Guard ION Practical Mitigation of DMAbased Rowhammer Attacks
Guard. ION: Practical Mitigation of DMA-based Rowhammer Attacks on ARM Victor van der Veen, Martina Lindorfer†, Yanick Fratantonio‡, Harikrishnan Padmanabha Pillai*, Giovanni Vigna†, Christopher Kruegel†, Herbert Bos, and Kaveh Razavi VU Amsterdam †UC Santa Barbara ‡EURECOM *Amrita University India
Takeaway 1. Overview of Rowhammer defenses 2. RAMPAGE Rowhammer attacks against the latest Android OS 3. Guard. ION Lightweight mitigation
DRAM Disturbance Errors Memory cells (capacitors) have a natural discharge rate (refresh every 64 ms) Activating neighboring cells increases the discharge rate • Victim cell is charged to represent 1 • Neighboring cells are accessed frequently • Victim cell leaks charge below a certain threshold • When read, victim cell is interpreted 0 Rowhammer
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
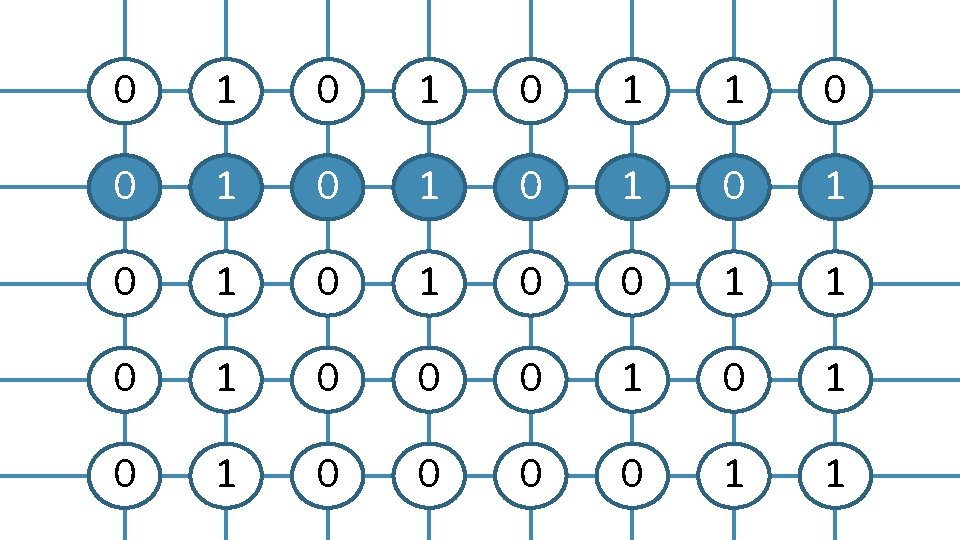
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
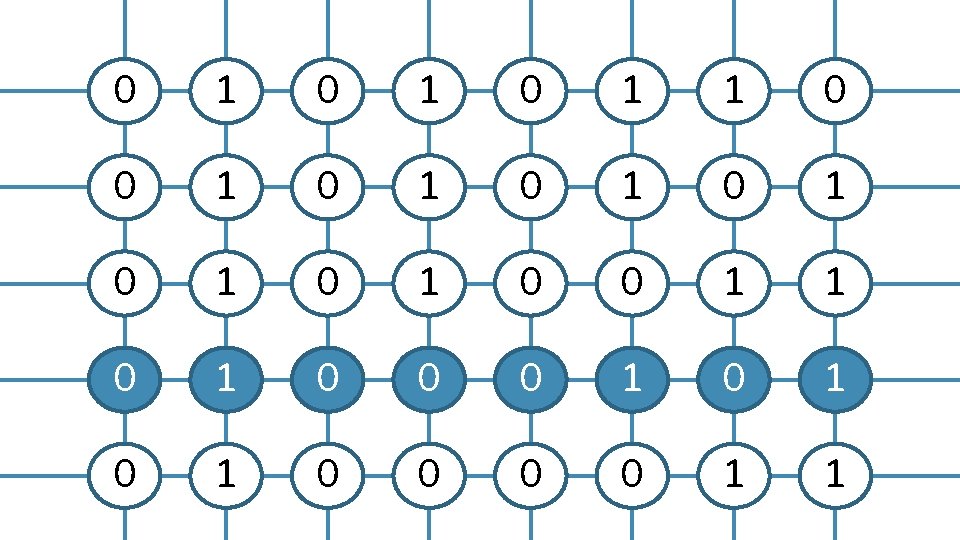
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
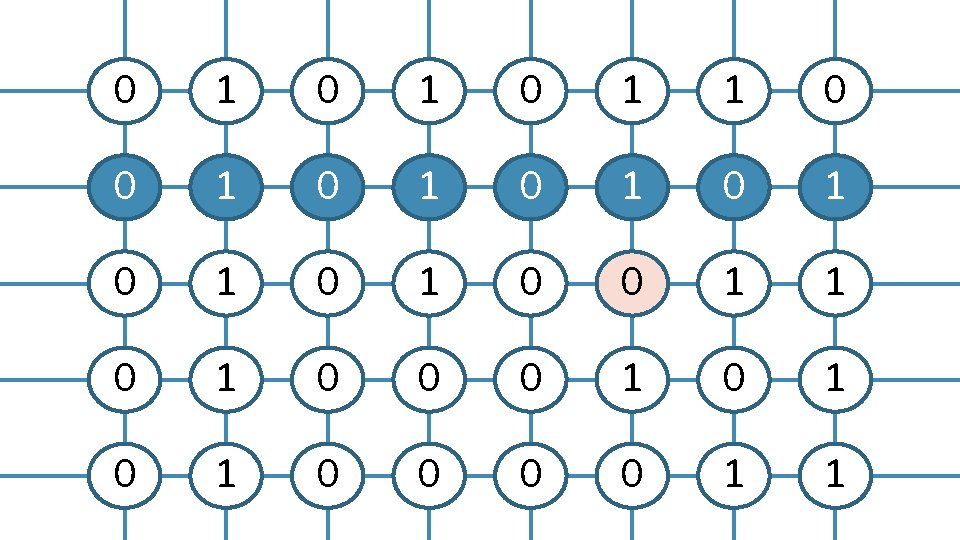
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
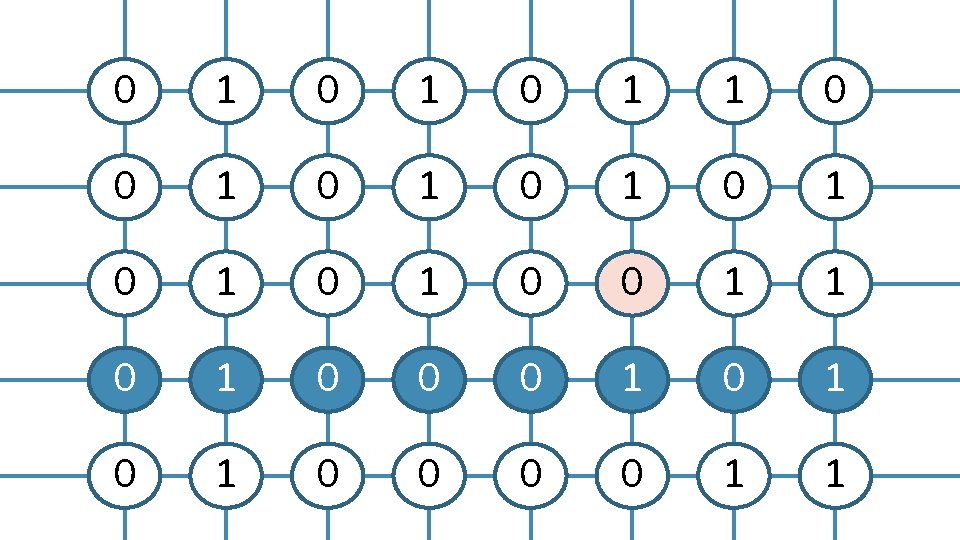
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
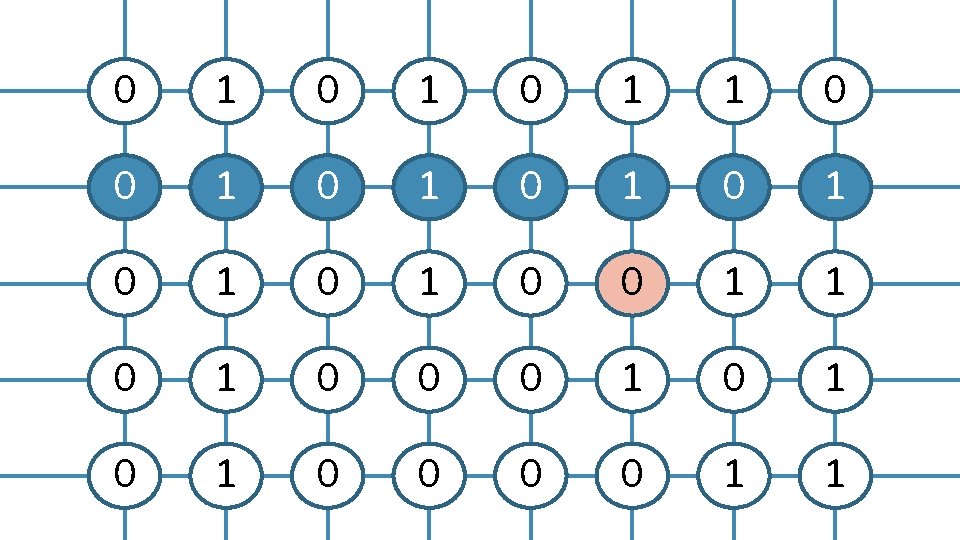
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1

0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
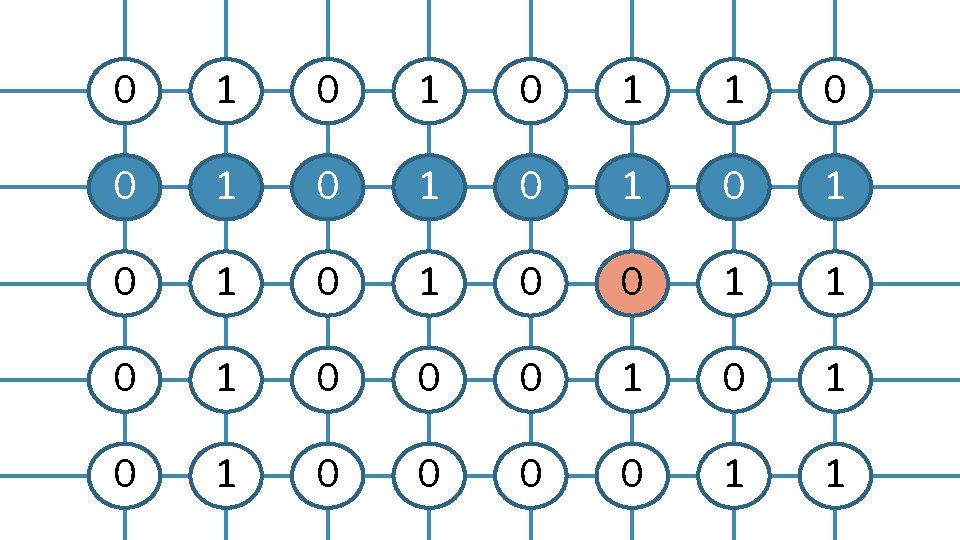
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
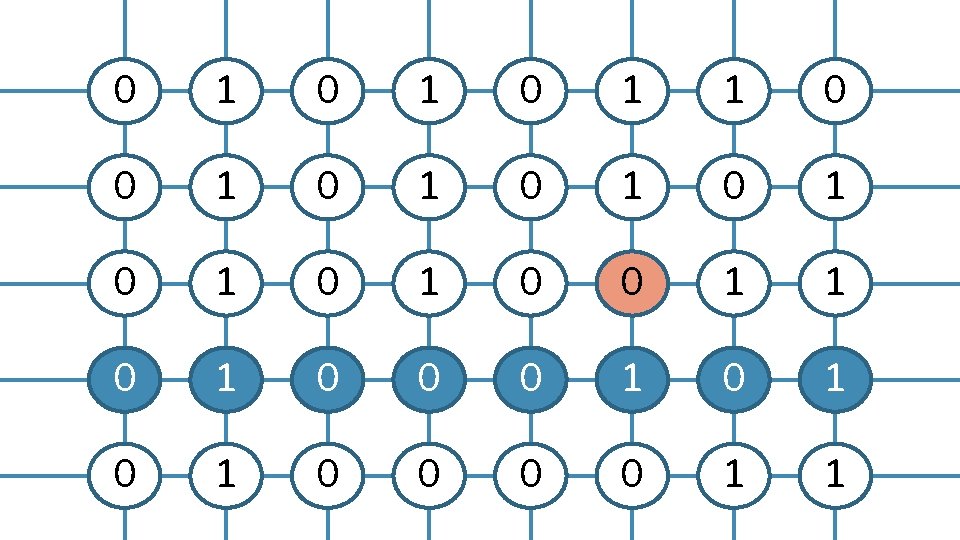
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
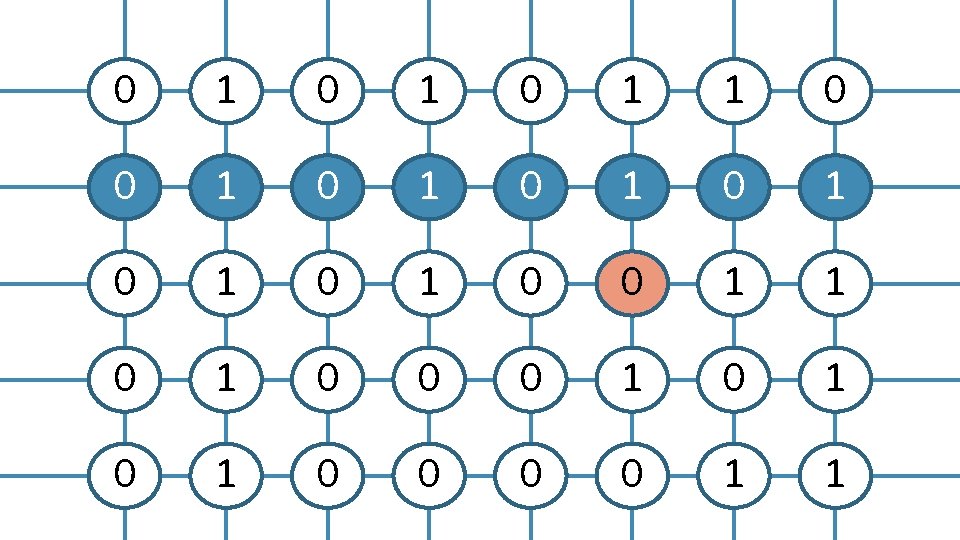
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
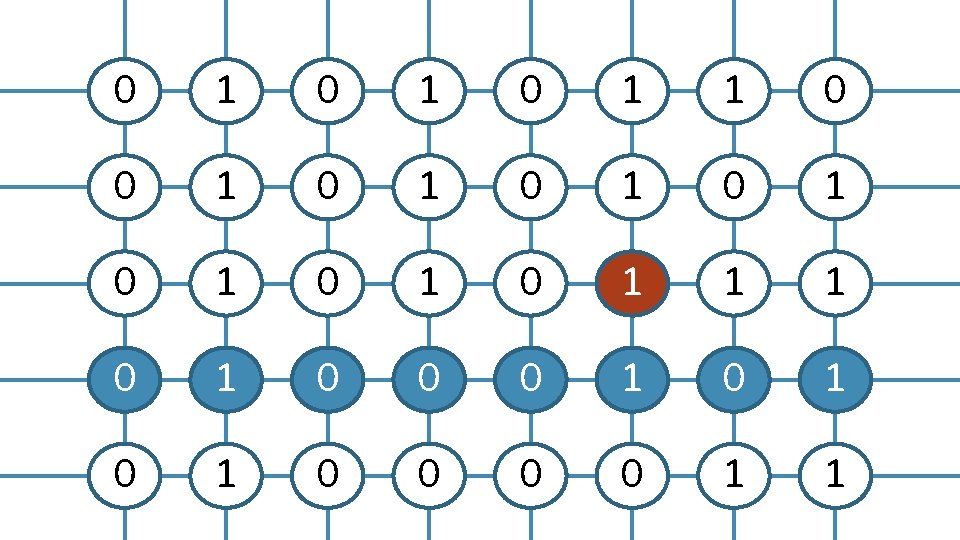
0 1 0 1 1 0 0 1 0 1 1 1 0 0 0 1 0 1 0 0 1 1
Rowhammer Flip a bit in a victim row by reading from two aggressor rows • Not every bit may flip • Bit flips are reproducible Challenges 1. Bypass the CPU cache 2. Get large contiguous chunks of memory
Privilege Escalation with Rowhammer Page tables • Map virtual addresses to physical addresses (virt x is at phys y) • Stored in DRAM Flipping a bit in a page table • Modifies the mapping: virt x is at phys z • Store a page table at phys z… • … read/write access to a page table: arbitrary read/write
Privilege Escalation with Drammer The Android ION memory allocator • Generalized memory manager to support DMA buffers • Multiple ION heaps, some with internal pooling Camera | Audio | Contiguous (kmalloc) | ADSP | IOMMU | qsecom | CMA | System | MM | … • User-space can request buffers with modified cache management Drammer (2016) exploits the contiguous heap to • Bypass the CPU cache • Get large contiguous allocations

Overview of Defenses

Rowhammer Defenses on ARM Software-based Rowhammer defenses ANVIL | B-CATT | Android ION patches Secure Do they stop Rowhammer attacks? Practical Can we deploy them in practice, on Android/ARM?

Rowhammer Defenses on ARM ANVIL 1. Performance counters measure cache misses / DRAM accesses Threshold exceeded? 2. Heavy-weight monitoring check for aggressor accesses Threshold exceeded? 3. Access the victim row to trigger a refresh ANVIL is secure, but not practical on ARM • No performance counters to support 2.
Rowhammer Defenses on ARM B-CATT • Scan memory during boot for vulnerable pages • Instruct the OS to mark those pages as unavailable B-CATT is not secure • A single scan does not yield all possible bit flips
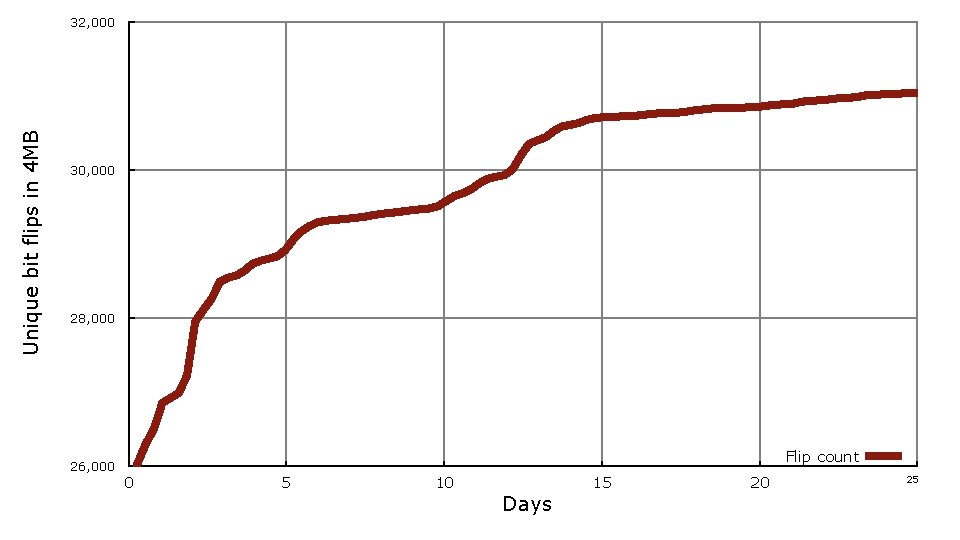
Unique bit flips in 4 MB 32, 000 30, 000 28, 000 26, 000 Flip count 0 5 10 15 Days 20 25
Rowhammer Defenses on ARM B-CATT • Scan memory during boot for vulnerable pages • Instruct the OS to mark those pages as unavailable B-CATT is not secure • A single scan does not yield all possible bit flips B-CATT is not practical • You may have to blacklist all pages • A full memory scan take over a day to complete
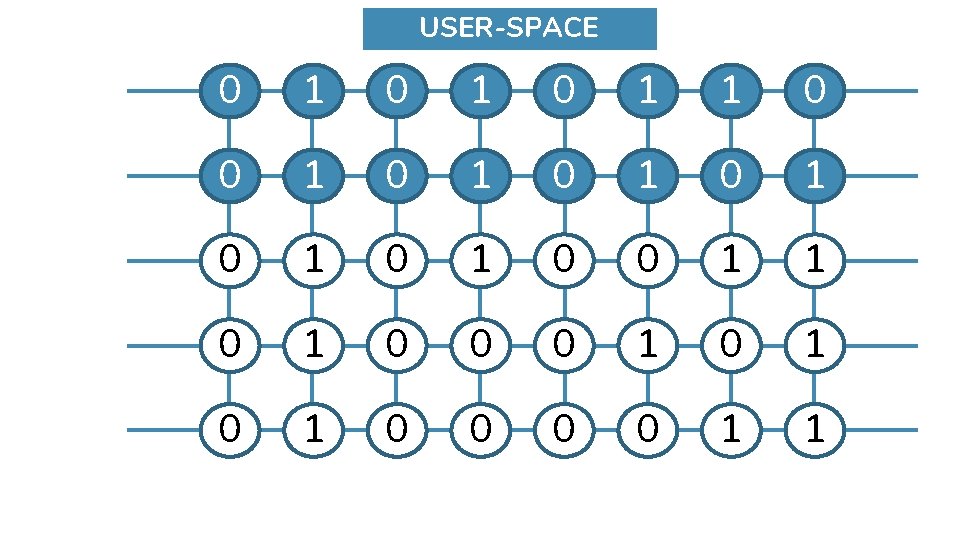
Rowhammer Defenses on ARM CATT • Partition memory in n chunks, one for each security domain • 1 for user-space allocations, 1 for kernel memory
0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
USER-SPACE 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1
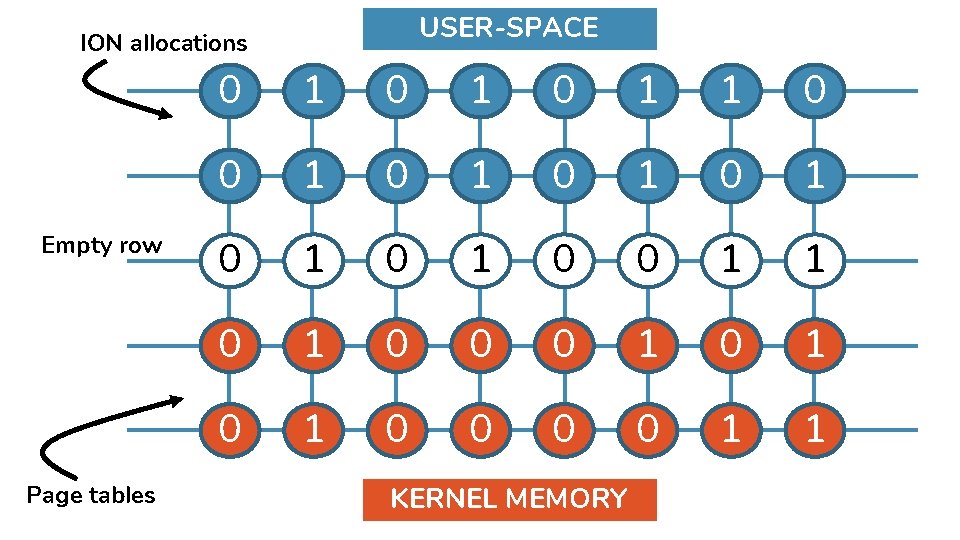
USER-SPACE ION allocations Empty row Page tables 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 1 1 KERNEL MEMORY
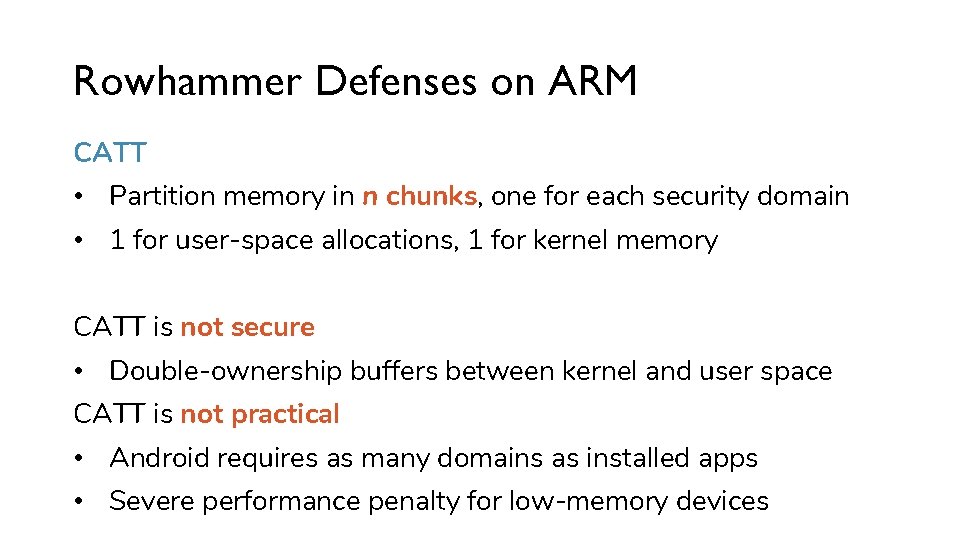
Rowhammer Defenses on ARM CATT • Partition memory in n chunks, one for each security domain • 1 for user-space allocations, 1 for kernel memory CATT is not secure • Double-ownership buffers between kernel and user space CATT is not practical • Android requires as many domains as installed apps • Severe performance penalty for low-memory devices

Rowhammer Defenses on ARM Android ION patches (1/2) • Disable the contiguous (kmalloc) heap • Reduce ION internal pool sizes to at most 64 KB (equal the rowsize) No longer guaranteed to get large contiguous chunks • Complicates scanning for bit flips • Complicates memory massaging Practical, but not secure

Rowhammer Defenses on ARM Android ION patches (2/2) • Better separation of highmem / lowmem Get ION allocations (highmem) away from page tables (lowmem) Practical, but not secure

RAMPAGE
Rampage: Rowhammer on Android Oreo 1. Contiguous memory with the ION system heap (vmalloc) • Allocate and free ION chunks (defragmentation) • (many) Multiple consecutive 64 KB requests • Timing side-channel (bank conflicts) to verify 2. Getting allocations in lowmem • Deplete highmem by using mmap • Monitor procfs/pagetypeinfo or procfs/zoneinfo to verify
Rampage Variants App-to-App attacks • ION-to-ION • CMA-to-CMA • CMA-to-system Privilege escalation (Drammer++) Po. C on LG G 4: 64 -bit device running Android 7. 1

GUARDION
Guard. ION Fine grained memory isolation for DMA buffers • Focus on Android/ARM • Cache-eviction based Rowhammer is impossible • Allocate physical guard rows for each DMA allocation
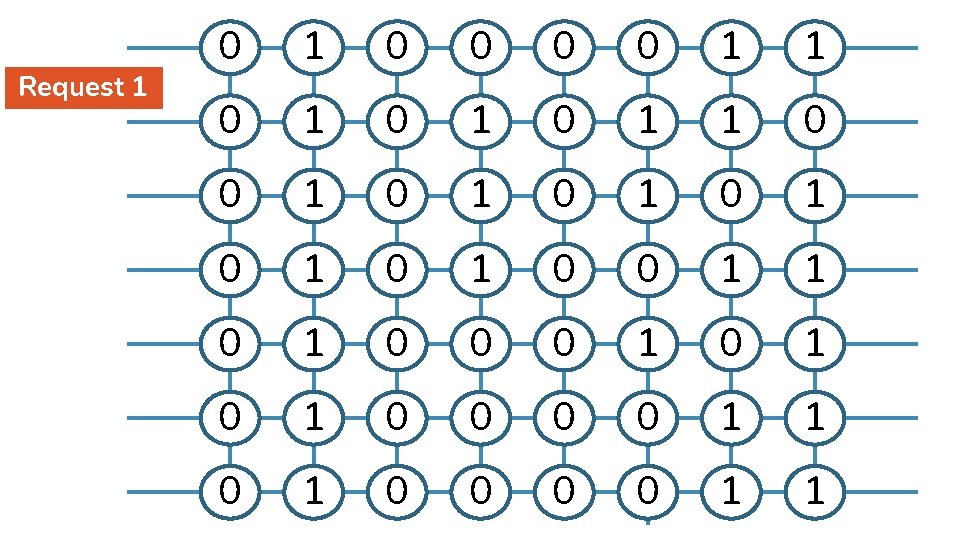
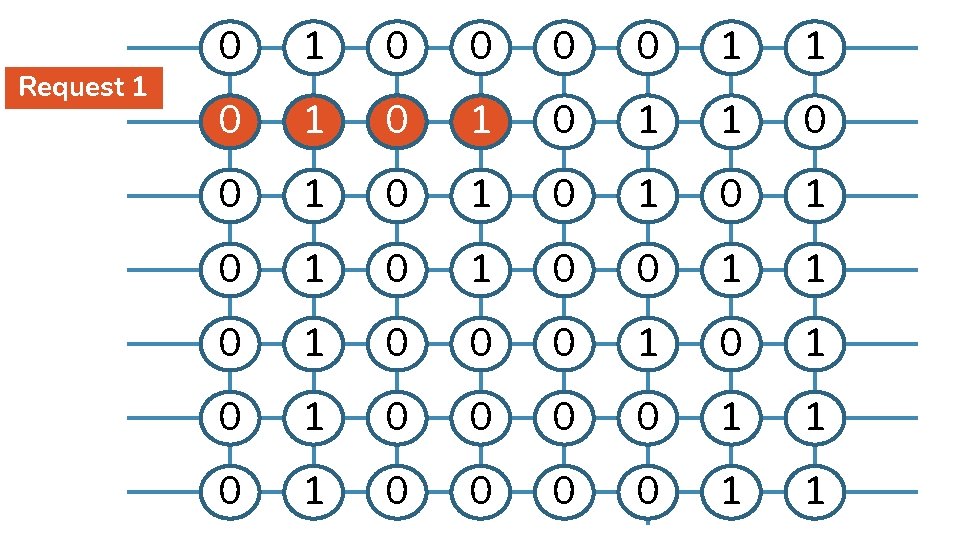
Request 1 0 0 0 0 1 1 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 0 0 1 1
Request 1 0 0 0 0 1 1 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 0 0 1 1
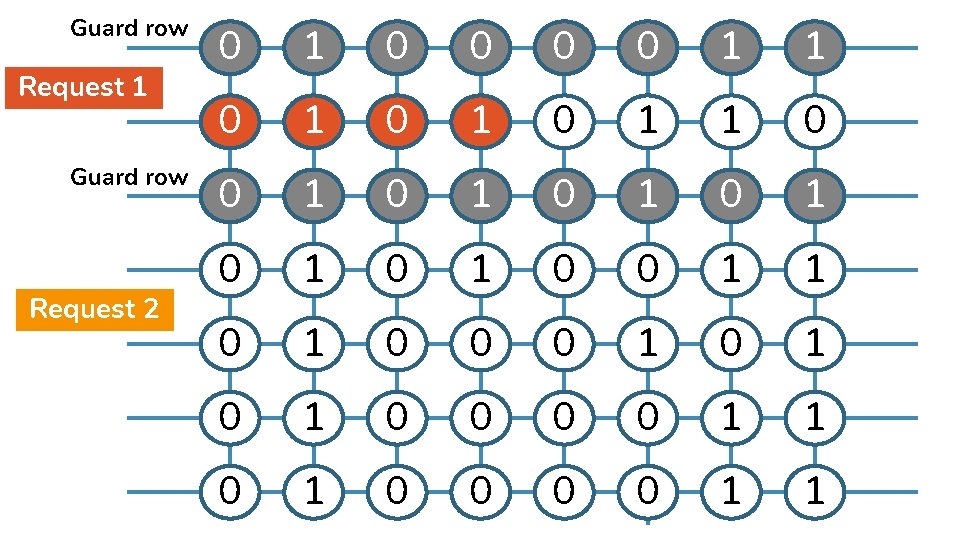
Guard row Request 1 Guard row Request 2 0 1 0 0 1 1 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 0 0 1 1
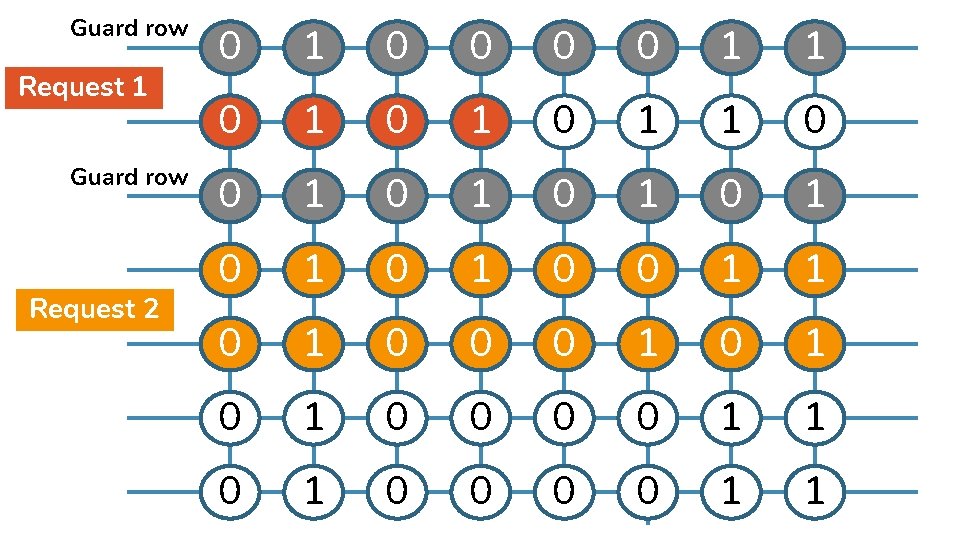
Guard row Request 1 Guard row Request 2 0 1 0 0 1 1 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 0 0 1 1
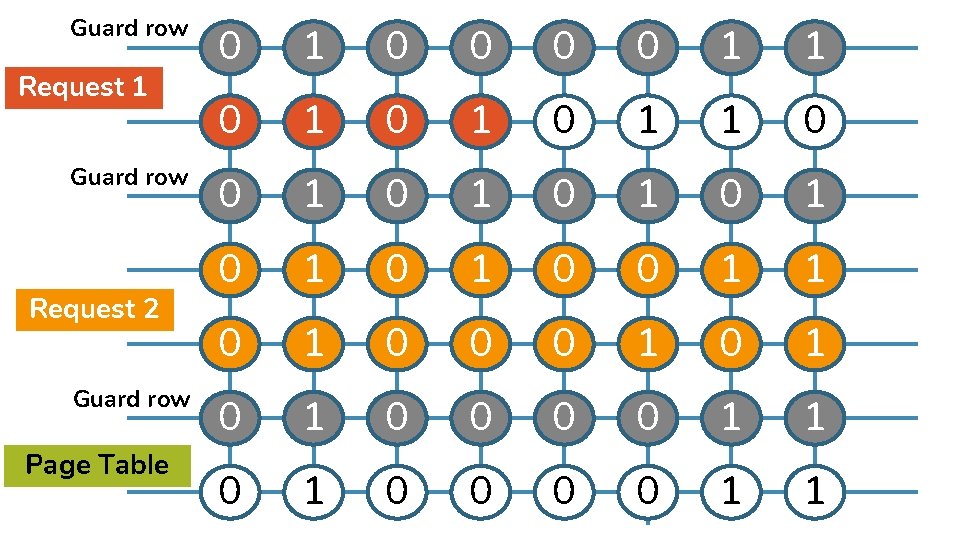
Guard row Request 1 Guard row Request 2 Guard row Page Table 0 1 0 0 1 1 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 0 0 1 1
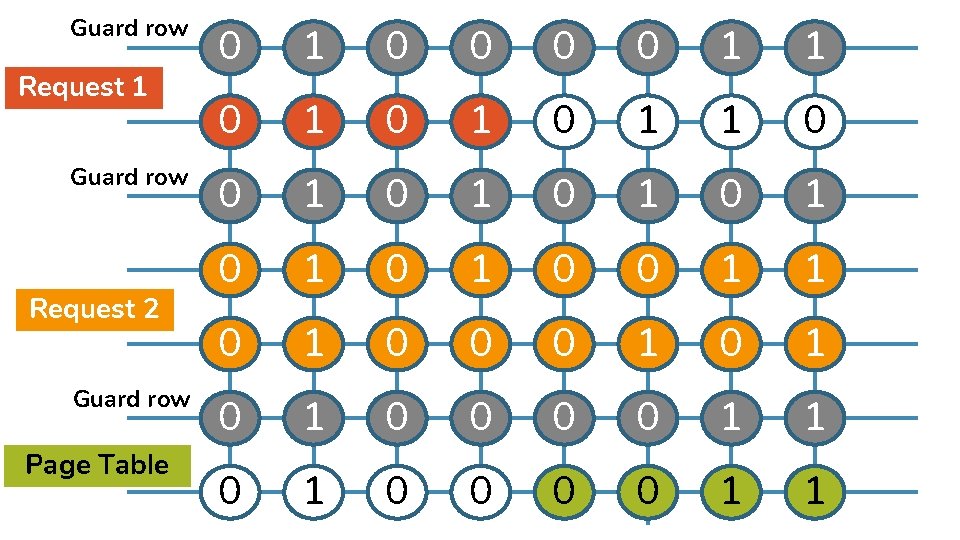
Guard row Request 1 Guard row Request 2 Guard row Page Table 0 1 0 0 1 1 0 1 0 1 1 0 0 1 0 1 0 1 0 0 1 1 0 0 0 1 0 1 0 0 0 0 1 1
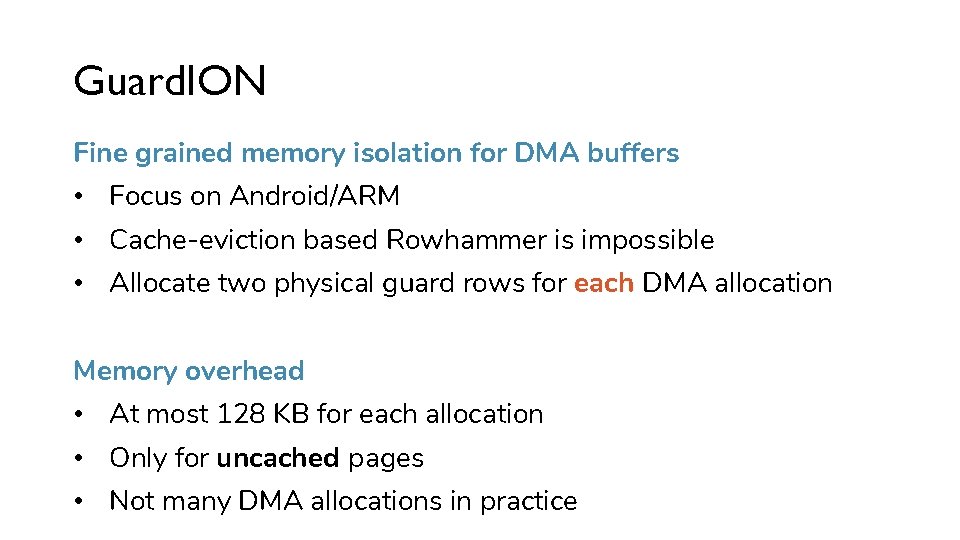
Guard. ION Fine grained memory isolation for DMA buffers • Focus on Android/ARM • Cache-eviction based Rowhammer is impossible • Allocate two physical guard rows for each DMA allocation Memory overhead • At most 128 KB for each allocation • Only for uncached pages • Not many DMA allocations in practice
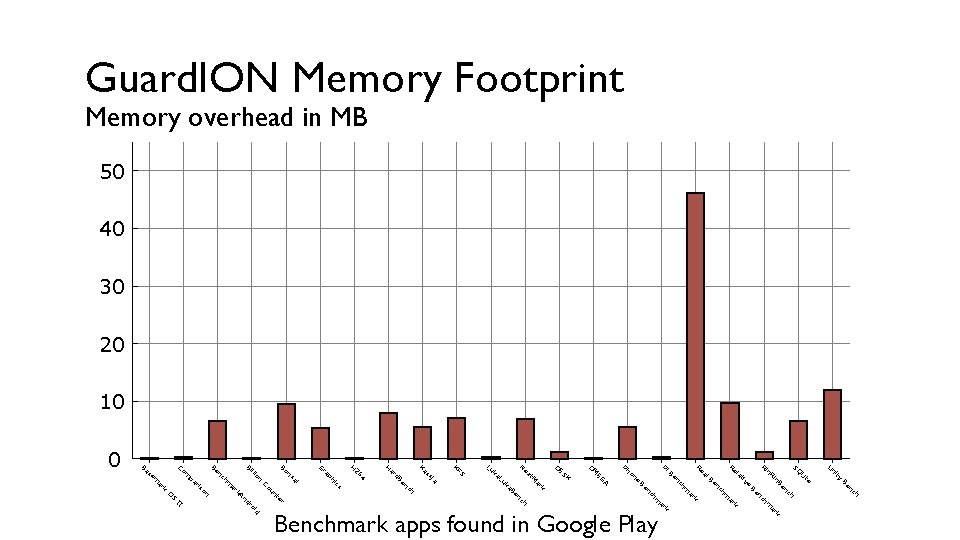
Guard. ION Performance overhead • With Guard. ION, we can re-enable large ION pools • No need for many small allocations, just a single large one • Performance increase! Implementation: • Protection for three heaps: system | CMA | contiguous • 422 lines in 5 files for 3 heaps
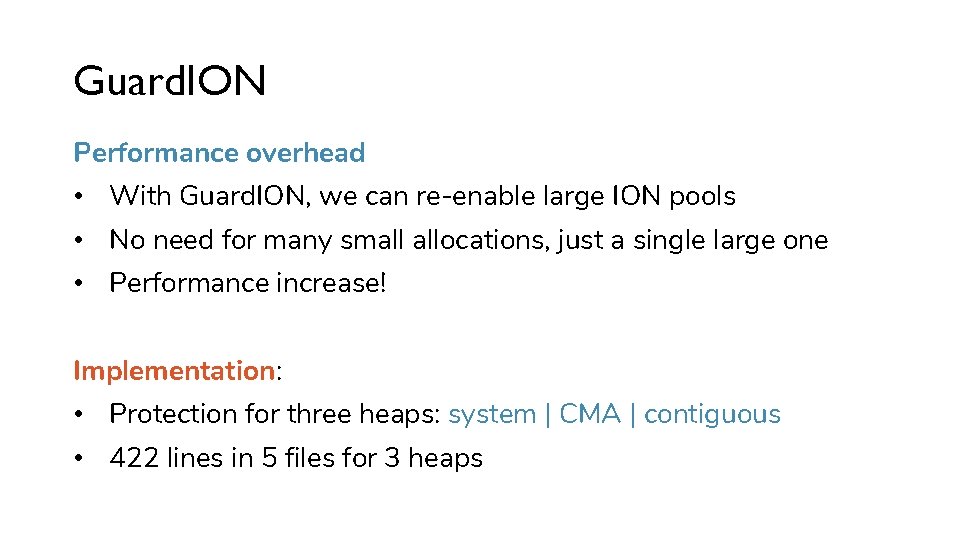
Guard. ION Memory Footprint Memory overhead in MB 50 40 30 20 10 ty ni U h h nc Be te Li SQ ch k ar m ch n Be nc Be in n. R Ri e tiv la Re n Be k ar hm nc k ar h nc hm nc Be A e Be al Re Pi on EG M Ph O K ES k ar t. M ch e a. B uk L ka ex O N Lu S KF ja ss Ka en d. B ar H 4 r te id Benchmark apps found in Google Play ro II nd S k. A un Co cs i ph ra 26 H G ai on ns lli Bo Bi O on ar hm nc Be ris pa m Co k ar em s Ba 0
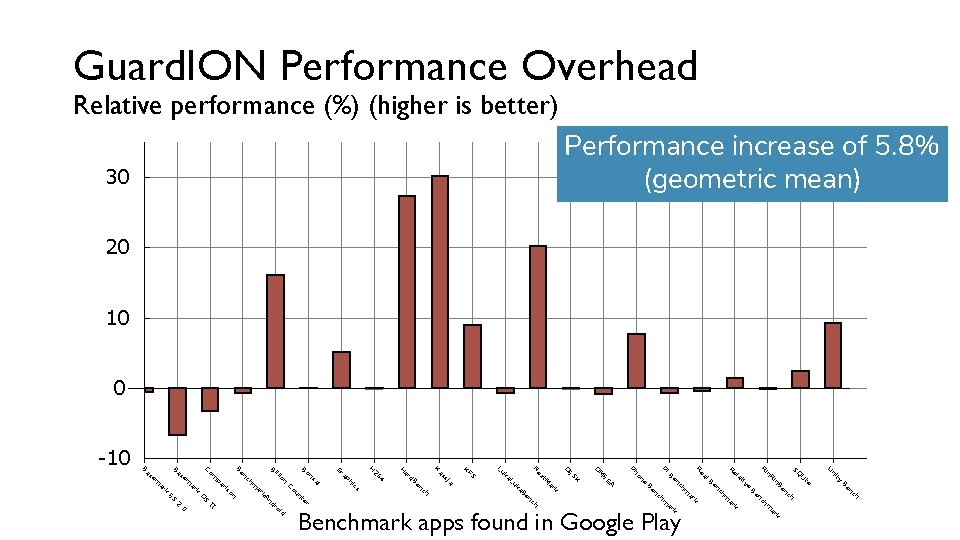
Guard. ION Performance Overhead Relative performance (%) (higher is better) Performance increase of 5. 8% (geometric mean) 30 20 10 0 -10 ty ni U h h nc Be te Li SQ nc ch ar m k ar hm n Be Be in n. R Ri e tiv la Re nc Be k ar hm nc k id k ar ro h nc hm nc Be k ar A e Be al Re Pi on EG M Ph O K ES O t. M ch r te e a. B uk L ka ex N Lu S KF ja ss Ka en d. B ar H cs i ph ra 4 26 H G un Co 0 2. II nd k. A S ES O on ar m ai on ns lli Bo Bi ch n Be k is r pa m Co k ar em s Ba Benchmark apps found in Google Play

CONCLUSION
Disclosure to Google CVE 2018 -9442 The benchmark code provided has much larger allocation sizes than those observed in real-world tests that we have conducted … memory footprint performance impact is much greater than what is cited from your benchmark • This is not good enough (yet) • Looking forward to improve Guard. ION
http: //rampageattack. com Conclusion Rowhammer in 2018 • Overview of defenses – still no working solution • RAMPAGE – Rowhammer attacks on recent Android devices • Guard. ION – Lightweight mitigation by isolating DMA buffers https: //github. com/vusec/guardion Future research 1. Real-world benchmarks for Android 2. Large-scale analysis on vulnerability of devices
- Slides: 48