Growing Pains The Internet in Adolescence Fred Baker
Growing Pains: The Internet in Adolescence Fred Baker ISOC Chairman of the Board Cisco Fellow
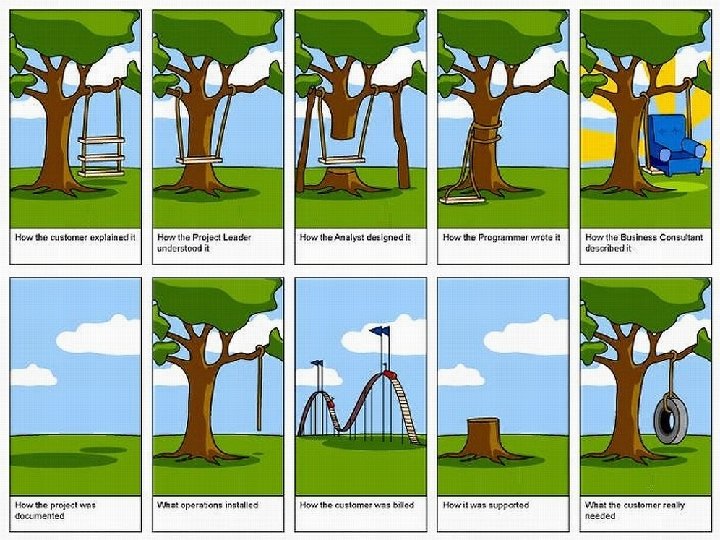
The parable of the swing
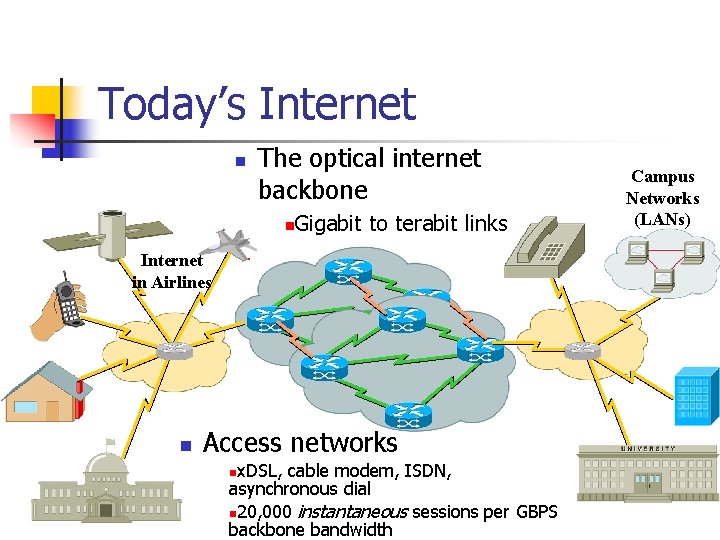
Today’s Internet n The optical internet backbone Gigabit to terabit links n Internet in Airlines n Access networks x. DSL, cable modem, ISDN, asynchronous dial n 20, 000 instantaneous sessions per GBPS backbone bandwidth n Campus Networks (LANs)
Brief History of the Internet Comic Book to Cyberspace
Datagram Switching n Len Kleinrock, 1962 n n n The strength of a chain is its weakest link The strength of a web is its surviving path Datagram Switching n n Developed at UCLA+Xerox PARC DARPA Funding
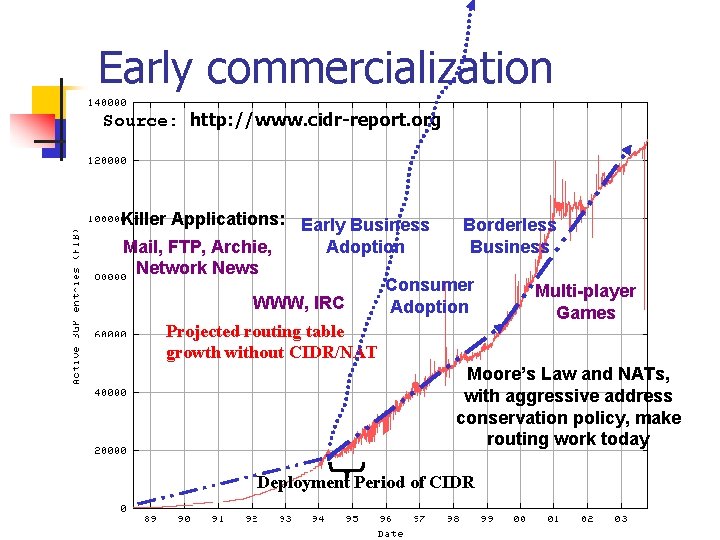
Early commercialization Source: http: //www. cidr-report. org Killer Applications: Early Business Borderless Mail, FTP, Archie, Adoption Business Network News Consumer Multi-player WWW, IRC Adoption Games Projected routing table growth without CIDR/NAT Moore’s Law and NATs, with aggressive address conservation policy, make routing work today Deployment Period of CIDR
Marketing rushes in where engineering fears to tread n Internet bubble: n n n “Build it and they will come” “New Economy” where profitability is irrelevant “. com” era
Profitability… n n …The Final Frontier. Companies are operating on the premise that if it doesn’t make money, it is not a good business to be in…
Status of Internet Technology in developed nations n A utility: n n n Water, Sewer Electricity, Natural Gas Telephone Internet access and facility is assumed in education, business, and increasingly in society
The Digital Divide n “In addressing the digital divide, Uganda and other countries in the region face three broad challenges: n n Creating and exploiting access to external information resources; Creating internal information resources; Creating and exploiting access to internal information resources. A common underlying factor that cuts across the three broad challenges is the need for a competent human resource. ” Dr. F. F. Tusubira Makerere University, February 2003
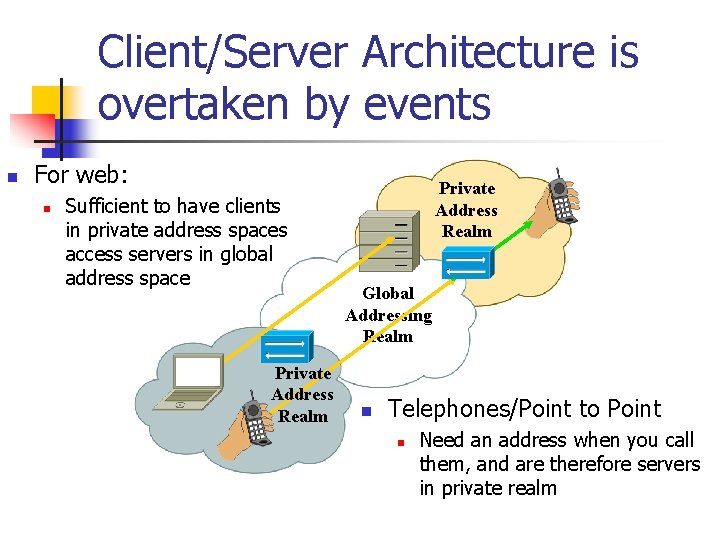
Client/Server Architecture is overtaken by events n For web: n Sufficient to have clients in private address spaces access servers in global address space Private Address Realm Global Addressing Realm n Telephones/Point to Point n Need an address when you call them, and are therefore servers in private realm
Who are today’s application innovators? n Open Source example: Freenet/Ka. Za. A n n n Large-scale peer-to-peer network Pools the power of member computers Create a massive virtual information store Open to anyone Highly survivable, private, secure, efficient, http: //www. firenze. linux. it/~marcoc/index. php? page=w hatis
History of the IETF
Originally supporting Research Networks n Dates: n n Started 1986 Non-US participation by 1988 First non-US meeting: Vancouver, August 1990 Constituents: n n n Originally US Government only Added NSFNET (NRN), education, research Eventually added vendors The government left… International participation
Characterizing the community: n Semi-homogenous n n “Netiquette” n n People largely knew and trusted each other Anti-social behavior drew direct and public censure as “impolite” Key interest: n Making the Internet interesting and useful for themselves and their friends.
IETF Mission Statement n Make the Internet Work n n Whatever it takes… But what is the Internet? n n IPv 4? IPv 6? MPLS? Applications like WWW? Mail? Vo. IP?
Historical principles n n n End to End principle Robustness principle Rough Consensus and Running Code Institutionalized altruism Mutual Benefit n n n Managed Trust Highly relational Principle of least surprise Openness Anti-kings Achieving “right” results because they are right
Now supporting all IP-based Networks n Constituents: n n Researchers Network Operators n n Implementers (engineers, often from vendors) n n n ISP, NRN, Enterprise Large percentage of attendees Interactions with various governments… Fully international participation
Characterizing the community: n Heterogeneous n n “Netiquette” n n n Business reasons for involvement Expectation of safe environment Moving towards codification of expectations Key interest: n Defining technology to use or to sell
Undercurrents n Business agenda n n n Intellectual Property Issues n n Business relationships rather than personal relationships Political process About protecting ideas, not sharing them Civil servants as leaders
IETF: in a maze of twisty passages – all different
What makes IETF hard? Breakdown of trust n n Community sees leaders as a cabal Leaders see community that designs for narrow scope of applicability or misses key issues
What makes IETF hard? Opaque processes n n n RFC Editor Secretariat Internet Assigned Number Authority Internet Engineering Steering Group Internet Architecture Board
What makes IETF hard? Consensus process n n Lack of comment interpreted as consent, but may mean loss of interest Consensus may not be desired by participants seeking market share
What makes IETF hard? Personal responsibility n Expectation that “they” should do something: n n IETF composed of people, and people do the work Personal involvement essential to progress

The IESG is rapidly approaching a solution
Sounds like bad news n Not really n n n The IETF is just deciding what it wants to be when it grows up… Quite a bit of good work going on there Other groups of interest n n NANOG, Apricot, RIPE, etc Many others
What is next for the Internet?
High-end research backbones n Combining IP routing and optical routing in overlay networks n n n “Designer networks” for research purposes Production networks for applications What parts of network to research? n n n Routing (IP, Optical) Applications IPv 6 -based
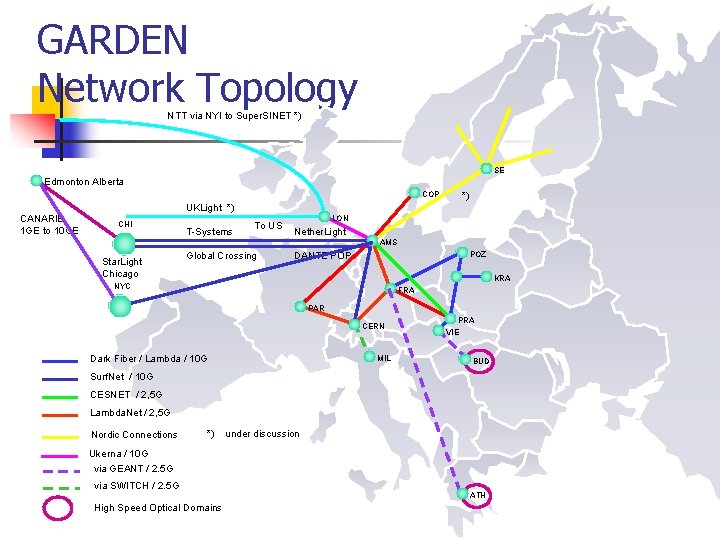
GARDEN Network Topology NTT via NYI to Super. SINET *) SE Edmonton Alberta COP CANARIE 1 GE to 10 GE *) UKLight *) CHI T-Systems To US LON Nether. Light AMS Star. Light Chicago Global Crossing POZ DANTE POP KRA NYC FRA PAR CERN Dark Fiber / Lambda / 10 G MIL PRA VIE BUD Surf. Net / 10 G CESNET / 2, 5 G Lambda. Net / 2, 5 G Nordic Connections *) under discussion Ukerna / 10 G via GEANT / 2. 5 G via SWITCH / 2. 5 G High Speed Optical Domains ATH
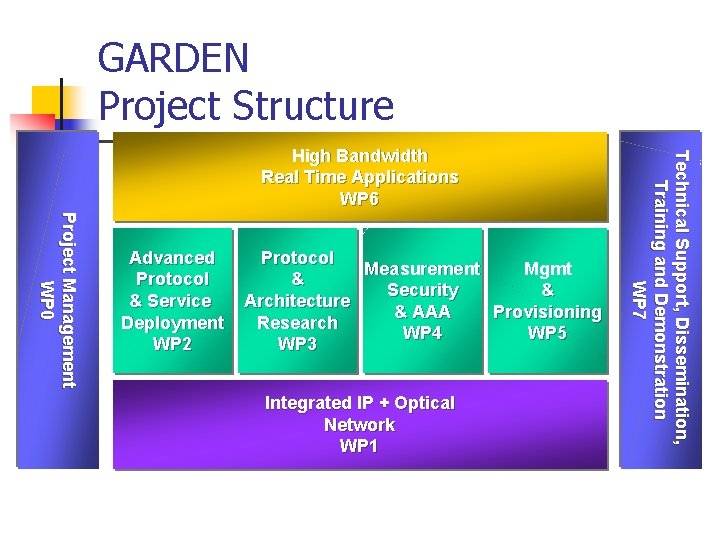
GARDEN Project Structure Project Management WP 0 Advanced Protocol & Service Deployment WP 2 Protocol Measurement Mgmt & Security & Architecture & AAA Provisioning Research WP 4 WP 5 WP 3 Integrated IP + Optical Network WP 1 Technical Support, Dissemination, Training and Demonstration WP 7 High Bandwidth Real Time Applications WP 6
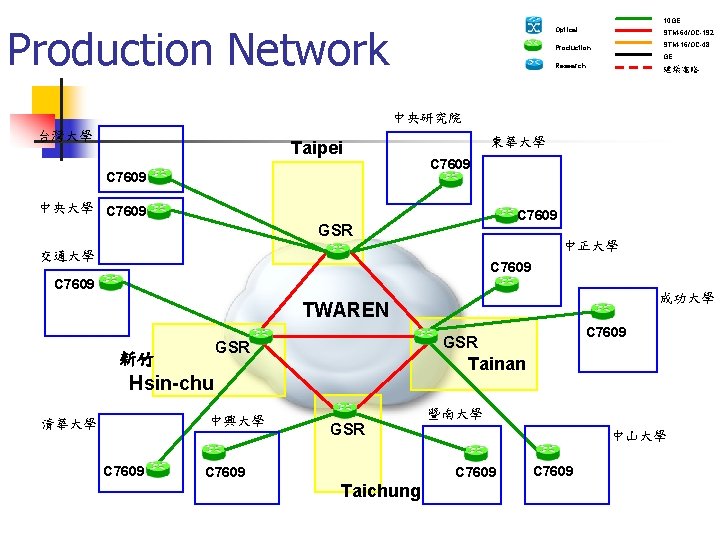
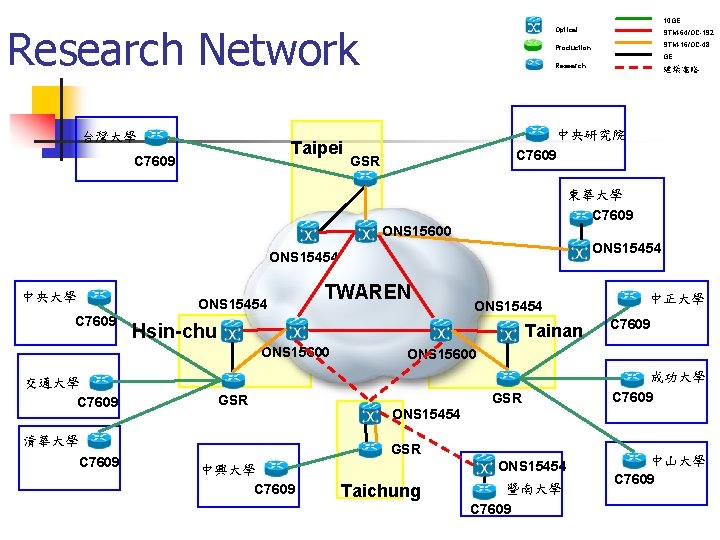
10 GE Production Network Optical STM-64/OC-192 Production STM-16/OC-48 GE Research 建議電路 中央研究院 台灣大學 Taipei C 7609 東華大學 C 7609 中央大學 C 7609 GSR 中正大學 交通大學 C 7609 成功大學 TWAREN GSR 新竹 Tainan Hsin-chu 中興大學 清華大學 C 7609 GSR 暨南大學 中山大學 C 7609 Taichung C 7609
10 GE Research Network 台灣大學 Taipei C 7609 Optical STM-64/OC-192 Production STM-16/OC-48 GE Research 建議電路 中央研究院 C 7609 GSR 東華大學 C 7609 ONS 15600 ONS 15454 中央大學 ONS 15454 C 7609 TWAREN Hsin-chu Tainan ONS 15600 交通大學 C 7609 GSR 清華大學 C 7609 ONS 15454 C 7609 ONS 15600 ONS 15454 GSR 中興大學 C 7609 中正大學 ONS 15454 Taichung 暨南大學 C 7609 成功大學 C 7609 中山大學 C 7609
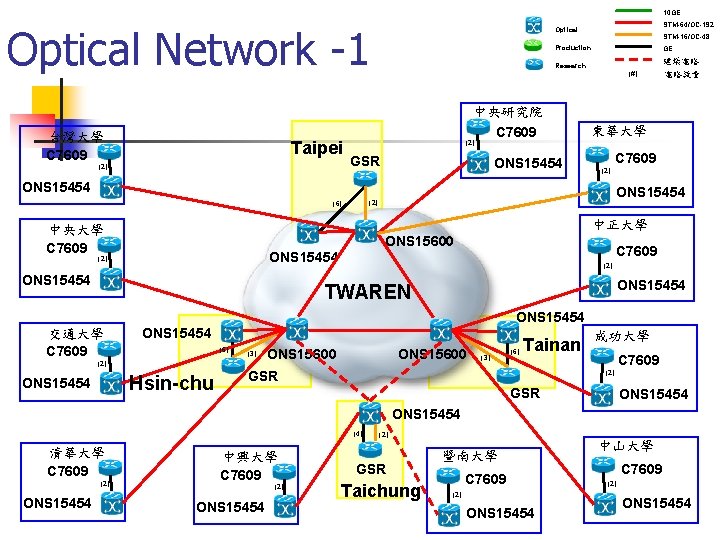
10 GE Optical Network -1 台灣大學 C 7609 Taipei (2) STM-64/OC-192 Optical STM-16/OC-48 Production GE Research 中央研究院 C 7609 (#) 建議電路 電路數量 東華大學 (2) GSR ONS 15454 C 7609 (2) ONS 15454 (2) (6) 中正大學 中央大學 C 7609 ONS 15600 C 7609 ONS 15454 (2) ONS 15454 TWAREN ONS 15454 交通大學 C 7609 ONS 15454 (6) (3) (2) Hsin-chu ONS 15454 ONS 15600 (3) (6) Tainan GSR 成功大學 C 7609 (2) GSR ONS 15454 (4) 清華大學 C 7609 (2) ONS 15454 中興大學 C 7609 (2) ONS 15454 (2) GSR Taichung 暨南大學 C 7609 (2) ONS 15454 中山大學 C 7609 (2) ONS 15454
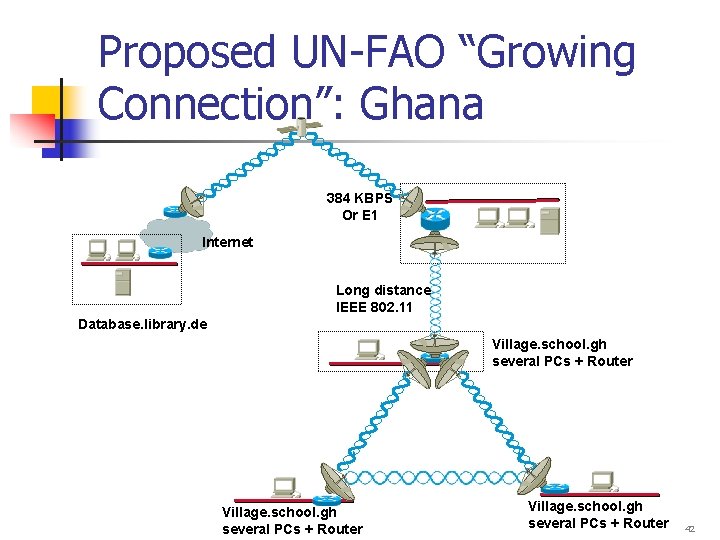
Proposed UN-FAO “Growing Connection”: Ghana 384 KBPS Or E 1 Internet Long distance IEEE 802. 11 Database. library. de Village. school. gh several PCs + Router 42
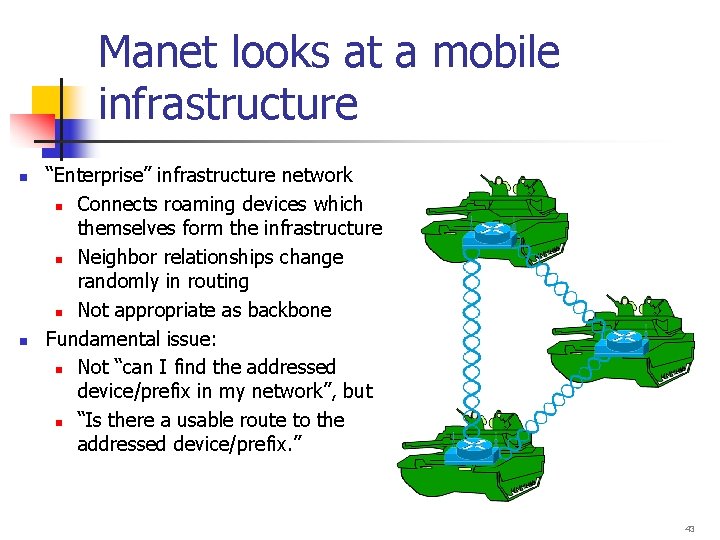
Manet looks at a mobile infrastructure n n “Enterprise” infrastructure network n Connects roaming devices which themselves form the infrastructure n Neighbor relationships change randomly in routing n Not appropriate as backbone Fundamental issue: n Not “can I find the addressed device/prefix in my network”, but n “Is there a usable route to the addressed device/prefix. ” 43
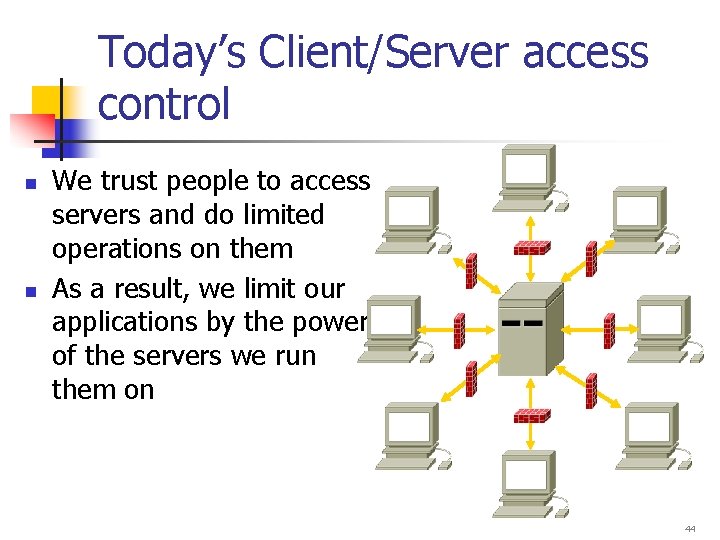
Today’s Client/Server access control n n We trust people to access servers and do limited operations on them As a result, we limit our applications by the power of the servers we run them on 44
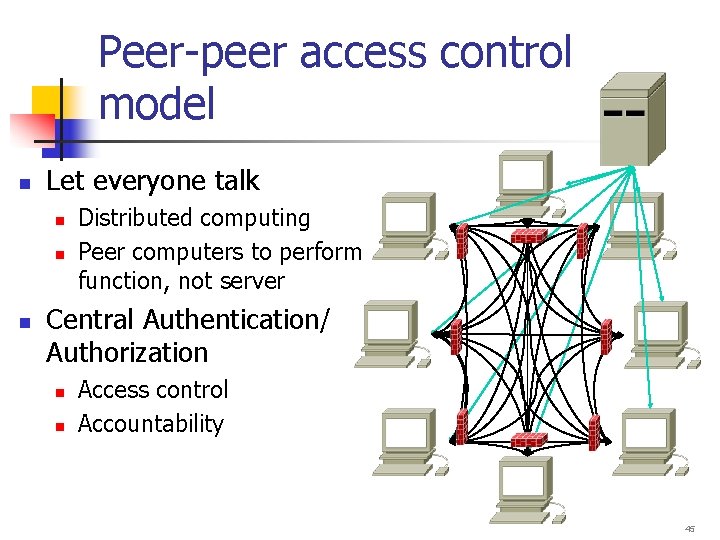
Peer-peer access control model n Let everyone talk n n n Distributed computing Peer computers to perform function, not server Central Authentication/ Authorization n n Access control Accountability 45
What needs to change? n Effective prophylactic security n n n Firewall ≠ Network Address Translator Secure Firewall Traversal Secure identity/authority management n n n Spam management… Good point-to-point application software and models (Freenet/Ka. Za. A? ) Managability…
“As new IP communications services and devices become available, they may stimulate new demand increase Vo. IP traffic flows beyond the growth rates characteristic of the traditional voice telephony market. … the total market may reach … six percent of the world's forecasted international traffic for the calendar year 2001” Telegeography 2002 47
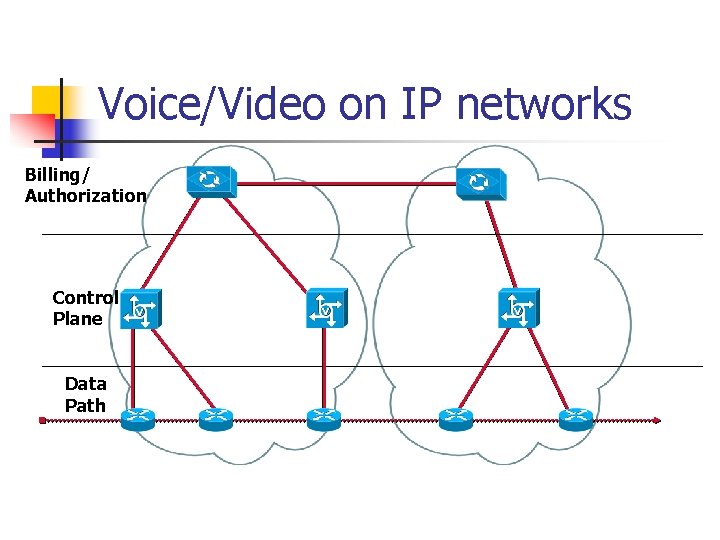
Voice/Video on IP networks Billing/ Authorization Control Plane Data Path
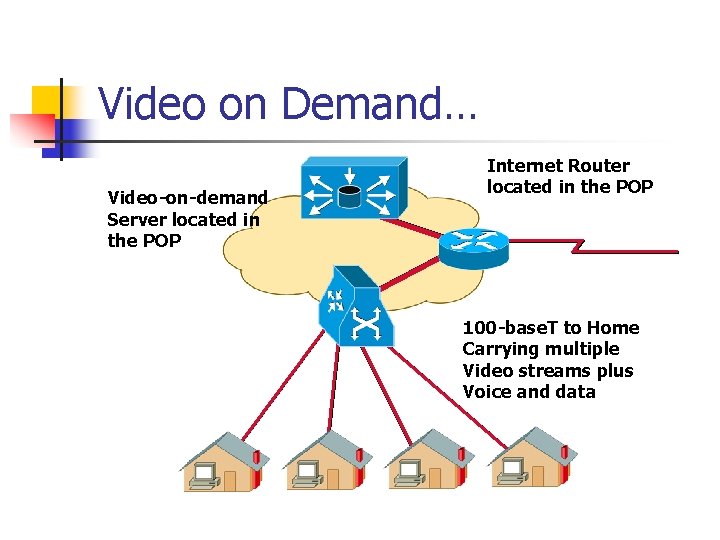
Video on Demand… Video-on-demand Server located in the POP Internet Router located in the POP 100 -base. T to Home Carrying multiple Video streams plus Voice and data
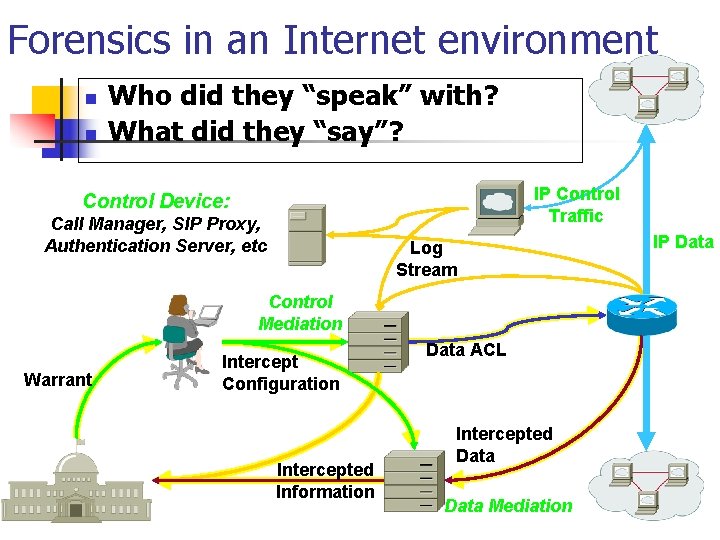
Forensics in an Internet environment n n Who did they “speak” with? What did they “say”? IP Control Traffic Control Device: Call Manager, SIP Proxy, Authentication Server, etc Log Stream Control Mediation Warrant Intercept Configuration Intercepted Information Data ACL Intercepted Data Mediation IP Data
Growing Up… n n n Profitability… User-tolerant (if not friendly) applications Business-tolerant applications… Manageable applications and networks Convergence…
Growing Pains: The Internet in Adolescence Fred Baker ISOC Chairman of the Board Cisco Fellow
- Slides: 46