Guide to Computer Forensics and Investigations Fourth Edition
- Slides: 20
Guide to Computer Forensics and Investigations Fourth Edition Chapter 6 - Working with Windows and DOS Systems Chapter 8 - Macintosh and Linux Boot Processes and File Systems
Objectives • • Describe Microsoft startup tasks Describe MS-DOS startup tasks Explain Macintosh boot process Explain UNIX and Linux boot processes Guide to Computer Forensics and Investigations 2
Understanding Microsoft Startup Tasks • Learn what files are accessed when Windows starts • This information helps you determine when a suspect’s computer was last accessed – Important with computers that might have been used after an incident was reported Guide to Computer Forensics and Investigations 3
Startup in Windows NT and Later • All NTFS computers perform the following steps when the computer is turned on: – – – Power-on self test (POST) Initial startup Boot loader Hardware detection and configuration Kernel loading User logon Guide to Computer Forensics and Investigations 4
Startup in Windows NT and Later (continued) • Startup Files for Windows XP: – – – – – NT Loader (NTLDR) Boot. ini Boot. Sect. dos NTDetect. com NTBootdd. sys Ntoskrnl. exe Hal. dll Pagefile. sys Device drivers Guide to Computer Forensics and Investigations 5
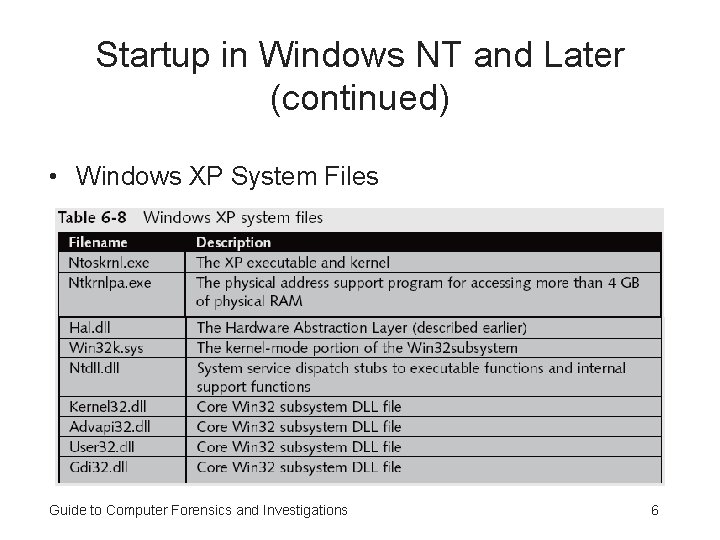
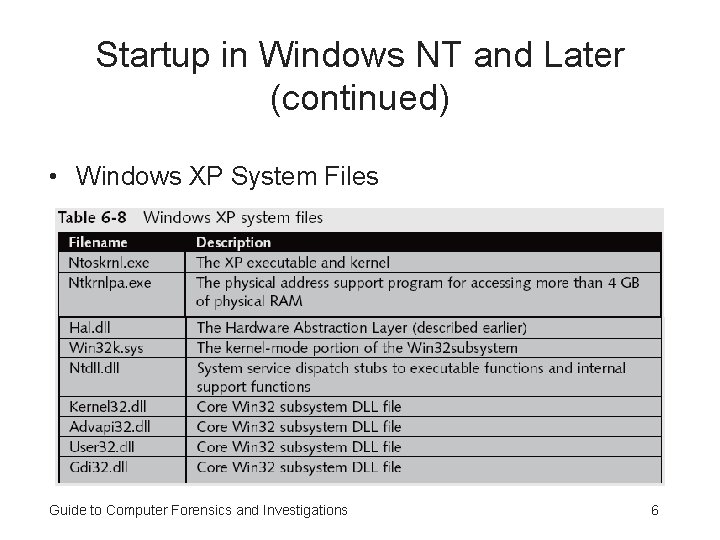
Startup in Windows NT and Later (continued) • Windows XP System Files Guide to Computer Forensics and Investigations 6
Startup in Windows NT and Later (continued) • Contamination Concerns with Windows XP – When you start a Windows XP NTFS workstation, several files are accessed immediately • The last access date and time stamp for the files change to the current date and time – Destroys any potential evidence • That shows when a Windows XP workstation was last used Guide to Computer Forensics and Investigations 7
Startup in Windows 9 x/Me • System files in Windows 9 x/Me containing valuable information can be altered easily during startup • Windows 9 x and Windows Me have similar boot processes – With Windows Me you can’t boot to a true MS-DOS mode • Windows 9 x OSs have two modes: – DOS protected-mode interface (DPMI) – Protected-mode GUI Guide to Computer Forensics and Investigations 8
Startup in Windows 9 x/Me (continued) • The system files used by Windows 9 x have their origin in MS-DOS 6. 22 – Io. sys communicates between a computer’s BIOS, the hardware, and the OS kernel • If F 8 is pressed during startup, Io. sys loads the Windows Startup menu – Msdos. sys is a hidden text file containing startup options for Windows 9 x – Command. com provides a command prompt when booting to MS-DOS mode (DPMI) Guide to Computer Forensics and Investigations 9
Understanding MS-DOS Startup Tasks • Two files are used to configure MS-DOS at startup: – Config. sys • A text file containing commands that typically run only at system startup to enhance the computer’s DOS configuration – Autoexec. bat • A batch file containing customized settings for MSDOS that runs automatically • Io. sys is the first file loaded after the ROM bootstrap loader finds the disk drive Guide to Computer Forensics and Investigations 10
Understanding MS-DOS Startup Tasks (continued) • Msdos. sys is the second program to load into RAM immediately after Io. sys – It looks for the Config. sys file to configure device drivers and other settings • Msdos. sys then loads Command. com • As the loading of Command. com nears completion, Msdos. sys looks for and loads Autoexec. bat Guide to Computer Forensics and Investigations 11
Exploring Macintosh Boot Tasks • Use Open Firmware – Processor- and system-independent firmware – Controls microprocessor after hardware initialization • The boot process for OS 9 is as follows: – – – 1. Power on the computer 2. Hardware self-test and Open Firmware run 3. Macintosh OS starts 4. The startup disk is located 5. System files are opened Guide to Computer Forensics and Investigations 12
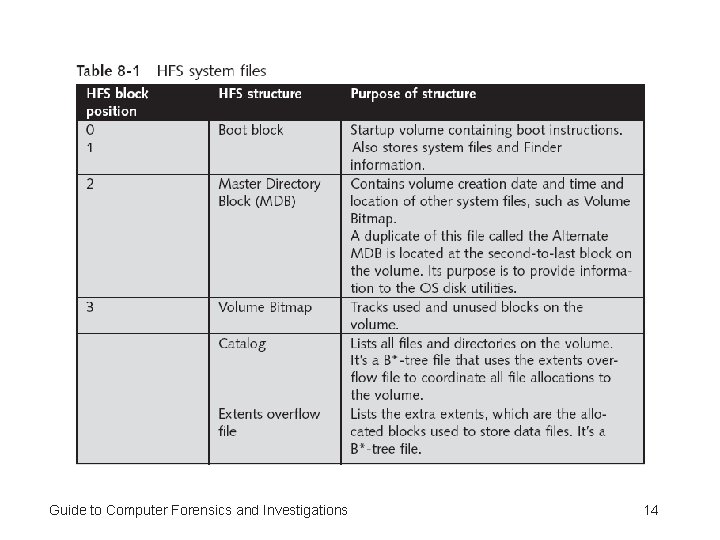
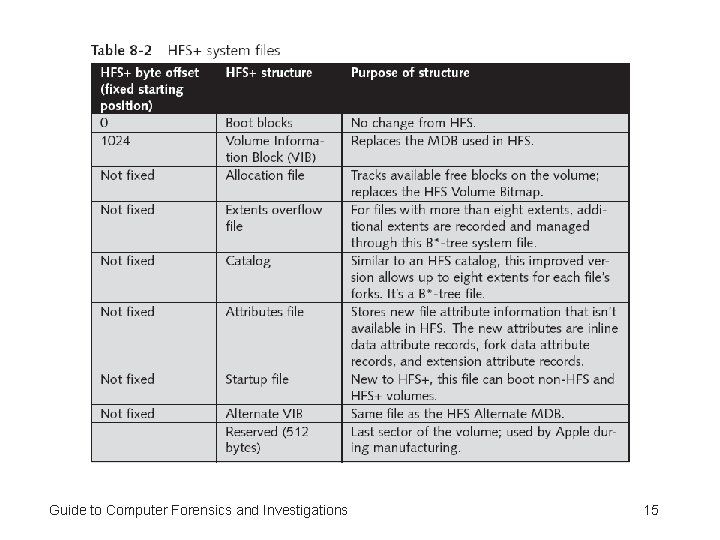
Exploring Macintosh Boot Tasks (continued) • The boot process for OS 9 (continued): – 6. System extensions are loaded – 7. OS 9 Finder starts • Tables 8 -1 and 8 -2 are an overview of how HFS and HFS+ system files handle data Guide to Computer Forensics and Investigations 13
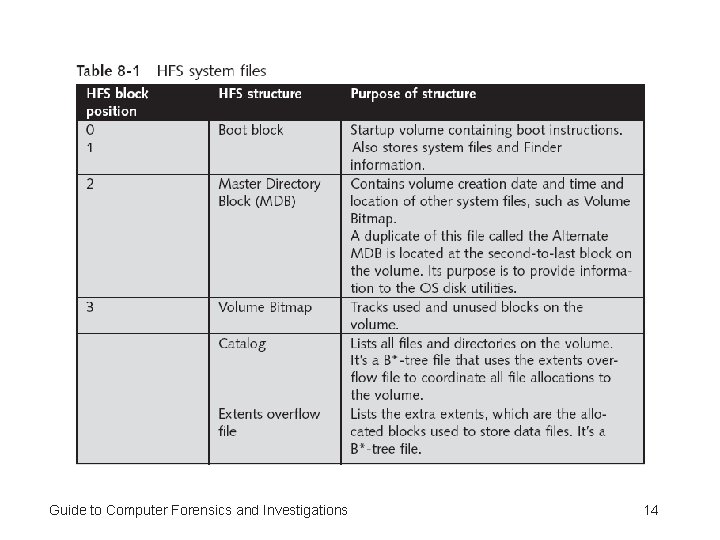
Guide to Computer Forensics and Investigations 14
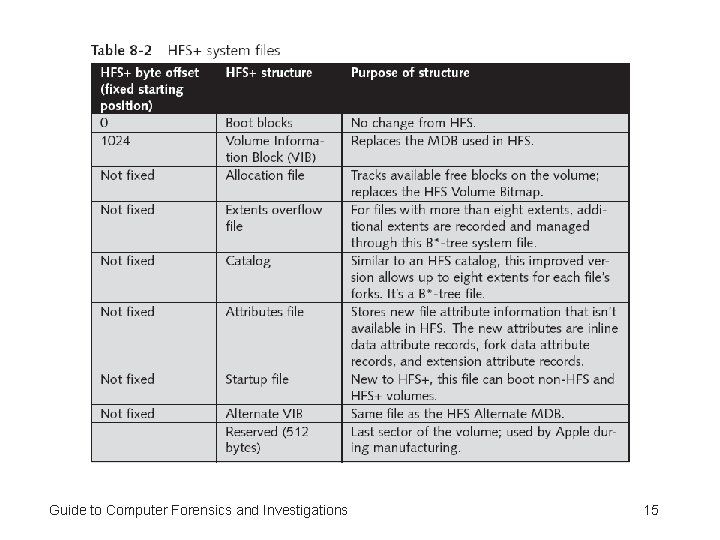
Guide to Computer Forensics and Investigations 15
Exploring Macintosh Boot Tasks (continued) • Older Macintosh OSs use – First two logical blocks as boot blocks – Master Directory Block (MDB) or Volume Information Block (VIB) • Stores all information about a volume – Volume Control Block (VCB) • Stores information from the MDB when OS mounts • Extents overflow file – Stores any file information not in the MDB or a VCB Guide to Computer Forensics and Investigations 16
Exploring Macintosh Boot Tasks (continued) • Catalog – Listing of all files and directories on the volume – Maintains relationships between files and directories • Volume Bitmap – Tracks used and unused blocks on a volume • Mac OS 9 uses the B*-tree file system for File Manager – Actual file data is stored on the leaf nodes – B*-tree also uses header, index, and map nodes Guide to Computer Forensics and Investigations 17
Understanding UNIX and Linux Boot Processes • Instruction code in firmware is loaded into RAM • Instruction code then: – Checks the hardware – Load the boot program • Boot program – Loads kernel – Transfers control to kernel • Kernel’s first task is to identify all devices Guide to Computer Forensics and Investigations 18
Understanding UNIX and Linux Boot Processes (continued) • Kernel – – – Boots system on single-user mode Runs startup scripts Changes to multiuser mode Identifies root directory, swap, and dump files Sets hostname and time zone Runs consistency checks on the file system and mounts partitions – Starts services and sets up the NIC – Establishes user and system accounting and quotas Guide to Computer Forensics and Investigations 19
Summary • System files in Windows 9 x/Me containing valuable information can be altered easily during startup • Two files are used to configure MS-DOS at startup: • Config. sys and Autoexec. bat • Linux kernel is regulated under the GNU General Public License (GPL) agreement Guide to Computer Forensics and Investigations 20