Health Information Management Technology An Applied Approach Chapter
- Slides: 33
Health Information Management Technology: An Applied Approach Chapter 10 Data Security © 2016
Data Security • Measures and tools to safeguard data, and the information systems on which they reside, from unauthorized access, use, disclosure, disruption, modification, or destruction (NIST)
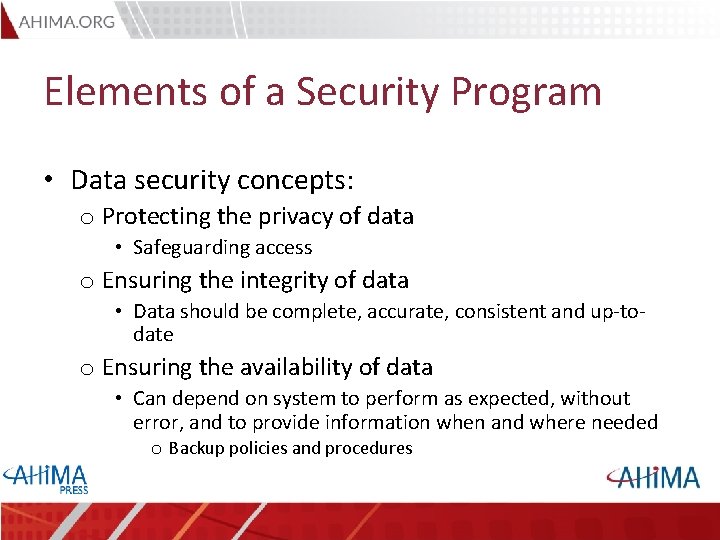
Elements of a Security Program • Data security concepts: o Protecting the privacy of data • Safeguarding access o Ensuring the integrity of data • Data should be complete, accurate, consistent and up-todate o Ensuring the availability of data • Can depend on system to perform as expected, without error, and to provide information when and where needed o Backup policies and procedures
Data Security Threats • Threats can be internal (from within an organization) or external (from outside an organization) • Potential threats to data security are caused by two main sources: o Threats caused by people o Threats caused by environmental and hardware or software factors
Threats Caused by People • Threats from insiders who make unintentional mistakes • Threats from insiders who abuse their access privileges to information • Threats from insiders who access information or computer systems for spite or profit • Threats from intruders who attempt to access information or steal physical resources • Threats from vengeful employees or outsiders who mount attacks on the organization’s information system
Threats Caused by Environmental and Hardware or Software Factors • • • Natural disasters Utility, hardware, and software failures Electrical outages and power surges Hardware or software malfunction Malicious software applications (malware)
Security Management Structure • Chief Security Officer (CSO) • Advisory or policy-making group (such as an information security committee) o o o Executive-level managers Health information management director or designee Chief information officer (CIO) Information technology system directors Network engineers Representatives from clinical departments
Components of a Security Program • A good security program should include: o o o o Employee awareness Risk management program Access safeguards Physical and administrative safeguards Software application safeguards Network safeguards Disaster planning and recovery Data quality control processes
Security Program: Employee Awareness • Train employees to recognize, respond, and report • New employee education o Policies and procedures • Including mobile devices, e-mails, faxes, social media • Annual signed confidentiality agreements • Periodic and ongoing security reminders
Security Program: Risk Management Program • Risk Analysis o Identify all security threats o Estimate how likely it is that risk may occur (likelihood determination) o Eliminate the impact of an untoward event (impact analysis) o Determine the value of information assets
Security Program: Risk Management Program • Incident Detection o Monitor information systems for abnormalities • Incident Response Plan o Watch and warn o Repair and report o Pursue and prosecute
Security Program: Access Safeguards • Identify which employees should have access to what data o Role-based access (RBAC) o User-based access (UBAC) o Context-based access control (CBAC) • Access controls that restrict access when necessary but allow access to complete job tasks • Develop procedures and methods for identification, authentication, and authorization of users
Security Program: Access Safeguards – Access Control Mechanisms • Identification: establish user IDs and or numbers • Authentication: verify the user o o o Password or PIN (something you know) Smart card or token (something you have) Biometrics (something you are) Two-factor authentication (combination of these) Single Sign-on • Authorization: permission given to an individual o CAPTCHA
Security Program: Physical and Administrative Safeguards • Physical safeguards: Protection from physical damage (natural elements, theft) o Secure and structurally sound locations o Physical separation and barriers • Administrative safeguards: Policies and procedures that address management of computer resources o Includes Information Technology Asset Disposition (ITAD) to identify how all data storage devices are destroyed and purged of data prior to repurposing or disposal
Security Program: Software Application Safeguards • Authentication • Edit checks • Audit trails
Security Program: Network Safeguards • Firewalls • Cryptographic technologies o Encryption (private key or public key) o Digital signatures o Digital certificates • Web security protocols • Intrusion detection systems
Security Program: Disaster Planning and Recovery • Disaster planning o Contingency plan: set of procedures to follow when responding to emergencies • Based on information gathered during risk assessment and analysis o Identify minimum allowable time for system disruption o Identify alternatives for system continuation o Evaluate cost and feasibility of each alternative o Develop procedures required to active the plan
Security Program: Disaster Planning and Recovery • Disaster Recovery o Disaster recovery plan addresses resources, actions, tasks, and data necessary to restore critical services as soon as possible and to manage business recovery processes • Business continuity plan o How to continue operations during computer system shutdown • Emergency mode of operations o Processes and controls to follow until operations are fully restored
Security Program: Data Quality Control Processes • Availability: data are easily obtainable • Consistency: data do not change • Definition: clear meaning for every data element
HIPAA Security Provisions • Health Insurance Portability and Accountability Act of 1996 o Security standards implemented 2005 o Security compliance responsibility of Office for Civil Rights (OCR) o Privacy Law revised in February of 2009 • HITECH improves enforcement of privacy and security rules
HIPAA Security Provisions: General Rules • Security program must document confidentiality, integrity and availability of all e. PHI • Protect e. PHI against reasonably anticipated threats or hazards to its security or integrity • Protect e. PHI against reasonable or anticipated uses or disclosures not permitted under the HIPAA Privacy Rule • Ensure workforce compliance with HIPAA Security Rule
HIPAA Security Provisions: General Rules • Security Rule is: o Flexible – security measures may be adopted that are appropriate and reasonable for the organization o Scalable – accommodates organizations of any size o Technology neutral – specific technologies are not prescribed
HIPAA Security Provisions: General Rules • Security Rule applies to: o Covered entities o Business associates o Hybrid entities o Other related entities
HIPAA Security Provisions: General Rules • Implementation specifications: o Required o Addressable (not optional) – covered entity must conduct risk assessment and evaluate whether the specification is appropriate as written • If not, must document why not • Must implement equivalent alternative method if reasonable and appropriate
HIPAA Security Provisions: 5 Categories • Provisions 1. 2. 3. 4. 5. Administrative safeguards Physical safeguards Technical safeguards Organizational requirements and policies Policies and documentation requirements
HIPAA Security Rule: Administrative Safeguards • • • Security management process Assigned security responsibility Workforce security Information access management Security awareness and training Security incident procedures Contingency plan Evaluation Business associate contracts
HIPAA Security Rule: Physical Safeguards • • Facility access controls Workstation use Workstation security Device and media controls
HIPAA Security Rule: Technical Safeguards • • • Access control Audit controls Integrity Person or entity authentication Transmission security
HIPAA Security Rule: Organizational Requirements • Business associate or other contracts • Group health plan requirements
HIPAA Security Rule: Policies and Procedures and Documentation Requirements • Policies and procedures • Documentation
American Recovery and Reinvestment Act and HITECH Changes • Changes o Business associates must comply with most of the same rules as covered entities (increase in potential BA liability) o Breach notification requirements for breaches of unsecured e. PHI • e. PHI that has not been made unusable, unreadable, or indecipherable to unauthorized persons • Encryption secures e. PHI • Affects data at rest, in motion, in use, and disposed
Forensics • Security committee or designated individuals must review o Access logs at specified intervals o Audit trails based on trigger events o Failed logins
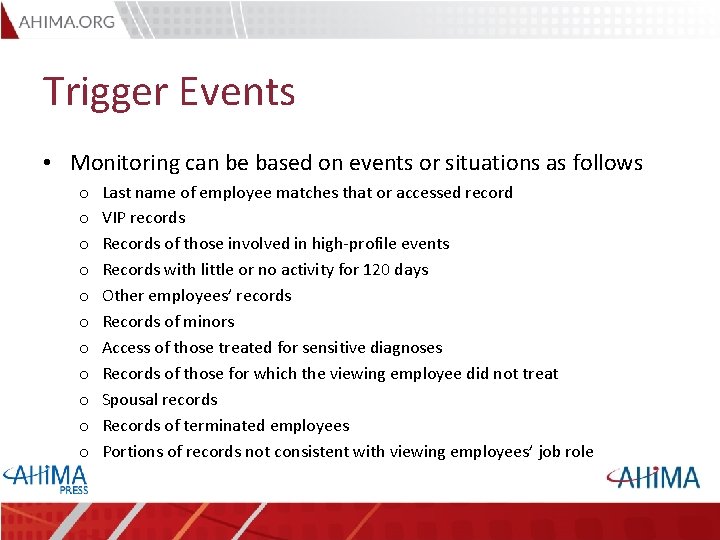
Trigger Events • Monitoring can be based on events or situations as follows o o o Last name of employee matches that or accessed record VIP records Records of those involved in high-profile events Records with little or no activity for 120 days Other employees’ records Records of minors Access of those treated for sensitive diagnoses Records of those for which the viewing employee did not treat Spousal records Records of terminated employees Portions of records not consistent with viewing employees’ job role