Global Internet Content Delivery Bruce Maggs Akamai Technologies
Global Internet Content Delivery Bruce Maggs Akamai Technologies and Carnegie Mellon University
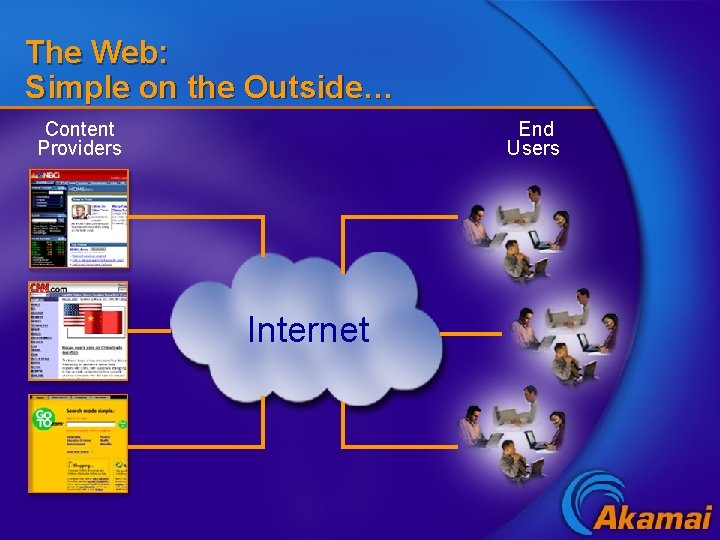
The Web: Simple on the Outside… Content Providers End Users Internet
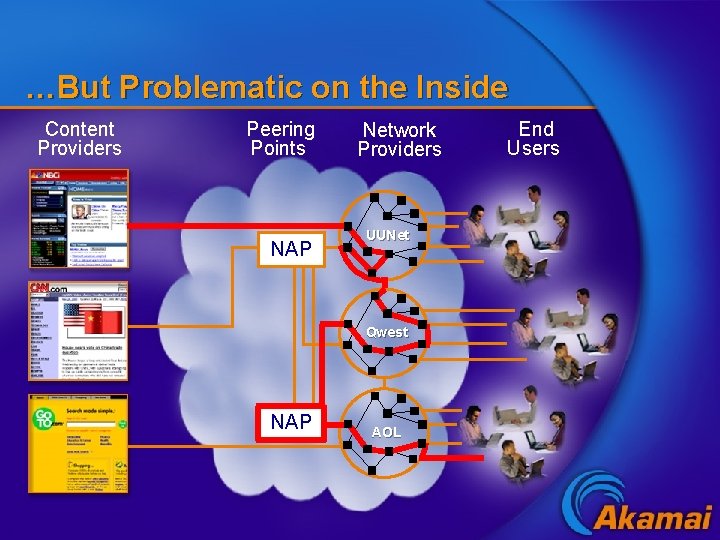
…But Problematic on the Inside Content Providers Peering Points NAP Network Providers UUNet Qwest NAP AOL End Users
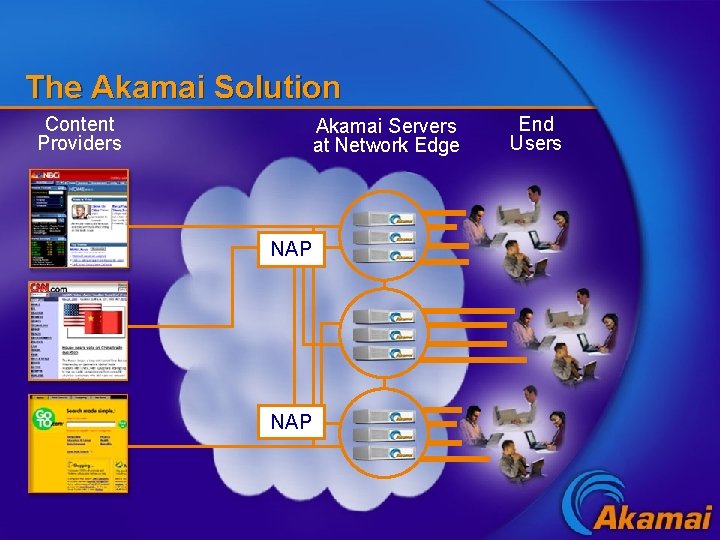
The Akamai Solution Content Providers Akamai Servers at Network Edge NAP End Users
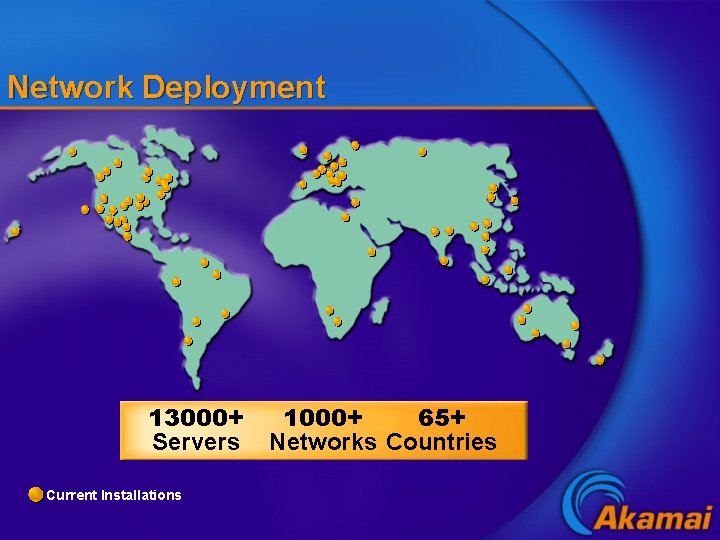
Network Deployment 13000+ Servers Current Installations 1000+ 65+ Networks Countries
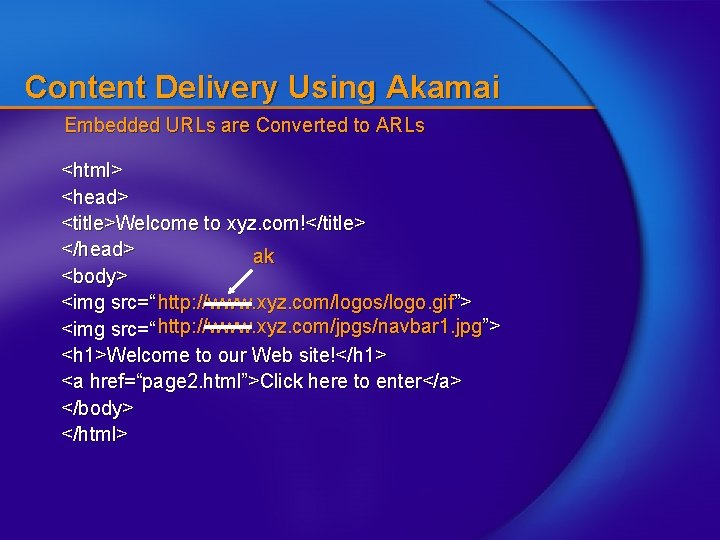
Content Delivery Using Akamai Embedded URLs are Converted to ARLs <html> <head> <title>Welcome to xyz. com!</title> </head> ak <body> <img src=“ http: //www. xyz. com/logos/logo. gif”> <img src=“ http: //www. xyz. com/jpgs/navbar 1. jpg”> <h 1>Welcome to our Web site!</h 1> <a href=“page 2. html”>Click here to enter</a> </body> </html>
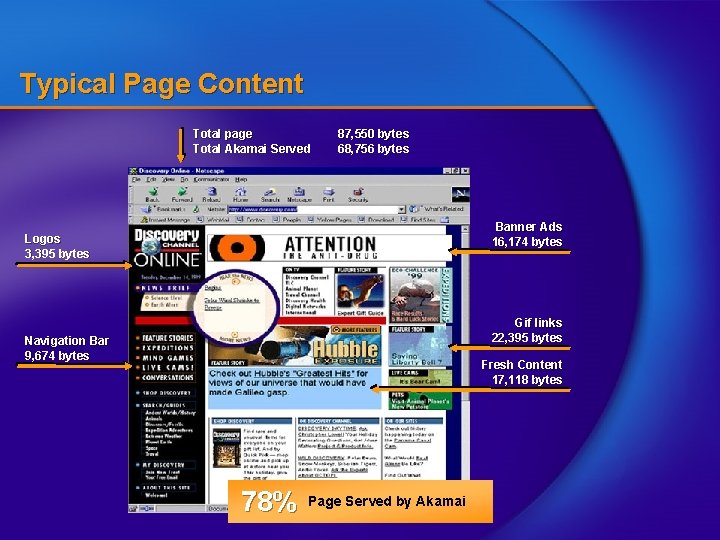
Typical Page Content Total page Total Akamai Served 87, 550 bytes 68, 756 bytes Banner Ads 16, 174 bytes Logos 3, 395 bytes Gif links 22, 395 bytes Navigation Bar 9, 674 bytes Fresh Content 17, 118 bytes 78% Page Served by Akamai
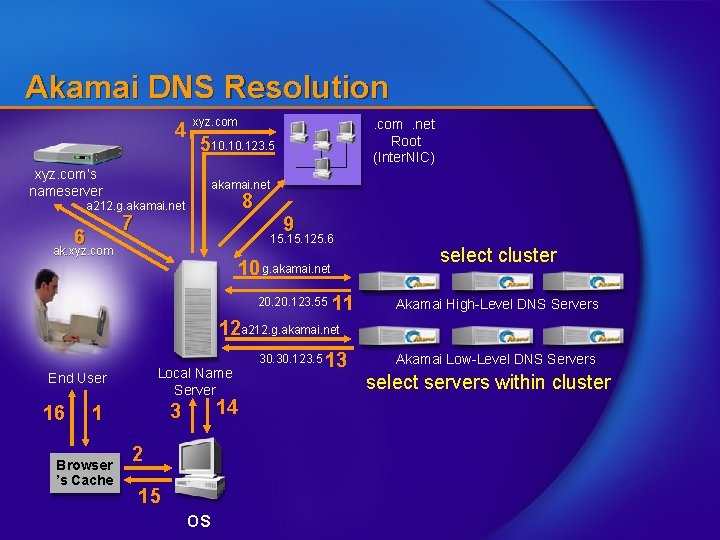
Akamai DNS Resolution 4 xyz. com 510. 123. 5 xyz. com’s nameserver akamai. net 8 a 212. g. akamai. net 7 6 . com. net Root (Inter. NIC) 9 15. 125. 6 ak. xyz. com 10 g. akamai. net 20. 123. 55 11 select cluster Akamai High-Level DNS Servers 12 a 212. g. akamai. net Local Name Server End User 16 Browser ’s Cache 14 3 1 2 15 OS 30. 123. 5 13 Akamai Low-Level DNS Servers select servers within cluster

Over 1300 Web Sites are Now Akamaized
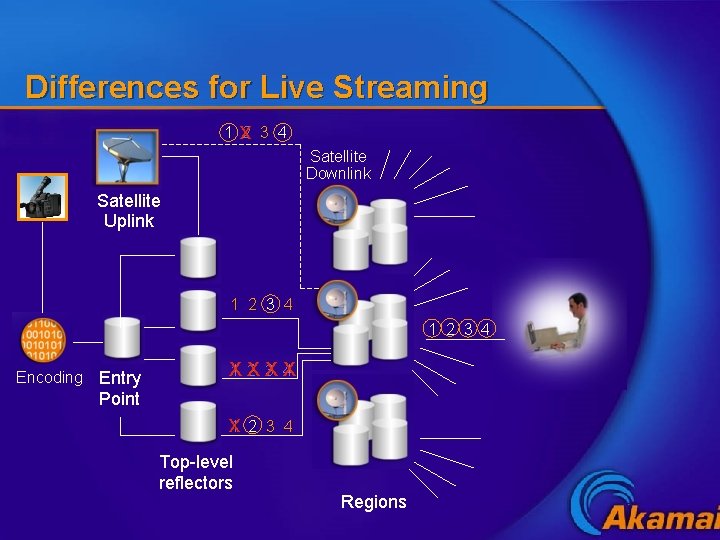
Differences for Live Streaming 1 x 2 3 4 Satellite Downlink Satellite Uplink 1 2 3 4 Encoding Entry Point 1 X 2 X 3 4 X X x 1 2 Top-level reflectors 3 4 Regions
![Page Assembly Container Page [TTL=5 d] [TTL=8 h] [XYZ news, content, promotions, etc. TTL=5 Page Assembly Container Page [TTL=5 d] [TTL=8 h] [XYZ news, content, promotions, etc. TTL=5](http://slidetodoc.com/presentation_image/2f3ac3417d66b28e7f500747096bf54c/image-11.jpg)
Page Assembly Container Page [TTL=5 d] [TTL=8 h] [XYZ news, content, promotions, etc. TTL=5 d] [TTL=15 m] [Breaking headlines TTL=2 h] Site owners create container pages that can be populated with varying content
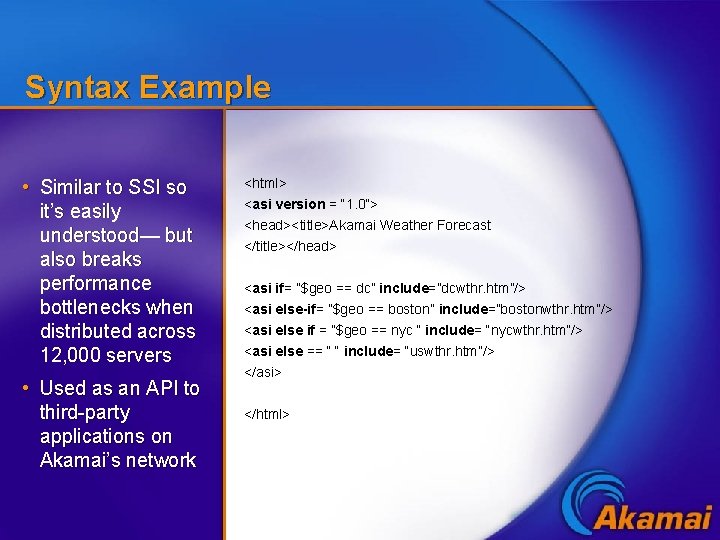
Syntax Example • Similar to SSI so it’s easily understood— but also breaks performance bottlenecks when distributed across 12, 000 servers • Used as an API to third-party applications on Akamai’s network <html> <asi version = “ 1. 0”> <head><title>Akamai Weather Forecast </title></head> <asi if= ”$geo == dc” include=”dcwthr. htm”/> <asi else-if= ”$geo == boston” include=”bostonwthr. htm”/> <asi else if = ”$geo == nyc “ include= “nycwthr. htm”/> <asi else == “ “ include= “uswthr. htm”/> </asi> </html>
Connecting from the Edge to the Source End User Source Server
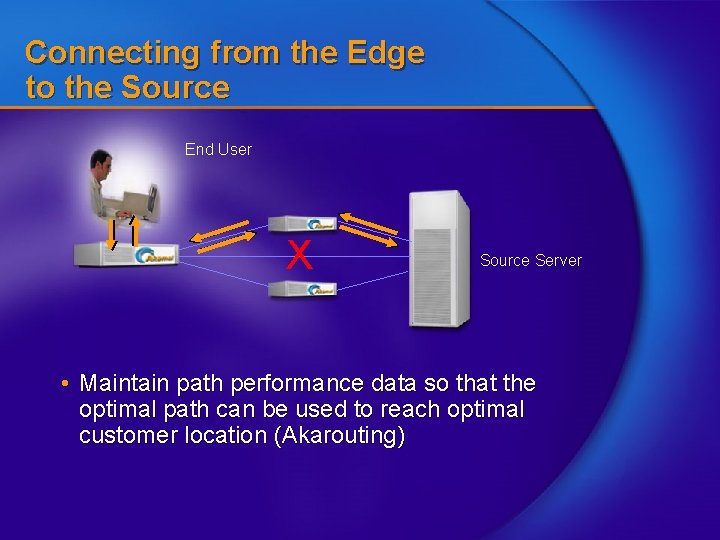
Connecting from the Edge to the Source End User X Source Server • Maintain path performance data so that the optimal path can be used to reach optimal customer location (Akarouting)

Akamai Cluster Servers pool resources • RAM • Disk • Throughput
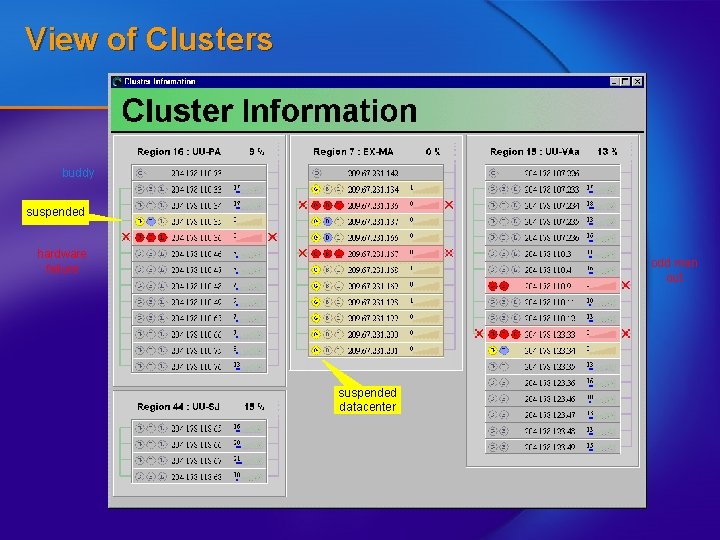
View of Clusters buddy suspended hardware failure odd man out suspended datacenter
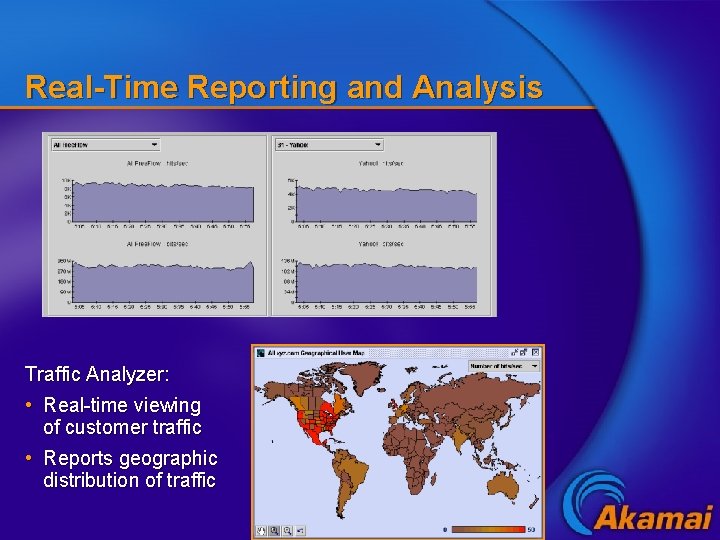
Real-Time Reporting and Analysis Traffic Analyzer: • Real-time viewing of customer traffic • Reports geographic distribution of traffic
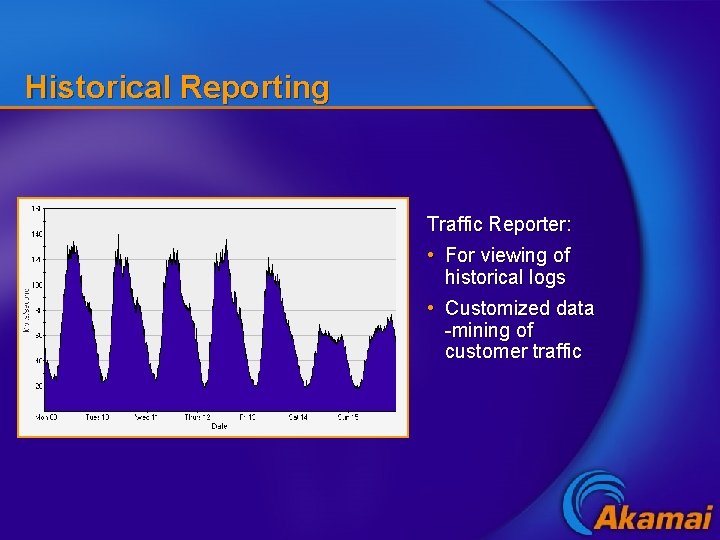
Historical Reporting Traffic Reporter: • For viewing of historical logs • Customized data -mining of customer traffic
9/11 Summary • Akamai’s network had capacity for all content providers requesting service • Total bits served on September 11 was approximately 3. 5 times normal • Traffic was higher on September 12 • (But not as high as January 7, 2002)
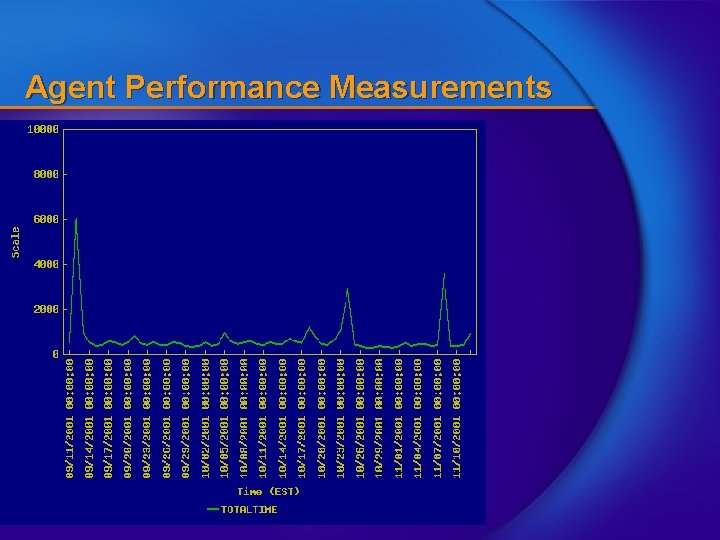
Agent Performance Measurements
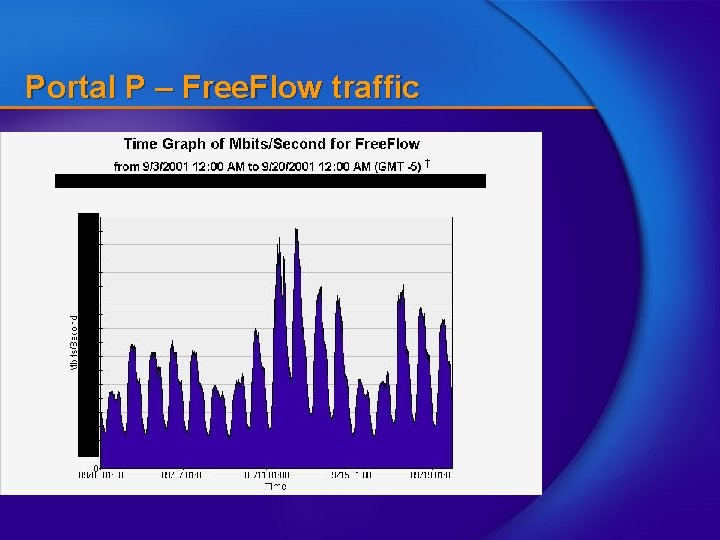
Portal P – Free. Flow traffic
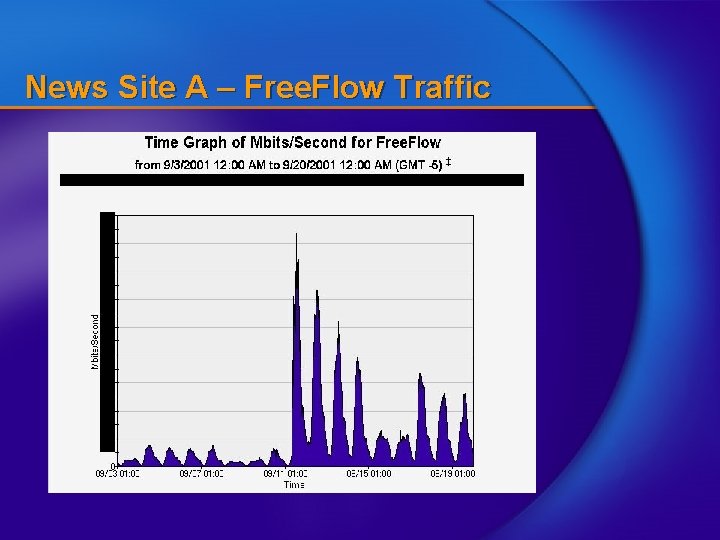
News Site A – Free. Flow Traffic
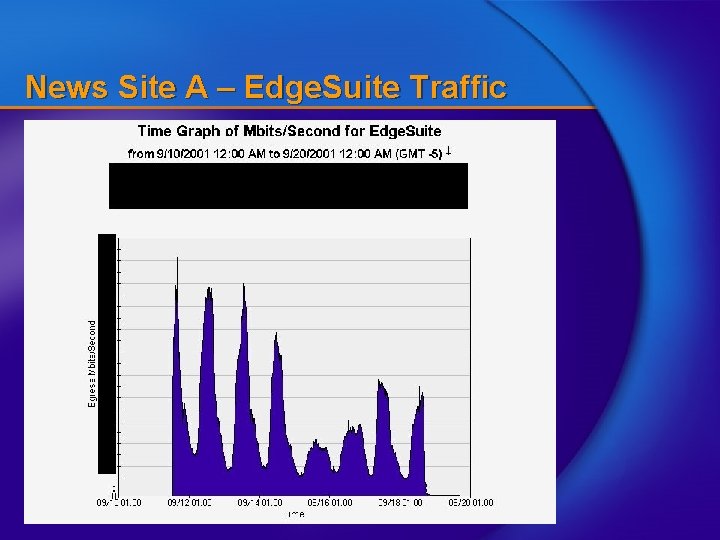
News Site A – Edge. Suite Traffic
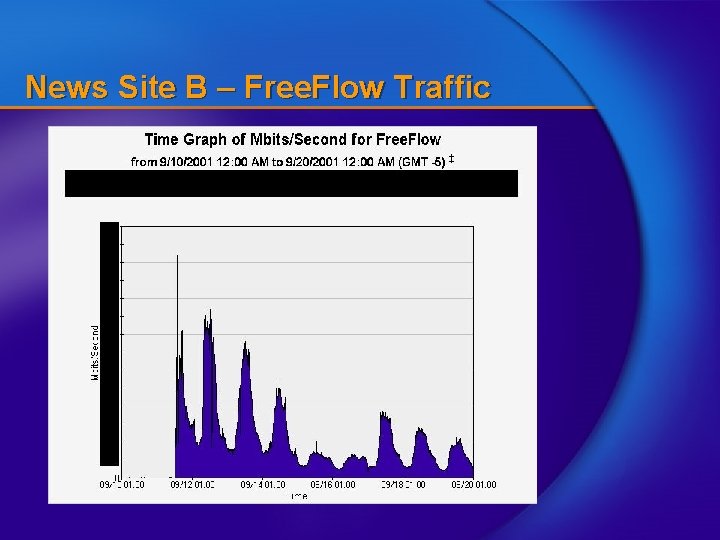
News Site B – Free. Flow Traffic
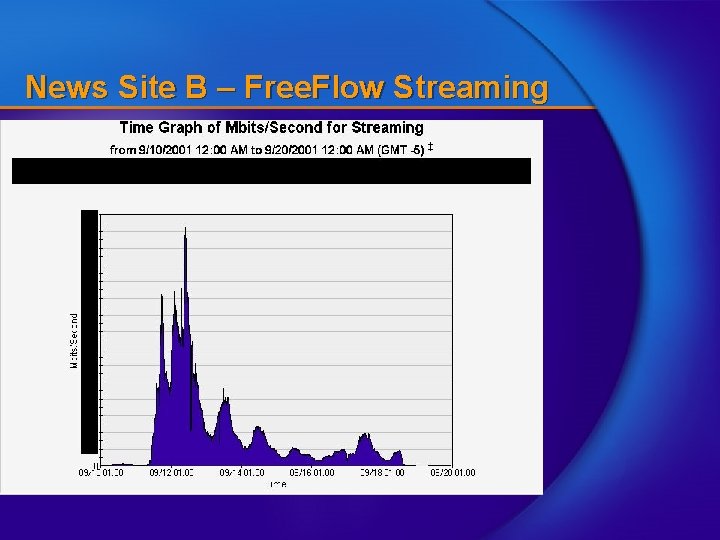
News Site B – Free. Flow Streaming
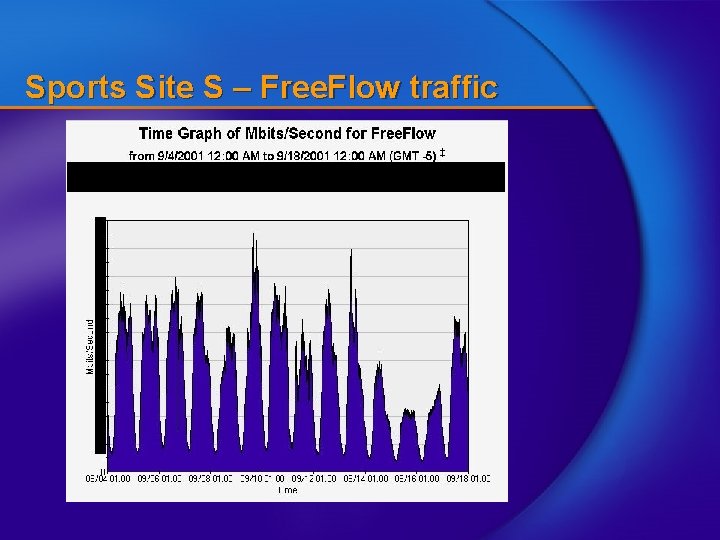
Sports Site S – Free. Flow traffic
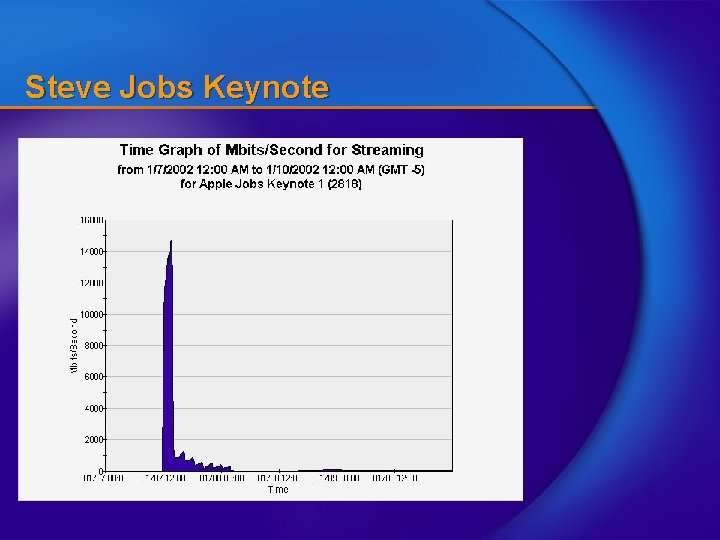
Steve Jobs Keynote
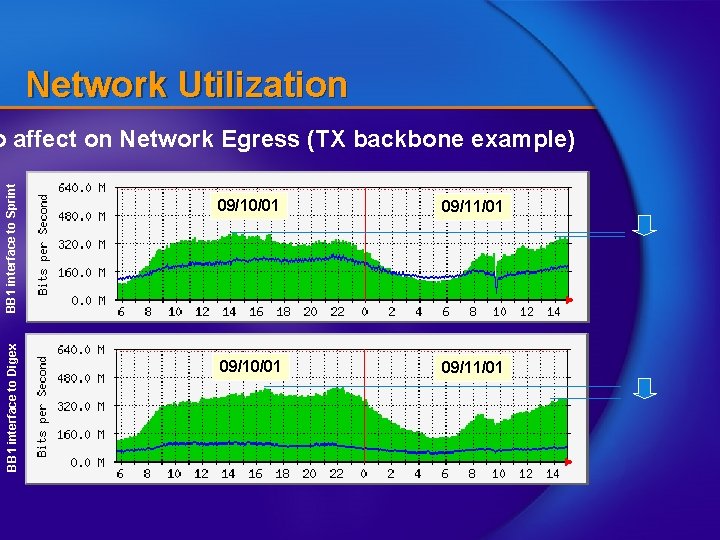
Network Utilization BB 1 interface to Digex BB 1 interface to Sprint o affect on Network Egress (TX backbone example) 09/10/01 09/11/01
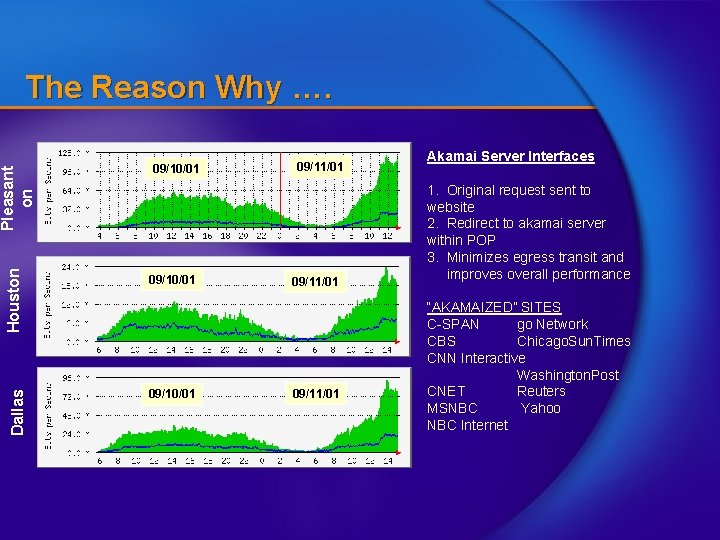
Dallas Houston Pleasant on The Reason Why …. 09/10/01 09/11/01 Akamai Server Interfaces 1. Original request sent to website 2. Redirect to akamai server within POP 3. Minimizes egress transit and improves overall performance “AKAMAIZED” SITES C-SPAN go Network CBS Chicago. Sun. Times CNN Interactive Washington. Post CNET Reuters MSNBC Yahoo NBC Internet
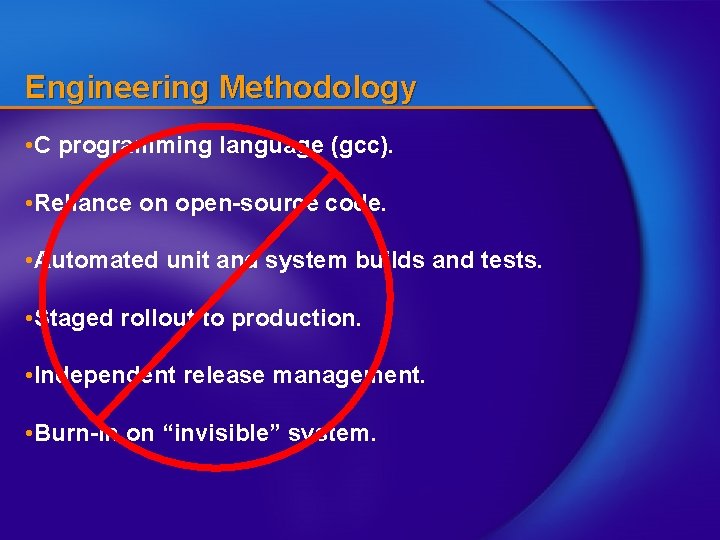
Engineering Methodology • C programming language (gcc). • Reliance on open-source code. • Automated unit and system builds and tests. • Staged rollout to production. • Independent release management. • Burn-in on “invisible” system.
Research Questions (Hard) • How do you know that new software for a distributed system of tens of thousands of servers will work when it is deployed? • How do you even know if a system of tens of thousands of servers is behaving properly? • How do you know when such a system is under attack?
- Slides: 32