Government Security Objectives Define trust trustworthy environment assurance

Government Security
Objectives Define trust, trustworthy environment, assurance, clearance, two-person integrity, no lone zone, certification, accreditation, emergency destruction, humint. • Define the four stages of operational planning. • Define operations security, unclassified indicator. • Define two types of TEMPEST zoning. • Define the meaning of red and black labels. • Define computer/transmission emanation protections: shielding, filtering, masking, attenuation, zoning, and protection distribution system. • Define checks in a security clearance • Determine access by security level and compartment. • Define Resource monitor, and differentiate between types of computers: Dedicated, Compartmented, Multilevel Resource, System-High. • Define threats: jamming, traffic analysis, and transmission security techniques: spread spectrum, burst transmissions, low power, directional antenna. • Define 3 techniques the government uses to secure encryption keys. • Define protection of voice communication. Italic has yet to be included. •
Trustworthy environment: Safe equipment, reliable boundary, safe people • Assurance: Behavior complies with policy – Formal methods can use proofs • Clearance: Trusted person • Two-Person Integrity: No Lone Zone
Trustworthy environment: Safe equipment, reliable boundary, safe people • Safe Communications • Safe Processing • Safe Storage
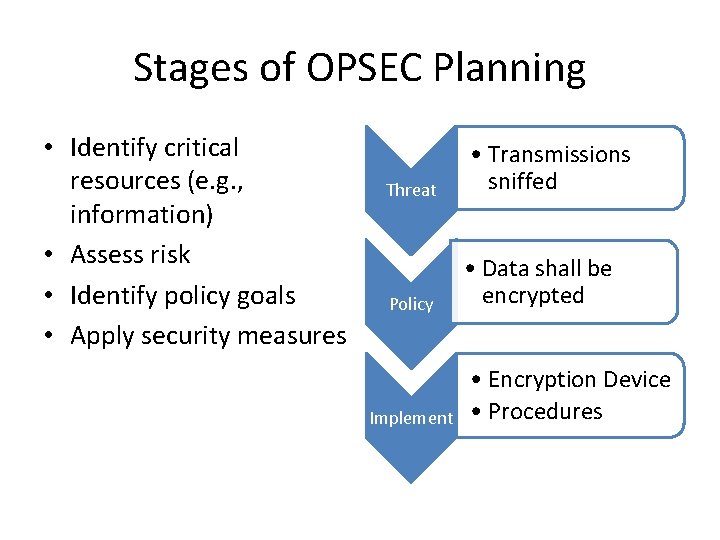
Stages of OPSEC Planning • Identify critical resources (e. g. , information) • Assess risk • Identify policy goals • Apply security measures Threat Policy Implement • Transmissions sniffed • Data shall be encrypted • Encryption Device • Procedures
Security Clearances SECURE PEOPLE
Trusted People: Security Clearance • Clearance: Enables trust • Background investigation may include: – Ask person about: drug use, work history, criminal history. – Third party checks on employment, habits. – Criminal background check – Credit check • Confidential Clearance: Low level clearance • Secret Clearance: High level clearance
TEMPEST Zoning – Unclassified Indicators SECURE BOUNDARIES
Operations Security Sometimes plans are broadcast unintentionally This is known as ‘unclassified indicators’. • Before a major offensive attack, to-go pizza orders go up in DC/Pentagon, pizza vendors recognize.
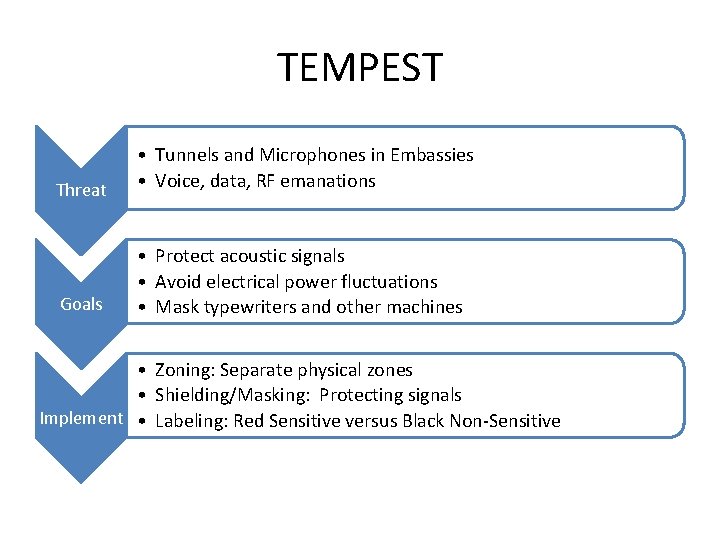
TEMPEST Threat • Tunnels and Microphones in Embassies • Voice, data, RF emanations Goals • Protect acoustic signals • Avoid electrical power fluctuations • Mask typewriters and other machines • Zoning: Separate physical zones • Shielding/Masking: Protecting signals Implement • Labeling: Red Sensitive versus Black Non-Sensitive
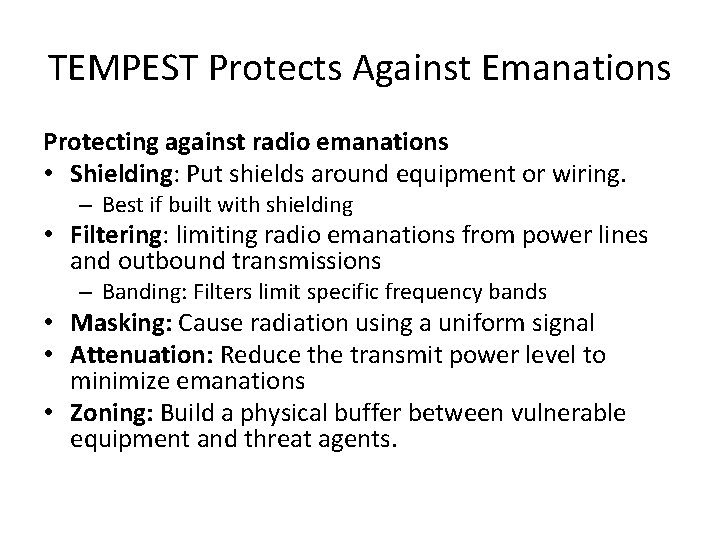
TEMPEST Protects Against Emanations Protecting against radio emanations • Shielding: Put shields around equipment or wiring. – Best if built with shielding • Filtering: limiting radio emanations from power lines and outbound transmissions – Banding: Filters limit specific frequency bands • Masking: Cause radiation using a uniform signal • Attenuation: Reduce the transmit power level to minimize emanations • Zoning: Build a physical buffer between vulnerable equipment and threat agents.
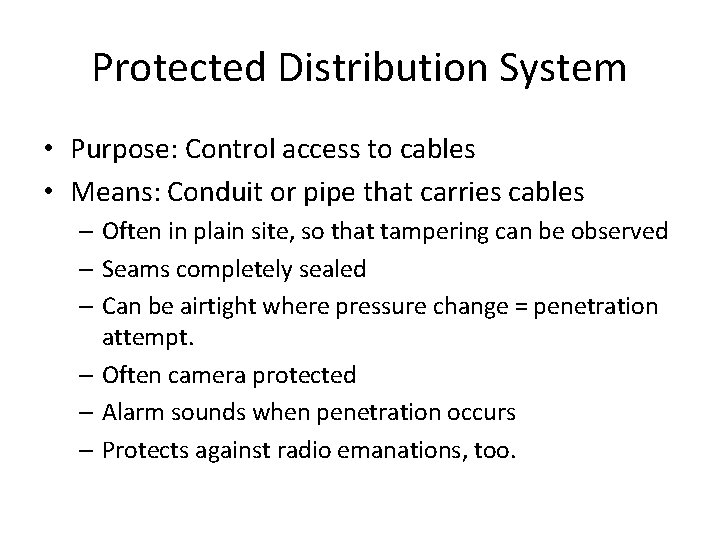
Protected Distribution System • Purpose: Control access to cables • Means: Conduit or pipe that carries cables – Often in plain site, so that tampering can be observed – Seams completely sealed – Can be airtight where pressure change = penetration attempt. – Often camera protected – Alarm sounds when penetration occurs – Protects against radio emanations, too.
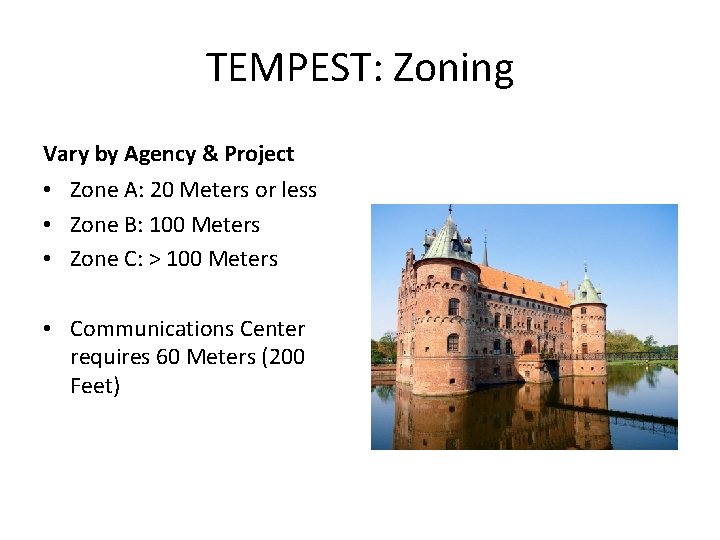
TEMPEST: Zoning Vary by Agency & Project • Zone A: 20 Meters or less • Zone B: 100 Meters • Zone C: > 100 Meters • Communications Center requires 60 Meters (200 Feet)
TEMPEST Zoning Threat: Crosstalk or Coupling Solution: Separation between Cables: • 2 inches: shielded components • 6 inches: unshielded components • 3 feet: crypto equipment & shielded components Power Filtering: • 2 inches from shielded components • 6 inches from other components • Red & Black grounds maintained separately. • Labeling: Red & Black
Access Control - SECURE PROCESSING
Trusted Computing: High Assurance Trustworthy: Never enters insecure state • Formal design specification • Formal methods: proofs show never enters insecure state – Secure, unsecure states defined • Code must match formal specifications Drawbacks: • Expensive to produce: can double cost • Very few systems achieve TCB
Trusted Computer System Trusted Computing Base • Formally verified to enforce mandatory protection policy • Verified (Tested) Drawbacks • Cannot assure high availability • Not easy to obtain: MS Word has been used Reference Monitor • • • Enforces security policy Not bypassable Tamperproof Verified Simple easiest
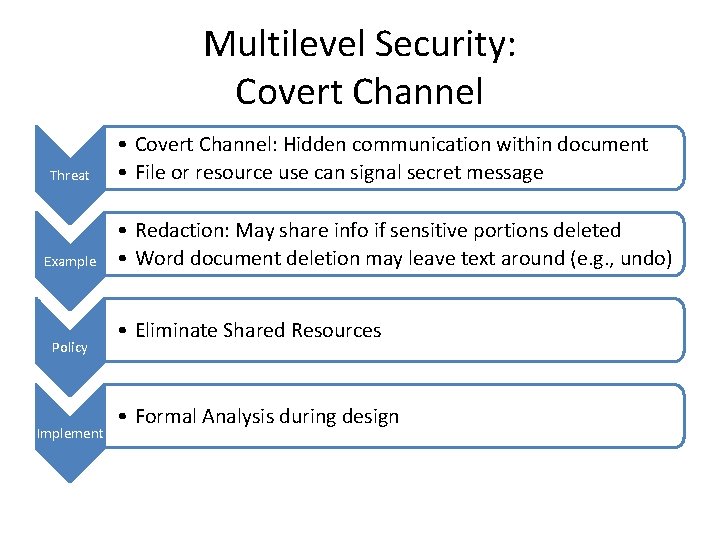
Multilevel Security: Covert Channel Threat Example Policy Implement • Covert Channel: Hidden communication within document • File or resource use can signal secret message • Redaction: May share info if sensitive portions deleted • Word document deletion may leave text around (e. g. , undo) • Eliminate Shared Resources • Formal Analysis during design
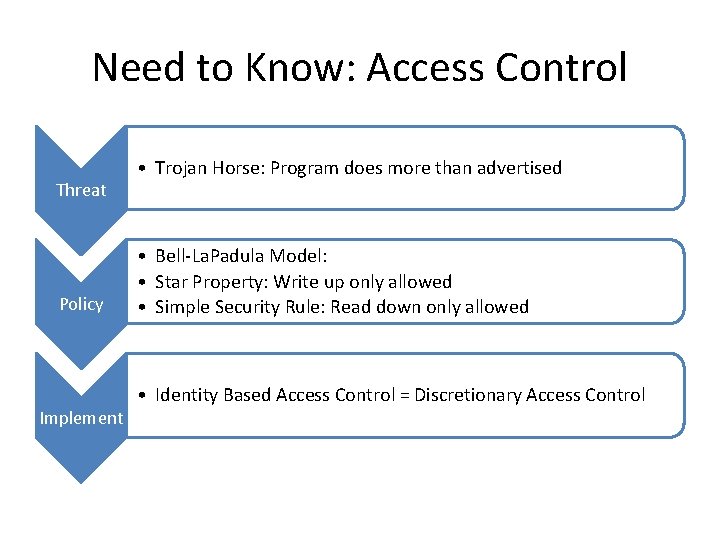
Need to Know: Access Control Threat Policy Implement • Trojan Horse: Program does more than advertised • Bell-La. Padula Model: • Star Property: Write up only allowed • Simple Security Rule: Read down only allowed • Identity Based Access Control = Discretionary Access Control
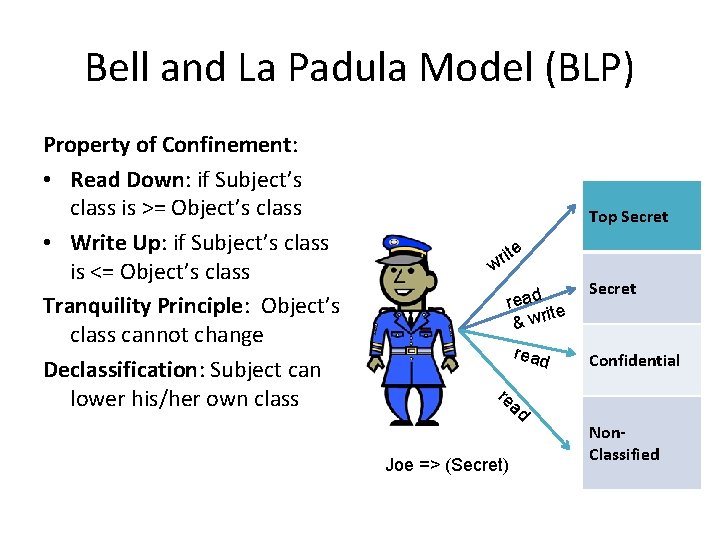
Bell and La Padula Model (BLP) Property of Confinement: • Read Down: if Subject’s class is >= Object’s class • Write Up: if Subject’s class is <= Object’s class Tranquility Principle: Object’s class cannot change Declassification: Subject can lower his/her own class Top Secret ite r w read ite & wr Secret read Confidential re ad Joe => (Secret) Non. Classified
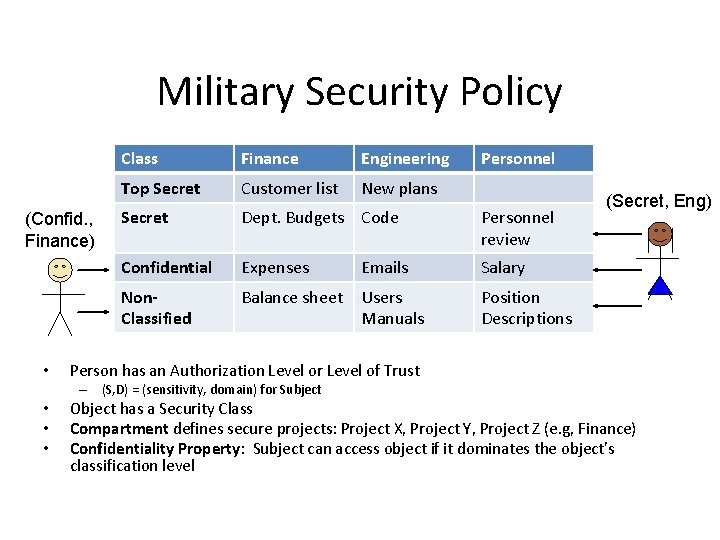
Military Security Policy (Confid. , Finance) • Class Finance Engineering Top Secret Customer list New plans Secret Dept. Budgets Code Personnel review Confidential Expenses Emails Salary Non. Classified Balance sheet Users Manuals Position Descriptions (Secret, Eng) Person has an Authorization Level or Level of Trust – (S, D) = (sensitivity, domain) for Subject • • • Personnel Object has a Security Class Compartment defines secure projects: Project X, Project Y, Project Z (e. g, Finance) Confidentiality Property: Subject can access object if it dominates the object’s classification level
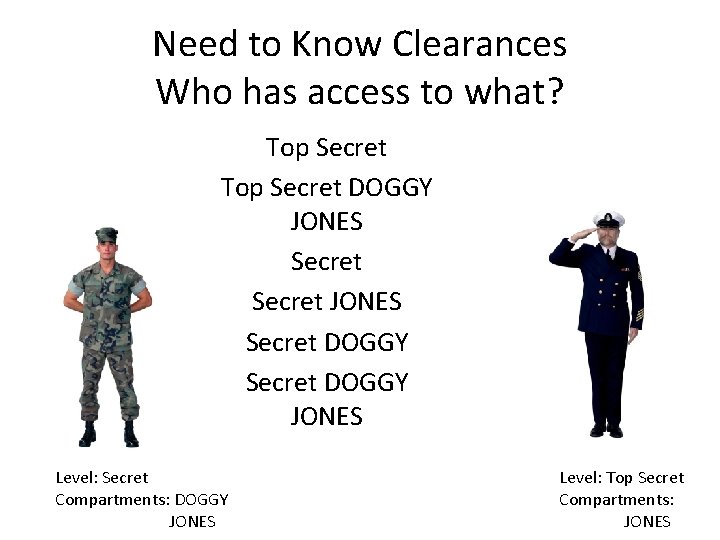
Need to Know Clearances Who has access to what? Top Secret DOGGY JONES Secret DOGGY JONES Level: Secret Compartments: DOGGY JONES Level: Top Secret Compartments: JONES
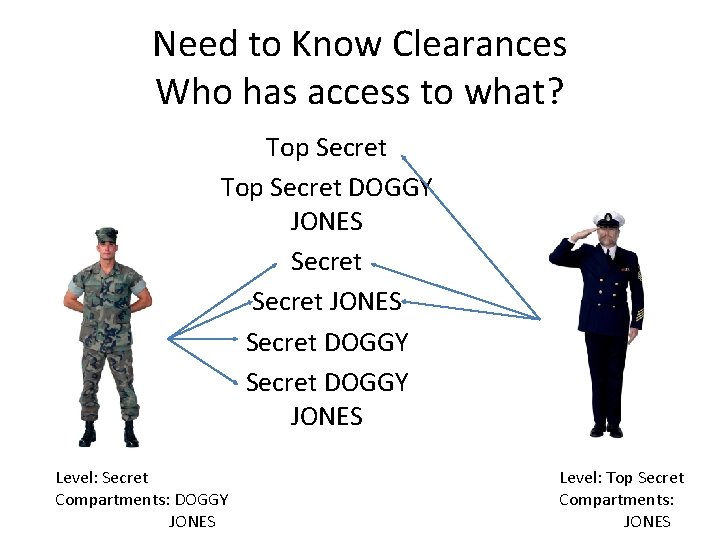
Need to Know Clearances Who has access to what? Top Secret DOGGY JONES Secret DOGGY JONES Level: Secret Compartments: DOGGY JONES Level: Top Secret Compartments: JONES
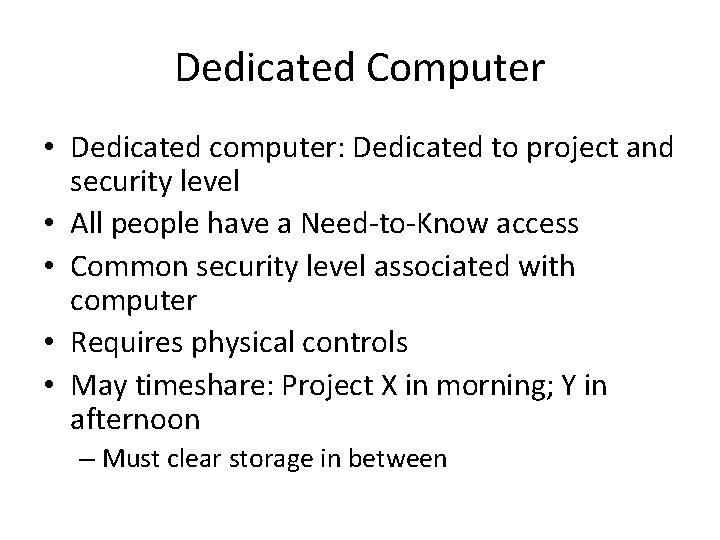
Dedicated Computer • Dedicated computer: Dedicated to project and security level • All people have a Need-to-Know access • Common security level associated with computer • Requires physical controls • May timeshare: Project X in morning; Y in afternoon – Must clear storage in between
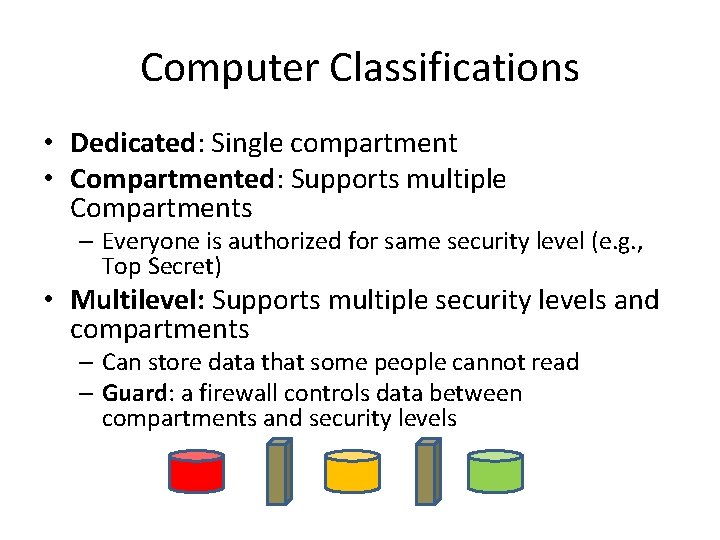
Computer Classifications • Dedicated: Single compartment • Compartmented: Supports multiple Compartments – Everyone is authorized for same security level (e. g. , Top Secret) • Multilevel: Supports multiple security levels and compartments – Can store data that some people cannot read – Guard: a firewall controls data between compartments and security levels
Encryption – Masking SECURE COMMUNICATIONS
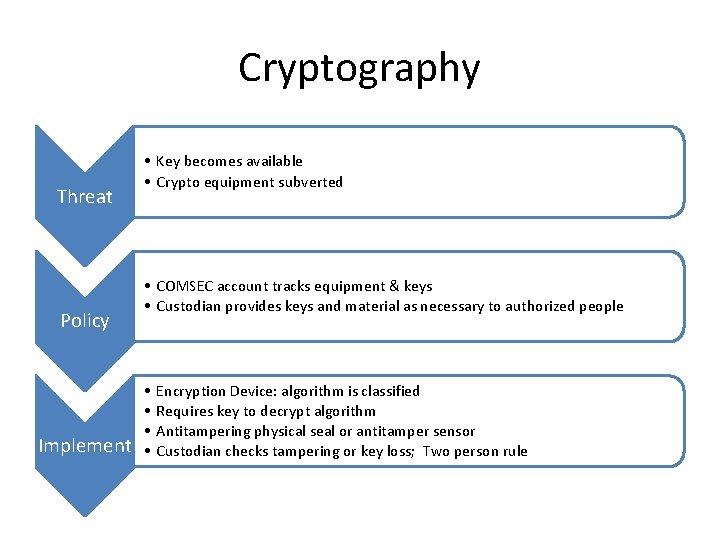
Cryptography Threat Policy Implement • Key becomes available • Crypto equipment subverted • COMSEC account tracks equipment & keys • Custodian provides keys and material as necessary to authorized people • • Encryption Device: algorithm is classified Requires key to decrypt algorithm Antitampering physical seal or antitamper sensor Custodian checks tampering or key loss; Two person rule
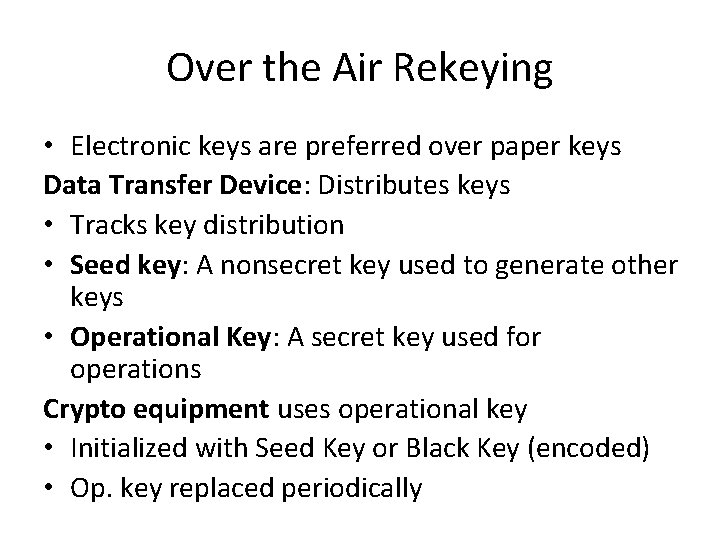
Over the Air Rekeying • Electronic keys are preferred over paper keys Data Transfer Device: Distributes keys • Tracks key distribution • Seed key: A nonsecret key used to generate other keys • Operational Key: A secret key used for operations Crypto equipment uses operational key • Initialized with Seed Key or Black Key (encoded) • Op. key replaced periodically
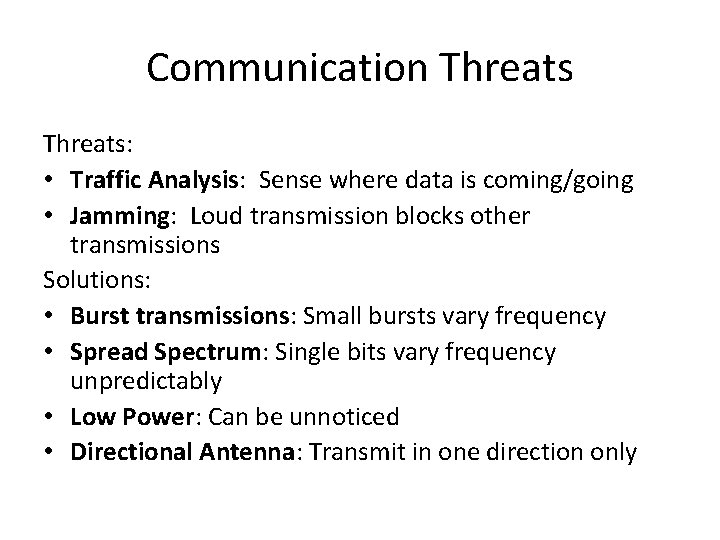
Communication Threats: • Traffic Analysis: Sense where data is coming/going • Jamming: Loud transmission blocks other transmissions Solutions: • Burst transmissions: Small bursts vary frequency • Spread Spectrum: Single bits vary frequency unpredictably • Low Power: Can be unnoticed • Directional Antenna: Transmit in one direction only
Example: Nuclear SECURE OPERATIONS
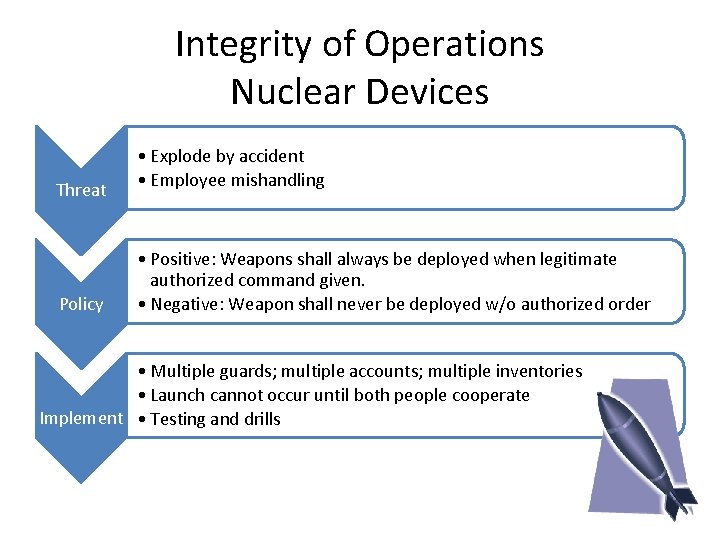
Integrity of Operations Nuclear Devices Threat Policy • Explode by accident • Employee mishandling • Positive: Weapons shall always be deployed when legitimate authorized command given. • Negative: Weapon shall never be deployed w/o authorized order • Multiple guards; multiple accounts; multiple inventories • Launch cannot occur until both people cooperate Implement • Testing and drills
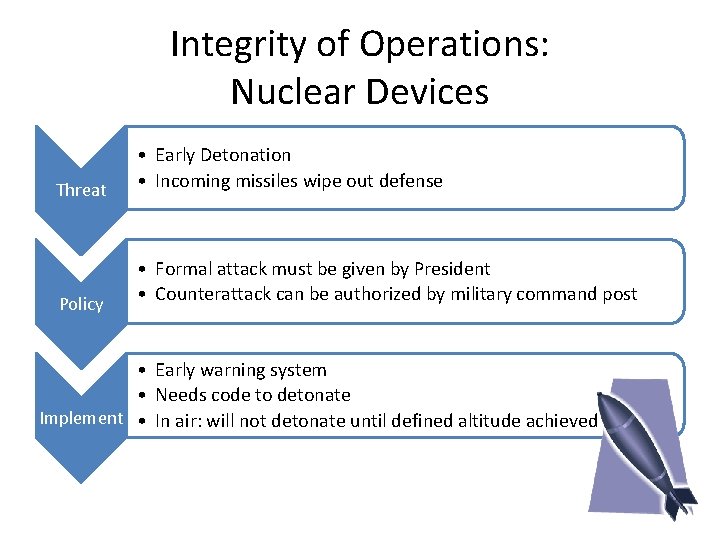
Integrity of Operations: Nuclear Devices Threat • Early Detonation • Incoming missiles wipe out defense Policy • Formal attack must be given by President • Counterattack can be authorized by military command post • Early warning system • Needs code to detonate Implement • In air: will not detonate until defined altitude achieved
- Slides: 32