Hannah H Education Academia Engagement hannah hncsc gov

- Slides: 27
Hannah H Education & Academia Engagement hannah. h@ncsc. gov. uk
A different kettle of phish How rethinking your approach to phishing can make your college a safer place to work and study. Hannah H – National Cyber Security Centre Anthony Bravo – Basingstoke College of Technology This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
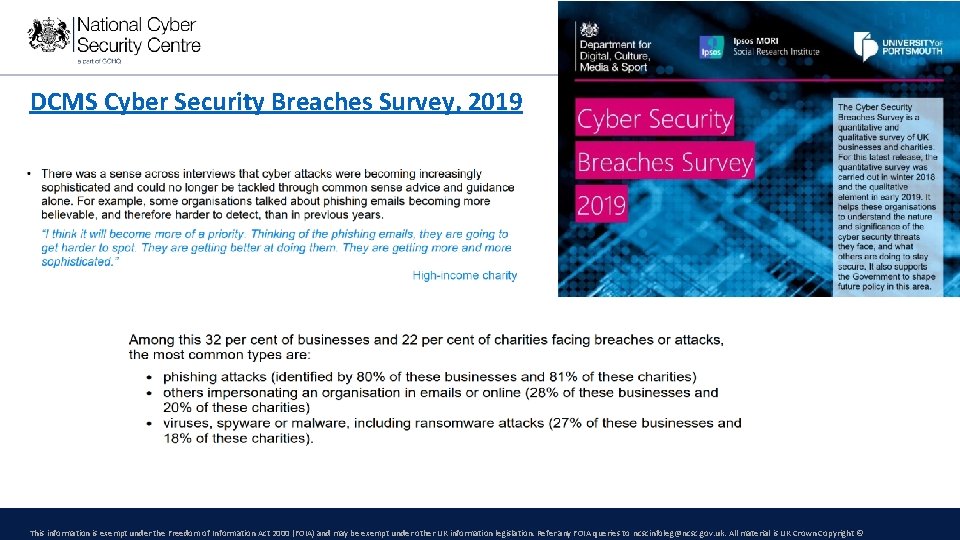
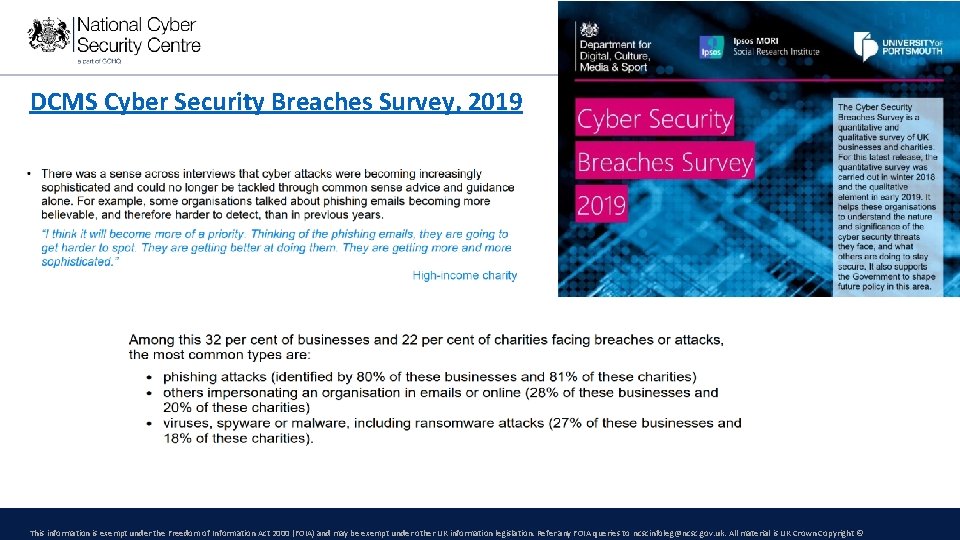
DCMS Cyber Security Breaches Survey, 2019 This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
Phishing facts and figures: JISC survey • Only 45% have compulsory cyber security training for all staff, and only 2% for students • IT managers are most worried about the following threats: 1. 2. 3. 4. Phishing / social engineering Procedures not followed by staff/students Ransomware / malware DDo. S attacks This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©

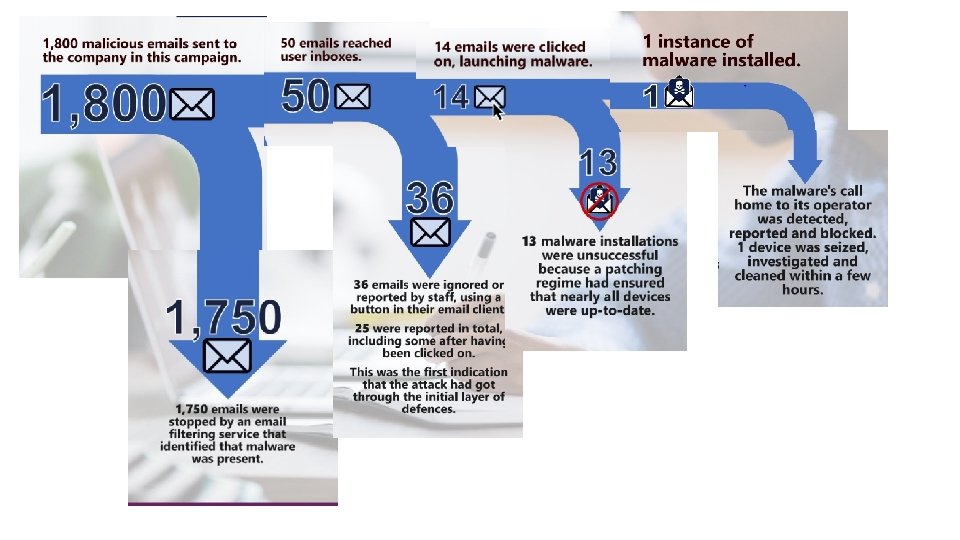
A college’s general experience of phishing – part 1 This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
Action Fraud / NFIB Work for general public and businesses Part of police Enables people to report suspicious emails they haven’t clicked on for them to be investigated Keep tabs on trends and changing approaches for criminals - Generally seeing fewer low sophistication approaches - But more effort going into websites than the initial email This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
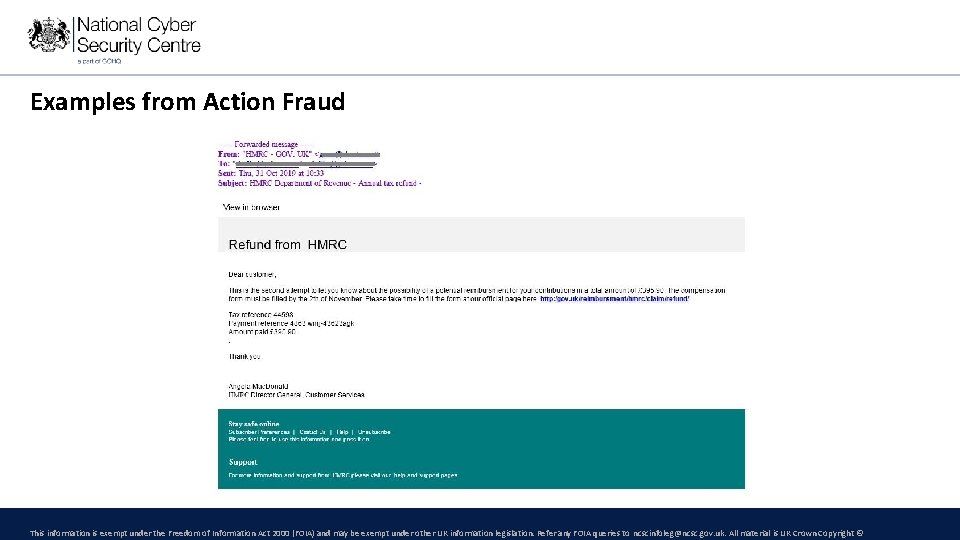
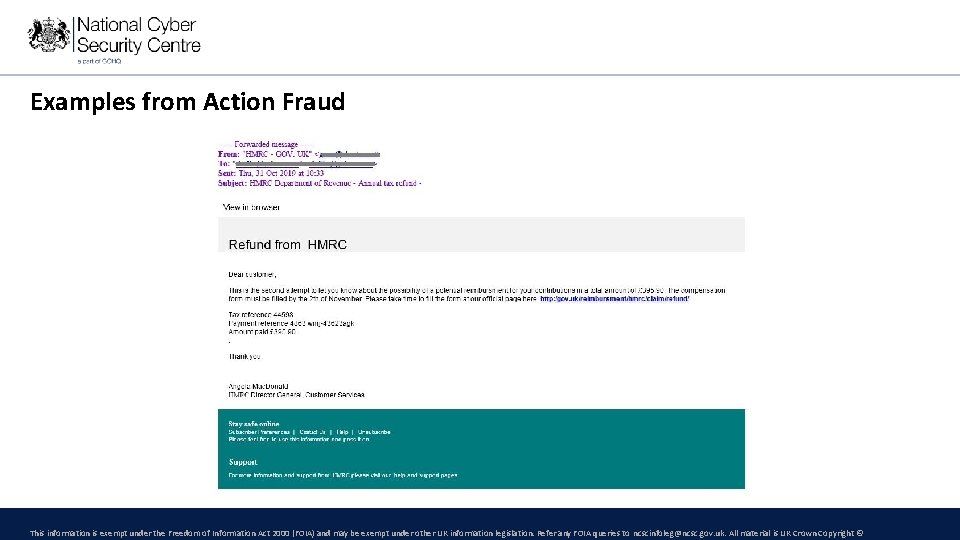
Examples from Action Fraud This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
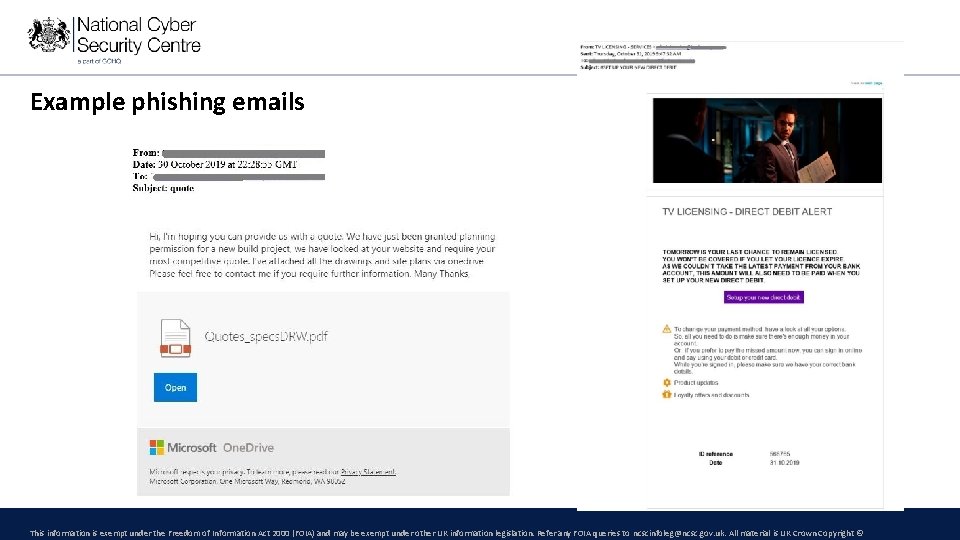
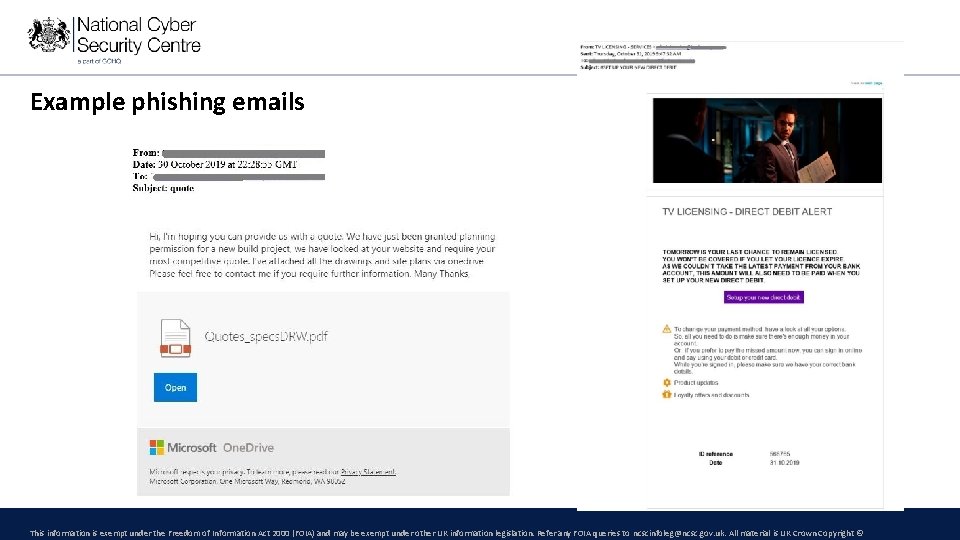
Example phishing emails This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
Phishing: the story so far – bringing it together • Why is it called ‘phishing’? • Who phishes? • Who is phished? • Why do people do it? • Why do people fall for it? – coming later! This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
A phishing story part 2 – The exercise This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
People, Phishing and Training This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
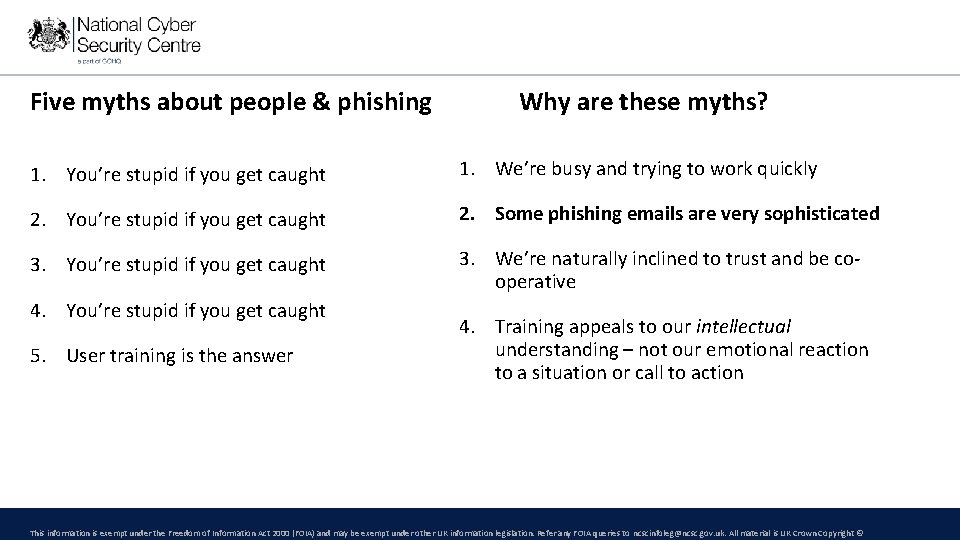
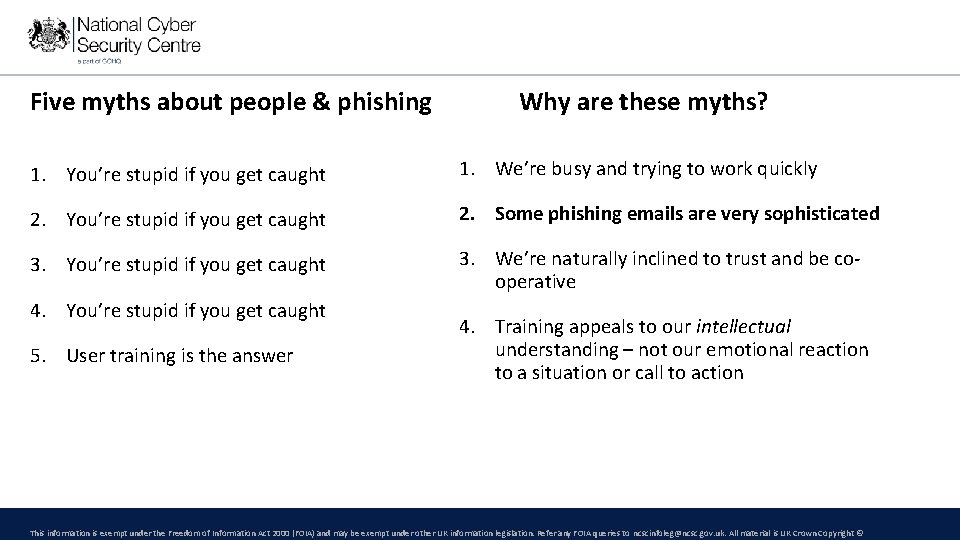
Five myths about people & phishing Why are these myths? 1. You’re stupid if you get caught 1. We’re busy and trying to work quickly 2. You’re stupid if you get caught 2. Some phishing emails are very sophisticated 3. You’re stupid if you get caught 3. We’re naturally inclined to trust and be cooperative 4. You’re stupid if you get caught 5. User training is the answer 4. Training appeals to our intellectual understanding – not our emotional reaction to a situation or call to action This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
(Phish) food for thought This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
A final story from Anthony… and some more sophisticated phish… • Spear-phishing • Whaling • ‘CEO fraud’ • A short video This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
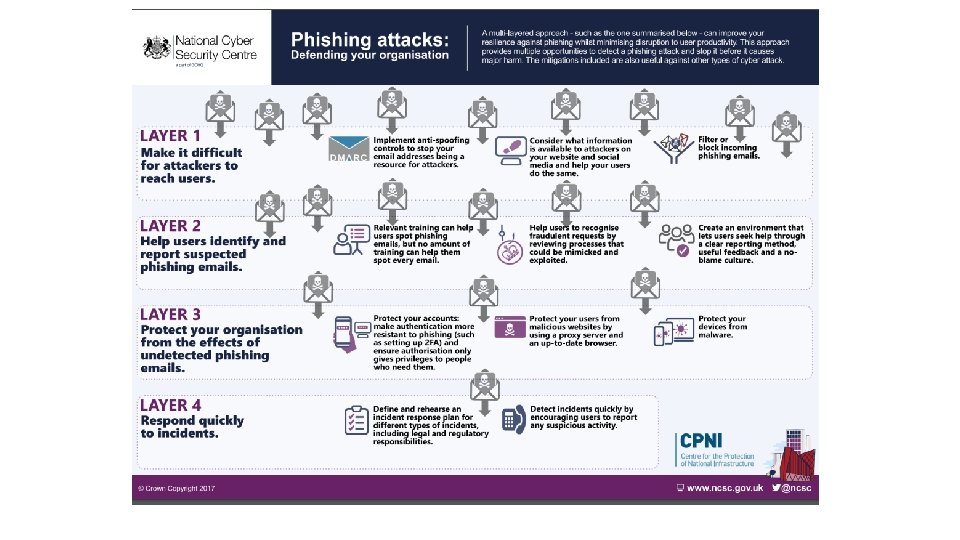
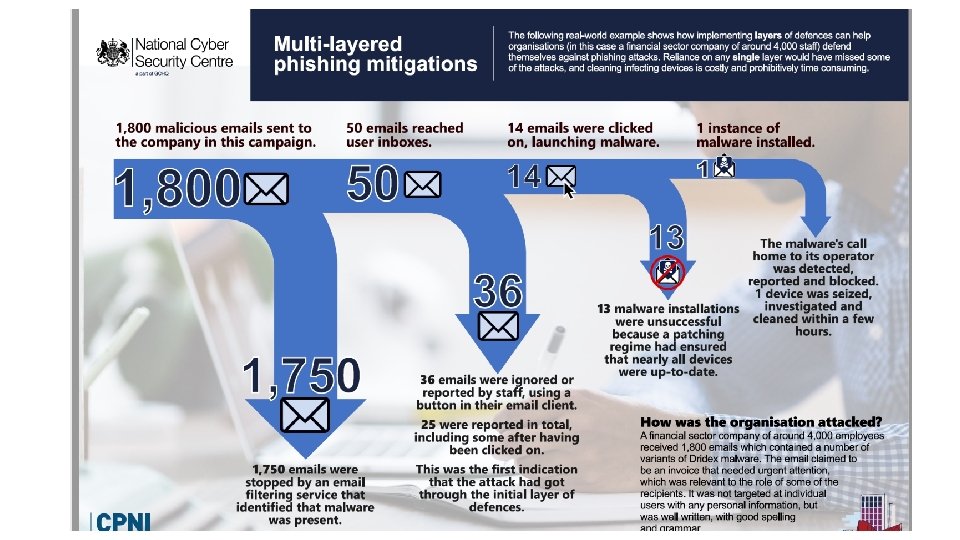
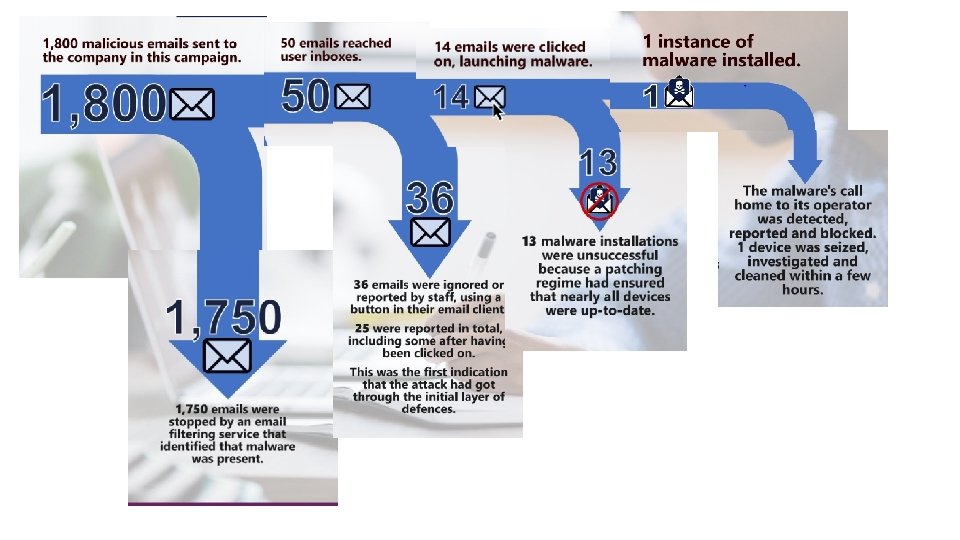
Layering your defences A holistic approach to phishing defence… requiring a whole-college response This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
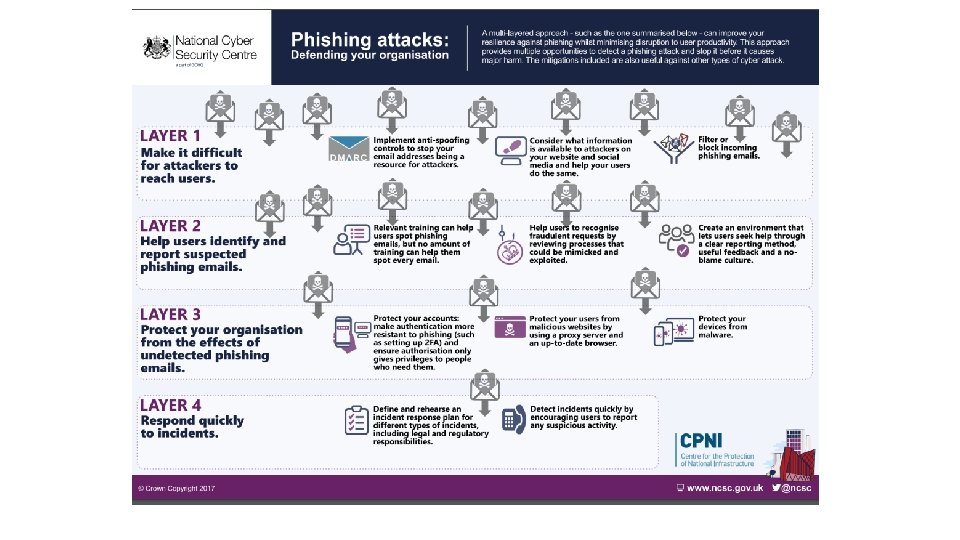
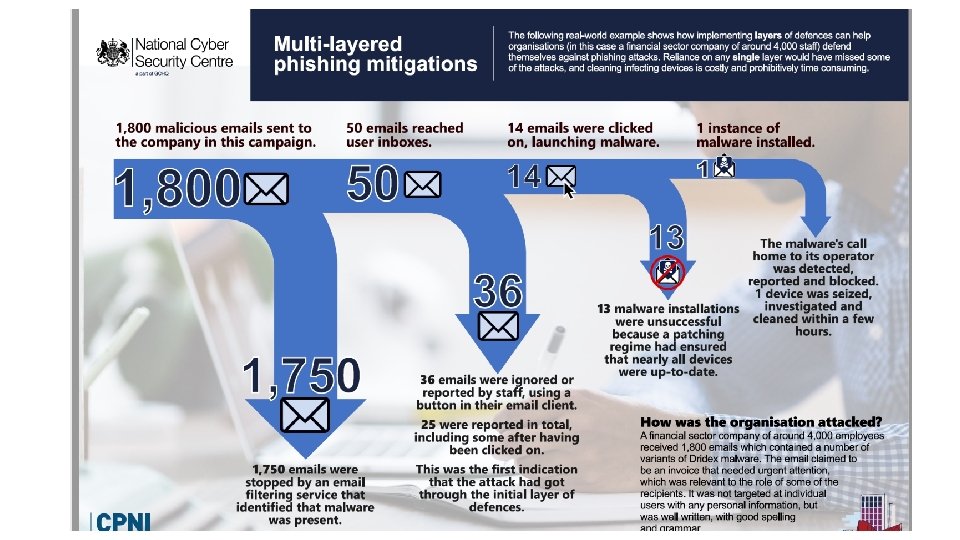
What are these ‘defences’ to be ‘layered’? 1. Stopping as many phishing emails as possible from getting to users in the first place 2. Helping users identify and report suspected phishing emails 3. Protecting your organisation from the effects of undetected phishing emails 4. Responding quickly to incidents See our detailed guidance This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
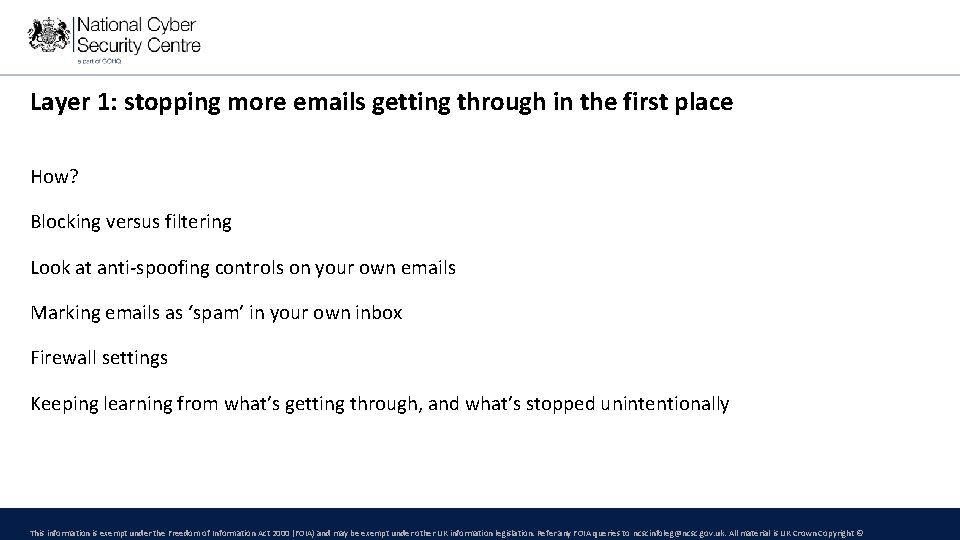
Layer 1: stopping more emails getting through in the first place How? Blocking versus filtering Look at anti-spoofing controls on your own emails Marking emails as ‘spam’ in your own inbox Firewall settings Keeping learning from what’s getting through, and what’s stopped unintentionally This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
Layer 2: Helping users identify and report potential phish • The layer that’s often over emphasised! • Who do you report suspicious emails to at work? • Do you hear back when you do so? • What can you do to encourage people to do this? (i. e. the moral imperative) • How can you include students as well as staff? • How can you create the right culture so it’s OK to report when ‘click happens’? This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
Layer 3: Protecting your organisation from the effects of any phishing emails • This is about technical controls and mitigations • But is still a cross-college issue • Cyber hygiene measures: E. g. 2 FA, ‘least access’ privileges, patching, limiting admin activities, strong passwords, culture of questioning processes that don’t work for people, segregating networks, back ups This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
Layer 4: Responding quickly to incidents • How is your IT department resourced to do this? • Do they have external support contracts, or with JISC, for example? • Do they have the opportunity to exercise? • Do senior leaders understand the importance of quick response times, even if it causes inconvenience to other users? This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
NCSC Resources –www. ncsc. gov. uk For everyone: For IT staff: • Phishing attacks: defending your organisation • Cyber Essentials / Cyber Essentials Plus • Small Business / Charity Guide • Ten Steps to Cyber Security • Top Tips for Staff e-learning package • • Cyber Security Toolkit for Boards • Weekly Threat Reports • Response and Recovery Guide • Ci. SP Our blogs on phishing campaigns and mitigations • Exercise in a Box Coming soon: Suspicious Email project (Action Fraud) Get in touch! Hannah. h@ncsc. gov. uk CPNI – Don’t Take The Bait – www. cpni. gov. uk/dont-takebait This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
Key takeaways • Phishing isn’t going away • It’ll be harder and harder for most of us to spot • Talk to your leadership team • Talk to your IT team • Think about staff training and student training • Work across the college: create a positive cyber security culture, learn from each other • Always report your suspicions / mistakes! To IT, to Action Fraud, to JISC? This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©
What’s been your key takeaway? How can you make a difference? What else can NCSC do to help colleges? How else should we be communicating with colleges? hannah. h@ncsc. gov. uk This information is exempt under the Freedom of Information Act 2000 (FOIA) and may be exempt under other UK information legislation. Refer any FOIA queries to ncscinfoleg@ncsc. gov. uk. All material is UK Crown Copyright ©