Hash Function Requirements Network Security 1 Hash Function
- Slides: 21
Hash Function Requirements Network Security 1
Hash Function Requirements Objectives of the Topic • After completing this topic, a student will be able to – explain hash function requirements. 2
Hash Function Requirements Figures and material in this topic have been adapted from • “Network Security Essentials : Applications and Standards”, 2014, by William Stallings. 3
Hash Function Requirements • The purpose of a hash function is to produce a “fingerprint” of a file, message, or other block of data. • It accepts a variablelength block of data M as input and produces a fixed-size hash value h = H(M). 4
Hash Function Requirements • A “good” hash function has the property that the results of applying the function to a large set of inputs will produce outputs that are evenly distributed and apparently random. 5
Hash Function Requirements • A change to any bit or bits in M results, with high probability, in a change to the hash code. • The principal object of a hash function is data integrity. 6
Hash Function Requirements • For a hash value h = H(x), we say that x is the preimage of h. • In other words, x is a data block whose hash function, using the function H, is h. 7
Hash Function Requirements • Because H is a manyto-one mapping, for any given hash value h, there will in general be multiple preimages. 8
Hash Function Requirements • A collision occurs if we have x ≠ y and H(x) = H(y). • Because we are using hash functions for data integrity, collisions are clearly undesirable. 9
Hash Function Requirements • To be useful for message authentication, a hash function H must have the following properties: • 1. H can be applied to a block of data of any size. • 2. H produces a fixedlength output. 10
Hash Function Requirements • 3. H(x) is relatively easy to compute for any given x, making both hardware and software implementations practical. 11
Hash Function Requirements • 4. For any given code h, it is computationally infeasible to find x such that H(x) = h. • A hash function with this property is referred to as oneway or preimage resistant. 12
Hash Function Requirements • 5. For any given block x, it is computationally infeasible to find y ≠ x with H(y) = H(x). • A hash function with this property is referred to as second preimage resistant. • This is also referred to as weak collision resistant. 13
Hash Function Requirements • 6. It is computationally infeasible to find any pair (x, y) such that H(x) = H(y). • Such a hash function is referred to as collision resistant. • This is sometimes referred to as strong collision resistant. 14
Hash Function Requirements • First three properties are requirements for the practical application of a hash function to message authentication. • The 4 th property is important if the authentication technique involves the use of a secret value. 15
Hash Function Requirements • The fourth property, preimage resistant, is the “one-way” property: It is easy to generate a code given a message, but virtually impossible to generate a message given a code. 16
Hash Function Requirements • The 5 th property prevents forgery when an encrypted hash code is used. 17
Hash Function Requirements • A hash function that satisfies the first five properties in the preceding list is referred to as a weak hash function. • If the sixth property is also satisfied, then it is referred to as a strong hash function. 18
Hash Function Requirements Security of Hash Functions: • Two approaches to attacking a secure hash function are: • Cryptanalysis, and • brute-force attack 19
Hash Function Requirements • Cryptanalysis of a hash function involves exploiting logical weaknesses in the algorithm. • The strength of a hash function against brute -force attacks depends on length of hash code produced by algorithm. 20
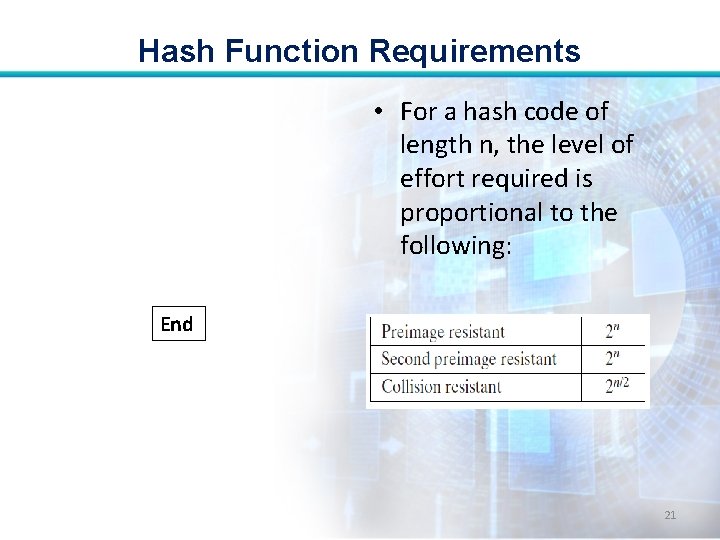
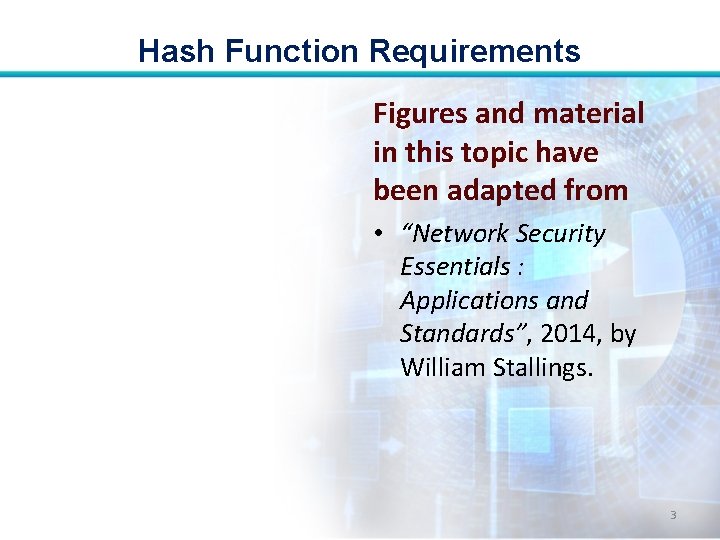
Hash Function Requirements • For a hash code of length n, the level of effort required is proportional to the following: End 21