Hasil Scan Situs Internet Bank Onno W Purbo
Hasil Scan Situs Internet Bank Onno W. Purbo Onno@indo. net. id
Tool yang digunakan n n nmap openssl
Korban n n n www. bi. go. id www. bii. co. id www. bni. co. id www. bankmandiri. co. id www. klikbca. com ibank. klikbca. com
![www. bi. go. id [root@yc 1 dav onno]# nmap -v -s. S www. bi. www. bi. go. id [root@yc 1 dav onno]# nmap -v -s. S www. bi.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-4.jpg)
www. bi. go. id [root@yc 1 dav onno]# nmap -v -s. S www. bi. go. id Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host psk. bi. go. id (202. 152. 5. 17) appears to be up. . . good. Initiating SYN half-open stealth scan against psk. bi. go. id (202. 152. 5. 17) Adding TCP port 21 (state open). Adding TCP port 22 (state open). Adding TCP port 20 (state open). Adding TCP port 80 (state open). Adding TCP port 5631 (state open). Adding TCP port 23 (state open). The SYN scan took 75 seconds to scan 1523 ports.

www. bi. go. id. . Interesting ports on psk. bi. go. id (202. 152. 5. 17): (The 1508 ports scanned but not shown below are in state: closed) Port State Service 20/tcp open ftp-data 21/tcp open ftp 22/tcp open ssh 23/tcp open telnet 80/tcp open http 137/tcp filtered netbios-ns 138/tcp filtered netbios-dgm 139/tcp filtered netbios-ssn 1524/tcp filtered ingreslock 2041/tcp filtered interbase 5631/tcp open pcanywheredata 6000/tcp filtered X 11 12345/tcp filtered Net. Bus 12346/tcp filtered Net. Bus
![www. bni. co. id [root@yc 1 dav onno]# nmap -v -s. S www. bni. www. bni. co. id [root@yc 1 dav onno]# nmap -v -s. S www. bni.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-6.jpg)
www. bni. co. id [root@yc 1 dav onno]# nmap -v -s. S www. bni. co. id Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host admin. bankmandiri. co. id (202. 155. 27. 222) appears to be up. . . good. Initiating SYN half-open stealth scan against admin. bankmandiri. co. id (202. 155. 27. 222) Adding TCP port 80 (state open). Adding TCP port 21 (state open). caught SIGINT signal, cleaning up
![www. bii. co. id [root@yc 1 dav onno]# nmap -v -s. S www. bii. www. bii. co. id [root@yc 1 dav onno]# nmap -v -s. S www. bii.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-7.jpg)
www. bii. co. id [root@yc 1 dav onno]# nmap -v -s. S www. bii. co. id Starting nmap V. 2. 53 by fyodor@insecure. org (www. insecure. org/nmap/ ) Host www. bii. co. id (202. 152. 2. 29) appears to be up. . . good. Initiating SYN half-open stealth scan against www. bii. co. id (202. 152. 2. 29) Adding TCP port 80 (state open). The SYN scan took 332 seconds to scan 1523 ports. Interesting ports on www. bii. co. id (202. 152. 2. 29): (The 1522 ports scanned but not shown below are in state: filtered) Port State Service 80/tcp open http TCP Sequence Prediction: Class=random positive increments Difficulty=411558 (Good luck!)
![http: //www. btn. co. id [root@586 onno]# nmap -v -s. S www. btn. co. http: //www. btn. co. id [root@586 onno]# nmap -v -s. S www. btn. co.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-8.jpg)
http: //www. btn. co. id [root@586 onno]# nmap -v -s. S www. btn. co. id Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host www. btn. co. id (202. 147. 255. 18) appears to be up. . . good. Initiating SYN half-open stealth scan against www. btn. co. id (202. 147. 255. 18) Adding TCP port 80 (state open). The SYN scan took 283 seconds to scan 1523 ports. Interesting ports on www. btn. co. id (202. 147. 255. 18): (The 1522 ports scanned but not shown below are in state: filtered) Port State Service 80/tcp open http Nmap run completed -- 1 IP address (1 host up) scanned in 284 seconds
![http: //www. lippobank. com [root@586 onno]# nmap -v -s. S www. lippobank. com Starting http: //www. lippobank. com [root@586 onno]# nmap -v -s. S www. lippobank. com Starting](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-9.jpg)
http: //www. lippobank. com [root@586 onno]# nmap -v -s. S www. lippobank. com Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host www 3. infostreet. com (206. 185. 24. 3) appears to be up. . . good. Initiating SYN half-open stealth scan against www 3. infostreet. com (206. 185. 24. 3)Adding TCP port 25 (state open). Adding TCP port 21 (state open). Adding TCP port 80 (state open). caught SIGINT signal, cleaning up [root@586 onno]#
![http: //www. bankmandiri. co. id [root@586 onno]# nmap -v -s. S www. bankmandiri. co. http: //www. bankmandiri. co. id [root@586 onno]# nmap -v -s. S www. bankmandiri. co.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-10.jpg)
http: //www. bankmandiri. co. id [root@586 onno]# nmap -v -s. S www. bankmandiri. co. id Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host www. bankmandiri. co. id (202. 155. 27. 222) appears to be up. . . good. Initiating SYN half-open stealth scan against www. bankmandiri. co. id (202. 155. 27. 222) Adding TCP port 21 (state open). Adding TCP port 80 (state open). The SYN scan took 512 seconds to scan 1523 ports. Interesting ports on www. bankmandiri. co. id (202. 155. 27. 222): (The 1520 ports scanned but not shown below are in state: filtered) Port State Service 20/tcp closed ftp-data 21/tcp open ftp 80/tcp open http Nmap run completed -- 1 IP address (1 host up) scanned in 515 seconds
![http: //www. bankdanamon. co m [root@586 onno]# nmap -v -s. S www. bankdanamon. com http: //www. bankdanamon. co m [root@586 onno]# nmap -v -s. S www. bankdanamon. com](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-11.jpg)
http: //www. bankdanamon. co m [root@586 onno]# nmap -v -s. S www. bankdanamon. com Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host redirect. dnsix. com (64. 75. 34. 136) appears to be up. . . good. Initiating SYN half-open stealth scan against redirect. dnsix. com (64. 75. 34. 136) Adding TCP port 80 (state open). The SYN scan took 214 seconds to scan 1523 ports. Interesting ports on redirect. dnsix. com (64. 75. 34. 136): (The 1522 ports scanned but not shown below are in state: filtered) Port State Service 80/tcp open http Nmap run completed -- 1 IP address (1 host up) scanned in 217 seconds
![ibank. klikbca. com [root@yc 1 dav onno]# nmap -vv -s. S -O ibank. klikbca. ibank. klikbca. com [root@yc 1 dav onno]# nmap -vv -s. S -O ibank. klikbca.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-12.jpg)
ibank. klikbca. com [root@yc 1 dav onno]# nmap -vv -s. S -O ibank. klikbca. com Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host (202. 158. 15. 52) appears to be down, skipping it. Note: Host seems down. If it is really up, but blocking our ping probes, try -P 0 Nmap run completed -- 1 IP address (0 hosts up) scanned in 43 seconds
![www. klikbca. com [root@yc 1 dav onno]# nmap -vv -s. S -O www. klikbca. www. klikbca. com [root@yc 1 dav onno]# nmap -vv -s. S -O www. klikbca.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-13.jpg)
www. klikbca. com [root@yc 1 dav onno]# nmap -vv -s. S -O www. klikbca. com Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host (202. 158. 15. 51) appears to be down, skipping it. Note: Host seems down. If it is really up, but blocking our ping probes, try -P 0 Nmap run completed -- 1 IP address (0 hosts up) scanned in 60 seconds
Keamanan https: //ibank. . . $ openssl s_client -host ibank. klikbca. com -port 443 CONNECTED(00000003) depth=1 /O=Veri. Sign Trust Network /OU=Veri. Sign, Inc. /OU=Veri. Sign International Server CA - Class 3 /OU=www. verisign. com /CPS Incorp. by Ref. LIABILITY LTD. © 97 Veri. Sign verify error: num=20: unable to get local issuer certificate verify return: 0 ---
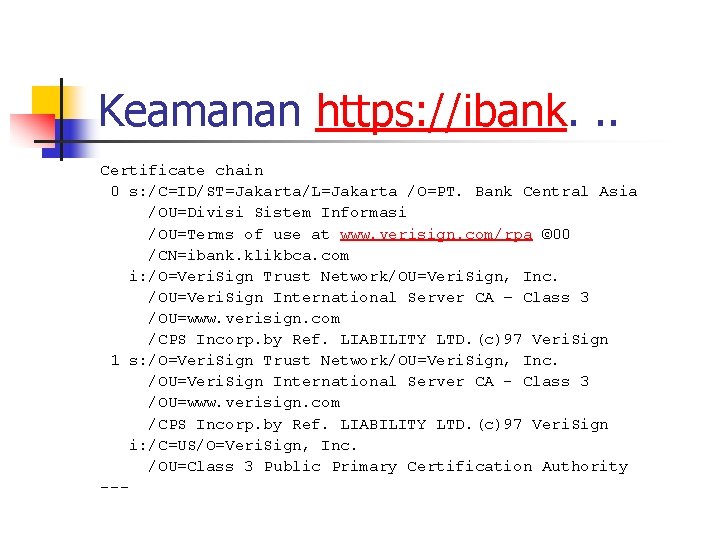
Keamanan https: //ibank. . . Certificate chain 0 s: /C=ID/ST=Jakarta/L=Jakarta /O=PT. Bank Central Asia /OU=Divisi Sistem Informasi /OU=Terms of use at www. verisign. com/rpa © 00 /CN=ibank. klikbca. com i: /O=Veri. Sign Trust Network/OU=Veri. Sign, Inc. /OU=Veri. Sign International Server CA – Class 3 /OU=www. verisign. com /CPS Incorp. by Ref. LIABILITY LTD. (c)97 Veri. Sign 1 s: /O=Veri. Sign Trust Network/OU=Veri. Sign, Inc. /OU=Veri. Sign International Server CA - Class 3 /OU=www. verisign. com /CPS Incorp. by Ref. LIABILITY LTD. (c)97 Veri. Sign i: /C=US/O=Veri. Sign, Inc. /OU=Class 3 Public Primary Certification Authority ---
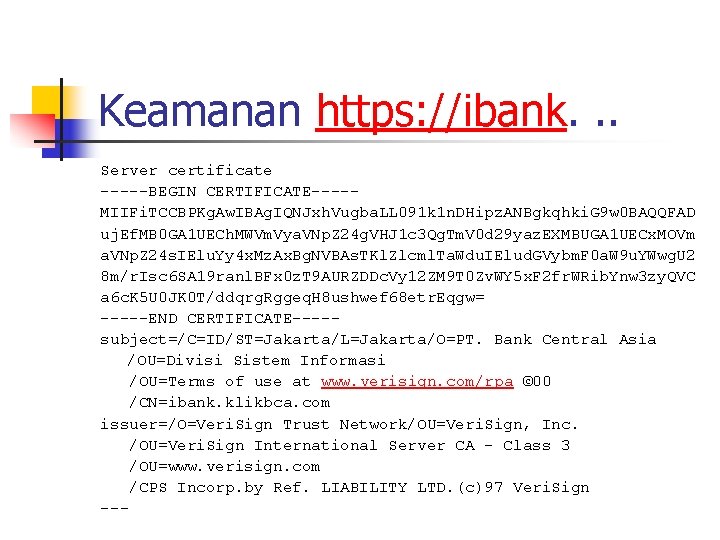
Keamanan https: //ibank. . . Server certificate -----BEGIN CERTIFICATE----MIIFi. TCCBPKg. Aw. IBAg. IQNJxh. Vugba. LL 091 k 1 n. DHipz. ANBgkqhki. G 9 w 0 BAQQFAD uj. Ef. MB 0 GA 1 UECh. MWVm. Vya. VNp. Z 24 g. VHJ 1 c 3 Qg. Tm. V 0 d 29 yaz. EXMBUGA 1 UECx. MOVm a. VNp. Z 24 s. IElu. Yy 4 x. Mz. Ax. Bg. NVBAs. TKl. Zlcml. Ta. Wdu. IElud. GVybm. F 0 a. W 9 u. YWwg. U 2 8 m/r. Isc 6 SA 19 ranl. BFx 0 z. T 9 AURZDDc. Vy 12 ZM 9 T 0 Zv. WY 5 x. F 2 fr. WRib. Ynw 3 zy. QVC a 6 c. K 5 U 0 JK 0 T/ddqrg. Rggeq. H 8 ushwef 68 etr. Eqgw= -----END CERTIFICATE----subject=/C=ID/ST=Jakarta/L=Jakarta/O=PT. Bank Central Asia /OU=Divisi Sistem Informasi /OU=Terms of use at www. verisign. com/rpa © 00 /CN=ibank. klikbca. com issuer=/O=Veri. Sign Trust Network/OU=Veri. Sign, Inc. /OU=Veri. Sign International Server CA - Class 3 /OU=www. verisign. com /CPS Incorp. by Ref. LIABILITY LTD. (c)97 Veri. Sign ---
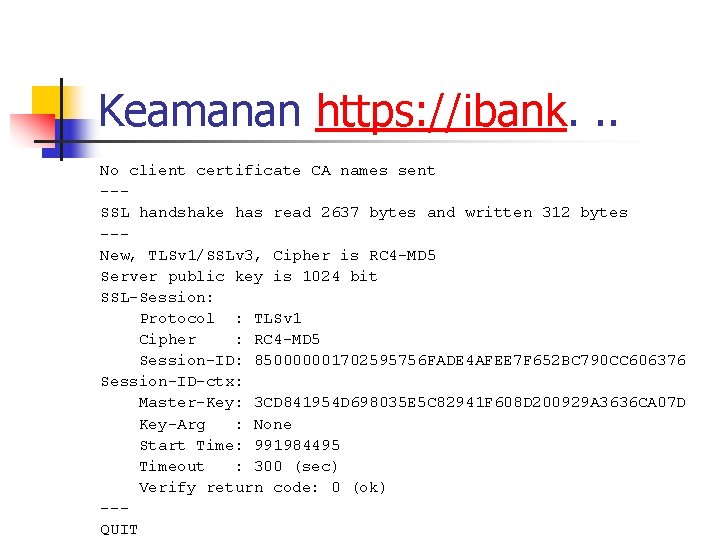
Keamanan https: //ibank. . . No client certificate CA names sent --SSL handshake has read 2637 bytes and written 312 bytes --New, TLSv 1/SSLv 3, Cipher is RC 4 -MD 5 Server public key is 1024 bit SSL-Session: Protocol : TLSv 1 Cipher : RC 4 -MD 5 Session-ID: 850000001702595756 FADE 4 AFEE 7 F 652 BC 790 CC 606376 Session-ID-ctx: Master-Key: 3 CD 841954 D 698035 E 5 C 82941 F 608 D 200929 A 3636 CA 07 D Key-Arg : None Start Time: 991984495 Timeout : 300 (sec) Verify return code: 0 (ok) --QUIT
![www. plasa. com [root@yc 1 dav onno]# nmap -v -s. S -O www. plasa. www. plasa. com [root@yc 1 dav onno]# nmap -v -s. S -O www. plasa.](http://slidetodoc.com/presentation_image/2dd306e7da652c77ae3d66855cf538da/image-18.jpg)
www. plasa. com [root@yc 1 dav onno]# nmap -v -s. S -O www. plasa. com Starting nmap V. 2. 53 by fyodor@insecure. org ( www. insecure. org/nmap/ ) Host plasa. com (202. 134. 0. 172) appears to be up. . . good. Initiating SYN half-open stealth scan against plasa. com (202. 134. 0. 172) Adding TCP port 32771 (state open). Adding TCP port 2049 (state open). Adding TCP port 22 (state open). Adding TCP port 21 (state open). Adding TCP port 111 (state open). Adding TCP port 80 (state open). Adding TCP port 32773 (state open). Adding TCP port 32772 (state open). The SYN scan took 77 seconds to scan 1523 ports.
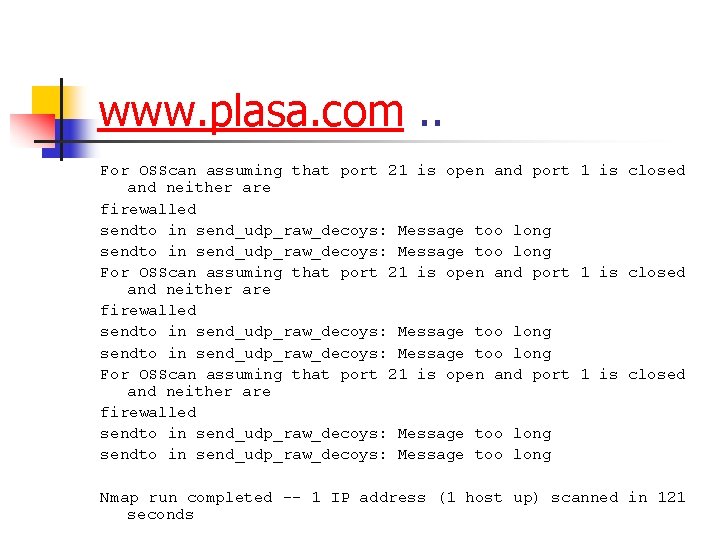
www. plasa. com. . For OSScan assuming that port 21 is open and port 1 is closed and neither are firewalled sendto in send_udp_raw_decoys: Message too long For OSScan assuming that port 21 is open and port 1 is closed and neither are firewalled sendto in send_udp_raw_decoys: Message too long Nmap run completed -- 1 IP address (1 host up) scanned in 121 seconds
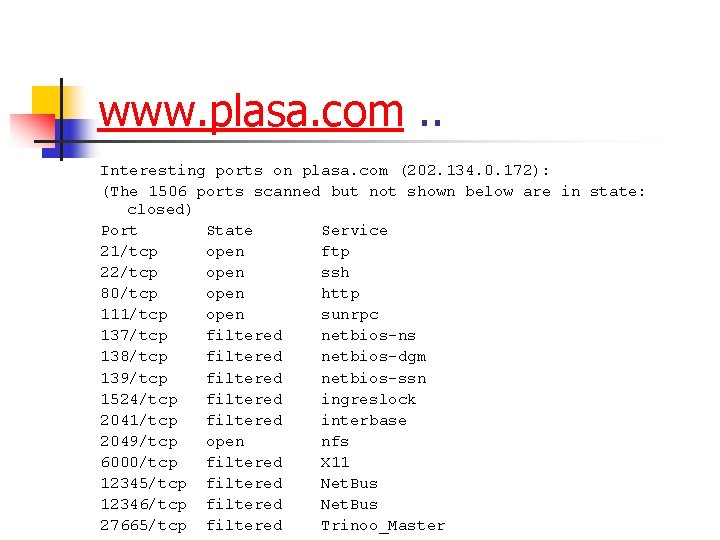
www. plasa. com. . Interesting ports on plasa. com (202. 134. 0. 172): (The 1506 ports scanned but not shown below are in state: closed) Port State Service 21/tcp open ftp 22/tcp open ssh 80/tcp open http 111/tcp open sunrpc 137/tcp filtered netbios-ns 138/tcp filtered netbios-dgm 139/tcp filtered netbios-ssn 1524/tcp filtered ingreslock 2041/tcp filtered interbase 2049/tcp open nfs 6000/tcp filtered X 11 12345/tcp filtered Net. Bus 12346/tcp filtered Net. Bus 27665/tcp filtered Trinoo_Master
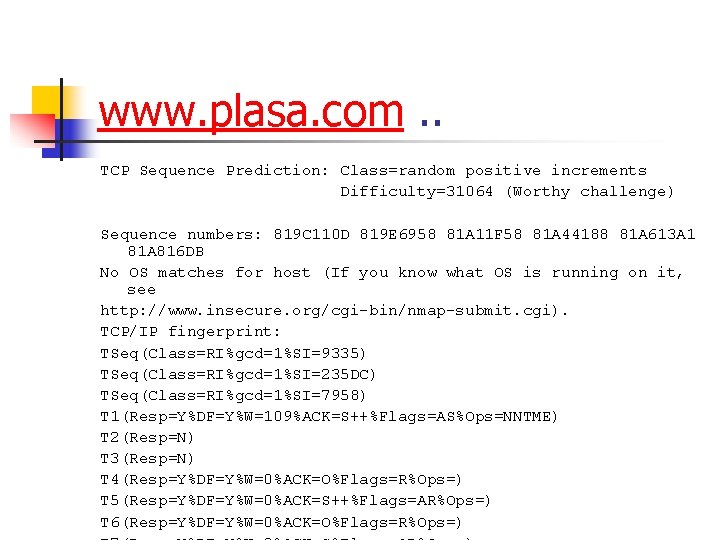
www. plasa. com. . TCP Sequence Prediction: Class=random positive increments Difficulty=31064 (Worthy challenge) Sequence numbers: 819 C 110 D 819 E 6958 81 A 11 F 58 81 A 44188 81 A 613 A 1 81 A 816 DB No OS matches for host (If you know what OS is running on it, see http: //www. insecure. org/cgi-bin/nmap-submit. cgi). TCP/IP fingerprint: TSeq(Class=RI%gcd=1%SI=9335) TSeq(Class=RI%gcd=1%SI=235 DC) TSeq(Class=RI%gcd=1%SI=7958) T 1(Resp=Y%DF=Y%W=109%ACK=S++%Flags=AS%Ops=NNTME) T 2(Resp=N) T 3(Resp=N) T 4(Resp=Y%DF=Y%W=0%ACK=O%Flags=R%Ops=) T 5(Resp=Y%DF=Y%W=0%ACK=S++%Flags=AR%Ops=) T 6(Resp=Y%DF=Y%W=0%ACK=O%Flags=R%Ops=)
- Slides: 21