3 4 5 6 7 8 Fast path 0, 00 0, 11 1, 01 1, 0, 01 1, Next hop P 5 P 1 P 4 P 2 P 3 1. h(00 -) = 0 2. h(00 0) = 1 3. h(01 1) = 4 4. h(11 00) = 7 5. h(10 01) = 2 6. h(00 11) = 8 7. h(11 010) = 6 8. h(11 011) = 5 9. h(01 0100) = 3 8
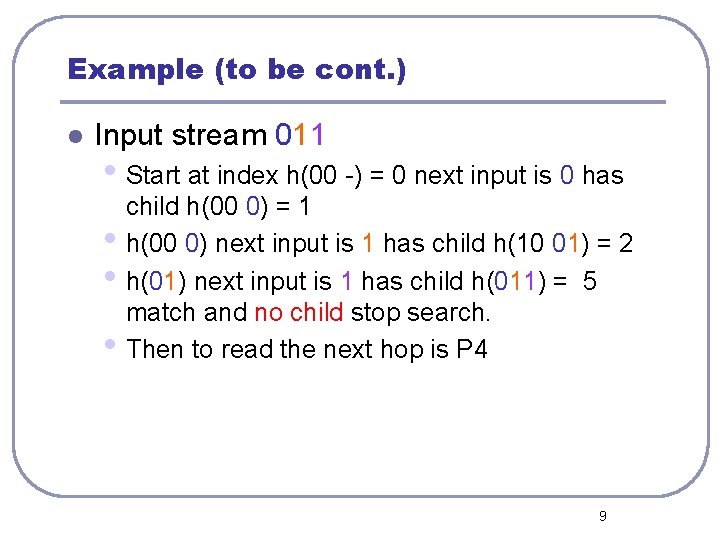
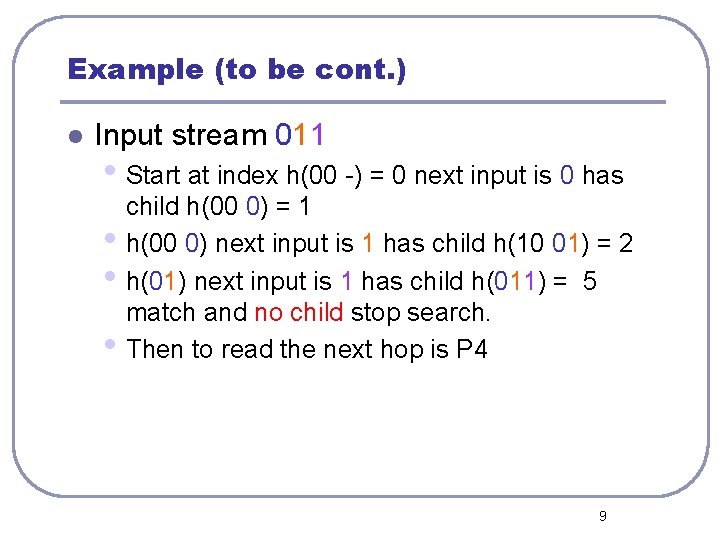
Example (to be cont. ) l Input stream 011 • Start at index h(00 -) = 0 next input is 0 has • • • child h(00 0) = 1 h(00 0) next input is 1 has child h(10 01) = 2 h(01) next input is 1 has child h(011) = 5 match and no child stop search. Then to read the next hop is P 4 9
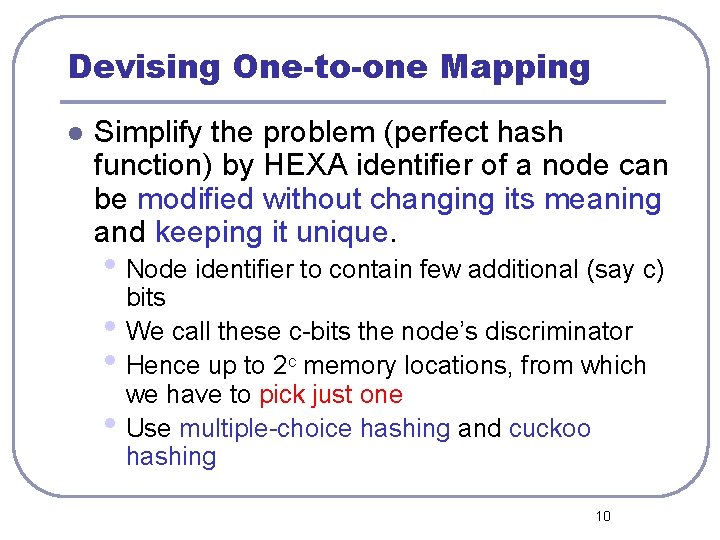
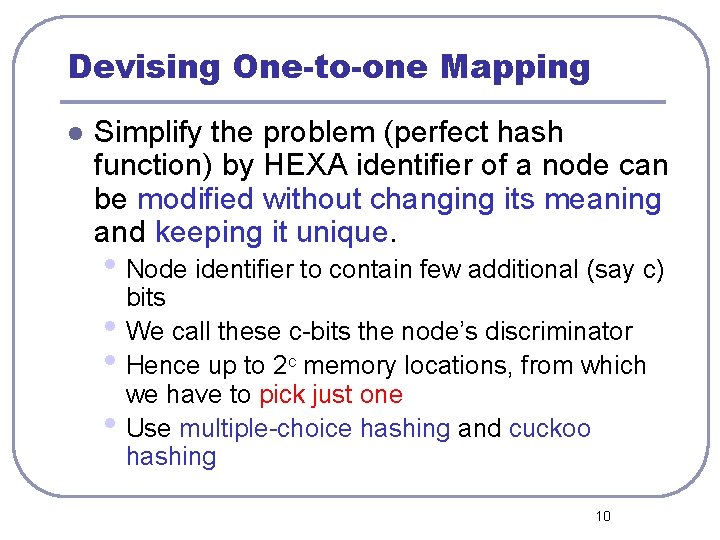
Devising One-to-one Mapping l Simplify the problem (perfect hash function) by HEXA identifier of a node can be modified without changing its meaning and keeping it unique. • Node identifier to contain few additional (say c) • • • bits We call these c-bits the node’s discriminator Hence up to 2 c memory locations, from which we have to pick just one Use multiple-choice hashing and cuckoo hashing 10
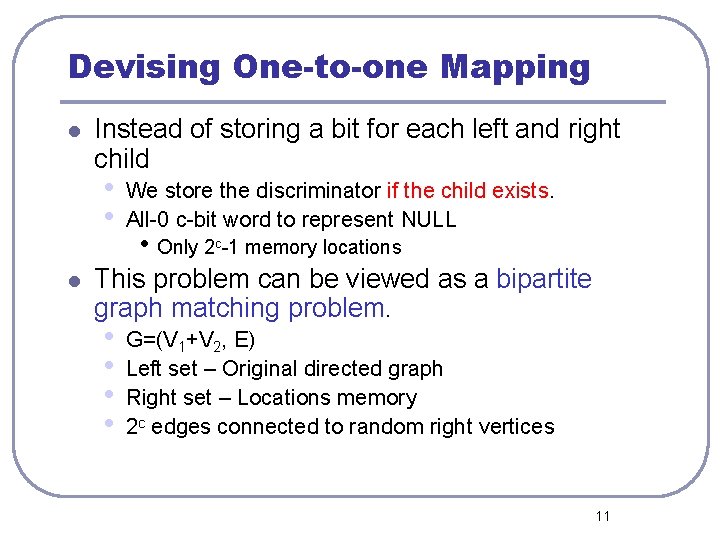
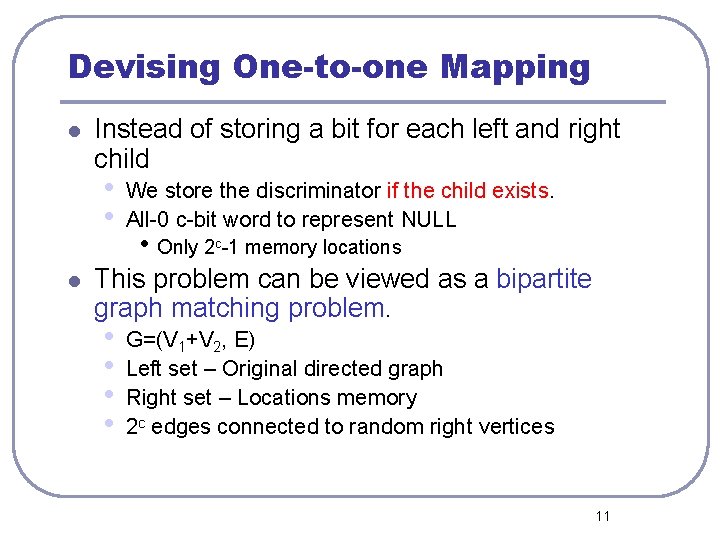
Devising One-to-one Mapping l Instead of storing a bit for each left and right child • • l We store the discriminator if the child exists. All-0 c-bit word to represent NULL • Only 2 c-1 memory locations This problem can be viewed as a bipartite graph matching problem. • • G=(V 1+V 2, E) Left set – Original directed graph Right set – Locations memory 2 c edges connected to random right vertices 11
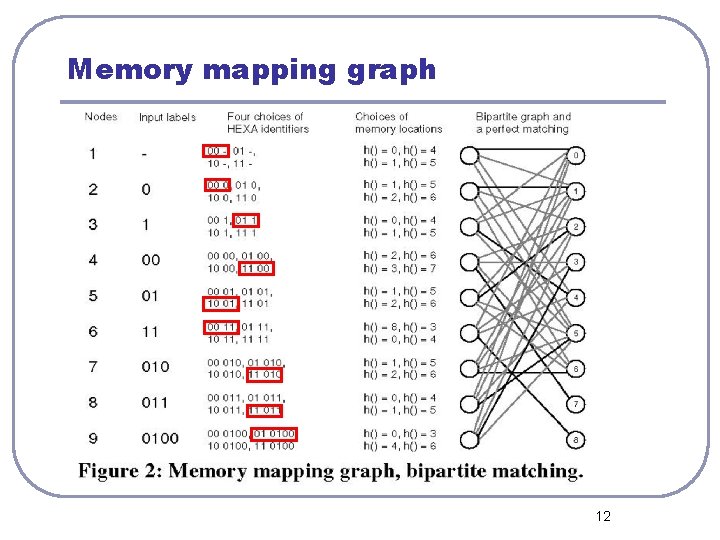
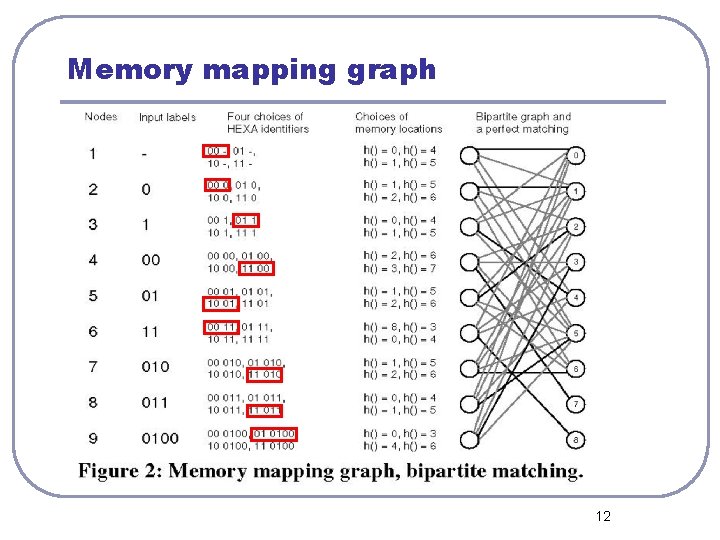
Memory mapping graph 12
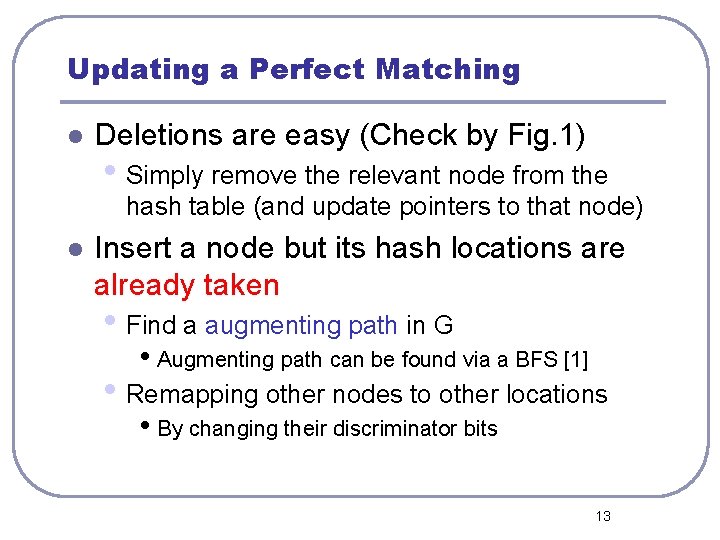
Updating a Perfect Matching l Deletions are easy (Check by Fig. 1) • Simply remove the relevant node from the hash table (and update pointers to that node) l Insert a node but its hash locations are already taken • Find a augmenting path in G • Augmenting path can be found via a BFS [1] • Remapping other nodes to other locations • By changing their discriminator bits 13
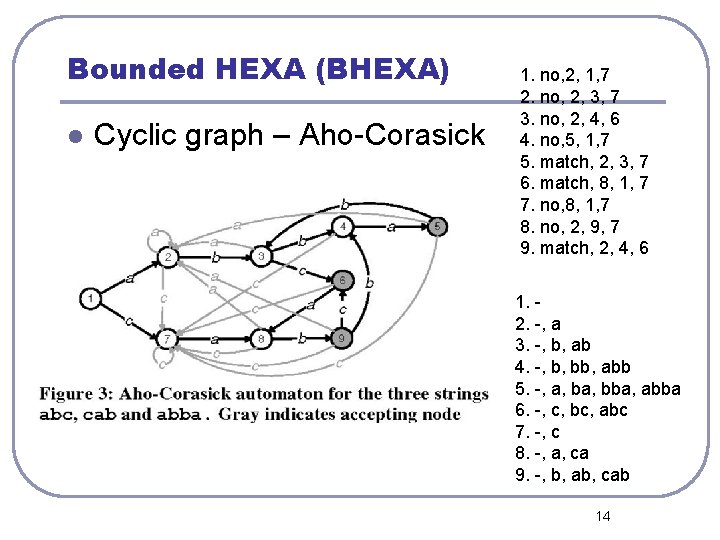
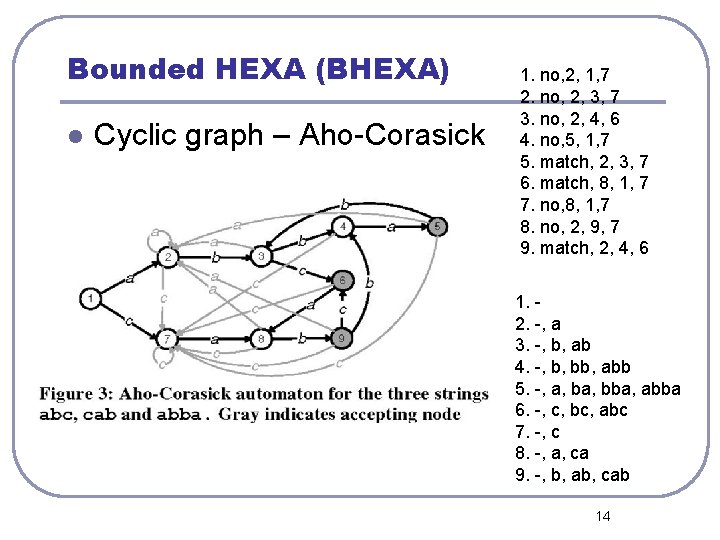
Bounded HEXA (BHEXA) l Cyclic graph – Aho-Corasick 1. no, 2, 1, 7 2. no, 2, 3, 7 3. no, 2, 4, 6 4. no, 5, 1, 7 5. match, 2, 3, 7 6. match, 8, 1, 7 7. no, 8, 1, 7 8. no, 2, 9, 7 9. match, 2, 4, 6 1. 2. -, a 3. -, b, ab 4. -, b, bb, abb 5. -, a, bba, abba 6. -, c, bc, abc 7. -, c 8. -, a, ca 9. -, b, ab, cab 14
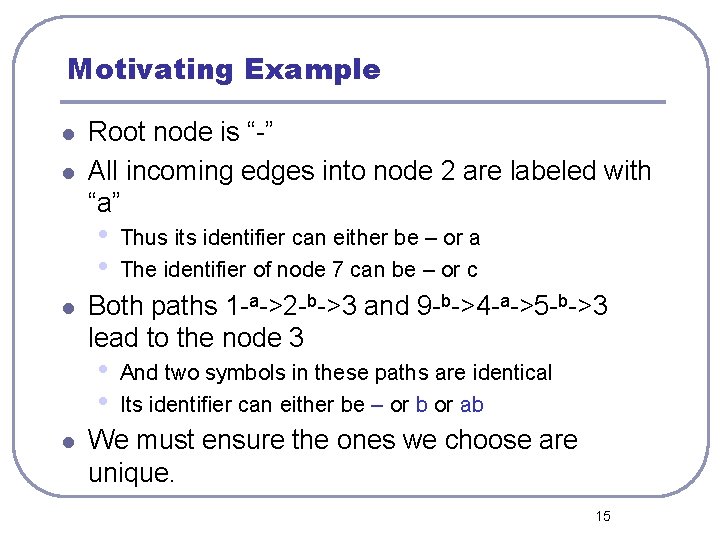
Motivating Example l l Root node is “-” All incoming edges into node 2 are labeled with “a” • • l Both paths 1 -a->2 -b->3 and 9 -b->4 -a->5 -b->3 lead to the node 3 • • l Thus its identifier can either be – or a The identifier of node 7 can be – or c And two symbols in these paths are identical Its identifier can either be – or b or ab We must ensure the ones we choose are unique. 15
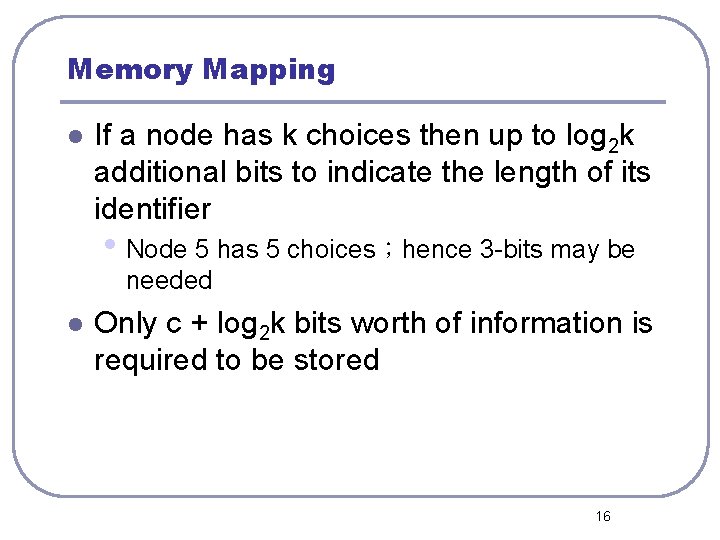
Memory Mapping l If a node has k choices then up to log 2 k additional bits to indicate the length of its identifier • Node 5 has 5 choices;hence 3 -bits may be needed l Only c + log 2 k bits worth of information is required to be stored 16
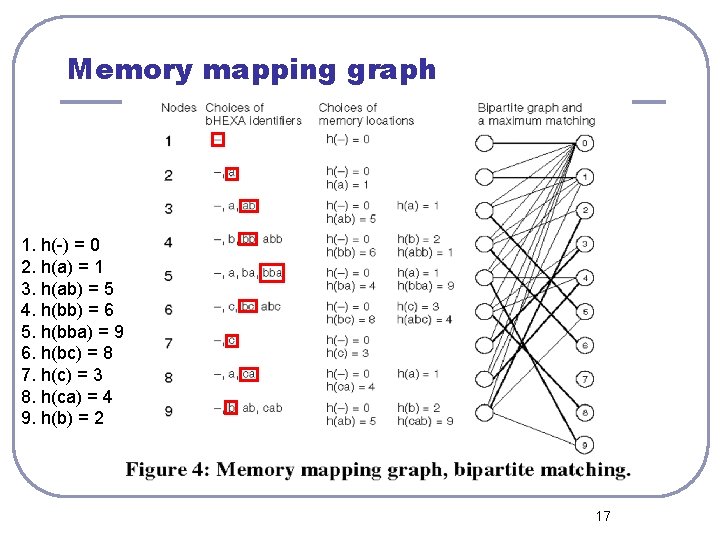
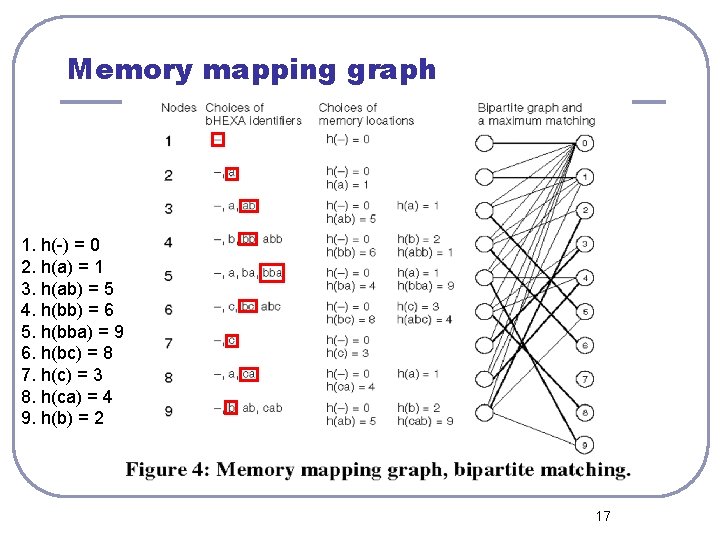
Memory mapping graph 1. h(-) = 0 2. h(a) = 1 3. h(ab) = 5 4. h(bb) = 6 5. h(bba) = 9 6. h(bc) = 8 7. h(c) = 3 8. h(ca) = 4 9. h(b) = 2 17
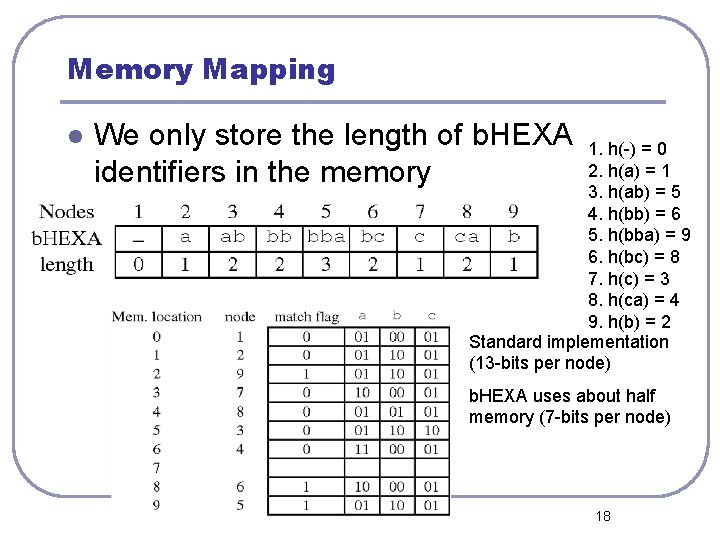
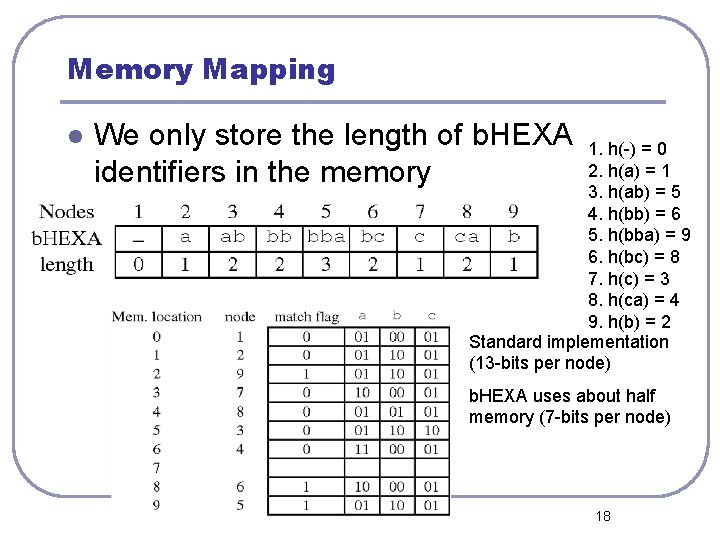
Memory Mapping l We only store the length of b. HEXA identifiers in the memory 1. h(-) = 0 2. h(a) = 1 3. h(ab) = 5 4. h(bb) = 6 5. h(bba) = 9 6. h(bc) = 8 7. h(c) = 3 8. h(ca) = 4 9. h(b) = 2 Standard implementation (13 -bits per node) b. HEXA uses about half memory (7 -bits per node) 18
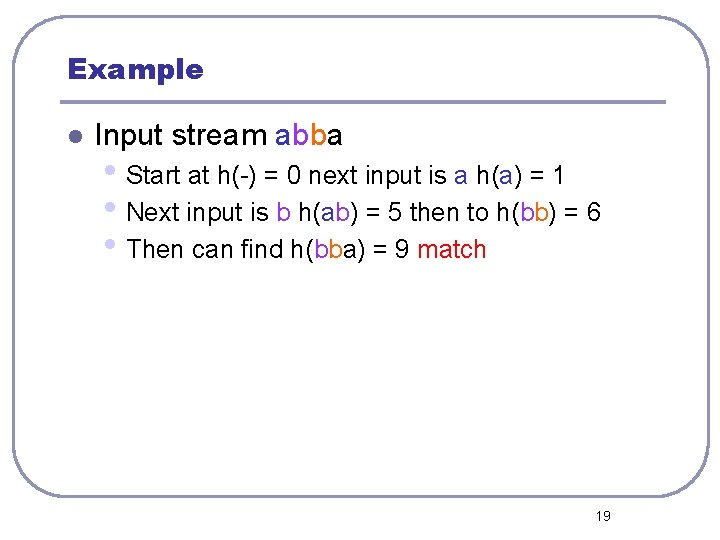
Example l Input stream abba • Start at h(-) = 0 next input is a h(a) = 1 • Next input is b h(ab) = 5 then to h(bb) = 6 • Then can find h(bba) = 9 match 19
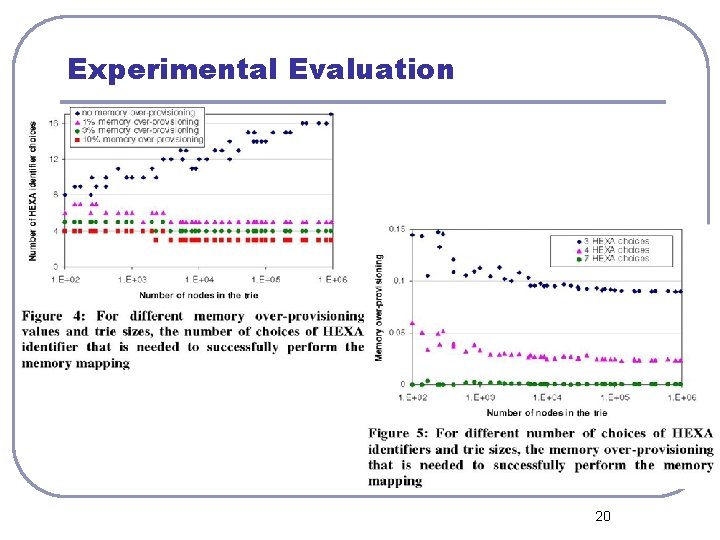
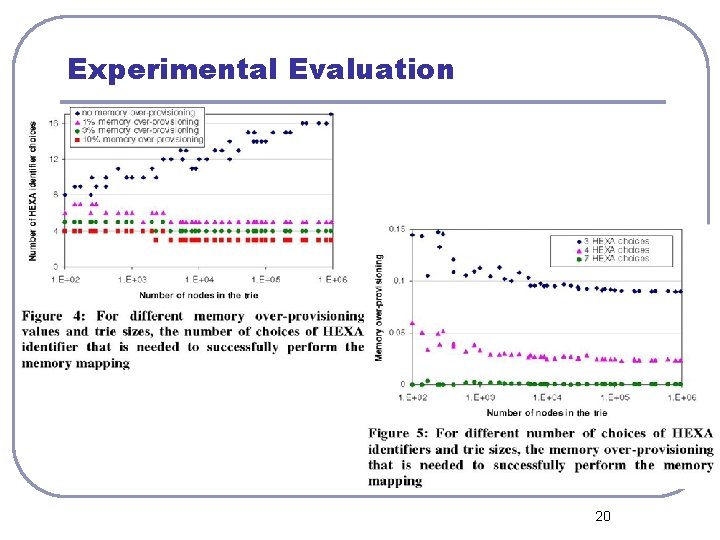
Experimental Evaluation 20
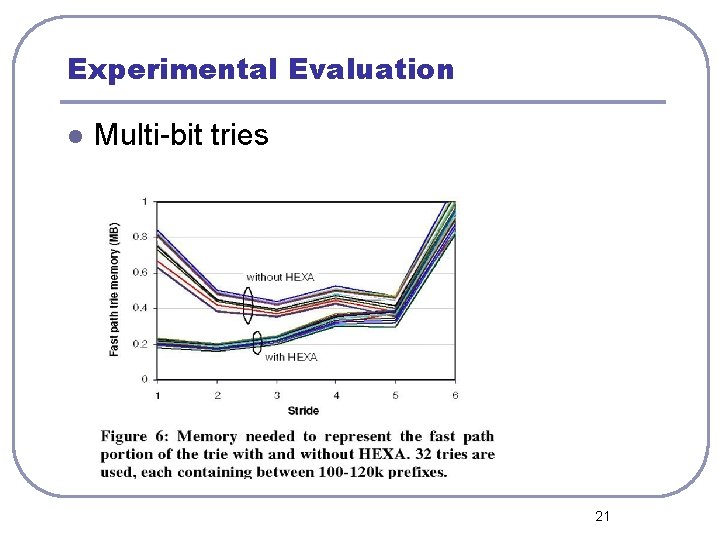
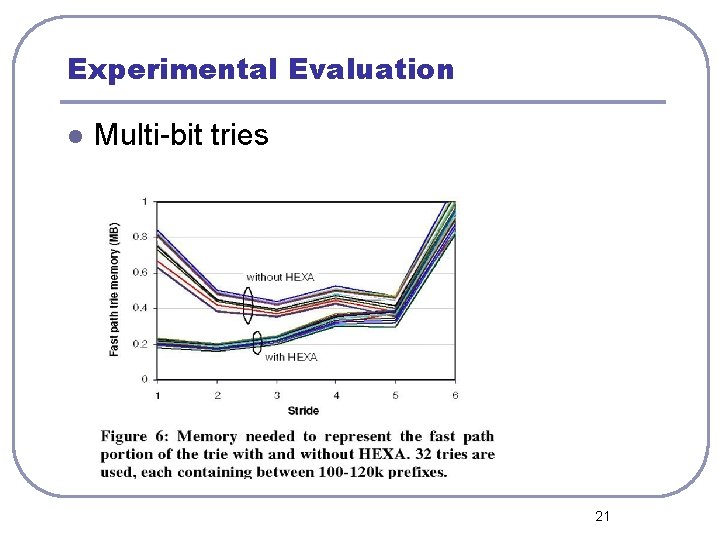
Experimental Evaluation l Multi-bit tries 21
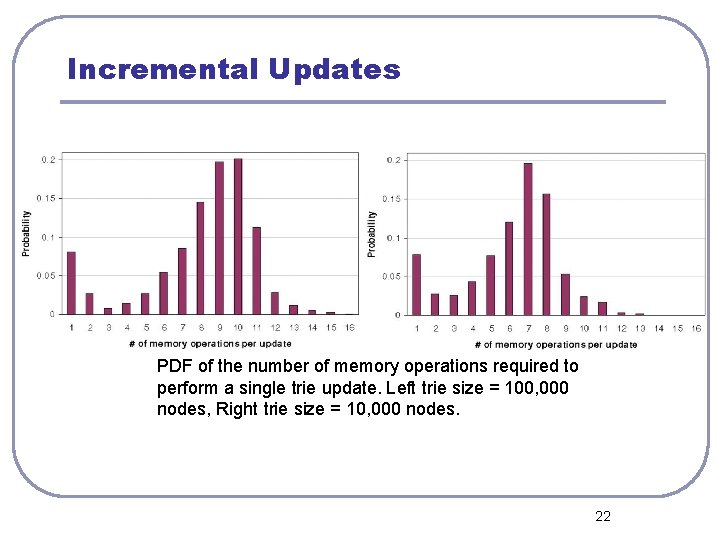
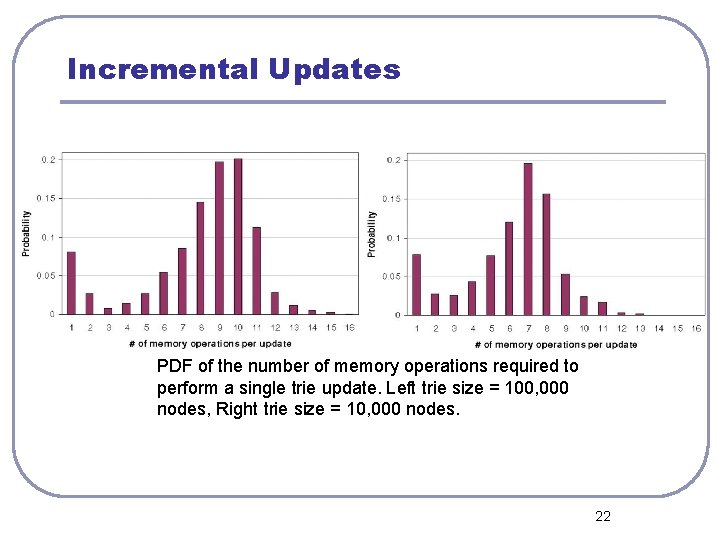
Incremental Updates PDF of the number of memory operations required to perform a single trie update. Left trie size = 100, 000 nodes, Right trie size = 10, 000 nodes. 22
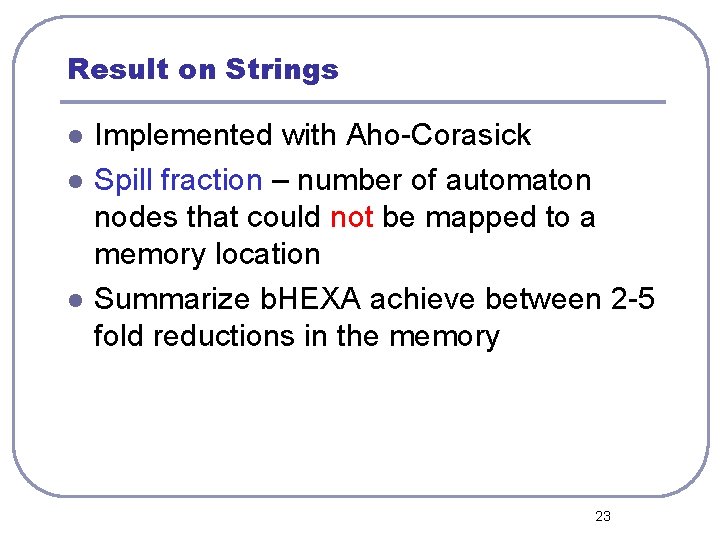
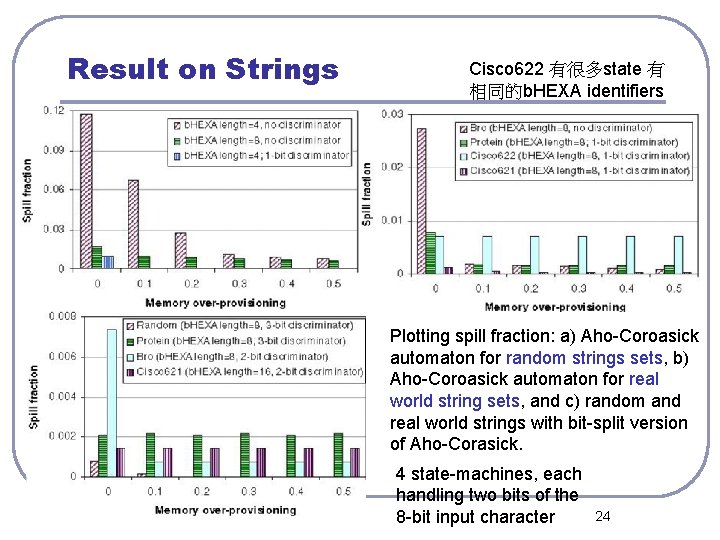
Result on Strings l l l Implemented with Aho-Corasick Spill fraction – number of automaton nodes that could not be mapped to a memory location Summarize b. HEXA achieve between 2 -5 fold reductions in the memory 23
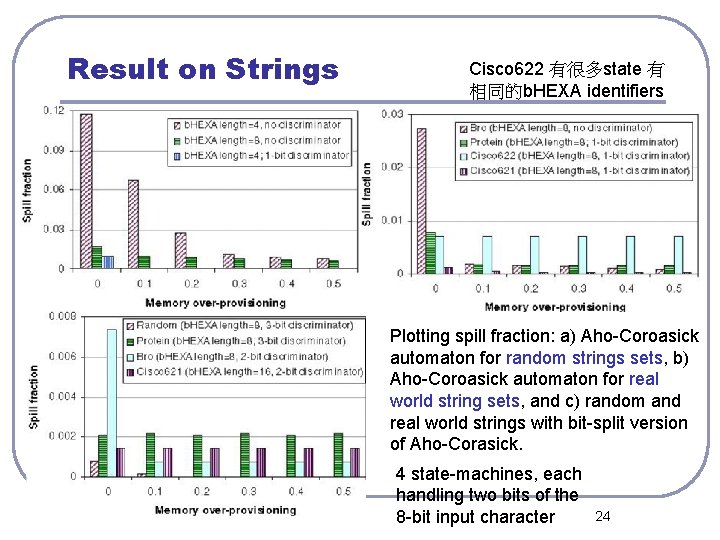
Result on Strings Cisco 622 有很多state 有 相同的b. HEXA identifiers Plotting spill fraction: a) Aho-Coroasick automaton for random strings sets, b) Aho-Coroasick automaton for real world string sets, and c) random and real world strings with bit-split version of Aho-Corasick. 4 state-machines, each handling two bits of the 8 -bit input character 24
l Tanks for your attention 25
Devising One-to-one Mapping l l If we require m=n, c is loglogn + O(1) to ensure perfect matching exists with high probability Fig. 2 we assume that the hash function is simply the numerical value of the identifier modulo 9 26
Memory Mapping l l m=10 h=(sum from i=1 to k Si x i )mod 10 • - = 0, a = 1, b = 2, c = 3 27